A SQL injection vulnerability in Anthropic’s reference Postgres MCP server allowed attackers to terminate the read-only transaction (via stacked statements like “COMMIT;”) and execute arbitrary write statements such as “DROP SCHEMA public CASCADE”. The issue is patched in Zed Industries’ fork @zeddotdev/postgres-context-server v0.1.4 and an unreleased reference fix; affected packages remain archived but still widely downloaded. #COMMIT #DROP_SCHEMA
Category: Threat Research

Socket Threat Research uncovered a malicious Go module, golang-random-ip-ssh-bruteforce, that pretends to be an SSH brute-forcing tool but exfiltrates first-successful credentials to a hardcoded Telegram bot controlled by the actor IllDieAnyway. The package continuously scans random IPv4 addresses for SSH, attempts logins from an embedded wordlist, disables host key verification, and sends ip:user:pass to @sshZXC_bot which forwards to @io_ping. #golang-random-ip-ssh-bruteforce #IllDieAnyway
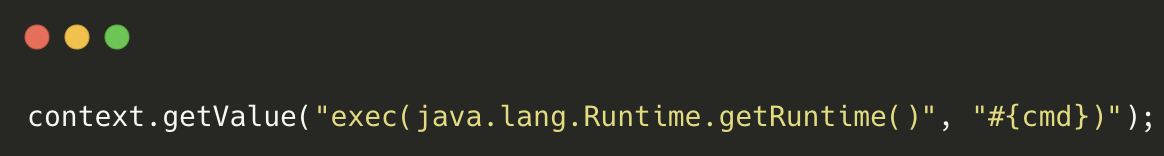
Attackers have been exploiting CVE-2024-36401 in GeoServer to achieve remote code execution and deploy legitimate SDKs or apps that silently monetize victims’ internet bandwidth as residential proxies. The campaign uses multiple distribution hosts and pivots infrastructure to evade detection while delivering payloads (examples: 37.187.74[.]75, 64.226.112[.]52) and abusing SDKs/apps designated e193, z593,…

