Beast is an evolved Ransomware-as-a-Service originally derived from Monster (first seen March 2022) that now targets Windows, Linux, and VMware ESXi with stronger encryption, multi-threading, service termination, shadow-copy deletion, and a TOR-hosted data leak site. A related variant, Boramae, shares near-identical code with advanced obfuscation and OpenSSL static linking, and Beast’s victims are concentrated in the United States across industries like Manufacturing and Construction. #Beast #Boramae
Keypoints
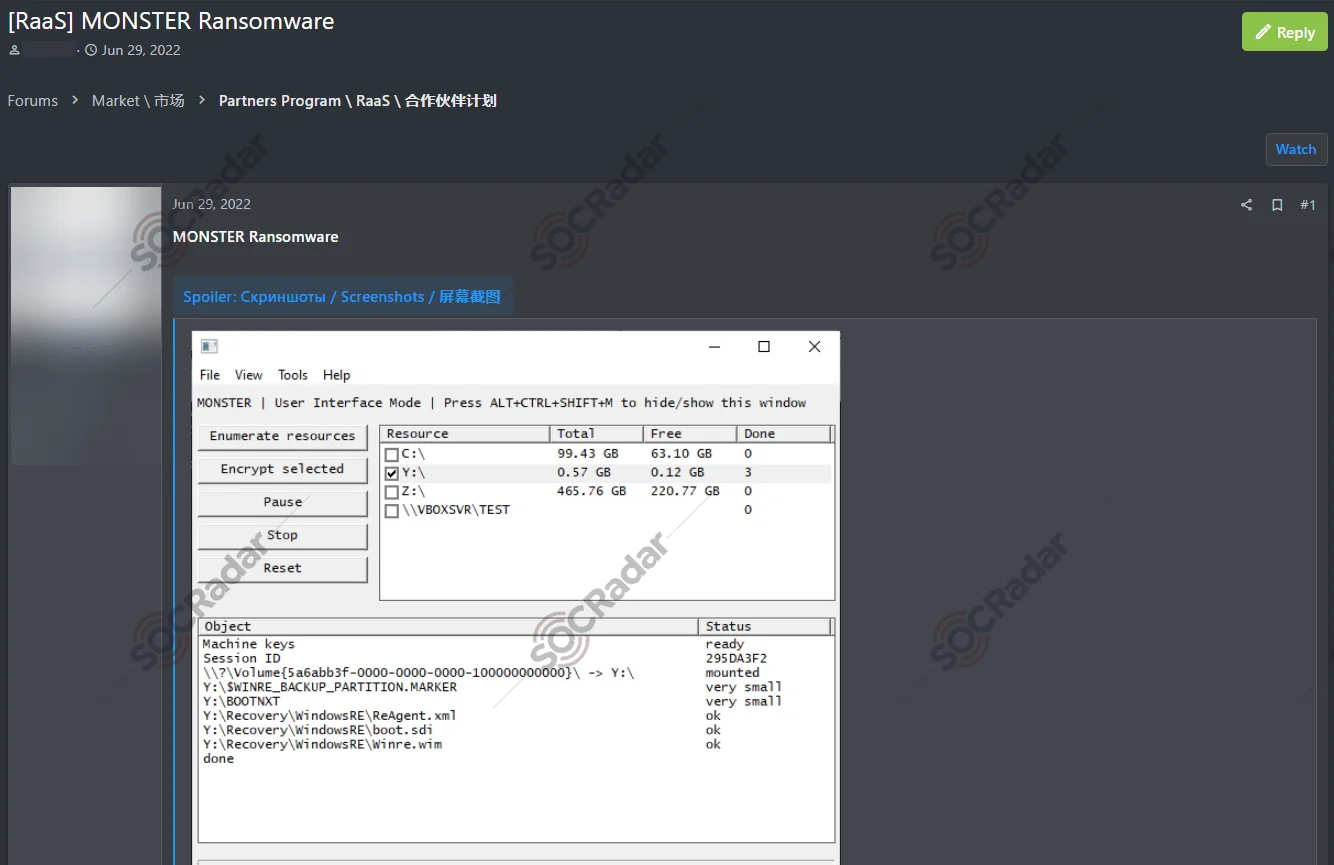
- Beast evolved from the Monster ransomware (first detected March 2022) and is offered as a customizable RaaS with affiliate recruitment across Russian, English, and Chinese forums.
- Beast expands platform support beyond Windows to include Linux and VMware ESXi, including features like daemon mode (Linux) and VM shutdown (ESXi).
