Malicious versions of the Nx build system were published to npm on August 26, 2025 after a GitHub Actions workflow injection allowed an attacker to steal an npm publish token and push packages that harvest credentials and exfiltrate them to public GitHub repositories. The malware abused local AI CLI tools (Claude, Gemini, Q) to enumerate files and steal tokens, SSH keys, and wallet data, then created attacker-controlled repos prefixed with s1ngularity-repository to store triple-base64’d exfiltrated payloads and also appended “sudo shutdown -h 0” to shell RC files to lock out developers. #Nx #s1ngularity-repository
Keypoints
- Multiple Nx and @nx scoped package versions (including [email protected], [email protected], @nx/[email protected], @nx/[email protected], etc.) were published with malware on npm after an attacker extracted an npm publish token via GitHub Actions workflow injection.
- The malicious packages used local AI CLI tools (Claude, Gemini, Q) to enumerate files and produce inventories, a novel supply-chain tactic leveraging developer AI tooling for reconnaissance and data theft.
- The malware harvested GitHub tokens (via gh auth token), npm credentials (~/.npmrc), environment variables, SSH keys, and cryptocurrency wallet files, then triple-base64 encoded and uploaded the data to public GitHub repos prefixed with s1ngularity-repository in victims’ accounts.
- More than 1,000 victim accounts were observed with attacker-created s1ngularity-repository repos containing exfiltrated credentials; victims are being notified and automated scanners reported leaked secrets.
- The malware appended “sudo shutdown -h 0” to ~/.bashrc and ~/.zshrc on non-Windows systems, causing immediate shutdowns on new interactive shells and creating a denial-of-service/persistence vector.
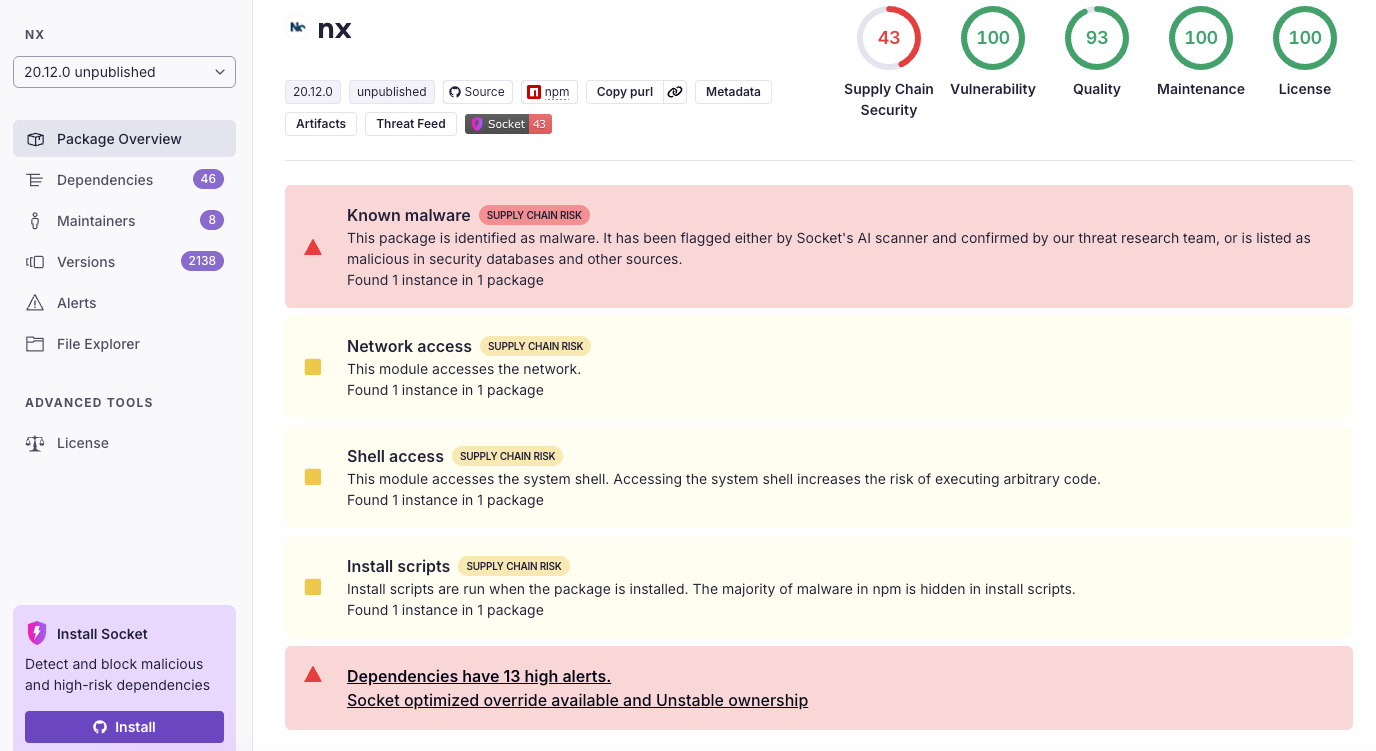
- Socket’s AI scanner, along with independent analysts (StepSecurity, Wiz), detected the malicious behavior quickly, enabling npm to remove the affected versions and Nx maintainers to revoke compromised access.
