Lazarus leveraged a ClickFix social-engineering lure in fake recruitment interviews to trick victims into running a malicious “Nvidia” update that installs BeaverTail and the Python trojan InvisibleFerret across Windows and macOS. The campaign uses bat/vbs/shell installers, Node.js deployment, a Win11-specific backdoor drvUpdate.exe (C2 103.231.75.101:8888), and C2 servers such as 45.159.248.110 to exfiltrate data. #BeaverTail #InvisibleFerret
Category: Threat Research
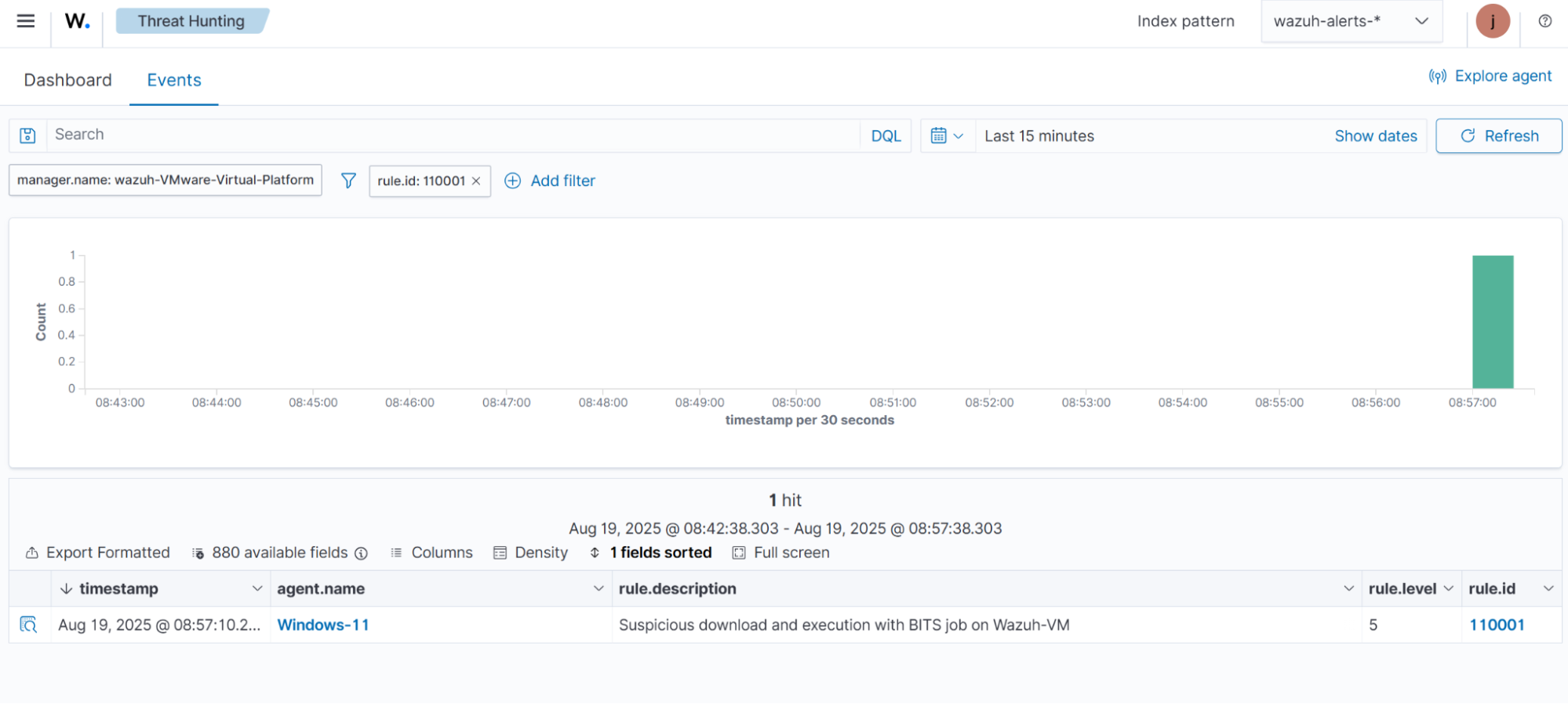
This article explains how Wazuh detects common defense evasion techniques on Windows endpoints by combining Sysmon log enrichment, built-in rules, and custom detection rules. It demonstrates simulations for several MITRE ATT&CK techniques and shows rule examples and alert IDs to monitor on the Wazuh dashboard. #BITSJobs #Mshta…

