Scattered Spider (UNC3944) is a financially motivated, adaptive cybercriminal group active since at least May 2022, using sophisticated social engineering, phishing kits (including Evilginx), and diverse hosting strategies to target high-value sectors like retail, finance, and entertainment. Recent activity includes disruptive 2025 UK retailer attacks, a fifth-generation phishing kit mimicking Okta portals, and a noisy August 2025 Telegram channel blending Scattered Spider, LAPSUS$, and ShinyHunters personas. #ScatteredSpider #Evilginx
Keypoints
- Scattered Spider has conducted high-impact breaches and ransomware incidents (e.g., MGM, Caesars, and April 2025 UK retailer attacks) using social engineering and technical exploitation.
- The group deploys multiple visually identical but distinct phishing kits, with the 2025 Kit #5 specifically targeting Okta portals and exfiltrating credentials immediately.
- They register domains in bulk and reuse dedicated servers and ASNs (Cloudflare, Choopa, DigitalOcean, Hostinger, Njalla, Virtuo) to support rapid, persistent campaigns.
- Operators shifted to more privacy-focused hosting (Virtuo, Njalla) and favored registrar NiceNIC since mid-2024, later incorporating Cloudflare in 2025.
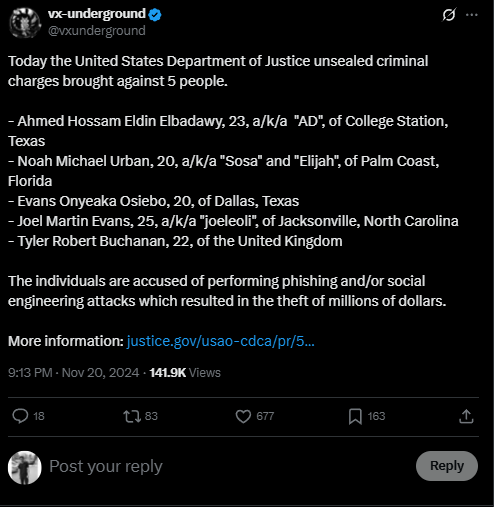
- Several arrests occurred in 2024 (including alleged leaders Noah Urban, Tyler Buchanan, others), yet the group continued evolving and producing new phishing kits in 2025.
- Scattered Spider uses Evilginx for MitM session hijacking; phishing pages often mimic target branding and redirect victims (historically to a Rick Astley video) to obscure payloads.
- A hybrid Telegram channel “Scattered LAPSUS$ Hunters” (Aug 2025) mixed validated and unverified leaks, extortion threats, and claims of a large exploit/0day arsenal, complicating threat attribution and response.
MITRE Techniques
- [T1566 ] Phishing for Information – Use of visually identical phishing kits and Okta-themed pages to capture credentials. Quote: ‘the phishing pages were designed to closely mimic the targeted organization’s Okta portal.’
- [T1539 ] Steal Web Session Cookies – Use of Evilginx MitM framework to hijack authentication sessions and capture credentials. Quote: ‘Scattered Spider’s use of the Evilginx framework … hijack authentication sessions and capture credentials.’
- [T1588 ] Obtain Capabilities: Tool – Deployment of Evilginx and custom phishing kits as offensive tooling. Quote: ‘Several domains linked to Scattered Spider have been identified as hosting Evilginx software.’
- [T1580 ] Cloud Infrastructure Discovery – Targeting cloud service dashboards and cloud-hosted identities (Okta). Quote: ‘The web pages … mimic the targeted organization’s Okta portal … “Powered by Okta” footer.’
- [T1589 ] Gather Victim Identity Information – Use of targeted branding and domain keywords (okta, sso, help) to increase social engineering success. Quote: ‘phishing kit used short-lived, brand-themed domains that often included keywords like “okta,” “sso,” “help.”’
- [T1584 ] (mapped Tactics: Recon) Domain Registration & Management – Bulk domain registration and staggered attack waves using clustered domains. Quote: ‘They routinely register clusters of domains within short windows …’
- [T1114 ] Email Collection – Phishing and data exfiltration campaigns leading to large data dumps (Gucci, Neiman Marcus, Chanel, Coca-Cola). Quote: ‘some posted data dumps … have been validated as genuine.’
- [T1567 ] Exfiltration Over Web Service – Immediate exfiltration of submitted credentials to attacker-controlled infrastructure. Quote: ‘Once credentials were submitted, the phishing infrastructure would immediately exfiltrate the data.’
- [T1090 ] Proxy – Use of hosting providers and CDNs (Cloudflare, Njalla, Virtuo) and server pivots to obscure infrastructure and resist takedown. Quote: ‘renting dedicated servers from more privacy-focused hosting providers … to avoid detection and disruption.’
- [T1657 ] Financial Theft – SIM swapping and cryptocurrency theft linked to arrested members (Noah Urban), supporting financial motivation. Quote: ‘Urban was implicated in SIM swapping schemes that led to the theft of approximately $800,000 in cryptocurrency.’
Indicators of Compromise
- [Domain ] Phishing/credential harvesting sites – corp-hubspot[.]com, morningstar-okta[.]com, and many others (see additional domains below).
- [Domain ] Evilginx hosting domains – corp-azure[.]com, corporatetools-okta[.]com (hosted on Virtuo, DigitalOcean, Choopa).
- [ASN/Hosting ] Infrastructure providers – Cloudflare (AS13335), DigitalOcean (AS14061), Choopa (AS20473), Njalla (AS39287), Virtuo (AS399486), Hostinger (AS47583).
- [Registrar ] Registration patterns – NiceNIC used for numerous bulk registrations (preferred since Q2 2024); historical registrars include GoDaddy, Hosting Concepts.
- [Domain ] Sample additional IOCs – 7-eleven-hr[.]com, doordash-support[.]com, gucci-cdn[.]com, pure-okta[.]com, signin-nydig[.]com (and many more listed in IOC section).
Read more: https://darkatlas.io/blog/scattered-spider-unc3944-a-comprehensive-and-detailed-threat-profile