Trustwave SpiderLabs discovered a deceptive campaign using fake AI-themed websites to trick users into installing a modified, digitally signed ScreenConnect installer that ultimately delivered an Xworm RAT via a multi-stage infection chain hosted on GitHub. The campaign used process hollowing, registry persistence, hidden remote sessions, and GitHub-hosted obfuscated Python scripts to evade EDR detection and enable credential theft and remote control. #ScreenConnect #XWorm
Category: Threat Research

FreeVPN.One, a Chrome extension with 100k+ installs and a verified badge, secretly captured screenshots of users’ browsing (including Google Sheets, banking pages, and photos) and exfiltrated them to aitd.one and related servers without consent. The extension escalated permissions over multiple updates, added encryption to hide exfiltration, and continued surveillance despite developer claims; #FreeVPN.One #aitd.one
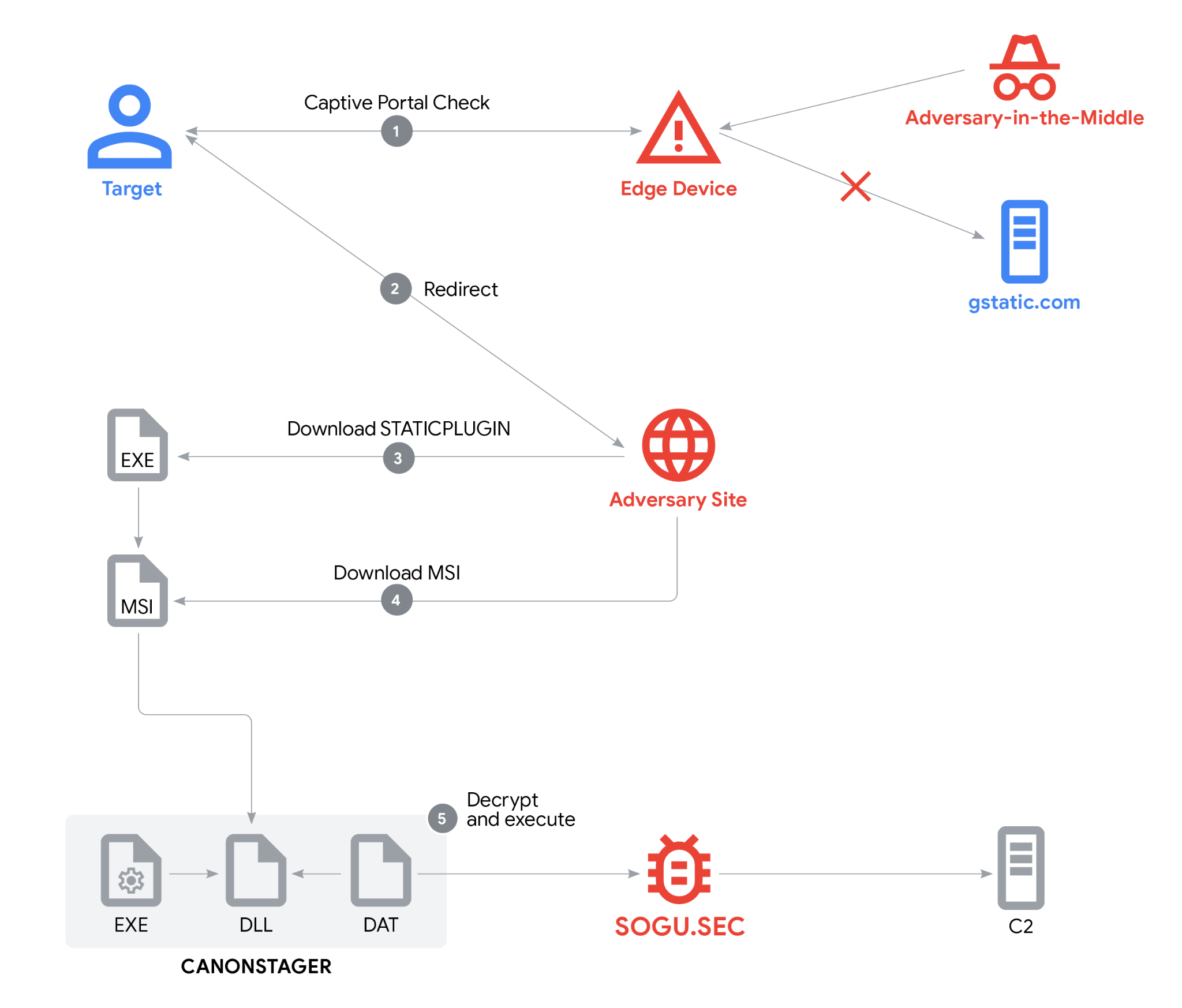
Google Threat Intelligence Group (GTIG) discovered a multifaceted espionage campaign by PRC-nexus actor UNC6384 that hijacked captive-portal browser redirects to deliver a digitally signed downloader (STATICPLUGIN) which ultimately side-loaded CANONSTAGER to deploy the in-memory SOGU.SEC backdoor. The campaign targeted diplomats in Southeast Asia and used valid TLS and code-signing certificates, AitM on edge devices, and layered social engineering to evade detection. #UNC6384 #STATICPLUGIN #CANONSTAGER #SOGU.SEC