IBM X-Force observed a new loader named QuirkyLoader since November 2024 used to deliver multiple known malware families via multi-stage email-based attacks. The actor employs DLL side-loading with a .NET-written, AOT-compiled loader that decrypts and injects final payloads into target processes. #QuirkyLoader #DLLSideLoading…
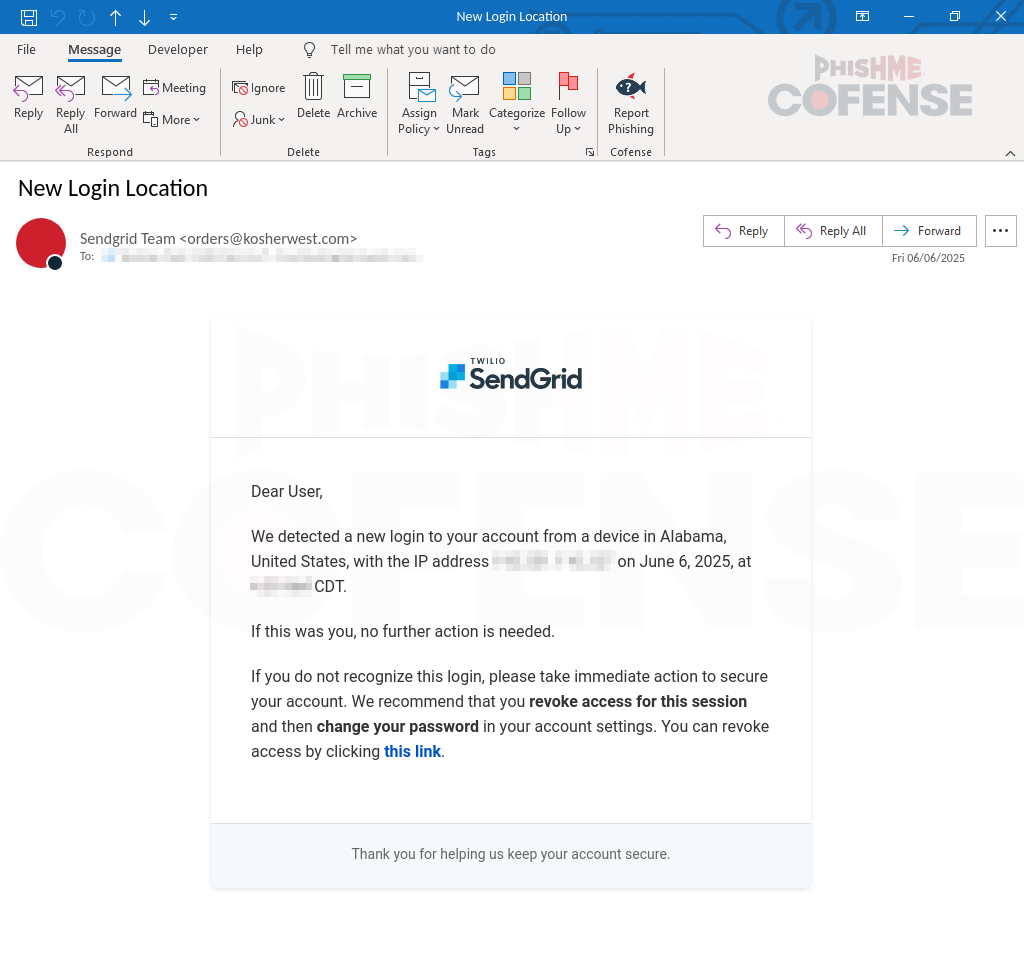
Cofense PDC observed a SendGrid-themed credential harvesting campaign using spoofed sender addresses, three urgency-themed phishing emails, and open-redirect links to lure users to fake SendGrid login pages. The attacks redirect through domains like destinpropertyexpert[.]com and hilllogistics[.]com to landing pages such as loginportalsg[.]com and sendgrid.aws-us5[.]com to capture credentials. #loginportalsg #destinpropertyexpert
The author investigated whether a low-privileged remote user can start the WebClient service to enable targeted NTLM relay and found multiple programmatic and indirect methods (ETW event, net.exe, explorer, searchConnector.ms) all funnel to davclnt.dll triggering an ETW event that ultimately starts the service. The final blocker is the UBPM ETW consumer…

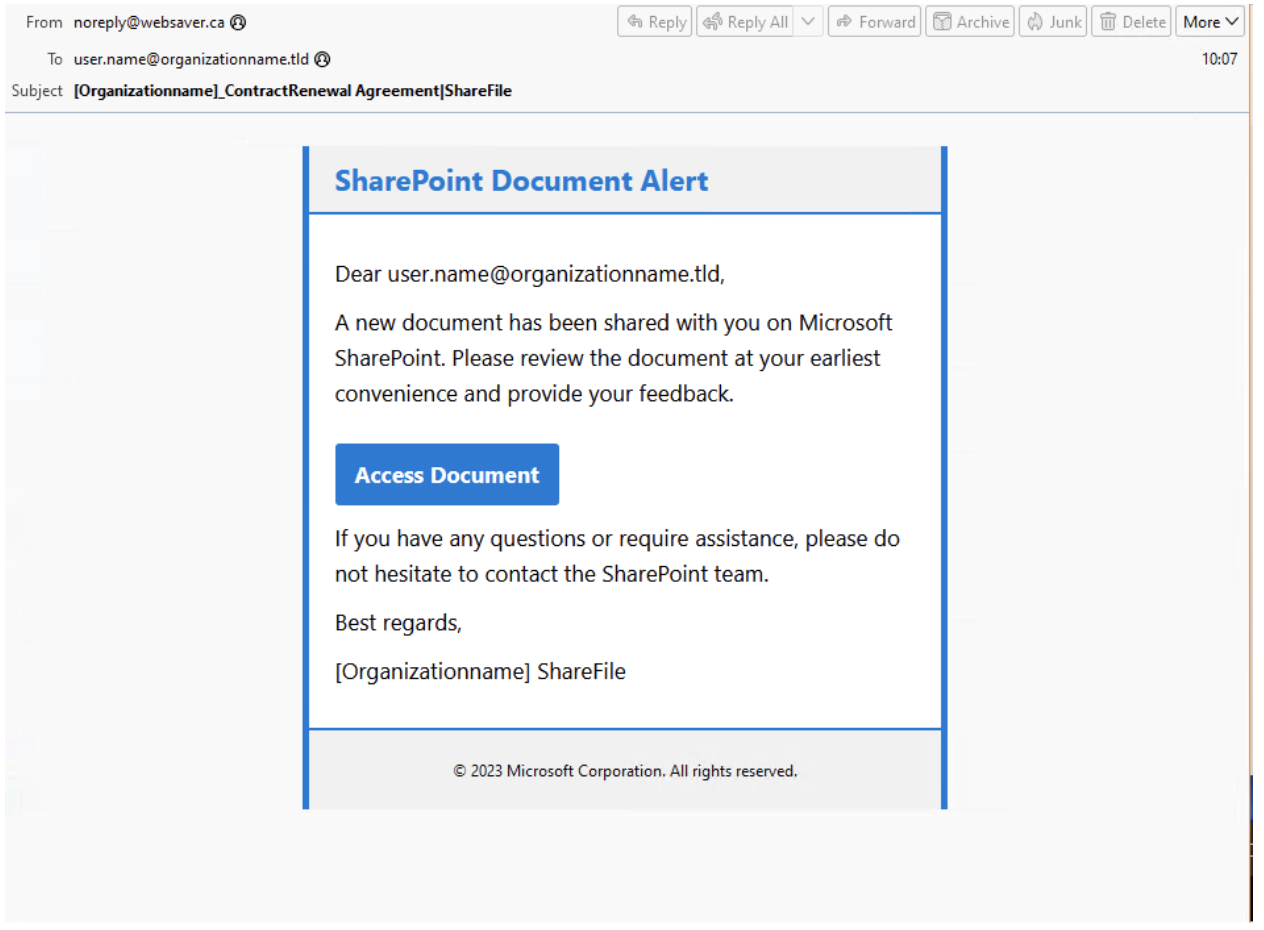
