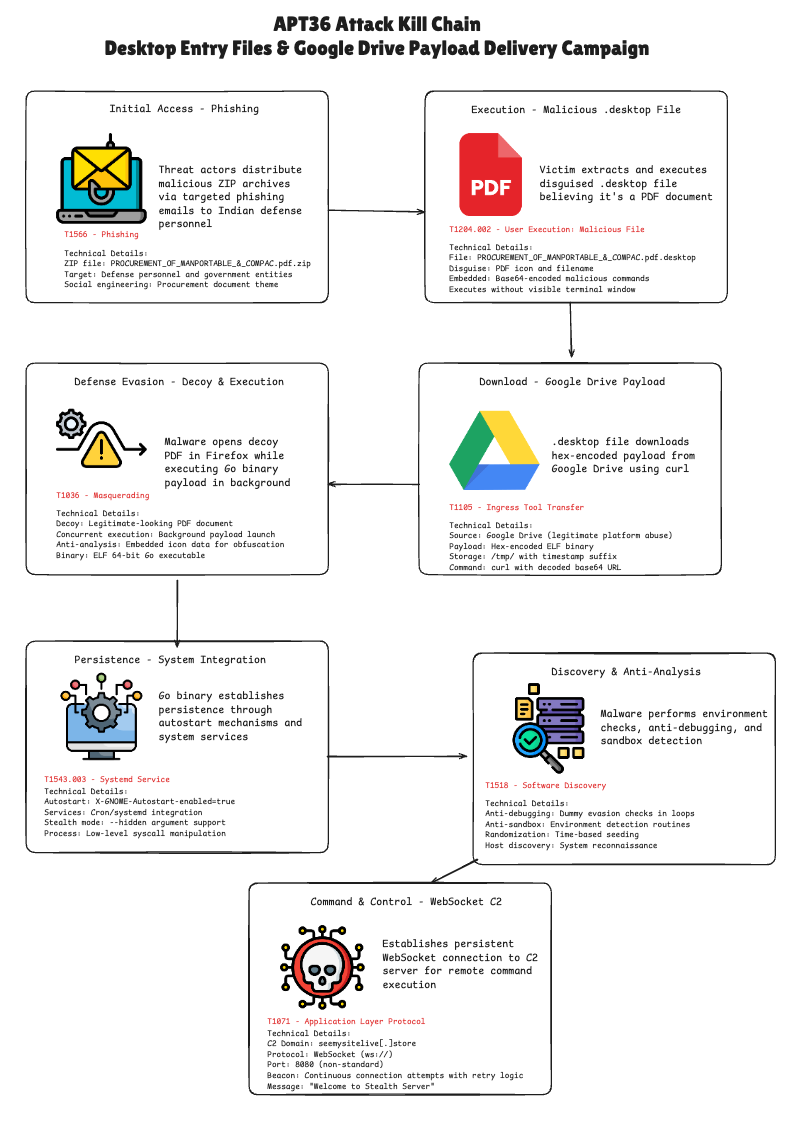
APT36 used a malicious Linux .desktop file inside a ZIP attachment to download and execute a Go-based dropper from Google Drive, then open a decoy PDF in Firefox to mask the compromise. The dropper performs anti-analysis checks, establishes persistence, and attempts WebSocket C2 connections to ws://seemysitelive.store:8080/ws. #APT36 #seemysitelive.store
Keypoints
- APT36 deployed a ZIP attachment (PROCUREMENT_OF_MANPORTABLE_&_COMPAC.pdf.zip) containing a malicious .desktop file that impersonates a PDF shortcut.
- The .desktop file embeds large Base64 icon data and conceals bash commands in the Exec field to fetch a hex-encoded payload from Google Drive and write it to /tmp with a timestamped filename.
- The downloaded payload is an ELF Go binary that includes anti-debugging/anti-sandbox routines, persistence mechanisms, and WebSocket-based C2 beaconing behavior.
- The attack launches the payload silently (Terminal=false) and concurrently opens a decoy PDF in Firefox to reduce user suspicion and maintain stealth.
- Command-and-control infrastructure included the domain seemysitelive[.]store and IP 164.215.103.55, with a WebSocket URL ws://seemysitelive[.]store:8080/ws returning “Welcome to Stealth Server.”