Festive-themed scams spike around Ganesh Chaturthi, with fraudsters using fake online idol sellers, cloned e-commerce sites, lottery and gift scams, fake event tickets, and fraudulent UPI/payment requests to steal money and personal data. Reported incidents include large financial losses from fake sweet orders, virtual darshan apps, and fraudulent contribution collectors, highlighting the need to verify sellers, avoid suspicious links, and report fraud promptly. #Utsav #TiwariMithaiwala

CTU researchers analyzed an August 2025 intrusion where an attacker deployed legitimate Velociraptor DFIR tooling to stage and run Visual Studio Code with tunneling enabled, likely to create a tunnel to an attacker-controlled C2 and enable remote code execution. The incident used Cloudflare Workers staging domains to host installers and C2 (files.qaubctgg.workers.dev, velo.qaubctgg.workers.dev) and triggered a Taegis alert that enabled containment before likely ransomware deployment. #Velociraptor #VisualStudioCode
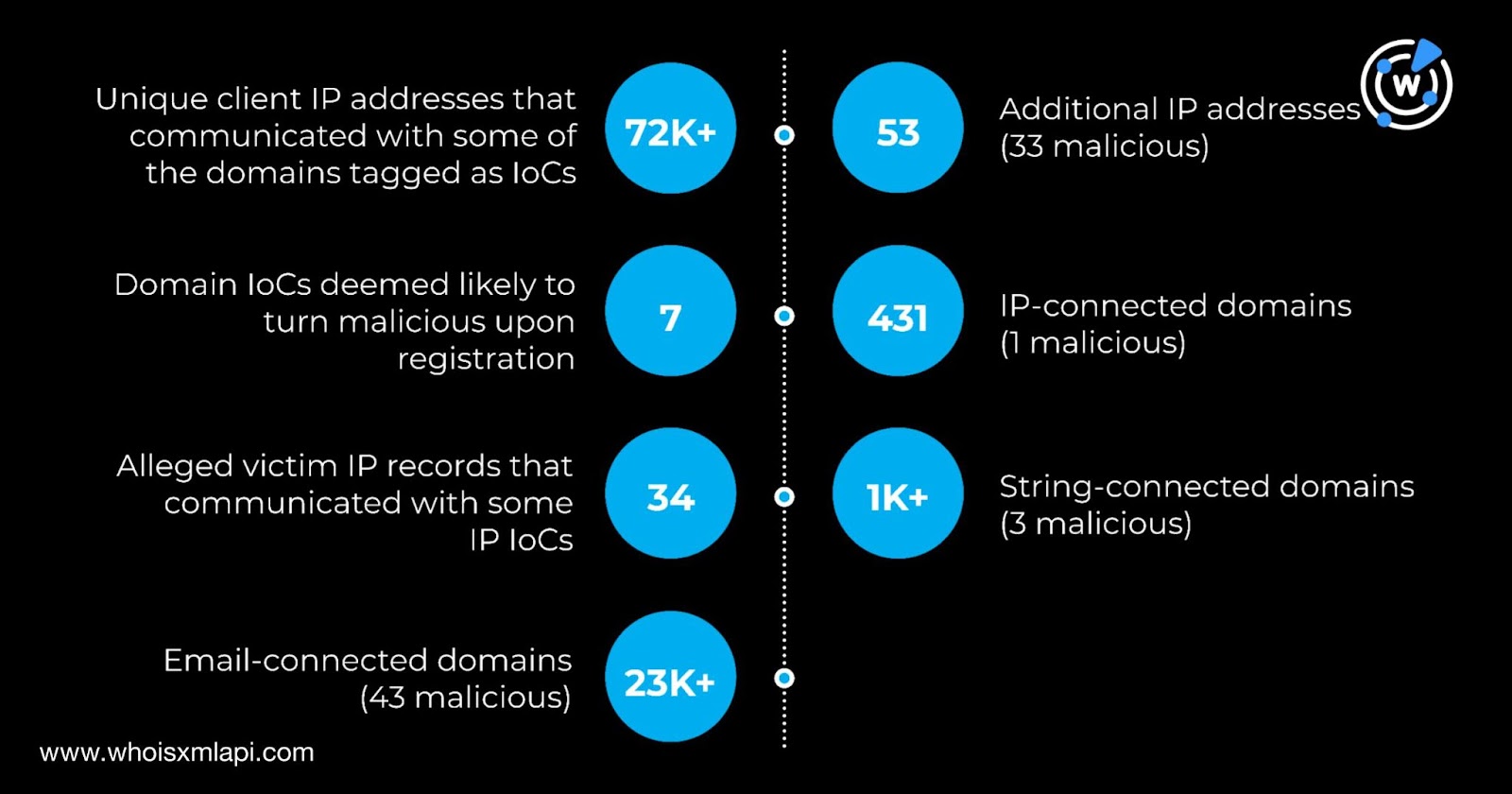
CIS CTI’s “Top 10 Malware Q2 2025” report lists the quarter’s top malware families and 62 associated IoCs (53 domains, 9 IPs) and expands that set to 62 IPs and thousands of related artifacts through WHOIS/DNS and threat-intel queries. Analysis found 72,921 unique client IPs querying IoC domains, multiple IoCs appearing on threat feeds before reporting, and additional weaponized IPs tied to the IoCs. #SocGholish #AgentTesla