Mandiant observed UNC5518 using compromised websites and ClickFix fake CAPTCHA lures to trick users into executing PowerShell droppers that install CORNFLAKE.V3, which UNC5774 uses as a backdoor to retrieve and execute additional payloads. The CORNFLAKE.V3 family (Node.js and PHP variants) supports multiple payload types, persistence via Run registry keys, Active Directory…

Between June and August 2025, COOKIE SPIDER’s SHAMOS (an AMOS variant) was distributed via malvertising and malicious one-line installation commands to target macOS users across many countries, with CrowdStrike Falcon blocking attempts to compromise over 300 customer environments. The campaign used Base64-obfuscated URLs and Bash scripts to bypass Gatekeeper, capture credentials…
Cybercriminals are abusing the Lovable AI website builder to create fraudulent sites for credential phishing, MFA/AiTM attacks, crypto wallet drainers, and malware delivery, often using CAPTCHA filters and posting stolen data to Telegram. Proofpoint observed tens of thousands of Lovable URLs in email campaigns (Feb–Jul 2025) and reported findings to Lovable,…

DBatLoader is a Delphi-compiled Windows x86 malware that uses heavy obfuscation, import hiding, anti-analysis checks, and persistence techniques to conduct stealthy surveillance and potential data exfiltration. The sample