Two high-severity WinRAR vulnerabilities, CVE-2025-6218 and CVE-2025-8088, allow attackers to write files outside the intended extraction directory and hide payloads using NTFS Alternate Data Streams, enabling stealthy persistence and remote code execution with minimal user interaction. Exploitation has been observed in the wild by threat actors RomCom and Paper Werewolf (GOFFEE), and patches are available in WinRAR 7.12 Beta 1 / 12 and version 13 respectively. #CVE-2025-6218 #CVE-2025-8088 #RomCom #PaperWerewolf
Category: Threat Research
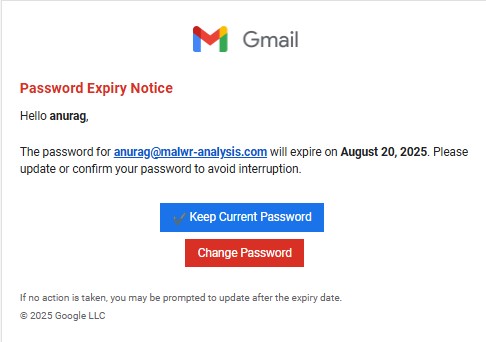
Attackers sent a Gmail-themed credential-harvesting phishing email that included a hidden prompt-injection block in the plain-text MIME section designed to distract or manipulate AI-based defensive tools. The campaign used SendGrid delivery, a Dynamics staging redirect, captcha-gated phishing pages, obfuscated multi-stage JavaScript, and telemetry calls to profile victims. #SendGrid #bwdpp.horkyrown.com…
Zimperium zLabs uncovered a new Hook Android banking trojan variant that adds ransomware-style and fake NFC overlays, lockscreen bypasses, transparent gesture-capture overlays, and stealthy screen-streaming, expanding to 107 remote commands (38 new). The malware is being widely distributed via phishing sites and GitHub repositories and shows signs of evolving C2 capabilities (RabbitMQ, Telegram) and broad targeting of wallet and banking apps. #Hook #RabbitMQ

A Remote Code Execution (RCE) exploit — CVE-2025-53770, known as the ToolShell zero-day — was used via SharePoint_FileStorage.dll to gain SYSTEM privileges on Colt Technology Services’ public SharePoint, enabling deployment of the WarLock toolkit and rapid lateral movement. The actor used ToolShell.exe and other LOLBins to evade EDR, staged C2 at cnkjasdfgd.xyz, and deployed WarLock ransomware across multiple internal servers. #CVE-2025-53770 #WarLock #cnkjasdfgd.xyz