- IOCs include hashes for the ZIP, .desktop, and Go payload, the Google Drive delivery URLs, and file-drop patterns in /tmp; detection and mitigation recommendations include blocking the C2, hunting for suspicious .desktop files, and scanning for the listed hashes.
- The campaign represents an evolution in APT36 targeting Linux environments and procurement-themed spearphishing to access government and defense-related systems.
MITRE Techniques
- [T1566 ] Phishing – Delivery via phishing ZIP attachments containing malicious .desktop files. Quote: ‘Delivery via phishing ZIP attachments containing malicious .desktop files’
- [T1204.002 ] User Execution: Malicious File – Execution of disguised .desktop files by users. Quote: ‘Execution of disguised .desktop files by users’
- [T1064 ] Scripting – Use of bash script commands in the .desktop Exec field to download payload. Quote: ‘Use of bash script commands in the .desktop Exec field to download payload’
- [T1543.003 ] Create or Modify System Process: Systemd Service – Persistence via autostart .desktop files and likely cron/systemd services. Quote: ‘Persistence via autostart .desktop files and likely cron/systemd services’
- [T1564.001 ] Hide Artifacts: Hidden Files and Directories – Dropping payload in hidden /tmp with obfuscation. Quote: ‘Dropping payload in hidden /tmp with obfuscation’
- [T1036 ] Masquerading – Disguising malware as legitimate PDF shortcuts with icon spoofing. Quote: ‘Disguising malware as legitimate PDF shortcuts with icon spoofing’
- [T1027.001 ] Obfuscated Files or Information: Binary Padding – Large base64 icon data to hide malicious commands. Quote: ‘Large base64 icon data to hide malicious commands’
- [T1110 ] Brute Force / Credential Dumping – Credential harvesting focus in broader APT36 operations (campaign context). Quote: ‘Credential harvesting focus in broader APT36 operations’
- [T1518 ] Software Discovery – Reconnaissance on victim environment (host info gathering). Quote: ‘Reconnaissance on victim environment (host info gathering)’
- [T1071 ] Application Layer Protocol – Using WebSocket protocol for C2 communications. Quote: ‘Using WebSocket protocol for C2 communications’
- [T1095 ] Non-Application Layer Protocol – WebSocket is a non-standard C2 communication. Quote: ‘WebSocket is a non-standard C2 communication’
- [T1105 ] Ingress Tool Transfer – Downloading payload from Google Drive. Quote: ‘Downloading payload from Google Drive’
- [T1571 ] Non-Standard Port – C2 over uncommon port 8080 using WebSocket. Quote: ‘C2 over uncommon port 8080 using WebSocket’
Indicators of Compromise
- [File Hashes ] Malicious ZIP archive – PROCUREMENT_OF_MANPORTABLE_&_COMPAC.pdf.zip MD5: 6ac0fe0fa5d9af8193610d710a7da63c, SHA256: 34ad45374d5f5059cad65e7057ec0f3e468f00234be7c34de033093efc4dd83d
- [File Hashes ] Malicious .desktop file – PROCUREMENT_OF_MANPORTABLE_&_COMPAC.pdf.desktop MD5: a484f85d132609a4a6b5ed65ece7d331, SHA256: 6347f46d77a47b90789a1209b8f573b2529a6084f858a27d977bf23ee8a79113
- [File Hashes ] Go binary payload – dropped ELF executable MD5: 566ddd4eb4ca8d4dd67b72ee7f944055, SHA256: 7a946339439eb678316a124b8d700b21de919c81ee5bef33e8cb848b7183927b
- [Domain/IP ] C2 infrastructure – seemysitelive[.]store, IP 164.215.103.55 (ASN: AS213373); WebSocket URL ws://seemysitelive[.]store:8080/ws returning “Welcome to Stealth Server”
- [URLs ] Payload delivery / decoy – Google Drive download pattern: https://drive.google.com/uc?export=download&id=1VQQiTt78N3KpYJzVbE-95uILnO84Wz_- , decoy view URL https://drive.google.com/file/d/1kn0L_6WYbfUUx0dmzwfALDnzkVHJAPTu/view?usp=drive_link
- [File Paths ] Payload drop locations – /tmp/PROCUREMENT_OF_MANPORTABLE_&_COMPAC.pdf-[TIMESTAMP] (example: /tmp/PROCUREMENT_OF_MANPORTABLE_&_COMPAC.pdf-1692547200) with executable permissions