ANY.RUN analysts tracked August campaigns including a 7-stage Tycoon2FA phishing chain, Rhadamanthys delivered via ClickFix with PNG steganography, and a new Salty2FA PhaaS linked to Storm-1575, exposing execution chains, decrypted traffic, and behaviors missed by static tools. The investigations produced IOCs and behavioral indicators SOC teams can use to build detection…

A critical unauthenticated WebSocket vulnerability (CVE-2025-52882) in Anthropic’s Claude Code IDE extensions allowed malicious websites to connect to local MCP servers and execute commands, including reading local files and running code in Jupyter notebooks; the flaw is fully patched in version 1.0.24 and later and vulnerable versions were removed from extension stores. #ClaudeCode #CVE-2025-52882
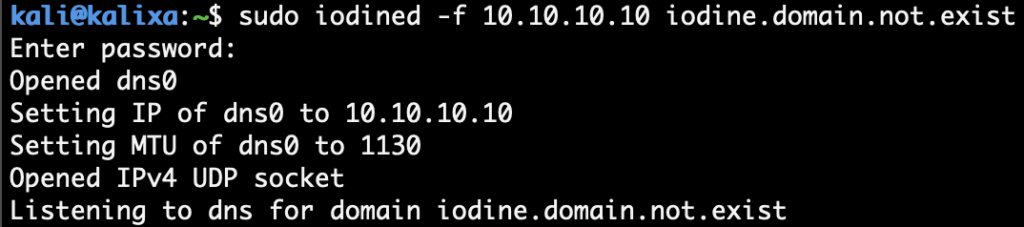
DNS tunneling is increasingly used for stealthy data exfiltration and command-and-control by embedding encoded data in DNS queries and responses, exploiting permissive DNS traffic and flexible record types like TXT. Notable tools—iodine, dnspot, and dnscat2—demonstrate tunneling, chat, and C2 over DNS; mitigation includes restricting resolvers, anomaly detection, and deep DNS inspection. #iodine #dnspot #dnscat2
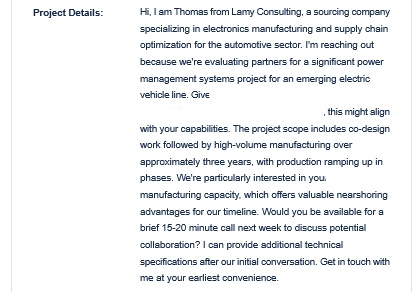
Check Point Research discovered the ZipLine campaign, a sophisticated social-engineering operation that uses corporate “Contact Us” forms to start legitimate-looking email conversations and deliver weaponized ZIP archives hosting a PowerShell