TinkyWinkey is a Windows keylogger composed of a service (svc.exe) and a keylogger payload (winkey.exe / keylogger.dll) that achieves persistence via a Windows service, injects a DLL into trusted processes, and captures keystrokes (including Unicode and media keys) alongside detailed system profiling. First observed June 24–25, 2025, components detected include svc.exe, winkey.exe, and keylogger.dll with corresponding SHA-256 hashes. #TinkyWinkey #svc.exe #winkey.exe #keylogger.dll
Category: Threat Research

FortiGuard Labs observed a global phishing campaign that delivers personalized phishing pages which prompt victims to download obfuscated JavaScript droppers (UpCrypter) that execute PowerShell and an in-memory MSIL loader to deploy multiple RATs. The campaign delivered PureHVNC, DCRat, and Babylon RAT via staged downloads, steganography, and persistence mechanisms targeting Windows environments. #UpCrypter #PureHVNC #DCRat #BabylonRAT

A publicly exposed, unrestricted PHP file upload on a Linux webserver allowed a threat actor to upload an obfuscated PHP web shell and a mailer script, though the uploaded payloads were not externally reachable and broader exploitation was prevented. Varonis’ forensic investigation highlighted missing EDR, lack of centralized logs, unpatched high-severity…

SikkahBot is an Android malware active since July 2024 that impersonates the Bangladesh Education Board to phish students, harvest personal and payment data, and gain high-risk permissions to perform automated banking fraud. It intercepts bank-related SMS, abuses Accessibility Service and USSD flows to execute unauthorized transactions and communicates with Firebase-based C2 servers. #SikkahBot #BKash

H1 2025 saw a 16% rise in disclosed CVEs with 161 actively exploited vulnerabilities, many targeting Microsoft and edge/gateway appliances and frequently used to deploy backdoors, RATs, and ransomware. Legacy malware like Sality and Tofsee resurfaced while RATs (AsyncRAT, XWorm, Remcos) and mobile threats (SuperCard X, GodFather) grew prominent, and ransomware groups evolved affiliate models and novel evasion techniques. #Sality #AsyncRAT
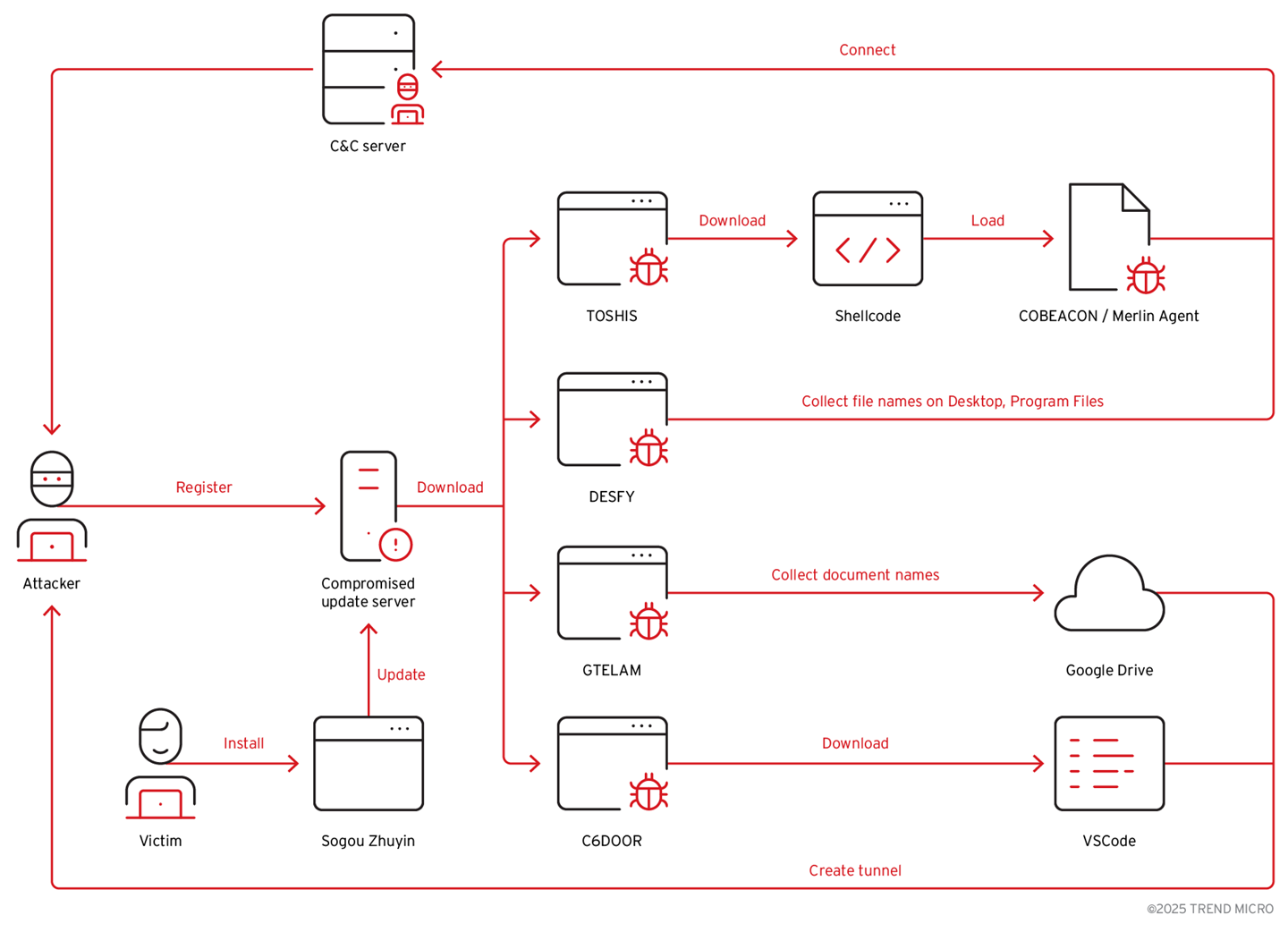
The TAOTH campaign abused an abandoned Sogou Zhuyin update server and targeted victims across Eastern Asia using spear-phishing and hijacked software updates to deliver multiple malware families, including TOSHIS, C6DOOR, DESFY, and GTELAM. Attackers focused on reconnaissance of high-value targets (dissidents, journalists, researchers, business/tech leaders) and reused shared C2 infrastructure and…
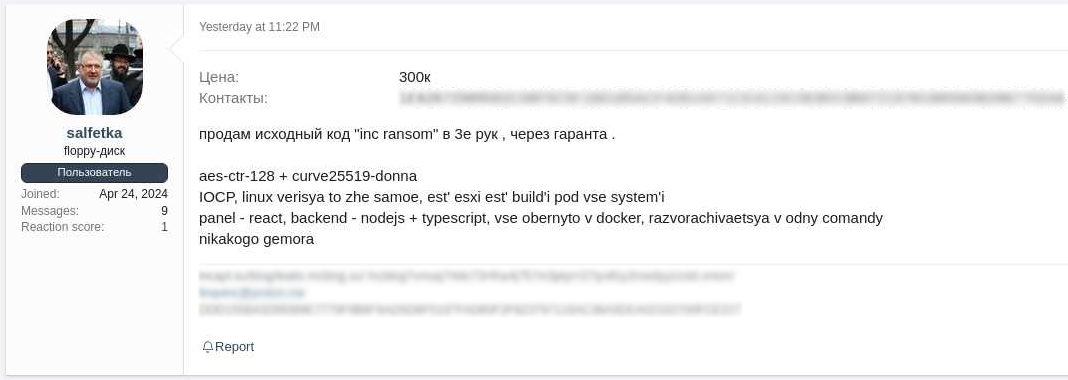
eSentire’s TRU investigated a ransomware incident in August 2025 where a Sinobi Group affiliate — likely a rebrand of Lynx — used compromised SonicWall MSP credentials, disabled Carbon Black EDR, exfiltrated data with RClone, and deployed