A malicious npm package named nodejs-smtp impersonates nodemailer and, on import, unpacks Electron app.asar files to implant code that redirects cryptocurrency transactions from Atomic and Exodus wallets to attacker-controlled addresses. The actor using the npm alias nikotimon (registration email darkhorse.tech322@gmail[.]com) has limited funds so far, but the trojanized mailer remains live and poses a scalable threat. #nodejs-smtp #nikotimon
Keypoints
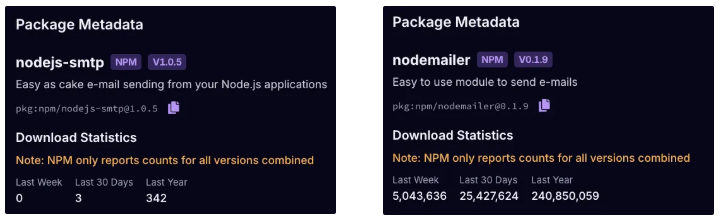
- Socket discovered nodejs-smtp, a trojanized npm package that impersonates nodemailer while performing malicious actions on import.
- On Windows, the package unpacks Atomic Wallet’s app.asar, replaces a vendor bundle with a malicious payload (a.js), repacks the archive, and deletes traces.
- The injected payload overwrites recipient addresses for BTC, ETH/USDT, TRX-USDT, XRP, and SOL transactions so funds route to the attacker’s wallets.
- nodejs-smtp retains mailer functionality and a nodemailer-compatible interface, enabling it to evade casual inspection and testing.
- The threat actor’s npm alias is nikotimon (registration email darkhorse.tech322@gmail[.]com); the package remains live on npm at time of writing.
- Socket’s tooling (Scanner, CLI, GitHub App, browser extension, MCP) can detect import-time side effects, archive manipulation, and impersonation signals to block such packages.
- Defenders should expect more wallet drainers via package registries and AI-assisted supply chain risks targeting multiple chains and Electron apps.
MITRE Techniques
- [T1195.002 ] Supply Chain Compromise – The malicious npm package modifies downstream Electron applications by unpacking app.asar, injecting a payload, and repacking the archive, enabling unauthorized code in target software: “it runs code that modifies Atomic Wallet on Windows by unpacking the app bundle, overwriting a vendor file with threat actor code, and repacking it.”
- [T1036.005 ] Masquerading: Match Legitimate Resource Name or Location – The package copies nodemailer’s tagline, styling, and README to impersonate the legitimate project and mislead developers: “The package copies the nodemailer … tagline, page styling, and README, impersonating the legitimate project to evade casual inspection.”
- [T1059.007 ] Command and Scripting Interpreter: JavaScript – Malicious JavaScript runs on import to perform filesystem and asar operations that implant code into wallet runtimes: “On import, it runs code that modifies Atomic Wallet … await asar.extractAll(asarIn, workDir); await fs.copyFile(implant, target); await asar.createPackage(workDir, asarIn);”
- [T1608.001 ] Stage Capabilities: Upload Malware – The actor bundles the implant (a.js) within the npm package and copies it into target application archives to stage persistent malicious code: “The threat actor’s payload bundled with this package … await fs.copyFile(implant, target);”
- [T1204.002 ] User Execution: Malicious File – The malicious behavior triggers on import (a developer action) causing silent compromise of installed desktop wallets without explicit user awareness: “Any application that requires this module triggers the tampering, even if no email is sent.”
- [T1657 ] Financial Theft – The implanted runtime code overwrites transaction recipient addresses to redirect multi-chain funds to attacker-controlled wallets: “the injected code overwrites the recipient address with hardcoded wallets controlled by the threat actor.”
Indicators of Compromise
- [Malicious Package ] npm package used to deliver payload – nodejs-smtp (impersonates nodemailer), observed live on npm.
- [Threat Actor Alias / Email ] Registration metadata – nikotimon, darkhorse.tech322@gmail[.]com.
- [Wallet Addresses ] Attacker-controlled destination addresses used by injected payload – BTC: 17CNLs7rHnnBsmsCWoTq7EakGZKEp5wpdy; ETH/USDT (ERC20): 0x26Ce898b746910ccB21F4C6316A5e85BCEa39e24.
- [Additional Wallet Addresses ] Other chain addresses used in redirection – TRX-USDT: TShimPsmriHr2GVL7ktVWofMBWCKU5aV8a; XRP: rh3UuQvbnBXSSXhSp3KEb98YhnU2JnXXhK.
- [File / Path ] Targeted Electron archive and vendor bundle paths – app.asar in Atomic/Exodus resources and vendor file example: dist/electron/vendors.64b69c3b00e2a7914733.js.
Read more: https://socket.dev/blog/wallet-draining-npm-package-impersonates-nodemailer