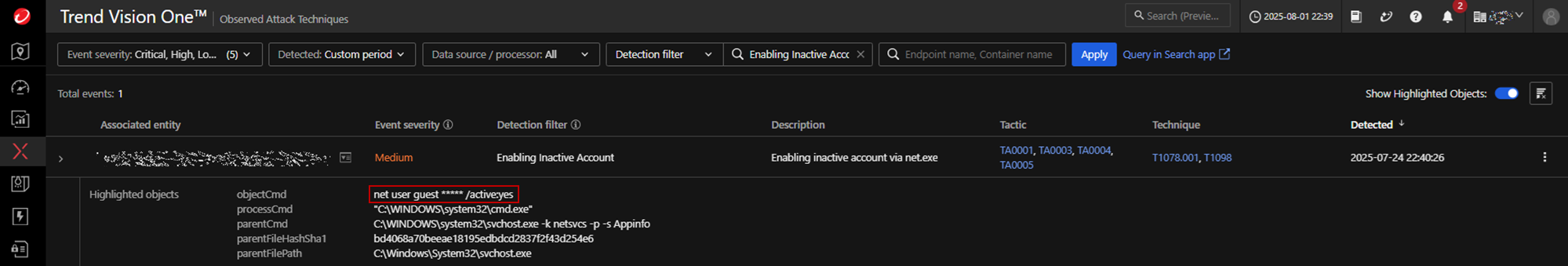
Warlock ransomware exploited unpatched, internet-facing Microsoft SharePoint servers to upload web shells, achieve remote code execution, escalate privileges, and perform extensive credential theft and lateral movement before deploying ransomware that appends .x2anylock and exfiltrates data via RClone. Trend observed use of tools like Mimikatz, renamed Cloudflare tunneling binaries, and a KillAV…
Category: Threat Research

Datadog Security Research discovered that the AWS API resource-explorer-2:ListResources could be used by attackers to quietly enumerate resources because it was logged as a data event and not recorded in CloudTrail by default. After disclosure, AWS reclassified ListResources as a management event to ensure it is logged to CloudTrail by default. #ResourceExplorer #ListResources
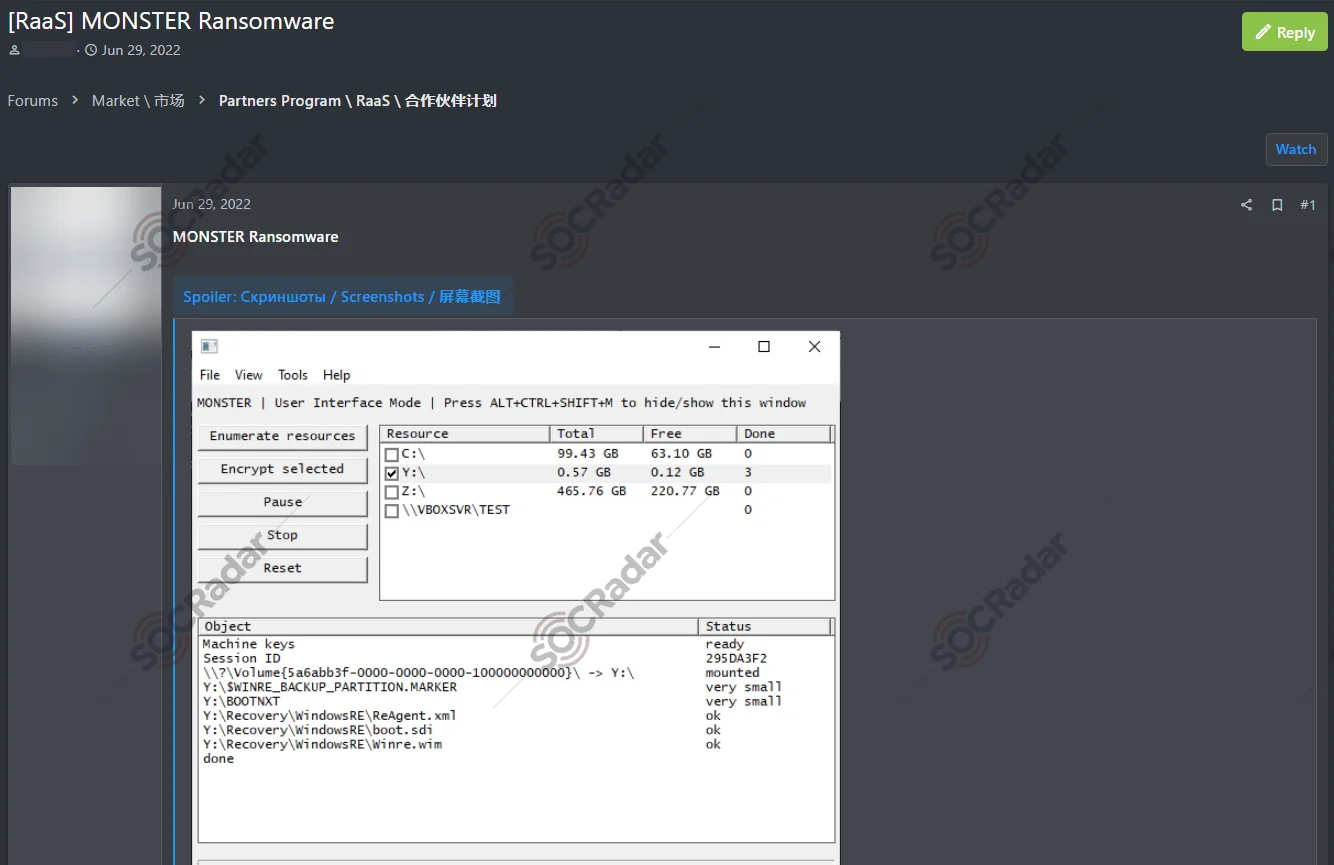
Beast is an evolved Ransomware-as-a-Service originally derived from Monster (first seen March 2022) that now targets Windows, Linux, and VMware ESXi with stronger encryption, multi-threading, service termination, shadow-copy deletion, and a TOR-hosted data leak site. A related variant, Boramae, shares near-identical