Amazon disrupted a watering hole campaign by APT29 that injected obfuscated JavaScript into legitimate websites to redirect a subset of visitors to actor-controlled domains mimicking Cloudflare verification pages and tricking users into authorizing attacker-controlled devices via Microsoft’s device code authentication flow. The actor used evasion tactics (randomized redirects, base64 encoding, cookies) and pivoted infrastructure after disruptions, with identified domains including findcloudflare[.]com and cloudflare[.]redirectpartners[.]com. #APT29 #findcloudflare[.]com
Keypoints
- Amazon’s threat intelligence team identified and disrupted a watering hole campaign attributed to APT29 (Midnight Blizzard) that compromised legitimate websites and injected obfuscated JavaScript.
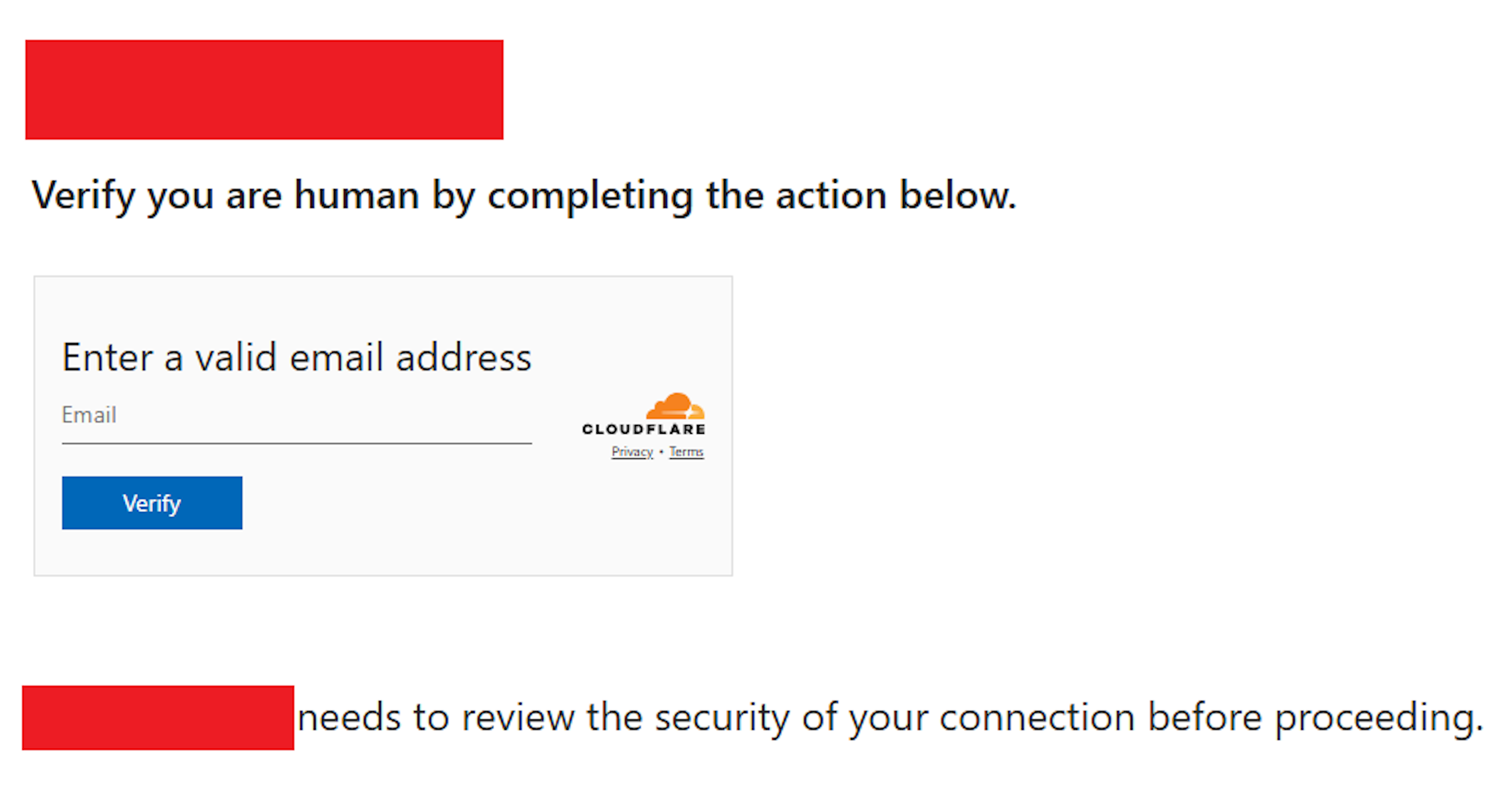
- The injected JavaScript redirected roughly 10% of site visitors to actor-controlled domains that imitated Cloudflare verification pages to funnel victims into Microsoft’s device code authentication flow.