GodRAT is a Gh0st RAT–derived remote access trojan targeting financial institutions via malicious .scr and .pif files distributed over Skype, using steganography to hide shellcode in images and leveraging plugins like FileManager for credential theft and file-system manipulation. Secondary implants and tools observed include AsyncRAT and browser password stealers; activity affected Hong Kong, UAE, Lebanon, Malaysia, and Jordan. #GodRAT #AsyncRAT
Two mid‑August incidents involved a ransomware variant calling itself “Cephalus” that used RDP access to compromised accounts and leveraged MEGA for likely data exfiltration. The attackers deployed the ransomware via DLL sideloading of SentinelAgentCore.dll through a legitimate SentinelOne executable (SentinelBrowserNativeHost.exe) which then loaded a data.bin containing the ransomware, and the ransom notes linked to news articles and data proof hosted on GoFile to pressure victims. #Cephalus #SentinelBrowserNativeHost.exe
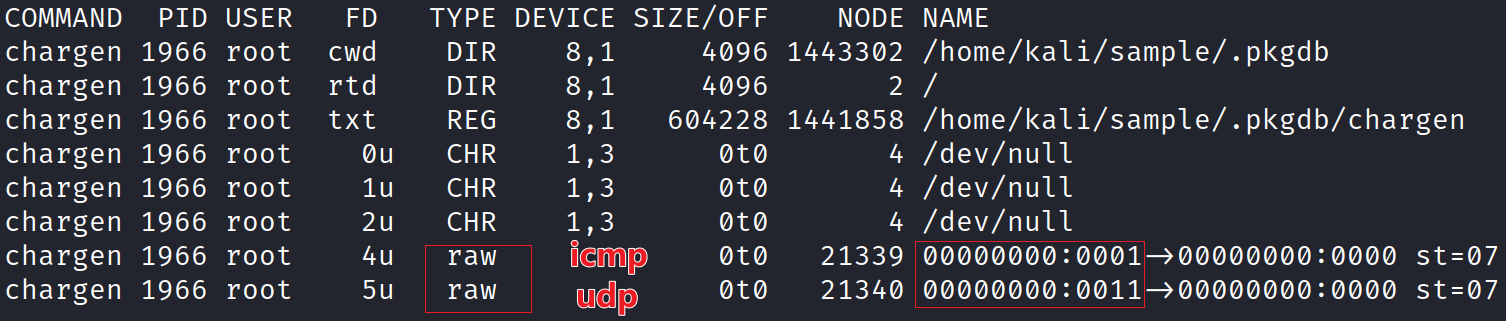
XLab discovered a novel Linux backdoor—MystRodX—delivered by a dropper dst86.bin from IP 139.84.156.79, featuring multi-layer XOR/AES encryption, passive activation via crafted DNS/ICMP triggers, and flexible C2 communication modes. Active C2s tied to campaigns “neybquno” and “zoufkcfr” (e.g., 149.28.137.254:8010) remain online, and multiple sample hashes and indicators are provided to aid hunting….
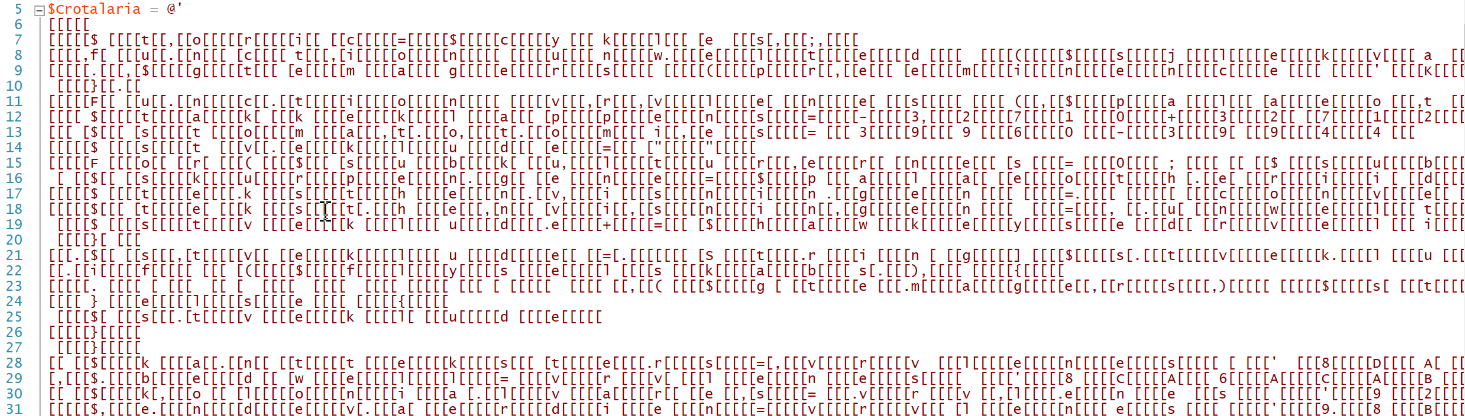
The article describes a PowerShell-based loader that allocates executable memory, copies two shellcode payloads from dropped files, and invokes them via CallWindowProcA instead of creating a new thread to evade EDR detection. The initial dropper is a Windows executable with SHA256 ec8ec8b3234ceeefbf74b2dc4914d5d6f7685655f6f33f2226e2a1d80e7ad488 and it loads payloads from files under %APPDATA%Cafeterias108butikscenters. #ec8ec8b3234ceeefbf74b2dc4914d5d6f7685655f6f33f2226e2a1d80e7ad488…