- Recommended remediation: remove affected package versions, clear npm cache, clean shell RC files and /tmp inventory files, audit and delete unauthorized s1ngularity-repository repos, and rotate/revoke all exposed tokens, keys, and wallets (including revoking the gh CLI OAuth app).
MITRE Techniques
- [T1608] Abuse of GitHub Actions/workflow injection – The attacker exploited a GitHub Actions workflow injection to extract an npm publish token and publish malicious package versions (“the root cause was a GitHub Actions workflow injection vulnerability… attacker exploited this weakness to extract an npm publish token”).
- [T1588] Obtain capabilities via package manager – Malicious versions of widely-used npm packages (nx and @nx scoped packages) were published and distributed via the npm registry to gain execution in developer environments (“used it to publish the malicious versions directly to the npm registry”).
- [T1059] Command and Scripting Interpreter – The malware executed local CLI tools and system commands (gh auth token, npm whoami, appending sudo shutdown -h 0 to shell RCs) to harvest tokens, read files, and disrupt systems (“If gh is on PATH, it runs gh auth token… forceAppendAgentLine() opens or creates ~/.bashrc and ~/.zshrc and blindly prefixes sudo shutdown -h 0”).
- [T1082] System Information Discovery / [T1016] System Network Configuration Discovery (combined) – The malware enumerated files and environment data using AI CLIs to create file inventories for targeted exfiltration (“enumerate the filesystem to locate potentially interesting text files… produce a newline-separated inventory of their full paths at /tmp/inventory.txt”).
- [T1114] Email Collection / T1005 Data from Local System (data discovery/exfiltration) – The malware read and base64-encoded local files (including .env, wallet files, SSH keys) into an inventory for exfiltration (“reads each path from the inventory… reads the bytes, and base64-encodes the entire content into an array”).
- [T1537] Transfer Data to Cloud Account – Exfiltration of harvested data by creating public GitHub repositories under victim accounts and uploading results.b64 via GitHub API (“creates a public repo prefixed with s1ngularity-repository… uploads it as results.b64 via PUT /repos//contents/results.b64”).
- [T1490] Inhibit System Recovery (persistence/denial-of-service) – The malware appends a shutdown command to shell RC files causing immediate shutdowns on new shells, preventing normal recovery (“appended sudo shutdown -h 0 to both ~/.bashrc and ~/.zshrc… every new terminal session triggers an immediate shutdown”).
- [T1218] Signed Binary Proxy Execution / Third-party LLM CLI abuse – The malware invoked third-party AI CLI tools (claude, gemini, q) as part of its reconnaissance, abusing developer AI tooling to enumerate files (“attempts to run three popular AI CLI’s, claude, gemini, and q… with a prompt to enumerate the filesystem”).
Indicators of Compromise
- [Compromised npm packages] Affected package versions published to npm – [email protected], [email protected], @nx/[email protected], @nx/[email protected] (and others listed: nx 20.10.0, 20.11.0, 20.12.0, 21.6.0, 21.7.0, 21.8.0; @nx/[email protected]; @nx/[email protected],20.9.0; @nx/[email protected]; @nx/[email protected],20.9.0; @nx/[email protected],20.9.0).
- [GitHub repositories] Public attacker repositories created in victim accounts – repos prefixed s1ngularity-repository (e.g., s1ngularity-repository-0, s1ngularity-repository-1) containing results.b64 with exfiltrated credentials (more than 1,000 victim accounts observed).
- [Malicious/modified files] Files created or modified on host – telemetry.js (malicious payload included in compromised packages), ~/.bashrc and ~/.zshrc (modified with “sudo shutdown -h 0”), /tmp/inventory.txt and /tmp/inventory.txt.bak (file path listings created by malware).
- [Credentials/tokens] Harvested credential types (examples of what to search for) – GitHub tokens via gh auth token (tokens looking like gho_ or ghp_), npm credentials from ~/.npmrc, SSH keys (id_rsa or keystore files), and wallet files (files matching UTC–, keystore.json, *.keyfile).