In September 2024, threat actors distributed malicious .scr and .pif files via Skype targeting financial firms to deliver a new Gh0st RAT–based backdoor named GodRAT that uses steganography to hide shellcode in images and downloads the RAT from C2 servers. GodRAT installs plugins (FileManager), deploys Chrome/MS Edge password stealers, and is accompanied by AsyncRAT, with artifacts and behavior linking it to AwesomePuppet and likely Winnti APT activity. #GodRAT #AwesomePuppet #Winnti
Keypoints
- Attackers distributed malicious .scr and .pif files masquerading as financial documents via Skype to target trading and brokerage firms.
- New RAT named GodRAT, based on Gh0st RAT, was delivered via shellcode loaders that either embed shellcode or extract it from steganographically-modified images.
- GodRAT supports plugins (notably FileManager) and was used to deploy Chrome and Edge password stealers; AsyncRAT was used as a secondary implant for persistence.
- Several loader types create persistence (e.g., registry Run key to launch Valve.exe) and use expired or embedded certificates to appear legitimate.
- GodRAT’s network protocol uses a 15-byte header with compressed, triple-XOR-encoded payloads and supports plugin injection, file operations, process execution, and configuration management.
- Source code and a builder for GodRAT were found online (July 2024), confirming reuse and customization of Gh0st RAT code; GodRAT is likely an evolution of AwesomePuppet linked to Winnti activity.
- Active campaign timeline spans 2024–2025 with detections across Hong Kong, United Arab Emirates, Jordan, Lebanon, and Malaysia; latest detections observed on 2025-08-12.
MITRE Techniques
- [T1140] Deobfuscate/Decode Files or Information – Shellcode and configuration are XOR-decoded and decoded using keys (e.g., “OSEDBIU#IUSBDGKJS…”) to obtain C2 details and next-stage payloads; quoted: ‘XOR-decodes embedded shellcode using the following hardcoded key’.
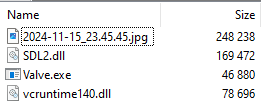
- [T1027] Obfuscated Files or Information – Steganography used to hide shellcode bytes inside image files (e.g., “2024-11-15_23.45.45.jpg”) which loaders extract and execute; quoted: ‘extracts shellcode bytes hidden within an image file “2024-11-15_23.45.45.jpg”‘.
- [T1055] Process Injection – Loaders create a new memory section in another process (e.g., curl.exe or cmd.exe) and write/executed shellcode to run GodRAT inside legitimate processes; quoted: ‘allocates memory, writes the shellcode buffer … and a thread is then created to execute the shellcode’.
- [T1105] Ingress Tool Transfer – The shellcode connects to a C2 and downloads a second-stage UPX-packed GodRAT DLL and bootstrap code; quoted: ‘The shellcode connects to the C2 server and transmits the string “GETGOD.” … the next (second) stage of the shellcode’.
- [T1071] Application Layer Protocol – GodRAT communicates with C2 over TCP using a custom protocol with a 15-byte header and triple-XOR-encoded compressed payloads; quoted: ‘The final data sent to the C2 server includes a 15-byte header followed by the compressed data blob’.
- [T1053] Scheduled Task/Job (persistence via Run key) – Some loaders create a registry Run entry (HKCUSoftwareMicrosoftWindowsCurrentVersionRunMyStartupApp) to persist and launch Valve.exe; quoted: ‘creates a registry load point entry at “HKCUSoftwareMicrosoftWindowsCurrentVersionRunMyStartupApp” that points to the legitimate executable Valve.exe’.
- [T1005] Data from Local System – FileManager and password stealers collect files, drive info, and browser login databases (Chrome/Edge Login Data, Local State) to exfiltrate credentials and file listings; quoted: ‘It looks for Chrome database files with login data … %LOCALAPPDATA%GoogleChromeUser DataDefaultLogin Data’.
- [T1112] Modify Registry – Loader creates registry Run entry for persistence pointing to Valve.exe; quoted: ‘creates a registry load point entry at “HKCUSoftwareMicrosoftWindowsCurrentVersionRunMyStartupApp”‘.
- [T1078] Valid Accounts (use of legitimate signed executables) – Attackers load malicious DLLs via signed legitimate executables like Valve.exe to blend in; quoted: ‘The loader “SDL2.dll” is loaded by the legitimate executable Valve.exe … Both … are signed with an expired digital certificate’.
Indicators of Compromise
- [File Hash] GodRAT shellcode injectors and loaders – cf7100bbb5ceb587f04a1f42939e24ab, d09fd377d8566b9d7a5880649a0192b4, e723258b75fee6fbd8095f0a2ae7e53c
- [File Hash] Plugins and stealers – 8008375eec7550d6d8e0eaf24389cf81 (FileManager plugin), 31385291c01bb25d635d098f91708905 (Chrome stealer), cdd5c08b43238c47087a5d914d61c943 (Edge stealer)
- [File Path] Dropped and persistence paths – %ALLUSERSPROFILE%googlechrome.exe (chrome stealer), %ALLUSERSPROFILE%googlemsedge.exe (edge stealer), %LOCALAPPDATA%bugreportbugreport_.exe and %LOCALAPPDATA%valvevalveSDL2.dll
- [Domain] C2 and hosting – holoohg.oss-cn-hongkong.aliyuncs[.]com (URL hosting AsyncRAT C2 bytes), wuwu6[.]cfd (AsyncRAT-related domain)
- [IP Address] C2 servers – 103[.]237[.]92[.]191 (GodRAT C2), 47[.]238[.]124[.]68 (AsyncRAT C2) and other observed C2s such as 118[.]99[.]3[.]33 and 118[.]107[.]46[.]174
Read more: https://securelist.com/godrat/117119/