Mandiant observed UNC5518 using ClickFix fake CAPTCHA pages to trick users into executing downloader scripts that delivered CORNFLAKE.V3, a Node.js or PHP-based backdoor attributed to UNC5774. The intrusions included persistence via Registry Run keys, Active Directory reconnaissance, and Kerberoasting, with follow-on payloads such as WINDYTWIST.SEA used for lateral movement. #UNC5518 #UNC5774 #CORNFLAKE.V3 #WINDYTWIST.SEA
Deceptive websites cloned from the Google Play Store are delivering AndroidOS SpyNote RAT via APK droppers that use dynamic payload decryption, DEX element injection, and added anti-analysis techniques to evade detection. The actor re-used infrastructure with minor IP rotations and continues to target consumers with spoofed popular apps like Chrome, CamSoda, and iHappy. #SpyNote #Chrome #CamSoda
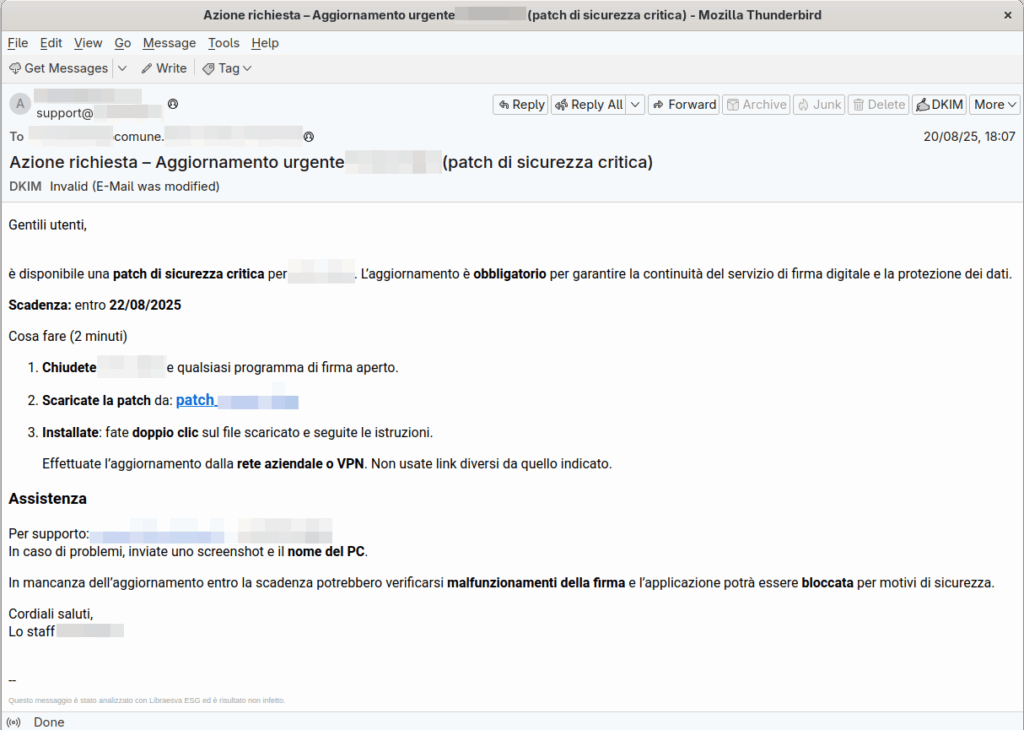
A phishing campaign targeting Italian public administrations used a fake urgent digital signature update to deliver a ZIP with a VBS that installs the legitimate remote-management tool Action1 for unauthorized access. CERT-AGID confirmed this is the first observed abuse of Action1 in Italy, shared IoCs with accredited organizations, and advised remediation steps. #Action1 #CERT-AGID

Anatsa (TeaBot) is an evolving Android banking trojan that now targets over 831 financial and cryptocurrency applications worldwide and uses enhanced anti-analysis and evasion techniques. The malware streamlines payload delivery, uses runtime DES decryption and device checks, and leverages Google Play decoy apps to distribute updates from C2 servers. #Anatsa #TeaBot

