Salty 2FA is a newly identified Phishing-as-a-Service framework that uses multi-stage obfuscated JavaScript, a distinct domain pattern combining .??.com compound domains with .ru infrastructure, and behavioral techniques to steal Microsoft 365 credentials and bypass multiple 2FA methods. Analysis mapped its execution chain, evasion methods, and wide-ranging targets, with notable examples including marketplace24ei[.]ru and frankfurtwebs[.]com[.]de. #Salty2FA #marketplace24ei[.]ru
Keypoints
- Salty 2FA is a new PhaaS framework that targets Microsoft 365 credentials and can bypass several 2FA methods (push, SMS, voice).
- The framework uses a distinctive domain pattern: compound “.??.com” subdomains paired with .ru-registered domains (e.g., nexttradeitaly[.]it[.]com + marketplace24ei[.]ru).
- The attack unfolds in multiple stages: obfuscated entry script, encrypted payload with fake login page, client-side logic with anti-analysis, encoded exfiltration, and multi-state 2FA handling.
- Client-side defenses include obfuscated code, dynamic Base64+XOR encoded element IDs, blocking DevTools shortcuts, and debugger-detection via timing checks.
- Data exfiltration places encoded payload in POST request parameters (request= with Base64+XOR) and uses session-based decoding keys stored in session=.
- Static IOCs are unreliable due to frequent mutation; detection should focus on persistent behavioral patterns (domain TLD chains, URL structures, resource loading patterns).
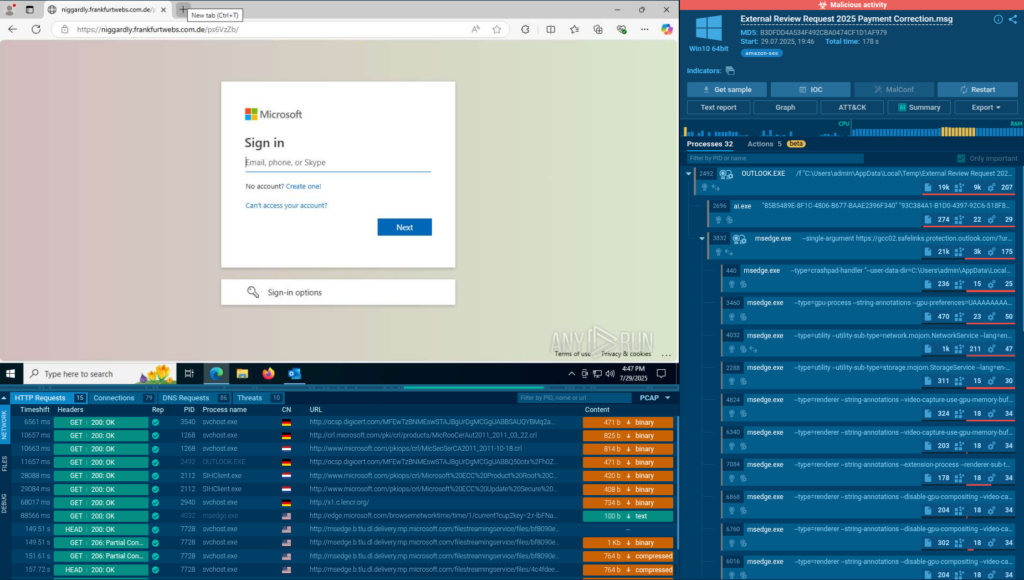
- Observed targets span many industries and countries, and sandboxing (ANY.RUN) was critical to mapping the execution flow and uncovering IOCs in real time.
MITRE Techniques
- [T1059] Command and Scripting Interpreter – JavaScript executes multi-stage payloads in the browser, e.g., “a small ‘trampoline’ JavaScript executes… initializes the Cloudflare Turnstile widget… and returns a cf_response token.”
- [T1027] Obfuscated Files or Information – Payloads and page text are obfuscated and padded with non-functional “noise” to hinder static analysis: “‘padded with non-functional “noise”’ and ‘page text itself… appears obfuscated in the code.’”
- [T1204.002] User Execution: Malicious Link – Phishing delivered via email with pre-filled victim emails and lures like “Voice message was left…” and “Access full document…”.
- [T1608] Stage Capabilities: Exfiltration Over Web Service – Stolen credentials are encoded and sent via POST requests to .ru endpoints using request= and session= parameters: “‘The data itself is encoded and placed in the request= parameter of the POST request, while the decoding key… is stored in the session= parameter.’”
- [T1499] Endpoint Denial of Service (Anti-Analysis via Debugger Detection) – The script measures execution time when a debugger is triggered and halts if a delay is detected: “‘Measuring execution time when a debugger is triggered and halting further activity if a delay is detected.’”
- [T1553] Subvert Trust Controls: Web Service Manipulation (Cloudflare Turnstile) – Uses Cloudflare Turnstile initialization and cf_response tokens to progress payload delivery: “‘initializes the Cloudflare Turnstile widget… and returns a cf_response token.’”
- [T1112] Modify Registry / Local Scripts (Client-side controls) – Client blocks keyboard shortcuts and DevTools usage to prevent local debugging and analysis: “‘Blocking keyboard shortcuts that open debugging tools (e.g., DevTools).’”
- [T1105] Ingress Tool Transfer – Staged retrieval of payloads from multiple domains (e.g., parochially[.]frankfurtwebs[.]com[.]de -> marketplace24ei[.]ru -> 790628[.]php) to chain and load malicious components: “‘Decoding… reveals the URL of the next payload: hxxps://marketplace24ei[.]ru//’ and later hxxps://marketplace24ei[.]ru/790628.php.’”
Indicators of Compromise
- [Domain] phishing infrastructure and landing pages – marketplace24ei[.]ru, frankfurtwebs[.]com[.]de
- [Compound Domain] unusual TLD chaining used in campaigns – nexttradeitaly[.]it[.]com, innovationsteams[.]com
- [URLs] example phishing/redirect paths – hxxps://parochially[.]frankfurtwebs[.]com[.]de/ps6VzZb/, hxxps://telephony[.]nexttradeitaly[.]com/SSSuWBTmYwu/
- [Email/IP] extracted from SPF/email headers – 153[.]127[.]234[.]4, 51[.]89[.]33[.]171 (and 2 more IPs)
- [Sandbox Sessions] analysis links for investigation – https://app.any.run/tasks/91e777dd-603b-47e4-ad8f-96e8bddf2cba, https://app.any.run/tasks/7d8e3a4d-5226-40b9-9e94-0f833c784abc
Read more: https://any.run/cybersecurity-blog/cybersecurity-blog/salty2fa-technical-analysis/