The Noodlophile Stealer campaign has evolved from fake AI video platform lures into a targeted, multilingual spear-phishing operation that exploits enterprises with large Facebook footprints using copyright-infringement-themed emails. Attackers now use legitimate signed applications and DLL side‑loading, Telegram-based staging, and enhanced obfuscation to deliver a stealer focused on browser data and cookies (notably Facebook cookies). #Noodlophile #Facebook
Keypoints
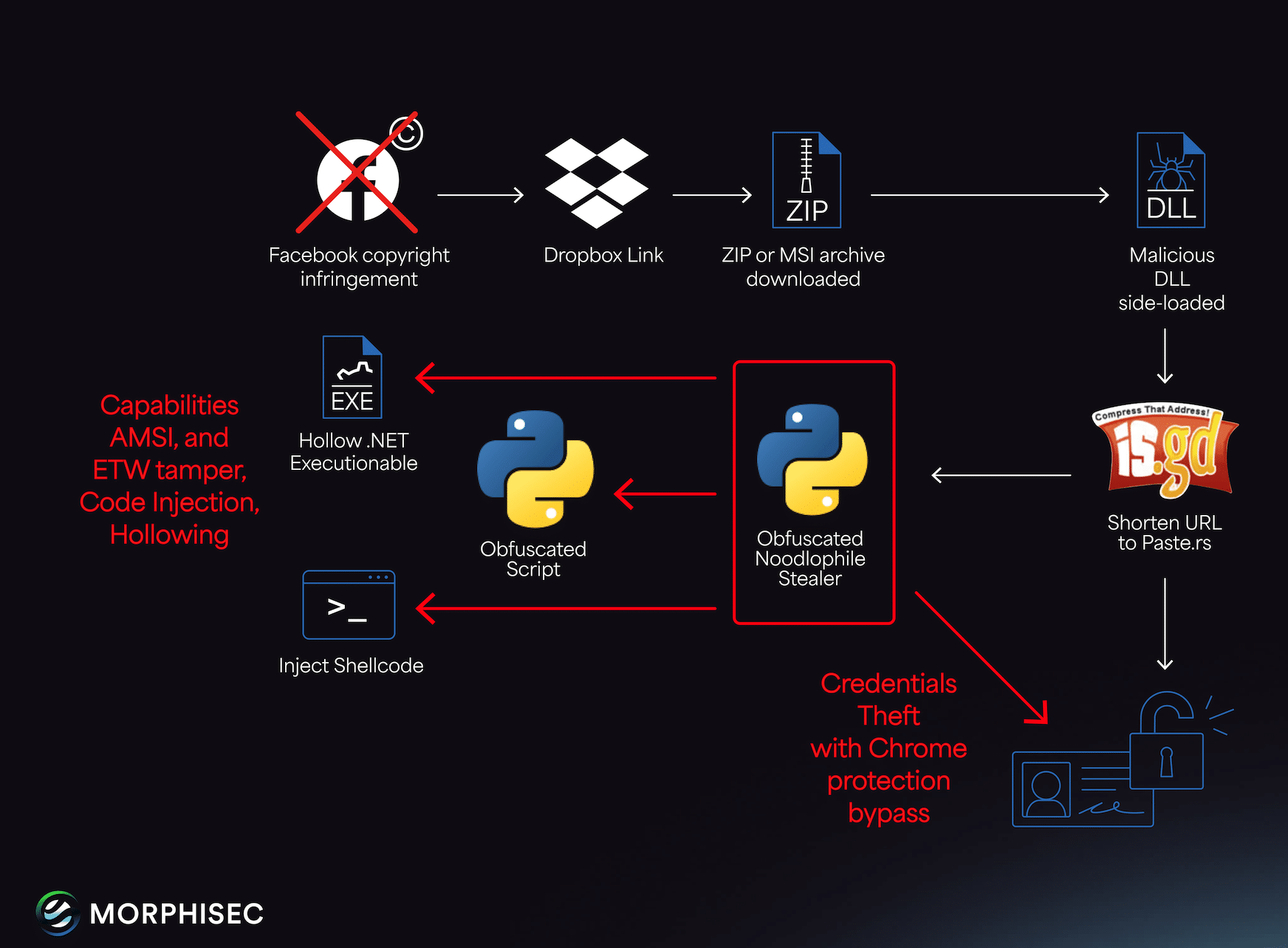
- Attackers send personalized copyright infringement spear-phishing emails containing specific Facebook Page IDs and ownership details to employees and generic inboxes (e.g., info@, support@).
- Delivery shifted from fake AI platforms to abusing legitimate signed applications (e.g., Haihaisoft PDF Reader, Excel converters) via DLL side-loading and chained DLL vulnerabilities.
