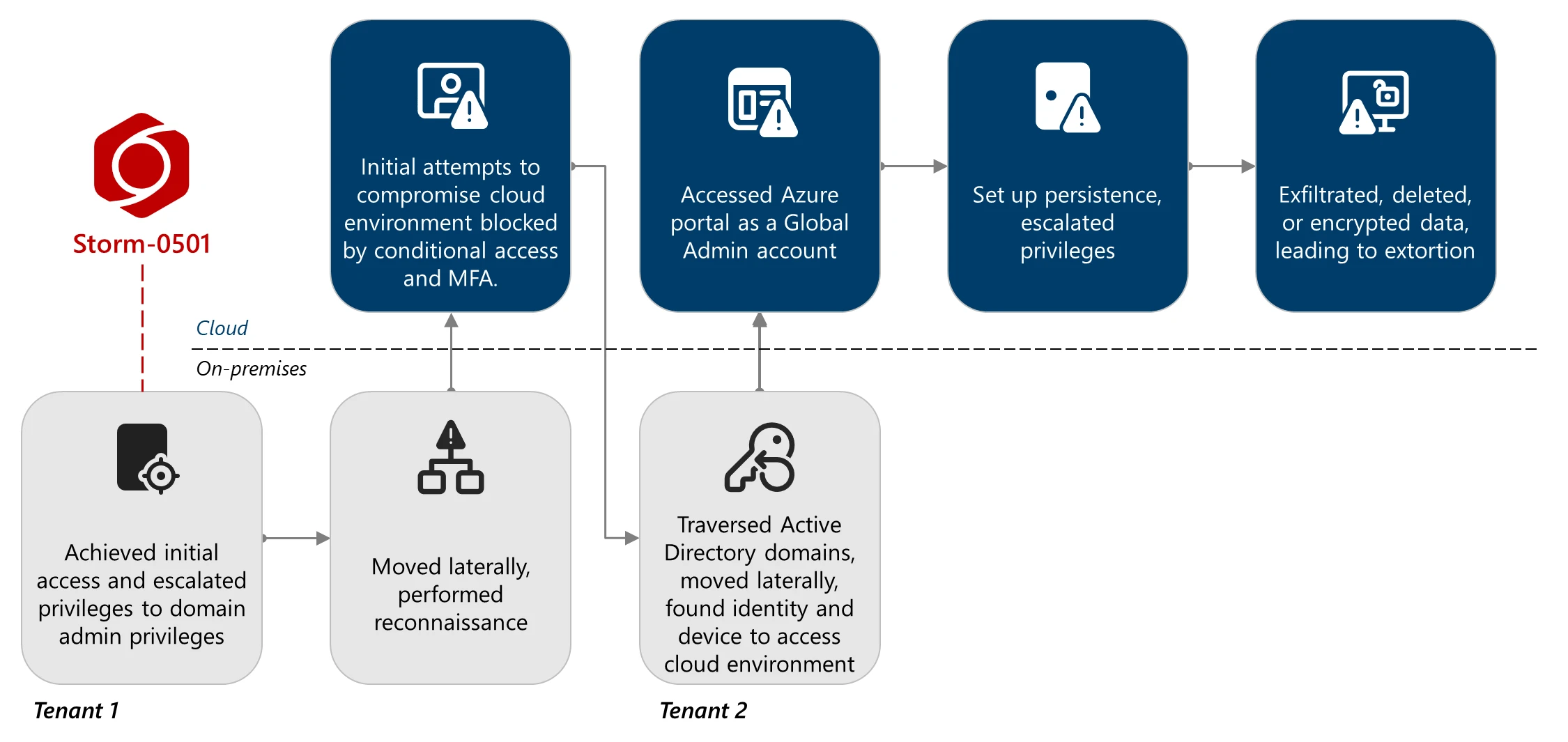
Microsoft Threat Intelligence observed Storm-0501 shift from on-premises endpoint ransomware to cloud-native ransomware tactics that prioritize rapid data exfiltration, destruction of cloud backups and resources, and extortion without deploying traditional malware. The actor abused Entra Connect Sync accounts and Global Administrator privileges to persist via malicious federated domains, escalate Azure privileges, exfiltrate data using AzCopy, delete or encrypt cloud resources, and demand ransom. #Storm-0501 #EntraConnectSync
Keypoints
- Storm-0501 evolved from deploying on-premises ransomware to leveraging cloud-native capabilities to exfiltrate, destroy, and extort data in Azure environments.
- The actor leveraged compromises of Active Directory and Entra Connect Sync servers to pivot into multiple Entra ID tenants and enumerate identities and resources using tools like AzureHound.
- Credential and identity escalation included DCSync attacks, resetting a Global Administrator synced account password, registering MFA under actor control, and signing in from a hybrid-joined device to meet Conditional Access policies.
- Persistent backdoors were created by registering threat-actor-owned federated domains and using AADInternals to craft SAML tokens that impersonate tenant users.
- With Global Admin access the actor elevated to User Access Administrator and Owner roles across subscriptions, stole storage account keys, exposed storage to public access, and exfiltrated data using AzCopy.