Sinobi ransomware that encrypts files using Curve-25519 + AES-128-CTR. The report details TTPs, crypto mechanics, remediation actions taken by eSentire, and recommendations to prevent similar breaches. #Sinobi #Lynx
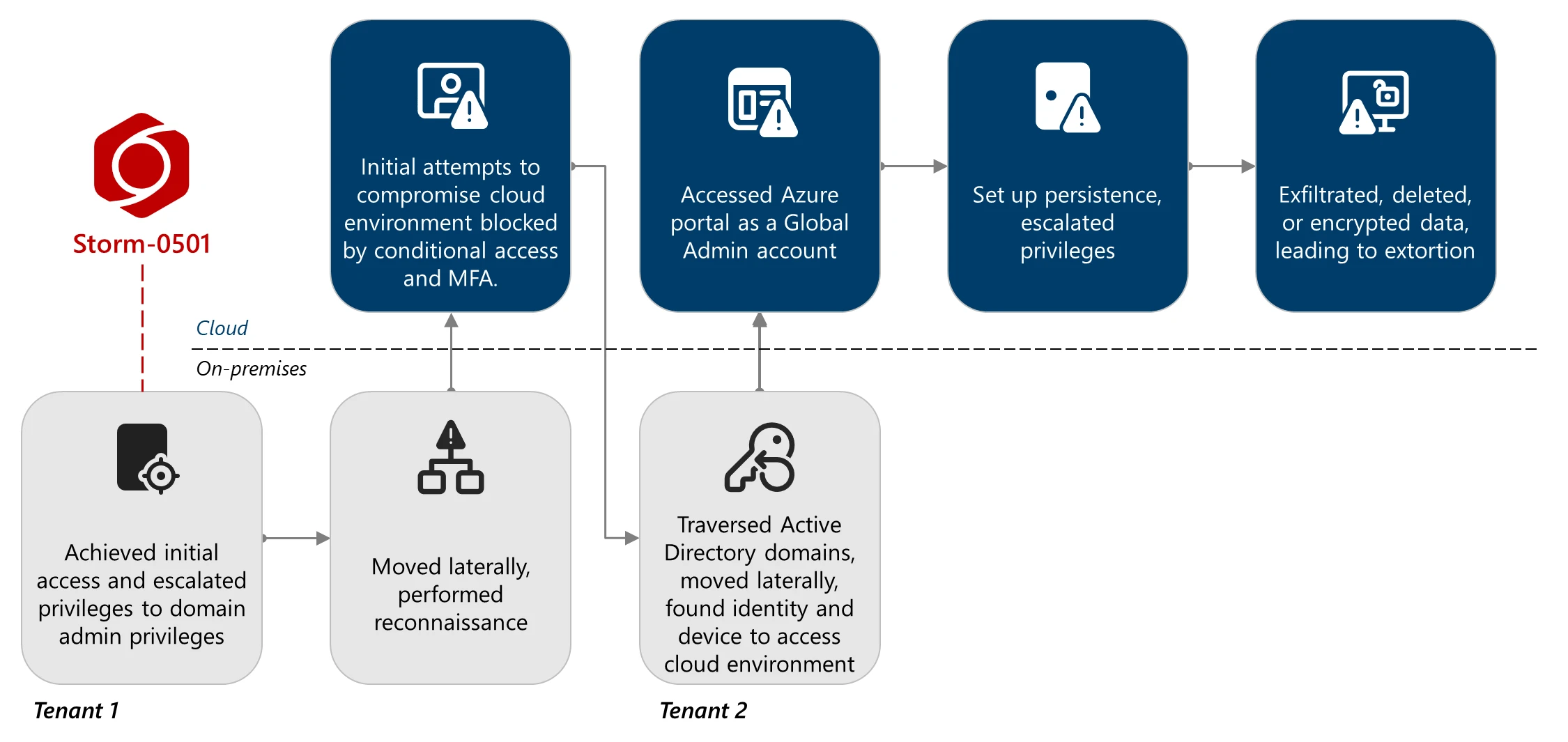
Microsoft Threat Intelligence observed Storm-0501 shift from on-premises endpoint ransomware to cloud-native ransomware tactics that prioritize rapid data exfiltration, destruction of cloud backups and resources, and extortion without deploying traditional malware. The actor abused Entra Connect Sync accounts and Global Administrator privileges to persist via malicious federated domains, escalate Azure privileges, exfiltrate data using AzCopy, delete or encrypt cloud resources, and demand ransom. #Storm-0501 #EntraConnectSync

A targeted Android malware campaign impersonated Indonesia’s state pension fund TASPEN to distribute a banking trojan/spyware APK that steals credentials, SMS OTPs, contacts, and biometric facial video, exfiltrating data to a remote C2 infrastructure. Evidence in error messages and developer artifacts points to a Chinese-speaking operator using domains like taspen[.]ahngo[.]cc and rpc.syids.top. #TASPEN #rpc.syids.top

Chinese state-sponsored APT actors have targeted telecommunications, government, transportation, lodging, and military networks worldwide by exploiting publicly known CVEs, compromising edge routers and using compromised devices and trusted provider links to pivot, persist, and exfiltrate data. Reported activity includes use of custom Go-based SFTP clients, on-box PCAP collection, Guest Shell/container abuse,…