CYFIRMA reports an APT36 campaign using weaponized .desktop shortcut files to deliver GO-written ELF payloads targeting BOSS Linux systems, enabling covert download, execution, persistence, and C2 communication with domains like securestore[.]cv and modgovindia[.]space. The operation leverages spear-phishing archives and tailored delivery to Indian government targets, resulting in data exfiltration and persistent access. #APT36 #securestore.cv #modgovindia.space

Attackers are distributing Proxyware installers via fake YouTube video downloader pages that deliver a downloader disguised as WinMemoryCleaner which ultimately installs various Proxyware clients (DigitalPulse, HoneyGain, Infatica). The infection chain uses a PowerShell-driven Node.js JavaScript payload scheduled as recurring tasks to fetch and install Proxyware, exfiltrate basic host info to C&C,…
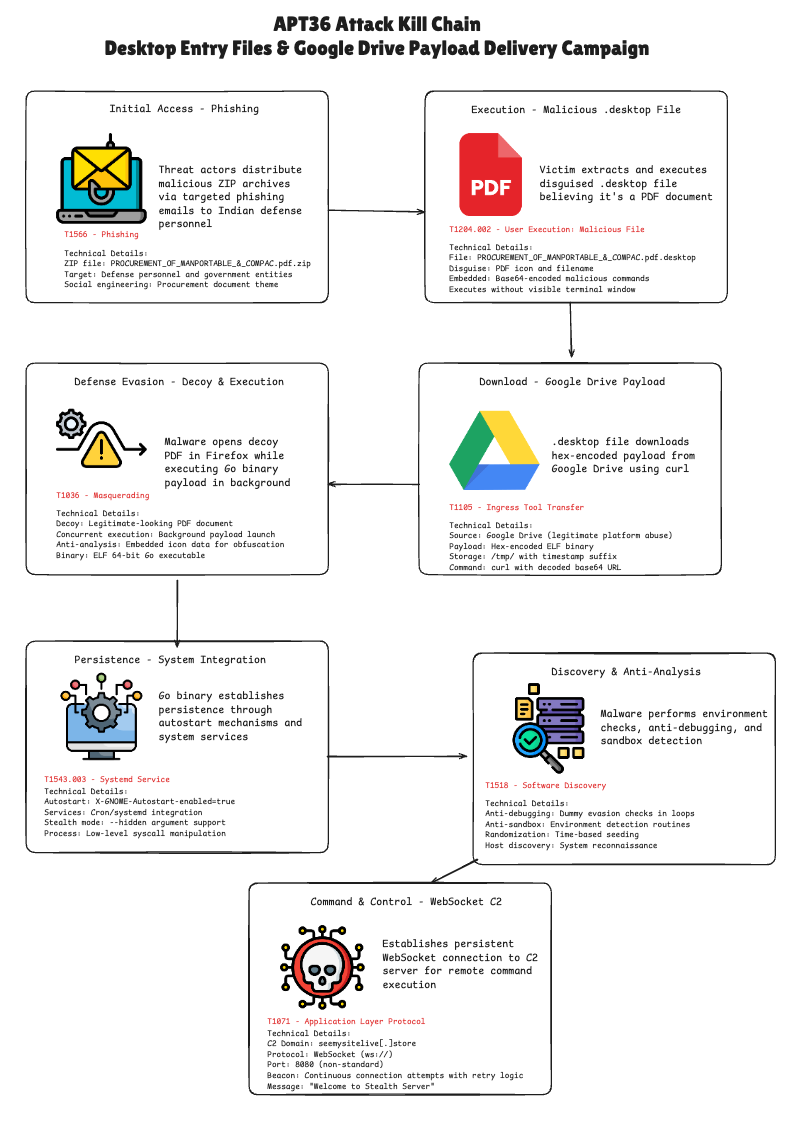
APT36 used a malicious Linux .desktop file inside a ZIP attachment to download and execute a Go-based dropper from Google Drive, then open a decoy PDF in Firefox to mask the compromise. The dropper performs anti-analysis checks, establishes persistence, and attempts WebSocket C2 connections to ws://seemysitelive.store:8080/ws. #APT36 #seemysitelive.store
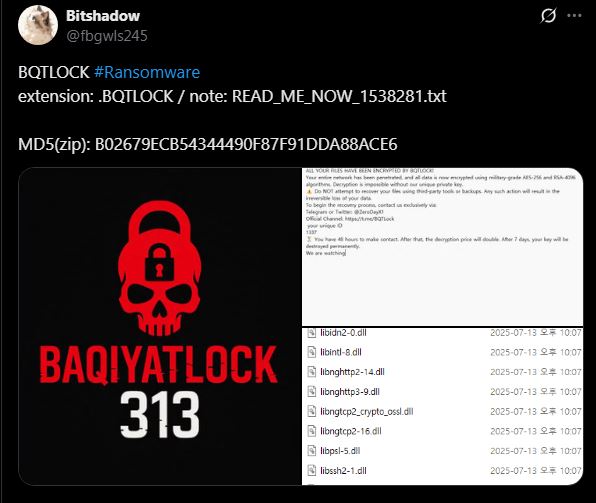
Bqtlock is a newly observed Ransomware-as-a-Service (RaaS) strain linked to the actor “ZerodayX” that uses anti-analysis techniques, process hollowing, privilege escalation, scheduled-task persistence, and double-extortion tactics while demanding Monero payments. The operator markets builder/subscription services with customizable options and has released an updated variant adding UAC bypasses, credential theft from browsers, stronger obfuscation, and expanded exfiltration via Discord webhooks. #Bqtlock #ZerodayX