- Impact activities included mass deletion of snapshots, restore points, storage accounts, and backup containers; when deletion failed, the actor created Key Vaults and encryption scopes and attempted to delete keys to render data inaccessible.
- Mitigations recommended include tightening DSA permissions, enabling modern authentication for Entra Connect, broad Defender coverage, Conditional Access and MFA for all privileged accounts, immutable storage and resource locks, and Defender for Cloud monitoring.
MITRE Techniques
- [T1518] Software Discovery – Used enumeration tools and commands (e.g., “sc query sensesc query windefend”) to check for Defender for Endpoint presence and avoid monitored systems [‘sc query sensesc query windefend’].
- [T1021.004] Remote Services: WinRM – Lateral movement using Evil-WinRM to execute PowerShell over WinRM for remote code execution [‘Evil-WinRM … PowerShell over Windows Remote Management (WinRM) for remote code execution’].
- [T1003.006] OS Credential Dumping: DCSync – Performed DCSync to request password hashes by impersonating a domain controller to extract credentials [‘DCSync attack … simulate the behavior of a domain controller’].
- [T1218] Signed Binary Proxy Execution – Used native Windows tools and common commands (e.g., quser.exe, net.exe) for discovery and execution to blend with legitimate activity [‘discovery using other common native Windows tools and commands such as quser.exe and net.exe’].
- [T1086] PowerShell – Executed discovery and hands-on-keyboard activity using PowerShell via remote sessions (as observed with Evil-WinRM and suspicious cmdlets) [‘suspicious cmdlets launch using AADInternals’].
- [T1087] Account Discovery – Enumerated users, roles, and Azure resources using Entra Connect Sync and AzureHound to map permissions and identify privileged accounts [‘leveraged the Entra Connect Sync Directory Synchronization Account (DSA) to enumerate users, roles, and Azure resources … using AzureHound’].
- [T1078] Valid Accounts – Abused synced non-human account (Global Administrator) by resetting its on-premises password and syncing it to cloud to gain access without initial second factor [‘reset the user’s on-premises password … legitimately synced to the cloud identity’].
- [T1550.003] Use of a Cloud Account – Registered a malicious federated domain and used federated token trust to craft SAML tokens to impersonate tenant users for persistence [‘registered a threat actor-owned Entra ID tenant as a trusted federated domain … craft security assertion markup language (SAML) tokens’].
- [T1548.002] Domain Policy Modification – Added a federated domain and provided a threat-actor-generated certificate to establish cross-tenant trust and backdoor access [‘registered a threat actor-owned Entra ID tenant as a trusted federated domain … a threat actor-generated root certificate is provided’].
- [T1531] Account Manipulation – Registered new MFA methods under control of the actor for the compromised Global Admin to satisfy Conditional Access MFA requirements [‘the threat actor was redirected to simply register a new MFA method under their control’].
- [T1538] Steal or Forge Kerberos Tickets – (Contextual) Abused synchronization and authentication flows to impersonate users via ImmutableId and federated SAML tokens [‘backdoor using a maliciously added federated domain, enabling them to sign in as almost any user, according to the ImmutableId user property’].
- [T1537] Transfer Data to Cloud Account – Exfiltrated large volumes of data from Azure Storage accounts to attacker infrastructure using AzCopy CLI [‘exfiltrated the data in these accounts to their own infrastructure by abusing the AzCopy Command-line tool (CLI)’].
- [T1486] Data Encrypted for Impact – Performed cloud-based encryption by creating Key Vaults and encryption scopes to encrypt storage blobs, then attempted to delete keys to render data inaccessible [‘created a new Azure Key Vault and a new Customer-managed key … encrypted the Storage blobs … attempted to delete the key’].
- [T1485] Data Destruction – Mass deletion of Azure snapshots, restore points, storage accounts, and backup protection containers to prevent recovery [‘mass-deletion of the Azure resources … Microsoft.Storage/storageAccounts/delete … Microsoft.Compute/snapshots/delete’].
- [T1530] Data from Cloud Storage Object – Used Azure Storage public access features and modified storage account configurations to expose and access sensitive blob containers for exfiltration [‘utilizing the public access features in Azure Storage … abused the Azure Microsoft.Storage/storageAccounts/write operation’].
Indicators of Compromise
- [Account/Identity ] compromised service and sync accounts – Entra Connect Sync Directory Synchronization Account (DSA), a non-human Global Administrator synced identity (no MFA registered)
- [Tools ] tooling observed – AzureHound (Azure environment mapping), AADInternals (federation and token crafting), Evil-WinRM (lateral movement), AzCopy (data exfiltration)
- [Commands/Artifacts ] detection-relevant commands – “sc query sensesc query windefend” (checking Defender for Endpoint), suspicious cmdlets via AADInternals
- [Azure Operations ] abused Azure management operations – examples include Microsoft.Authorization/elevateAccess/action, Microsoft.Authorization/roleAssignments/write, Microsoft.Storage/storageAccounts/delete, Microsoft.Compute/snapshots/delete (and other delete/write operations)
- [Azure Resource Types ] targeted resource examples – Azure Storage accounts and blob containers (exposed and exfiltrated), Azure Key Vaults and encryption scopes (created and abused)