Trustwave SpiderLabs details an EncryptHub campaign that uses social engineering, Teams-based remote access, and exploitation of CVE-2025-26633 (MSC EvilTwin) to load malicious .msc files and deploy payloads like Fickle Stealer. The actor also uses Golang tools (SilentCrystal, a SOCKS5 backdoor), Brave Support and rivatalk.net hosting for payload delivery and C2 communications. #EncryptHub #CVE-2025-26633
Category: Threat Research

Positive Technologies discovered JavaScript keyloggers injected into Exchange Server authentication pages that either write stolen credentials to local files accessible externally or exfiltrate them directly to external servers (via HTTP requests, Telegram bots, DNS tunneling, headers, or open directories). Analysis found reused, obfuscated code variants collecting credentials, cookies, and User-Agent, with examples of target URLs like /owa/auth/logon.aspx and exfil methods including Telegram and DNS; #ExchangeServer #Telegram

Rooting and jailbreaking frameworks like KernelSU, APatch, SKRoot and Magisk hook into the Android kernel and often implement weak or flawed authentication, enabling malicious apps to escalate privileges and fully compromise rooted devices. zLabs demonstrated …
ThreatFabric disclosed PhantomCard, an Android banking trojan in Brazil that performs NFC relay fraud by prompting users to tap cards and then capturing/transmitting card data and PINs to criminals. The campaign is delivered via fake Google Play pages, operate…

In July 2025, phishing emails accounted for 60% of malicious attachments, commonly using HTML/script attachments and hyperlinks in documents to collect credentials or redirect victims to fake sites; attacks also included exploit documents (CVE-2017-11882) delivering Lokibot and compressed PE files in ZIPs. Reported artifacts include specific MD5 hashes and Korean-language phishing…
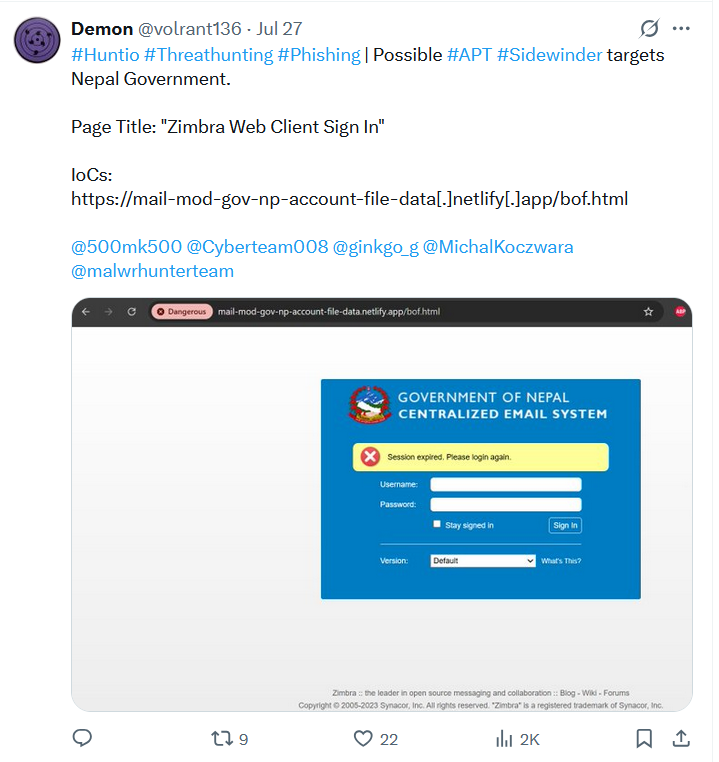
APT Sidewinder ran widespread spear-phishing campaigns impersonating government and defense portals in Bangladesh, Nepal, and Turkey, using Netlify/Pages.dev-hosted fake Zimbra and secure-portal pages to harvest credentials. Centralized credential collection domains mailbox3-inbox1-bd.com and mailbox-inbox-bd.com (resolving to 146.70.118.226) indicate reused backend infrastructure and redundancy. #Sidewinder #mailbox3-inbox1-bd.com