code with advanced obfuscation and OpenSSL static linking, and Beast’s victims are concentrated in the United States across industries like Manufacturing and Construction. #Beast #Boramae

Knownsec 404 discovered Silver Fox campaigns impersonating common tools (Google Translate, WPS, translation apps, browsers, VPNs) that use fake flash prompts and counterfeit download pages to trick users into running MSI/EXE installers which deploy the Winos remote-access Trojan. The Silver Fox family is modular and widely reused by cybercriminals and APTs (e.g., Golden Eye Dog), using obfuscation and sandbox evasion to persist and steal data. #SilverFox #Winos #GoldenEyeDog
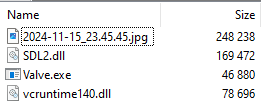
In September 2024, threat actors distributed malicious .scr and .pif files via Skype targeting financial firms to deliver a new Gh0st RAT–based backdoor named GodRAT that uses steganography to hide shellcode in images and downloads the RAT from C2 servers. GodRAT installs plugins (FileManager), deploys Chrome/MS Edge password stealers, and is accompanied by AsyncRAT, with artifacts and behavior linking it to AwesomePuppet and likely Winnti APT activity. #GodRAT #AwesomePuppet #Winnti
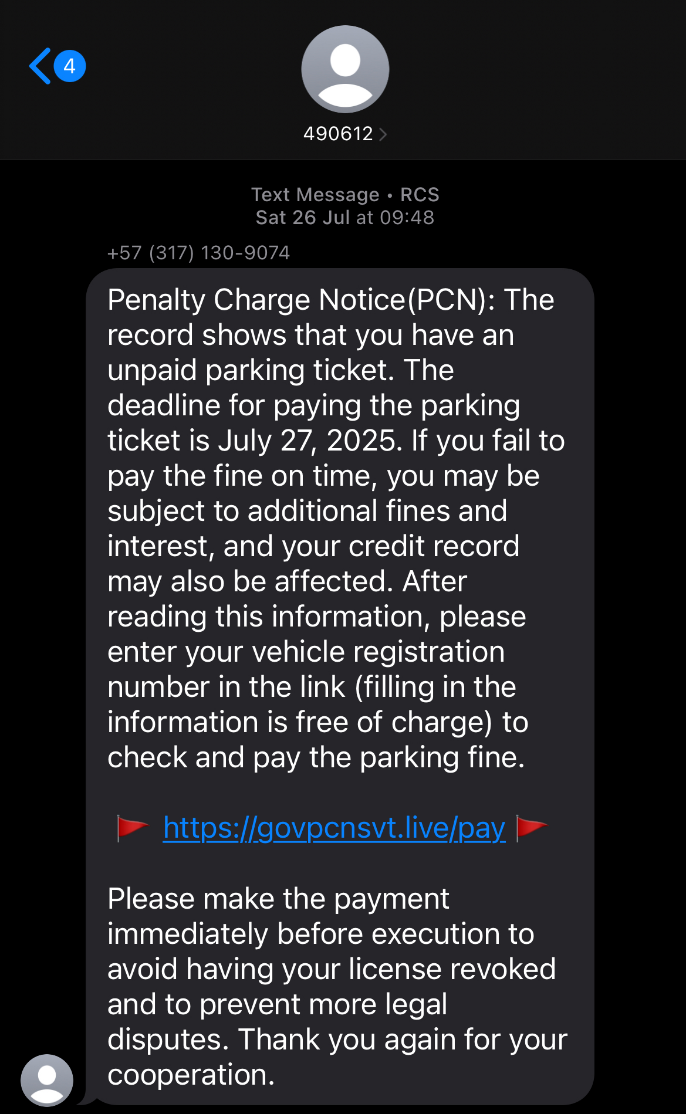
A transient smishing campaign impersonating UK government and local authority services used hundreds of short-lived, lookalike domains (many on Cloudflare and Dominet registrar) to host parking fine and winter fuel payment lures that only serve content at specific paths like /pay, /bills, or /index.html. Investigators pivoted on a distinctive HTTP header-hash (e4d0cf4f3dc9a95493a2) and observed AJAX /api token issuance and websocket (/ws) exfiltration behavior across multiple domains. #govpcnsvt #e4d0cf4f3dc9a95493a2

In July 2025, AhnLab reported an increase in ransomware activity including a major attack on Korea’s largest financial institution and the rise of new groups such as BEAST, Payouts King, D4rk4rmy, and Sinobi. The report provides trend statistics on ransomware detections, targeted companies from leak sites, and industry/region impacts collected by…
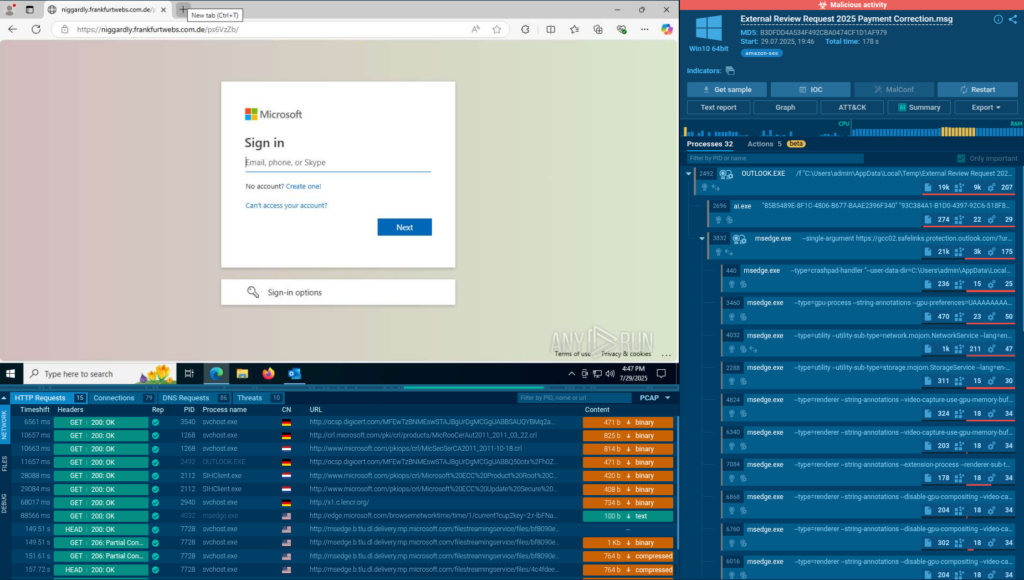
Salty 2FA is a newly identified Phishing-as-a-Service framework that uses multi-stage obfuscated JavaScript, a distinct domain pattern combining .??.com compound domains with .ru infrastructure, and behavioral techniques to steal Microsoft 365 credentials and bypass multiple 2FA methods. Analysis mapped its execution chain, evasion methods, and wide-ranging targets, with notable examples including…