- Key capabilities include Elliptic-curve and ChaCha20 encryption, multithreaded processing, service termination, shadow-copy deletion, SMB scanning for lateral movement, and a TOR-based self-hosted data leak site.
- Operators and affiliates use phishing (copyright/resume lures with nested archives), compromised RDP, and stolen credentials from underground forums as initial access vectors.
- Beast’s activity shows strong targeting of U.S. organizations (10 of 18 known victims) with sectors most affected being Manufacturing and Construction; Healthcare, Business Services, Financial Services, and Education also observed.
- The Boramae variant shares almost identical code with Beast but is larger due to static OpenSSL linking and uses advanced string obfuscation (incremental XOR and subtraction-based decoding), complicating detection.
- Mitigations recommended include layered defenses: email filtering, MFA, patching, EDR with behavioral detection, network segmentation, offline immutable backups, CTI monitoring of Beast’s TOR DLS, and regular testing/tabletop exercises.
MITRE Techniques
- [T1047 ] Windows Management Instrumentation – Used to delete shadow copies and interfere with recovery: ‘deletes shadow copies via WMI queries to block recovery attempts.’
- [T1106 ] Native API – Employed by malware routines for direct system calls and low-level operations (implied by platform-specific builds and encryption routines).
- [T1543.003 ] Create or Modify System Process: Windows Service – Beast establishes persistence and service modification capabilities in Windows builds.
- [T1078.001 ] Valid Accounts: Default Accounts – Affiliates leverage stolen or default credentials obtained from underground forums for initial access.
- [T1078.002 ] Valid Accounts: Domain Accounts – Compromised domain accounts are used to move laterally and access network resources.
- [T1406.002 ] Obfuscated Files or Information: Software Packing – Boramae and Beast use string obfuscation and packing techniques: ‘advanced string obfuscation, including incremental XOR key changes for each character.’
- [T1620 ] Reflective Code Loading – Observed obfuscation and packing behaviors suggest in-memory or reflective loading techniques to evade detection.
- [T1070.004 ] Indicator Removal on Host: File Deletion – Beast deletes shadow copies and other artifacts to hinder recovery: ‘deletes shadow copies via WMI queries to block recovery attempts.’
- [T1036 ] Masquerading – Executables are disguised with HWP or Excel icons and named to appear benign in phishing campaigns.
- [T1083 ] File and Directory Discovery – Beast scans file systems to identify targets for encryption and collection.
- [T1057 ] Process Discovery – The ransomware enumerates processes to terminate backup, database, and security software (e.g., Veeam, MSSQL, QuickBooks, Symantec).
- [T1135 ] Network Share Discovery – Beast scans SMB ports and subnets to locate accessible shared folders for propagation.
- [T1016 ] System Network Configuration Discovery – The malware checks network configuration and uses IP checks (via iplogger.co) to avoid CIS-country devices.
- [T1021.002 ] Remote Services: SMB/Windows Admin Shares – SMB scanning and use of admin shares enable lateral movement across networks.
- [T1055 ] Process Injection – Techniques for in-memory manipulation and persistence indicate process injection capabilities to maintain execution and evade detection.
- [T1119 ] Automated Collection – Beast performs automated collection of files for encryption across local and network drives prior to extortion.
- [T1486 ] Data Encrypted for Impact – Primary impact is file encryption using Elliptic-curve and ChaCha20 cryptography to lock victim data.
- [T1489 ] Service Stop – Beast terminates services (backup, database, security) to disrupt operations before encryption.
- [T1490 ] Inhibit System Recovery – By deleting shadow copies and other recovery artifacts, Beast inhibits system recovery mechanisms.
Indicators of Compromise
- [File extension ] Encrypted file markers – ‘.boramae’ used by the Boramae variant to mark encrypted files.
- [File name ] Ransom note and artifacts – ‘README.txt’ ransom note dropped into affected directories; ‘[ID].BEAST.zip’ or ‘[ID].BEAST’ filenames used by Windows builds.
- [Mutex ] Process mutex string – Earlier Beast builds used the mutex string ‘BEAST HERE?’ to prevent multiple instances (string removed in Boramae).
- [Domains/IP checks ] Geolocation evasion – Use of iplogger.co to check external IP and avoid infecting CIS-country devices.
- [Infrastructure ] Data leak hosting – TOR-based self-hosted data leak site (onion service) used to publish stolen data rather than public file-sharing services.
- [Tools/linked malware ] Infostealer delivery – Vidar infostealer observed in phishing campaigns delivering Beast, indicating presence of info-stealer IOCs.
Read more: https://socradar.io/dark-web-profile-beast-ransomware/