- Payloads are staged via Dropbox links and TinyURL/T.ly redirects; archives contain disguised BAT scripts, SFX, and renamed files that reveal scripts and a portable Python interpreter.
- Intermediate BAT scripts establish persistence (HKCU Run keys or ProgramsStartup), download additional payloads in some variants, and execute a Python-based next-stage stealer.
- Obfuscation increased: scripts extract payload URLs from Telegram group descriptions and final payloads hosted on paste sites (e.g., paste.rs), enabling in-memory execution and evasion of disk-based detection.
- Noodlophile currently harvests browser data (cookies.sqlite, Web Data, Login Data, Gecko/Chrome credentials), credit card data, system and security product enumeration, and maintains self-deletion and persistence mechanisms.
- Code contains placeholder functions for future features (screenshot, keylogging, file exfiltration, AMSI/ETW tampering), indicating likely rapid capability expansion.
MITRE Techniques
- [T1586] Compromise Infrastructure – Use of free paste sites (e.g., “https://paste[.]rs/Gc2BJ”) and Dropbox links as hosting for payloads, quoted: ‘https://paste[.]rs/Gc2BJ’.
- [T1566] Phishing – Highly personalized spear-phishing emails claiming copyright infringement and including Facebook Page IDs to induce victims to click links, quoted: ‘View Copyright Infringement Evidence.pdf’.
- [T1204] User Execution – Malicious archives contain disguised BAT scripts and SFX files executed by users or via LOLBins, quoted: ‘batch scripts renamed as .docx files or self-extracting archives (SFX) posing as .png files’.
- [T1574] Hijack Execution Flow (DLL Side-Loading) – Abuse of legitimate signed applications and vulnerable DLLs to side-load malicious DLLs (recursive stub loading and chained DLL vulnerabilities), quoted: ‘legitimate, signed applications vulnerable to DLL side-loading, such as Haihaisoft PDF Reader and Excel converters’.
- [T1105] Ingress Tool Transfer – Downloading additional disguised files and next-stage scripts from remote servers or Telegram-extracted URLs, quoted: ‘renamed BAT scripts download additional disguised files … from remote servers’.
- [T1055] Process Injection – In-memory execution of final stealer to avoid disk-based detection, quoted: ‘in-memory execution to avoid disk-based detection’.
- [T1547] Boot or Logon Autostart Execution – Persistence via HKCU Run registry entries and ProgramsStartup folder, quoted: ‘create registry entries under HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionRun’ and ‘persistence via the ProgramsStartup directory’.
- [T1083] File and Directory Discovery – Renaming and revealing archived files (e.g., .pptx, .docx) to locate BAT scripts and Python interpreters, quoted: ‘side-loaded DLLs rename additional files within the archive … to reveal BAT scripts and portable Python interpreters’.
- [T1005] Data from Local System – Stealer collects browser databases and local system information (cookies.sqlite, Login Data, Win32_ComputerSystem), quoted: ‘steals Facebook cookies … SELECT * FROM Win32_ComputerSystem’.
- [T1497] Virtualization/Sandbox Evasion – Use of obfuscated scripts and Telegram-based dynamic URLs to complicate detection and takedown, quoted: ‘scripts extract a URL from the description of a Telegram group, enabling dynamic execution’.
Indicators of Compromise
- [Email Patterns] phishing subjects and senders – gmail.com senders using subjects like “Copyright Infringement Notice” and phrases “Immediate Action Required”, “Facebook Page ID”.
- [URLs/Domains] staging and payload hosts – https://paste[.]rs/Gc2BJ, https://www.dropbox[.]com/s/[id]/Archive.zip?dl=1, and multiple TinyURL/T.ly redirects (e.g., https://is[.]gd/PvLoKt, https://t[.]ly/cCEsy).
- [Telegram IDs/Tokens] command-and-control and staging – Telegram bot IDs/tokens such as 7913144042:AAGjalVuULPrUgnBqD8d4O33scWPa0GjPUE and chat IDs like -1002394294746.
- [IP Addresses] remote text/payload hosts – examples: 196.251.84[.]144 (suc/zk2.txt), 15.235.172[.]219 (vmeo/getlink?id=dcaathur).
- [File Hashes] malicious files and loaders – examples: CE69FA15…B2EB2 (dcaathur), 95D964EF…7390D (.net stealer from zk2.txt), and other hashes (and 10+ more hashes listed).
- [File Names] archive and script artifacts – examples: “Jūs_esat_pārkāpis_reģistrētas_preču_zīmes_tiesības_1.zip”, “Alerta_!de_!uso_!indebido_!de_!contenido_!protegido.zip”, “tm.docx”.