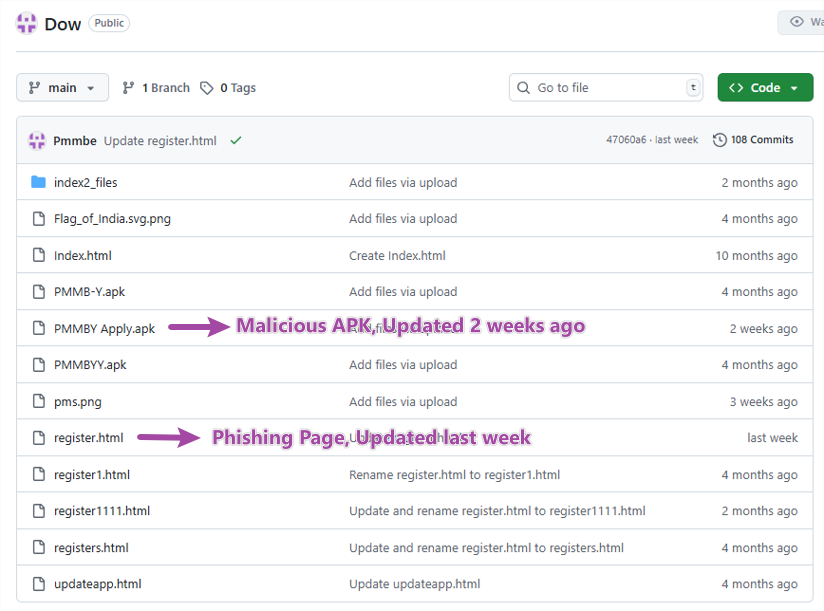
An Android phishing campaign impersonating an Indian government electricity subsidy scheme lures victims via YouTube and a GitHub-hosted phishing site to install a malicious APK that steals UPI credentials, SMS messages, and contact data while enabling remote control via Firebase. McAfee reported the apps and repository to Google and GitHub, leading…
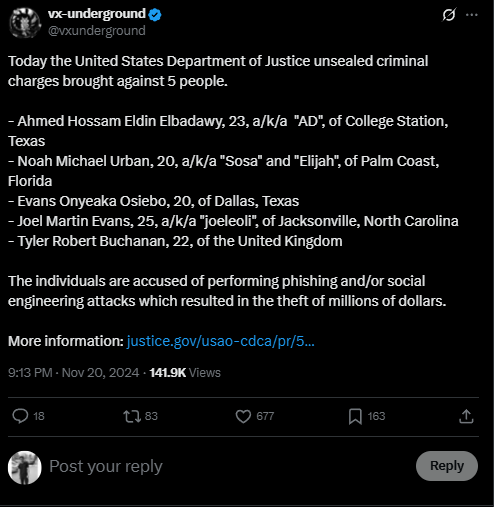
Scattered Spider (UNC3944) is a financially motivated, adaptive cybercriminal group active since at least May 2022, using sophisticated social engineering, phishing kits (including Evilginx), and diverse hosting strategies to target high-value sectors like retail, finance, and entertainment. Recent activity includes disruptive 2025 UK retailer attacks, a fifth-generation phishing kit mimicking Okta portals, and a noisy August 2025 Telegram channel blending Scattered Spider, LAPSUS$, and ShinyHunters personas. #ScatteredSpider #Evilginx
