The article details a spear-phishing campaign targeting businesses across multiple regions using fake law firm emails to spread the Noodlophile infostealer malware. The campaign employs sophisticated techniques like DLL side-loading and disguised artifacts to evade detection. #Noodlophile #DLLSideLoading
Keypoints
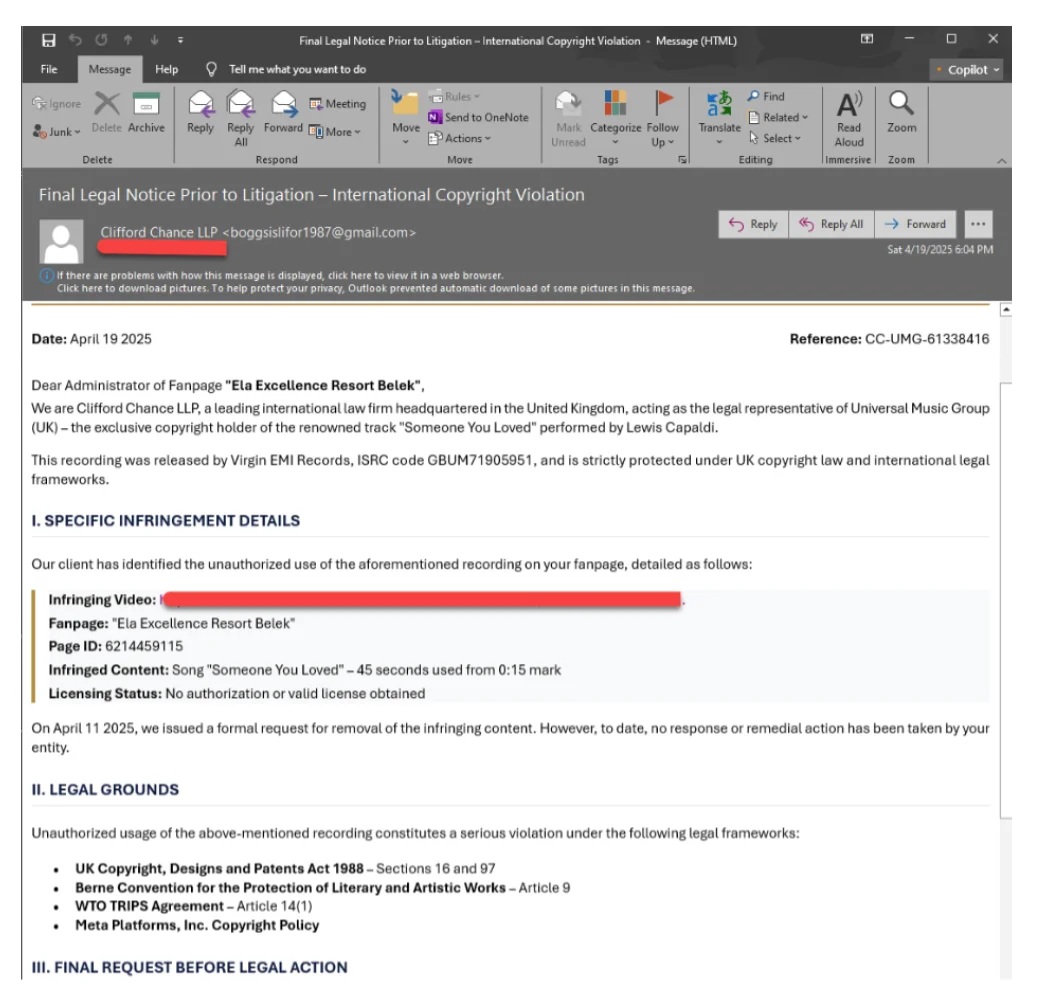
- Attackers send targeted spear-phishing emails impersonating law firms to deliver malware.
- The threat employs language diversity and generative AI tools for convincing scams.
- Malware is delivered through legitimate, signed applications exploiting DLL side-loading vulnerabilities.
- Noodlophile can steal login credentials, credit card info, and system details from infected devices.
- Newer versions of the malware can potentially include keylogging, screenshot capture, and file encryption features.