AppSuite PDF Editor is a trojanized Electron-based PDF editor that contains a full-featured backdoor capable of persistence, scheduled tasks, browser data exfiltration, and remote command execution. The campaign uses high-ranking websites and a Microsoft Installer to distribute the MSI which downloads the malicious app from vault.appsuites.ai. #AppSuite #OneStart
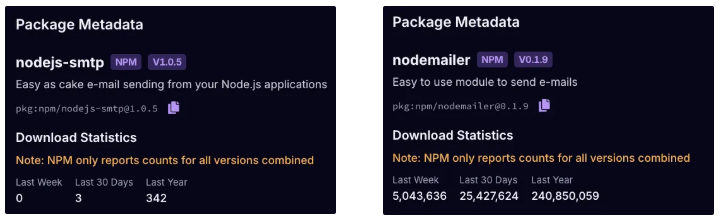
A malicious npm package named nodejs-smtp impersonates nodemailer and, on import, unpacks Electron app.asar files to implant code that redirects cryptocurrency transactions from Atomic and Exodus wallets to attacker-controlled addresses. The actor using the npm alias nikotimon (registration email darkhorse.tech322@gmail[.]com) has limited funds so far, but the trojanized mailer remains live and poses a scalable threat. #nodejs-smtp #nikotimon

Lynx is a Ransomware-as-a-Service group that emerged in mid-2024, likely rebranding or repurposing the INC ransomware source code to produce Windows and Linux (including ESXi) variants that use AES-128 CTR with Curve25519 and append a .lynx extension. The group operates via affiliates, practices double extortion through a public leak site, and by August 2025 had claimed nearly 300 victims concentrated in the United States and industries like Manufacturing and Business Services. #Lynx #INC
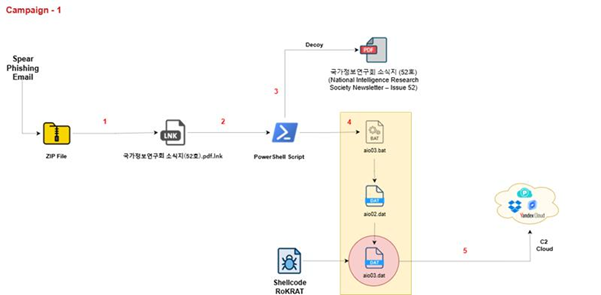
Seqrite Lab uncovered “Operation HanKook Phantom,” a spear-phishing campaign by APT37 using legitimate-looking PDF decoys and malicious LNK files that execute multi-stage, fileless PowerShell loaders to deploy ROKRAT and exfiltrate data via cloud services and a hardcoded HTTP C2. The campaign targets South Korean government, academic, and research organizations and employs XOR-encrypted payloads, in-memory execution, and cloud-based C2 channels like Dropbox, pCloud, and Yandex; #APT-37 #ROKRAT

Interlock ransomware, active since September 2024, conducts continuous attacks across North America and Europe by encrypting files with AES-256-GCM and stealing sensitive data for extortion via a Tor-based negotiation site. The malware uses OpenSSL for combined AES/RSA encryption (RSA-4096 for key wrapping), hides core code via runtime code patching, and appends…

Cyfirma’s analysis describes Inf0s3c Stealer, a PyInstaller-packed, UPX-compressed Python-based grabber that collects system details, user data (including Discord and Telegram tokens, wallets, browser artifacts, and Wi‑Fi credentials), captures screenshots/webcam images, packages results into a password-protected RAR archive, and exfiltrates the archive to an attacker-controlled Discord channel. The report links the sample’s design and obfuscation to other projects like Blank Grabber and Umbral‑Stealer and provides YARA detection guidance and mitigation recommendations. #Inf0s3c #Blank_Grabber