Microsoft patched 121 vulnerabilities in April 2025, with CVE-2025-29824 actively exploited by the PipeMagic backdoor observed in campaigns since 2022 and resurfacing in 2024–2025 targeting Saudi Arabia and Brazil. The malware uses varied loaders (trojanized Rufus, fake ChatGPT Rust/Tauri apps, .mshi msbuild loaders, and DLL hijacking), named pipes and 127.0.0.1:8082 for communication, and modules for injection, I/O, and bypassing AMSI to enable credential theft and lateral movement. #PipeMagic #CVE-2025-29824

ReasonLabs identified a long-running polymorphic trojan campaign that force-installs malicious Chrome and Edge extensions by using fake installer sites, scheduled PowerShell tasks, registry policies, shortcut tampering, and DLL patching to hijack searches and persist. Over 300,000 users were impacted across Chrome and Edge with extensions such as Custom Search Bar, Micro Search, yglSearch, and Simple New Tab, while indicators include domains like wincloudservice[.]com and securedatacorner[.]com and signer Tommy Tech LTD. #CustomSearchBar #wincloudservice

Researchers discovered Plague, a novel Linux backdoor that masquerades as a PAM library (e.g., libselinux.so.8) to provide persistent, stealthy SSH access and authentication bypass. The implant uses layered string obfuscation, antidebug/environment checks, and session artifact removal to evade detection and persist across updates. #Plague #libselinux.so.8