demonstrates capabilities including registry manipulation, screenshot capture, code injection, debugger/sandbox detection, and possible keylogging while blending into enterprise Delphi application ecosystems. #DBatLoader #Delphi
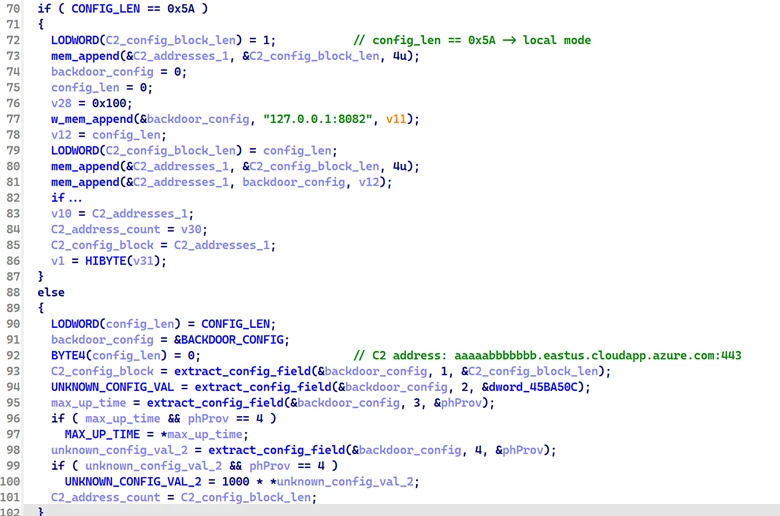
Microsoft observed a modular backdoor named PipeMagic, attributed to financially motivated threat actor Storm-2460, masquerading as a trojanized ChatGPT Desktop Application and used in attack chains exploiting CVE-2025-29824 to deploy ransomware. The malware uses named-pipe encrypted IPC, in-memory modules (network, execute, payload, unknown linked lists), and a TCP-based C2 hosted at aaaaabbbbbbb.eastus.cloudapp.azure[.]com to manage and execute payloads. #PipeMagic #Storm-2460 #CVE-2025-29824
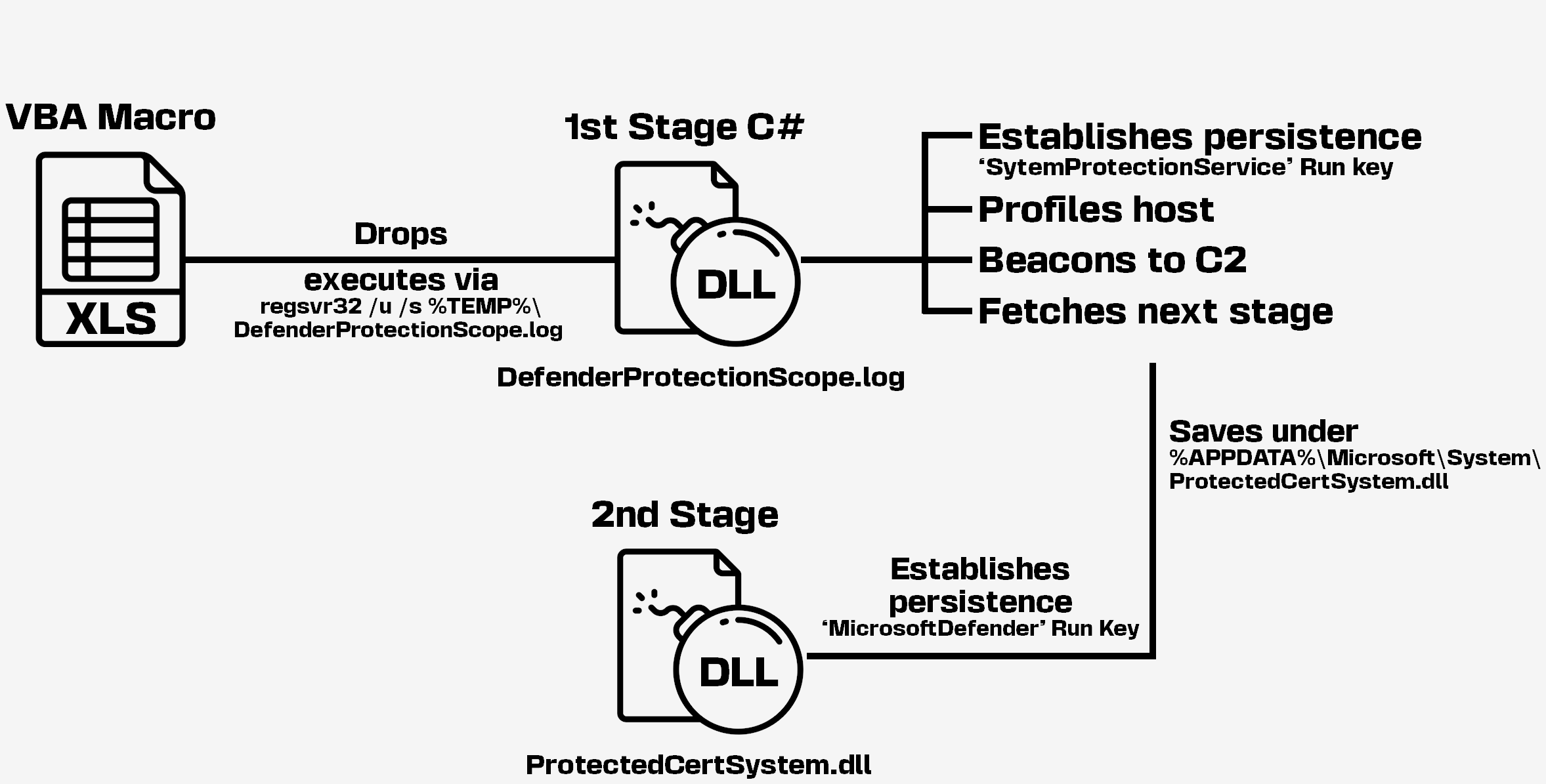
Two clusters of weaponized archives (XLS with obfuscated VBA) delivered between April and July 2025 targeted Ukraine and Poland, dropping first-stage DLL implants that collect system information and retrieve next-stage payloads from web-based C2 infrastructure. The activity shows tool, code, and infrastructure overlaps consistent with previously reported UAC-0057/UNC1151 (FrostyNeighbor/Ghostwriter) operations, using…

