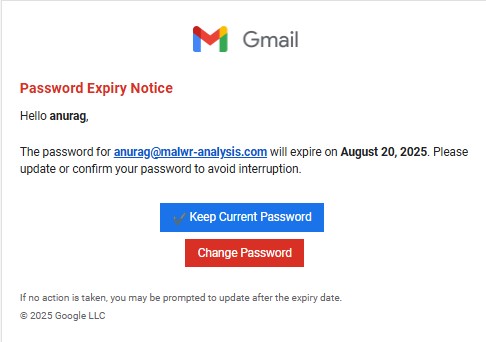
Attackers sent a Gmail-themed credential-harvesting phishing email that included a hidden prompt-injection block in the plain-text MIME section designed to distract or manipulate AI-based defensive tools. The campaign used SendGrid delivery, a Dynamics staging redirect, captcha-gated phishing pages, obfuscated multi-stage JavaScript, and telemetry calls to profile victims. #SendGrid #bwdpp.horkyrown.com
Keypoints
- The phishing email impersonated Gmail with a “Login Expiry Notice” lure and urgency to harvest credentials.
- A hidden, Grok/GPT-style prompt injection block was embedded in the email’s plain-text MIME to target AI analysis workflows.
- Delivery used SendGrid (SPF/DKIM pass, DMARC fail), a staging redirect via assets-eur.mkt.dynamics.com, and a captcha-gated front-end at bwdpp.horkyrown.com.
- The phishing site included multi-stage obfuscated JavaScript (AES-CBC encrypted stage, eval(atob(…)), then a decrypted payload) implementing a managed Gmail-like login and 2FA flows to capture inputs and prolong interaction.
- Telemetry and profiling calls were observed (get.geojs.io for GeoIP; 6fwwke.glatrcisfx.ru seen as a beacon), used to fingerprint users and avoid analysis environments.
- Prompt injection aims to distract or override automated AI triage, potentially causing delayed classification, false negatives, and noise in SOC automation.
- Soft attribution signals (registrant WHOIS, URL path words like “tamatar”) suggest possible South Asian ties, but attribution remains tentative.
MITRE Techniques
- [T1071] Application Layer Protocol – Phishing delivery via email and web redirects using SendGrid and Dynamics staging redirect (“…originated via SendGrid…abused Microsoft Dynamics to make the first hop appear trustworthy…”).
- [T1566.001] Phishing: Spearphishing Attachment/Link – Credential-harvesting site with Gmail-themed login pages and social-engineering subject/body (“Login Expiry Notice…urging the recipient to update or confirm their credentials”).
- [T1176] Browser Extensions (or T1204?) – Use of obfuscated JavaScript and multi-stage loaders (AES-CBC encrypted payload then eval(atob(…))) to execute in the victim’s browser (“AES-CBC encrypted payload, decrypted via CryptoJS…Output wrapped in eval(atob(…)).”).
- [T1078] Valid Accounts (Credential Harvesting) – Fake login pages designed to collect credentials and 2FA inputs (“Gmail-themed login page…Validated password and 2FA inputs, showing fake errors to prolong interaction.”).
- [T1562] Impair Defenses (Sub-technique: Disable or Modify Tools) – Prompt-injection block targeted at AI-based defenses to cause long reasoning loops and misclassification (“…hidden AI prompts inside the email designed to confuse automated analysis…If an AI model ingests this raw email, it may get distracted into long reasoning loops instead of labelling it as phishing.”).
- [T1070.004] Indicator Removal on Host – CAPTCHA gating and geo/fingerprint checks to evade automated analysis/sandboxes (“Captcha blocks automated crawlers and sandboxes…GeoIP Request collects victim IP, ASN, and geolocation useful for profiling users and filtering out analysis environments.”).
- [T1588] Obtain Capabilities (Phishing Kit / Infrastructure) – Use of attacker-controlled domains, obfuscation, captcha gating and telemetry (bwdpp.horkyrown.com, glatrcisfx.ru) to host and operate the phishing kit (“phishing front-end + captcha…telemetry / beacon”).
Indicators of Compromise
- [Email Artifact] phishing email metadata – From: Alert [email protected]; Subject: “Login Expiry Notice 8/20/2025 4:56:21 p.m.”; Via/Mailed-By/Signed-By: sendgrid.net
- [Domain] staging redirect and phishing host – assets-eur.mkt.dynamics.com (staging redirect), bwdpp.horkyrown.com (phishing front-end + captcha)
- [Domain / Beacon] telemetry/collector – 6fwwke.glatrcisfx.ru (observed GET /tamatar@1068ey as a likely beacon)
- [Service] GeoIP profiling endpoint – get.geojs.io (v1/ip/geo.json used to collect victim IP/ASN/geo)
- [HTTP Request] suspicious request examples – GET hxxps://6fwwke.glatrcisfx.ru/tamatar@1068ey (beacon), GET hxxps://get.geojs.io/v1/ip/geo.json (GeoIP)
Read more: https://malwr-analysis.com/2025/08/24/phishing-emails-are-now-aimed-at-users-and-ai-defenses