loader that deploys an in-memory implant called MixShell. The implant uses DNS TXT tunneling with HTTP fallback for C2, supports reverse proxying and file/command operations, and the campaign abuses aged or cloned domains and Heroku-hosted payloads. #MixShell #ZipLine

Insikt Group identified five distinct TAG-144 (Blind Eagle) activity clusters active during 2024–2025 that primarily targeted Colombian government entities using open-source and cracked RATs, dynamic DNS domains, and extensive abuse of legitimate internet services for staging and steganographic payload delivery. The report also documents overlaps with Red Akodon, widespread use of compromised Colombian government email accounts for spearphishing, and a large set of IoCs including domains, IPs, and file hashes. #TAG-144 #BlindEagle #RedAkodon #AsyncRAT #REMCOS #LimeRAT

The Underground ransomware group conducts targeted, customized encryption and data theft operations against organizations worldwide, using a combination of AES and RSA encryption with per-file keys and stripe-based encryption for large files. Their operations include system reconnaissance, deletion of shadow copies and logs, and publication of stolen data via a Tor-based…

FortiGuard Labs tracked the evolved “Gayfemboy” malware exploiting multiple vendor vulnerabilities (DrayTek, TP-Link, Raisecom, Cisco) to deliver a downloader that installs the botnet and coin miners across diverse sectors and countries. Campaign infrastructure included