Static Tundra is a Russian state-sponsored espionage group linked to the FSB’s Center 16 that has for over a decade exploited Cisco Smart Install (CVE-2018-0171) and unpatched/end-of-life devices to steal configurations and maintain long-term access using implants like SYNful Knock and bespoke SNMP tooling. The group primarily targets telecommunications, higher education…

Insikt Group analyzed a sprawling Lumma infostealer affiliate ecosystem, finding affiliates use multiple MaaS families (Lumma, Vidar, Stealc, Meduza) and a wide range of operational enablers such as proxy/VPN services, anti-detect browsers, crypting/exploit services, and underground forums to run parallel scams and monetize stolen data. The report includes new tooling (cracked EMAIL SOFTWARE 1.4.0.9, DONUSSEF), IoCs (Lumma sample hash, Ngioweb IPs, C2 panels), and recommends defenders monitor exfiltration, deploy YARA/Sigma/Snort detections, and track underground forums. #Lumma #Vidar #MeduzaStealer
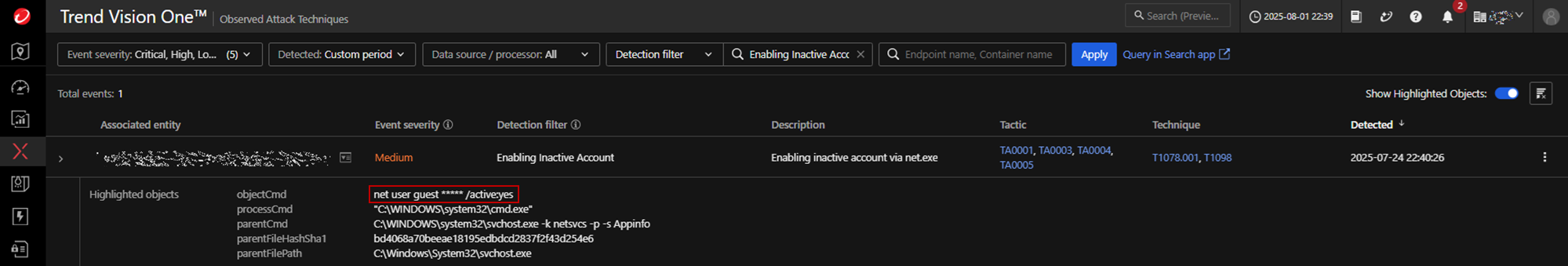
Warlock ransomware exploited unpatched, internet-facing Microsoft SharePoint servers to upload web shells, achieve remote code execution, escalate privileges, and perform extensive credential theft and lateral movement before deploying ransomware that appends .x2anylock and exfiltrates data via RClone. Trend observed use of tools like Mimikatz, renamed Cloudflare tunneling binaries, and a KillAV…