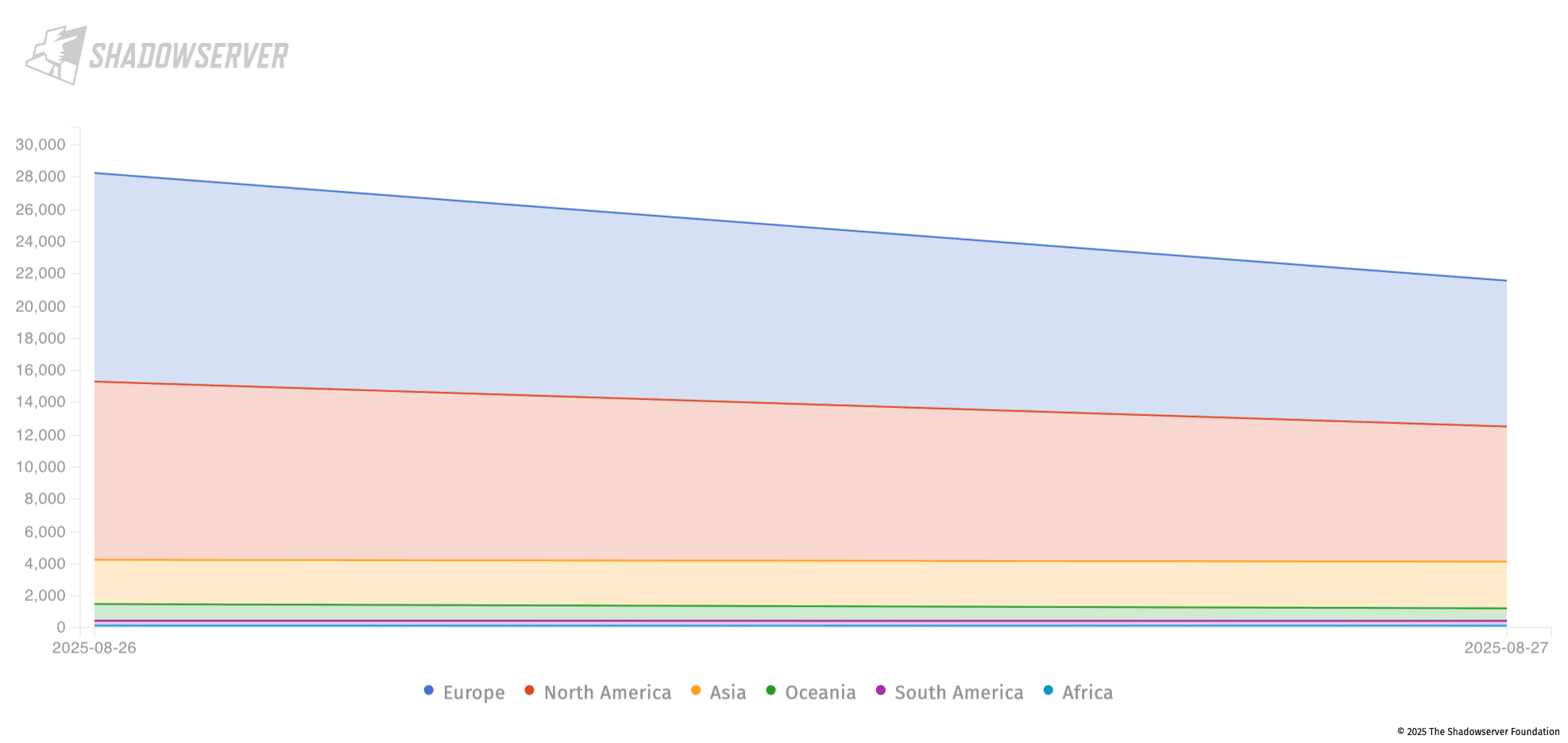
Citrix disclosed three critical/high vulnerabilities in NetScaler ADC and Gateway (CVE-2025-7775, CVE-2025-7776, CVE-2025-8424) that enable remote code execution, denial of service, and unauthorized management access; CVE-2025-7775 is already being actively exploited and all three are in CISA’s KEV catalog. Over 28,000 exposed NetScaler instances were observed online, increasing urgency to patch, restrict management interfaces, and hunt for post-exploitation artifacts. #CVE-2025-7775 #CVE-2025-7776

Warlock is a Ransomware-as-a-Service strain first advertised on RAMP in June 2025 and used by the China-based actor Storm-2603 in at least 11 confirmed incidents, primarily targeting unpatched on-premises Microsoft SharePoint servers via the “ToolShell” exploit chain. AttackIQ released emulations and attack graphs to help organizations validate defenses against Warlock’s exploitation…
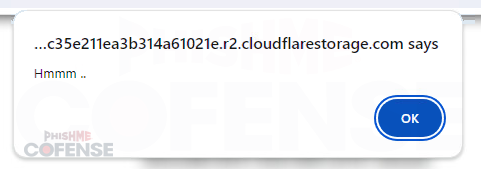
Threat actors use layered evasion methods in phishing kits and email campaigns—embedding links in legitimate hosts, abusing open redirects and QR codes, applying geo/User-Agent/language filters, CAPTCHA or developer-tools detection, email/domain allowlists, password protection, and