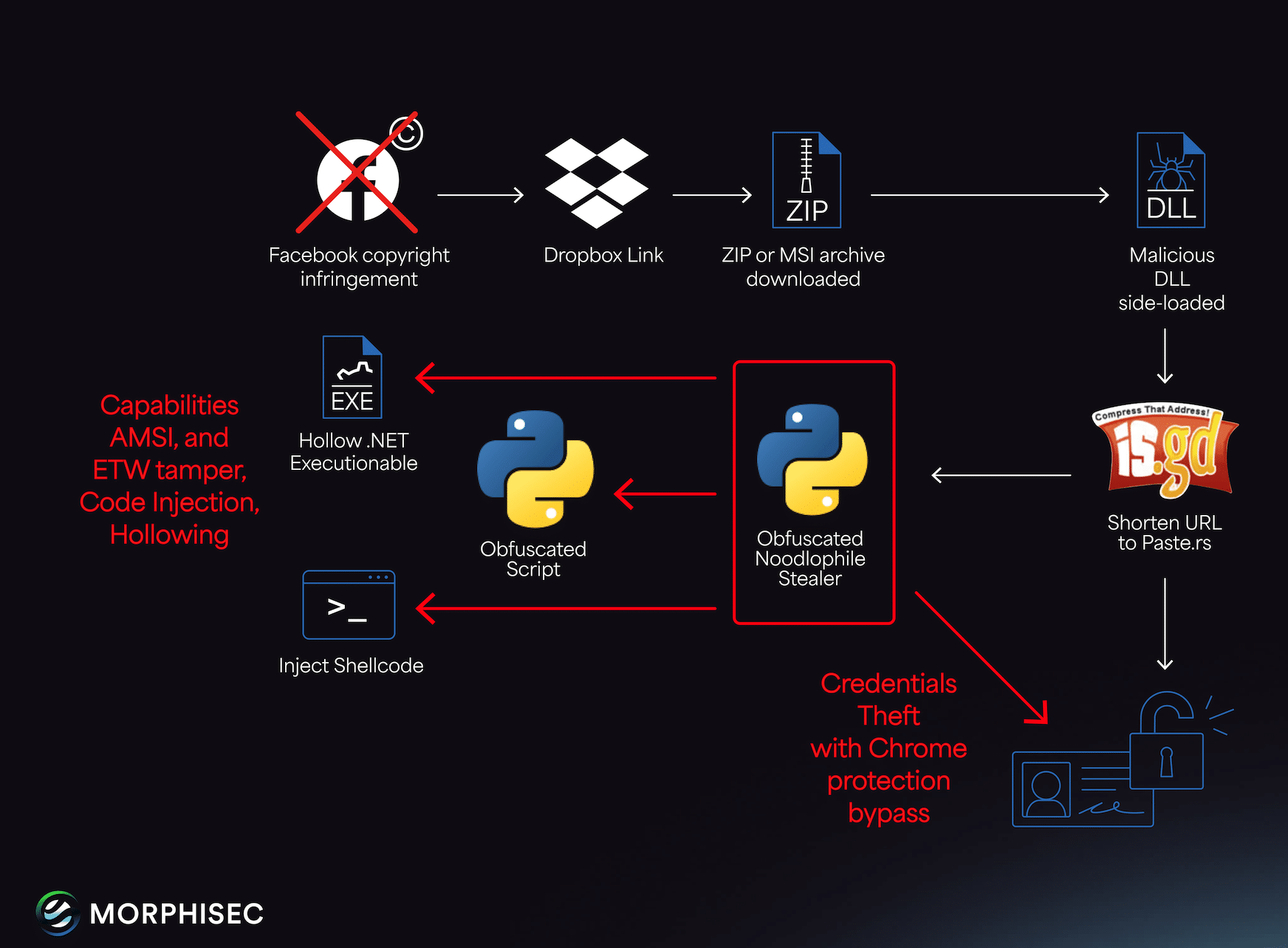
The Noodlophile Stealer campaign has evolved from fake AI video platform lures into a targeted, multilingual spear-phishing operation that exploits enterprises with large Facebook footprints using copyright-infringement-themed emails. Attackers now use legitimate signed applications and DLL side‑loading, Telegram-based staging, and enhanced obfuscation to deliver a stealer focused on browser data and cookies (notably Facebook cookies). #Noodlophile #Facebook
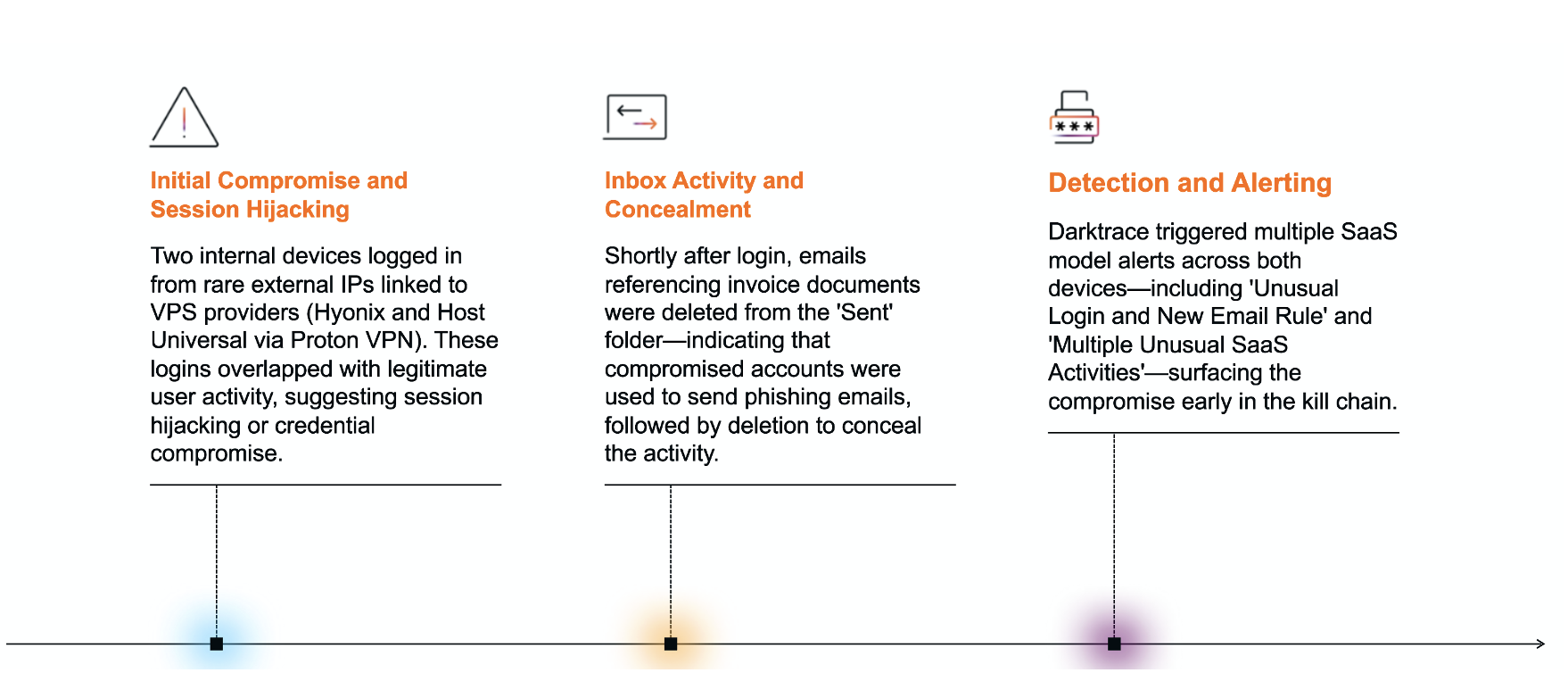
Threat actors increasingly abuse VPS providers (e.g., Hyonix, Host Universal, Mevspace, Hivelocity) to conduct SaaS-targeted campaigns—enabling stealthy logins, inbox rule manipulation, email deletion, and phishing while evading geolocation and IP-reputation defenses. Darktrace observed coordinated compromises across customers involving rare VPS IP logins, MFA bypasses or token claims, obfuscated email rules, and domain fluxing leading to spam/outbound phishing. #Hyonix #HostUniversal