ReversingLabs discovered a loophole in the VS Code Marketplace that allows removed extension names to be reused by different publishers, enabling malicious actors to impersonate previously removed legitimate or malicious extensions. The researchers observed a campaign delivering a downloader extension (ahbanC.shiba) that fetched a second-stage PowerShell payload to encrypt files and demand a Shiba Inu token ransom. #ahbanC.shiba #ahban.shiba

NightSpire is a ransomware group active since February 2025 that operates a Dedicated Leak Site (DLS) with countdown timers and uses highly threatening extortion language while offering ProtonMail, OnionMail, and Telegram channels for negotiations. Their double-extortion operations target corporations across multiple countries and industries, using block encryption for large/virtual-disk-type files and…
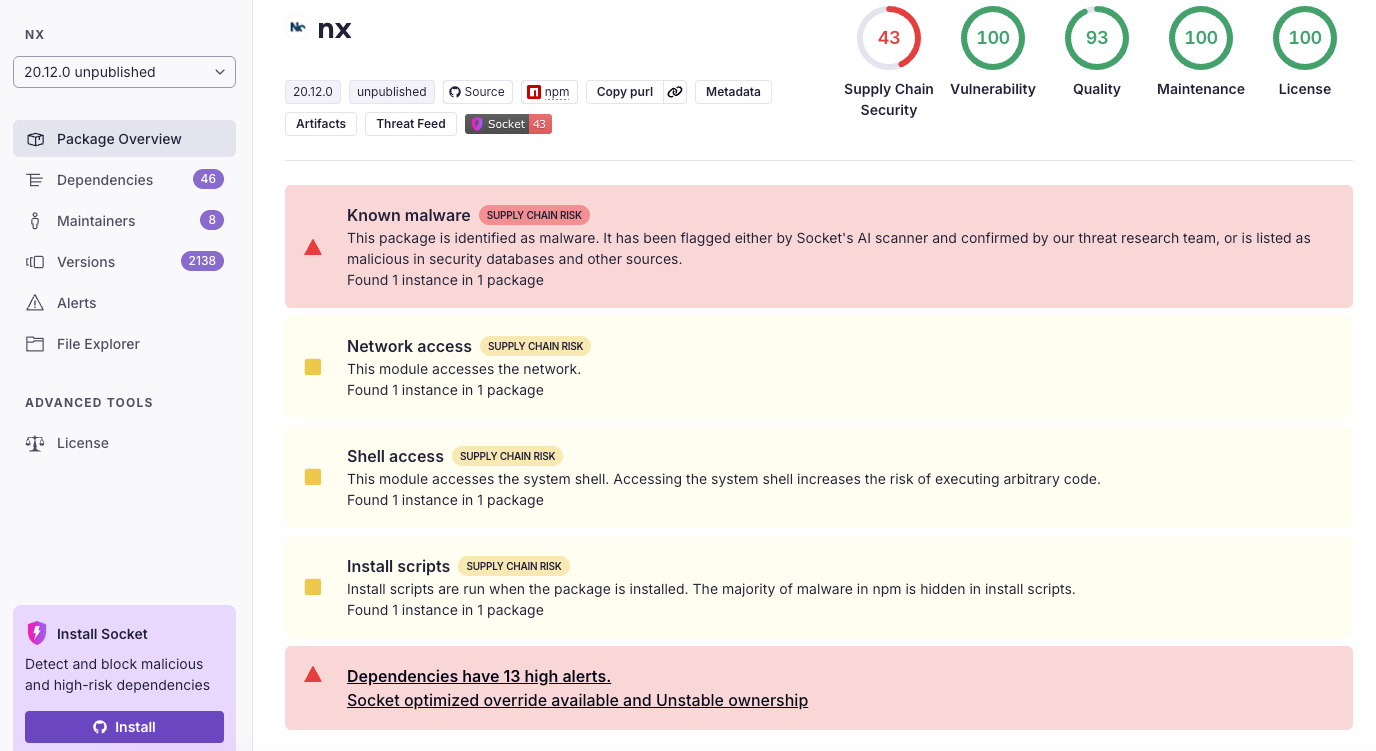
Malicious versions of the Nx build system were published to npm on August 26, 2025 after a GitHub Actions workflow injection allowed an attacker to steal an npm publish token and push packages that harvest credentials and exfiltrate them to public GitHub repositories. The malware abused local AI CLI tools (Claude, Gemini, Q) to enumerate files and steal tokens, SSH keys, and wallet data, then created attacker-controlled repos prefixed with s1ngularity-repository to store triple-base64’d exfiltrated payloads and also appended “sudo shutdown -h 0” to shell RC files to lock out developers. #Nx #s1ngularity-repository