consistent attack source and download hosts, multiple C2 domains, UPX anti-unpacking tricks, sandbox evasion, process-killing of competitors, DDoS/backdoor capabilities, and explicit IOCs. #Gayfemboy #cross-compiling.org
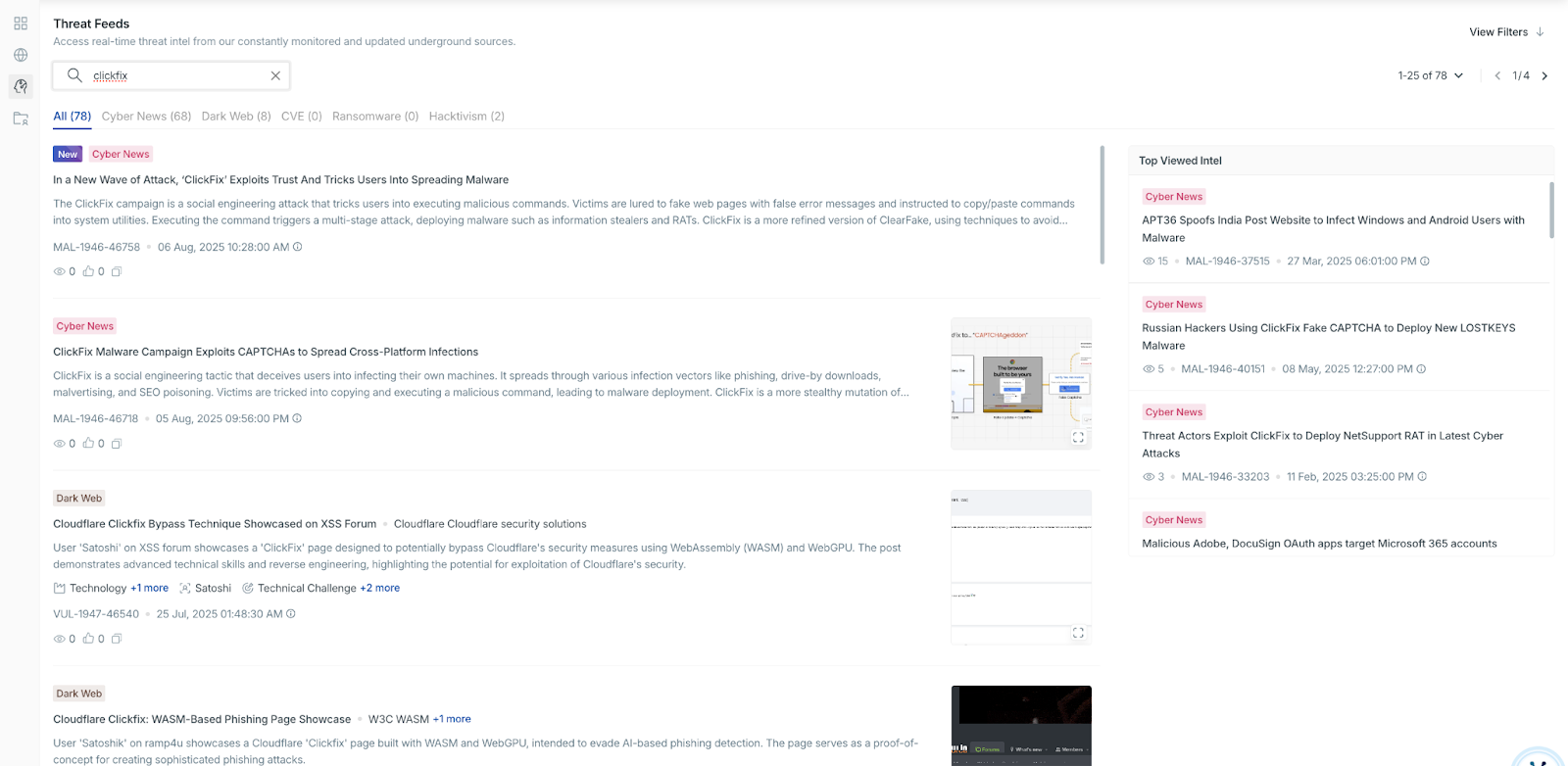
Researchers demonstrated that invisible prompt injection combined with prompt overdose can force AI summarizers to output hidden ClickFix-style instructions, enabling covert delivery of ransomware execution steps embedded in HTML via CSS obfuscation. The technique exploits summarizers in email clients, browser extensions, and productivity tools, turning them into unintentional distribution channels for attacker-controlled commands. #ClickFix #prompt_overdose
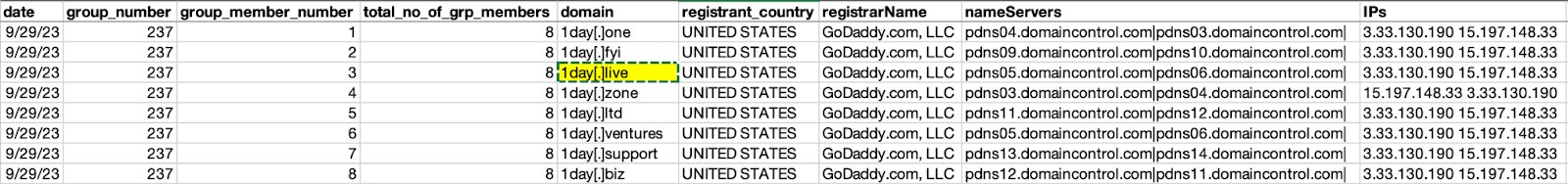
Proofpoint linked RomCom to TA829 and TransferLoader to UNK_GreenSec but noted campaign similarities; WhoisXML API expanded the analysis of 109 IoC domains, uncovering typosquatting groups and numerous connected artifacts. The investigation found four TransferLoader domain IoCs in five typosquatting groups, multiple shared infrastructure signals (registrars, NS providers, IPs), and thousands of connected domains and IPs with dozens marked malicious. #RomCom #TransferLoader
%20and%20anhemvn6%5B.%5Dcom%20(right)%20when%20sites%20were%20still%20active.jpg?width=922&height=271&name=Figure%201.%20Screenshots%20of%20gptgrok%5B.%5Dai%20(left)%20and%20anhemvn6%5B.%5Dcom%20(right)%20when%20sites%20were%20still%20active.jpg)