- APT29 employed evasion techniques including randomized sampling of redirects, base64 encoding of malicious code, cookie-based suppression of repeated redirects, and rapid infrastructure pivoting when disrupted.
- Amazon isolated affected EC2 instances, collaborated with Cloudflare, other providers, and Microsoft to disrupt domains and continued tracking actor activity after migrations off AWS.
- Observed actor behavior aligns with prior APT29 activity (phishing with fake AWS domains and campaigns using application-specific passwords) and demonstrates scalability in intelligence collection.
- Recommendations include user vigilance for suspicious redirect chains and device authorization prompts, enabling MFA, and IT actions such as disabling unneeded device authentication flows, enforcing conditional access, and monitoring authentication events.
- Published IOCs include domains used by the campaign and excerpts of injected/decoded JavaScript to assist detection and response.
MITRE Techniques
- [T1189 ] Drive-by Compromise – Use of compromised legitimate websites to inject JavaScript and redirect visitors to attacker-controlled infrastructure: “…injected JavaScript that redirected approximately 10% of visitors to these actor-controlled domains.”
- [T1222 ] Modify Registry (represented by persistence/evasion via cookies and client-side state) – Setting cookies to prevent repeated redirects of the same visitor as an evasion measure: “…Setting cookies to prevent repeated redirects of the same visitor.”
- [T1059 ] Command and Scripting Interpreter (JavaScript) – Use of obfuscated/base64-encoded JavaScript to perform redirects and hide malicious logic: “…Employing base64 encoding to hide malicious code.”
- [T1530 ] Data from Cloud Storage Object (Impersonation of cloud verification pages) – Mimicking Cloudflare verification pages to appear legitimate and harvest credentials/authorizations: “…domains…mimicked Cloudflare verification pages to appear legitimate.”
- [T1608 ] Stage Capabilities (Infrastructure Pivoting) – Rapidly adapting and migrating infrastructure when disrupted, including moving off AWS to other cloud providers: “…pivoting to new infrastructure when blocked” and “move off AWS to another cloud provider.”
- [T1110 ] Brute Force / Credential Access (Credential harvesting focus) – Campaign focused on credential harvesting and device authorization abuse to obtain access: “…continued focus on credential harvesting and intelligence collection… tricking users into authorizing attacker-controlled devices through Microsoft’s device code authentication flow.”
Indicators of Compromise
- [Domain ] Actor-controlled redirect domains used to lure victims – findcloudflare[.]com, cloudflare[.]redirectpartners[.]com
- [Injected Code ] Compromised sites containing obfuscated JavaScript – decoded JavaScript snippet referencing “[removed_domain]” and base64-encoded payloads (example shown in article), and other obfuscated scripts
- [Infrastructure ] EC2 instances and other cloud-hosted infrastructure used by actor – isolated EC2 instances (context: Amazon isolated affected EC2 instances), and actor migration to another cloud provider
Read more: https://aws.amazon.com/blogs/security/amazon-disrupts-watering-hole-campaign-by-russias-apt29/