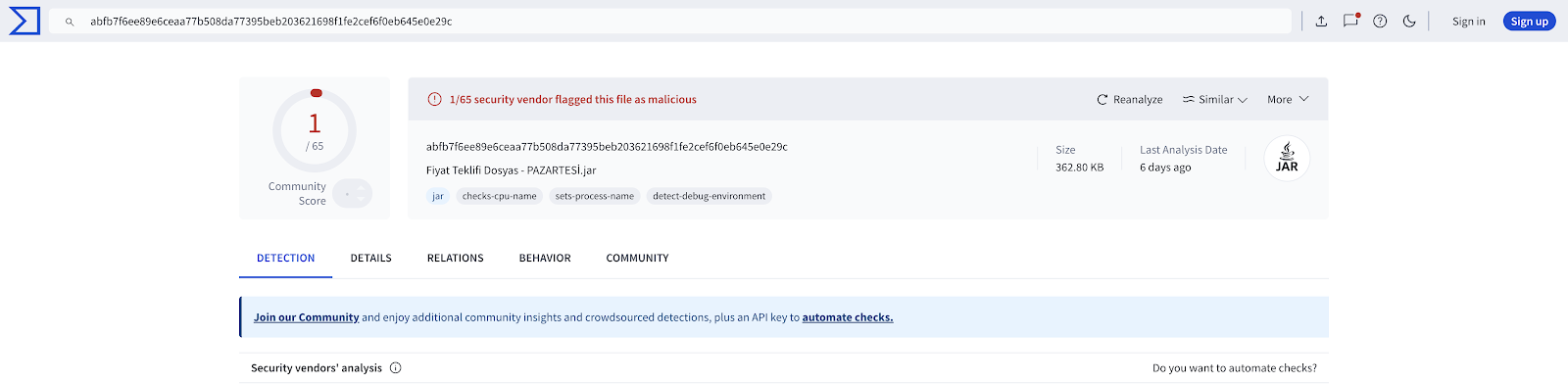
A multi-stage Java-based botnet loader targeting Turkish Windows users employs heavy obfuscation, sandbox evasion, TOR-based C2, advanced persistence, and a wide range of remote-control capabilities that impacted banks, ISPs, and mid-level organizations. The sample bypassed all public sandboxes and antivirus products except Threat.Zone and evaded EDR/XDR in real incidents, underscoring the…
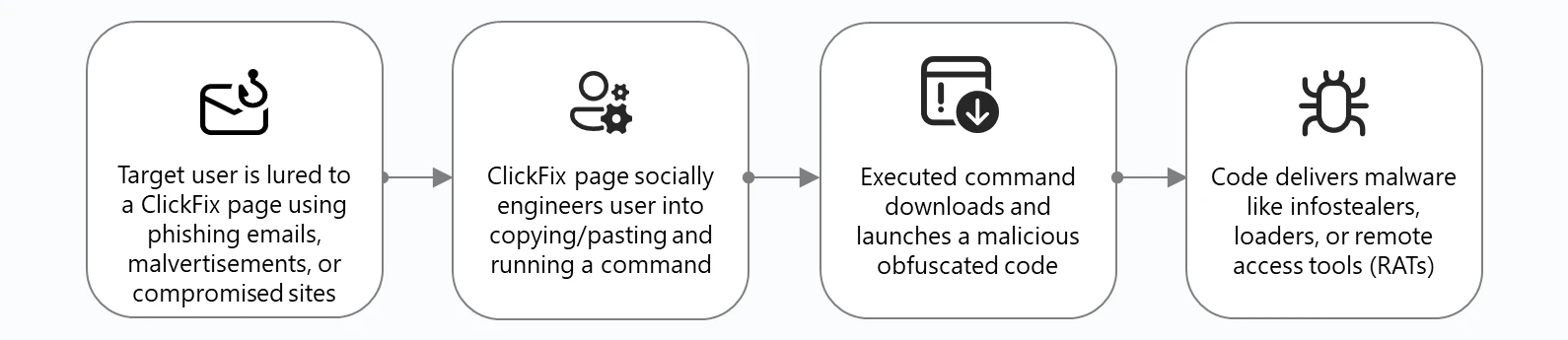
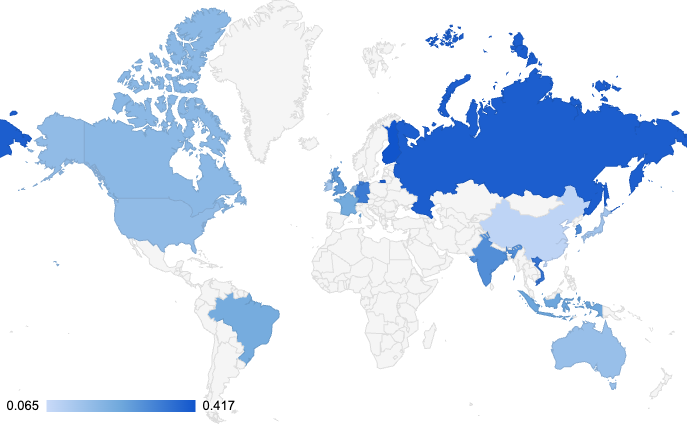
ClickFix is a social-engineering technique that tricks users into copying, pasting, and executing malicious commands (via Run, PowerShell, Terminal, etc.) to deliver in-memory loaders, infostealers, RATs, and rootkits across Windows and macOS. Microsoft observed widespread campaigns delivering payloads such as Lumma Stealer, Lampion, MintsLoader, Latrodectus, and AMOS and recommends user education, device hardening, and Defender XDR protections. #LummaStealer #Lampion
TA-NATALSTATUS is a long-running cryptojacking threat actor that exploits unauthenticated Redis instances to gain root via legitimate Redis commands, then deploys a modular infection chain that hides, persists, and propagates across thousands of exposed servers globally. Their toolkit includes rootkit-style process hijacking, command obfuscation, immutable file locks, and kill lists to remove rival miners, with confirmed IOCs like SSH key comment uc1, Monero wallet 84nw3…, and domains such as natalstatus.org. #TA-NATALSTATUS #natalstatus.org
