An Android phishing campaign impersonating an Indian government electricity subsidy scheme lures victims via YouTube and a GitHub-hosted phishing site to install a malicious APK that steals UPI credentials, SMS messages, and contact data while enabling remote control via Firebase. McAfee reported the apps and repository to Google and GitHub, leading to actions including blocking the FCM account and removal of the GitHub repository. #PMBY #PMMBY #FCM #GitHub #sqcepo.replit.app
Keypoints
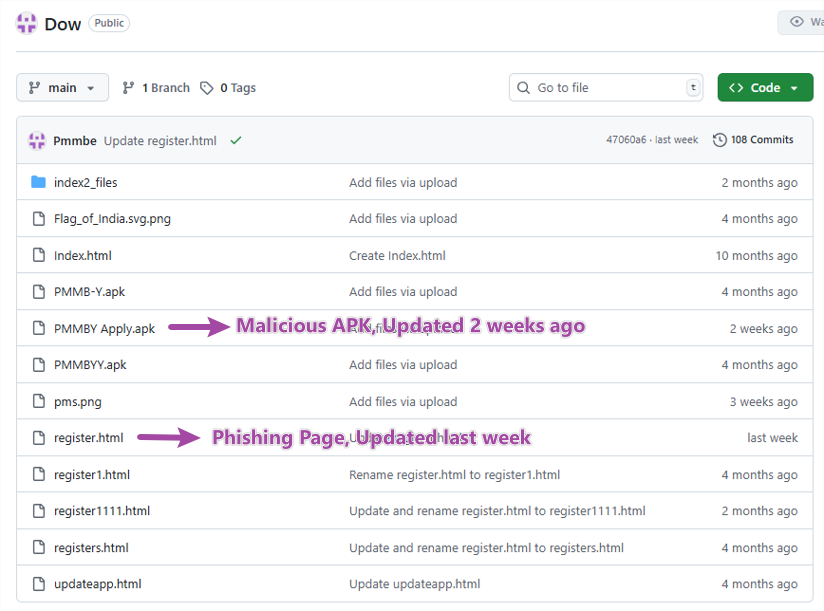
- Attackers used YouTube videos with shortened URLs to drive victims to a GitHub-hosted phishing website that mimics an official Indian subsidy portal.
- The phishing site links to a GitHub-hosted APK; the initial installer (PMBY) embeds and installs the real malware (PMMBY) labeled as a “Secure Update.”
- PMMBY requests aggressive permissions (READ_CONTACTS, READ_SMS, SEND_SMS, CALL_PHONE, notification access) to steal contacts, SMS (including 2FA), and send smishing messages to victims’ contacts.
- UPI credential theft is performed via a fake UPI-Lite HTML form hosted on sqcepo.replit.app, which uploads phone number, bank details, and UPI PIN to attacker-controlled endpoints.
- Malware exfiltrates incoming SMS to https://sqcepo.replit.app/addsm.php and uses Firebase Cloud Messaging (FCM) as a command-and-control channel to remotely issue commands.
- Repository activity shows continuous development since October 2024 with frequent updates, and hosting on GitHub was abused to appear legitimate and bypass detections.
- McAfee reported the malicious apps and GitHub repo; Google blocked the FCM account and GitHub removed the repository; McAfee Mobile Security detects the threat as high-risk.
MITRE Techniques
- [T1190] Exploit Public-Facing Application – Phishing website hosted on GitHub mimics official portal to deliver APK via links (“…the shortened URL redirects to a phishing website hosted on GitHub…”).
- [T1608] Stage Capabilities – Malicious APK contains an embedded APK in assets/app.apk used to install the real malware (“…it contains an embedded APK file at assets/app.apk, which is the actual malware…”).
- [T1204] User Execution – Social engineering via YouTube videos and fake subsidy promises to convince users to download and install the app (“…promotional videos claiming users can receive ‘government electricity subsidies’…”).
- [T1436] Masquerading – App presents fake Google Play icon and “Secure Update” UI to appear legitimate (“…fake Google Play icon…the icon points to an APK file on GitHub” and “installed under the guise of ‘Secure Update’”).
- [T1402] Input Capture – Fake UPI-Lite HTML form captures UPI PIN and bank details and uploads them to attacker-controlled endpoints (“…the phone number, bank details, and UPI PIN are uploaded to https://sqcepo.replit.app/addup.php”).
- [T1431] SMS Collection – Requests READ_SMS and SEND_SMS to read incoming SMS and upload them to attacker server (“…when it receives the incoming SMS message…posts below data to remote server(https://sqcepo.replit.app/addsm.php)”).
- [T1446] Exfiltration Over Web Service – Exfiltrates harvested SMS and credentials to replit.app endpoints (“…uploads to https://sqcepo.replit.app/addup.php” and “https://sqcepo.replit.app/addsm.php”).
- [T1552] Unsecured Credentials – Use of attacker-controlled web endpoints to collect authentication secrets (UPI PIN, bank details) (“…UPI credential theft…uploaded to https://sqcepo.replit.app/addup.php”).
- [T1105] Remote File Copy – GitHub used to host and distribute APK and phishing site files (“…Both the phishing site source and the APK file are hosted on the same GitHub repository…”).
- [T1069] Permission Groups Discovery/Modification – Requests and uses sensitive Android permissions to enable malicious functionality (“…requests aggressive permission when it is launched. READ_CONTACTS, CALL_PHONE, READ_SMS, SEND_SMS, Notification access”).
- [T1071] Application Layer Protocol – Uses HTTPS requests to rebrand.ly and replit.app endpoints for configuration and data exfiltration (“…creates a background task to send a https request to https://rebrand.ly/dclinkto2…response text is https://sqcepo.replit.app/gate.html,https://sqcepo.replit.app/addsm.php”).
- [T1531] Access Token Manipulation (FCM abuse) – Uses Firebase Cloud Messaging to send remote commands to infected devices (“…Attackers use FCM(Firebase Cloud Messaging) to send commands to control devices. According to the _type value, malware executes different commands.”).
Indicators of Compromise
- [Domain ] phishing & exfiltration endpoints – sqcepo.replit.app (gate.htm/gate.html, addsm.php, addup.php)
- [Shortened URL ] distribution redirect – rebrand.ly/dclinkto2 (used to retrieve phishing endpoints)
- [Hosting Service ] malware/phishing hosting – GitHub repository hosting APK and phishing site (repository removed; activity since Oct 2024)
- [App/File Names ] installer and malware – PMBY (initial APK), PMMBY (malware APK; embedded at assets/app.apk)
- [URLs ] UPI phishing and SMS upload – https://sqcepo.replit.app/gate.htm, https://sqcepo.replit.app/addsm.php, https://sqcepo.replit.app/addup.php