quick-deploy subdomains to delay detection and frustrate analysts. Defenders should combine manual analyst techniques (User-Agent/VPN spoofing, targeted mailbox checks) with tuned automated systems to detect suspicious subdomains and adapt to evolving offensive AI-driven defenses. #GeoJS #Mispadu
%20and%20anhemvn6%5B.%5Dcom%20(right)%20when%20sites%20were%20still%20active.jpg?width=922&height=271&name=Figure%201.%20Screenshots%20of%20gptgrok%5B.%5Dai%20(left)%20and%20anhemvn6%5B.%5Dcom%20(right)%20when%20sites%20were%20still%20active.jpg)
Trustwave SpiderLabs discovered a deceptive campaign using fake AI-themed websites to trick users into installing a modified, digitally signed ScreenConnect installer that ultimately delivered an Xworm RAT via a multi-stage infection chain hosted on GitHub. The campaign used process hollowing, registry persistence, hidden remote sessions, and GitHub-hosted obfuscated Python scripts to evade EDR detection and enable credential theft and remote control. #ScreenConnect #XWorm

FreeVPN.One, a Chrome extension with 100k+ installs and a verified badge, secretly captured screenshots of users’ browsing (including Google Sheets, banking pages, and photos) and exfiltrated them to aitd.one and related servers without consent. The extension escalated permissions over multiple updates, added encryption to hide exfiltration, and continued surveillance despite developer claims; #FreeVPN.One #aitd.one