Intezer discovered a new, low-detected Linux FireWood backdoor variant that retains core RAT functionality but changes implementation details, persistence paths, and command handling while simplifying its beaconing loop. The variant is linked with Project Wood lineage and has low-confidence ties to the Gelsemium APT; known hashes include 898a5bd8…acb6 and d7be3494…78af. #FireWood #ProjectWood
CYFIRMA analyzed an Android banking malware called “Lazarus Stealer” (unrelated to the DPRK-linked Lazarus Group) that disguises itself as GiftFlipSoft to stealthily intercept SMS, monitor apps, deploy phishing overlays, and exfiltrate banking credentials and SMS/OTP data. Infrastructure and code strings link the developer/operator to Russian-language control panels and Telegram, with C2 hosts such as 193.151.108.33 and the domain venom-lazarus.life. #Lazarus_Stealer #venom-lazarus.life
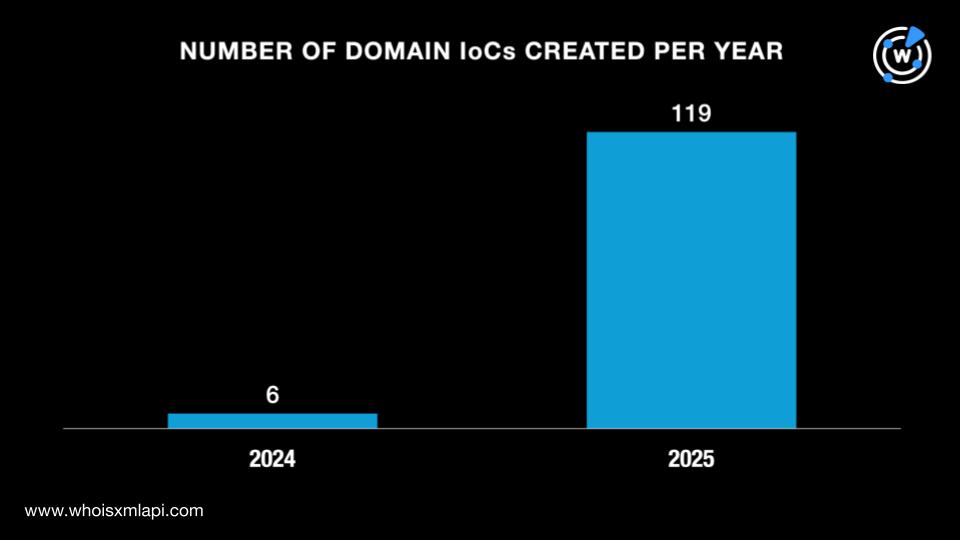
Check Point Research detailed a spearphishing campaign by Iranian threat actor Educated Manticore that used fake Gmail and Google Meet pages to steal credentials and 2FA codes from Israeli journalists, cybersecurity experts, and academics. Researchers identified 141 IoCs (129 domains, 12 IPs) and additional related artifacts, with many domains registered in 2025 via Namecheap and numerous historical DNS/IP resolutions. #EducatedManticore #alpha-man.info

Huntress observed a KawaLocker (KAWA4096) ransomware incident where the attacker gained RDP access, used HRSword and other tools to disable security software and then deployed KawaLocker against the E: volume. Detection breadcrumbs included HRSword activity, deletion of Volume Shadow Copies, and specific file hashes and filenames that identify the incident. #KawaLocker #HRSword
ShinyHunters resurfaced with coordinated Salesforce-targeting campaigns using ticket-themed phishing domains and Okta-branded credential harvesting pages, sparking speculation of collaboration with Scattered Spider. Domain registration patterns and shared infrastructure point to likely next targets in financial services and technology providers. #ShinyHunters #ScatteredSpider #Salesforce

Zscaler ThreatLabz discovered a malicious PyPI package chain where termncolor imported a Trojanized dependency, colorinal, which loaded terminate.dll/terminate.so to decrypt and drop a signed executable (vcpktsvr.exe) and a malicious DLL (libcef.dll) that performs system discovery and C2 via Zulip-like traffic. The operation uses AES-CBC decryption, DLL sideloading for execution and persistence via a Run registry entry, and associated artifacts have been removed from PyPI. #termncolor #colorinal

Void Blizzard (aka Laundry Bear) is a Russian state-sponsored group active since at least 2024 that targets NATO/EU governments, defense contractors, and critical infrastructure using credential theft, phishing (including QR-based AitM), and “living off the land” cloud abuse. Dutch AIVD/MIVD and Microsoft exposed their methods after attacks such as the September 2024 Dutch police compromise and an April 2025 spear-phishing campaign using Evilginx and a typosquatted domain. #VoidBlizzard #Evilginx
Cofense PDC uncovered a LeeMe ransomware campaign using compromised sender accounts, SAP Ariba-themed lures, password-protected GoFile downloads, a fake installation GUI, AES-256 encryption, and built-in exfiltration (keylogger/credential theft) to extort victims. Artifacts include specific executable and Python script hashes, GoFile/Telegram endpoints, and a Bitcoin ransom wallet; #LeeMe #SAP_Ariba
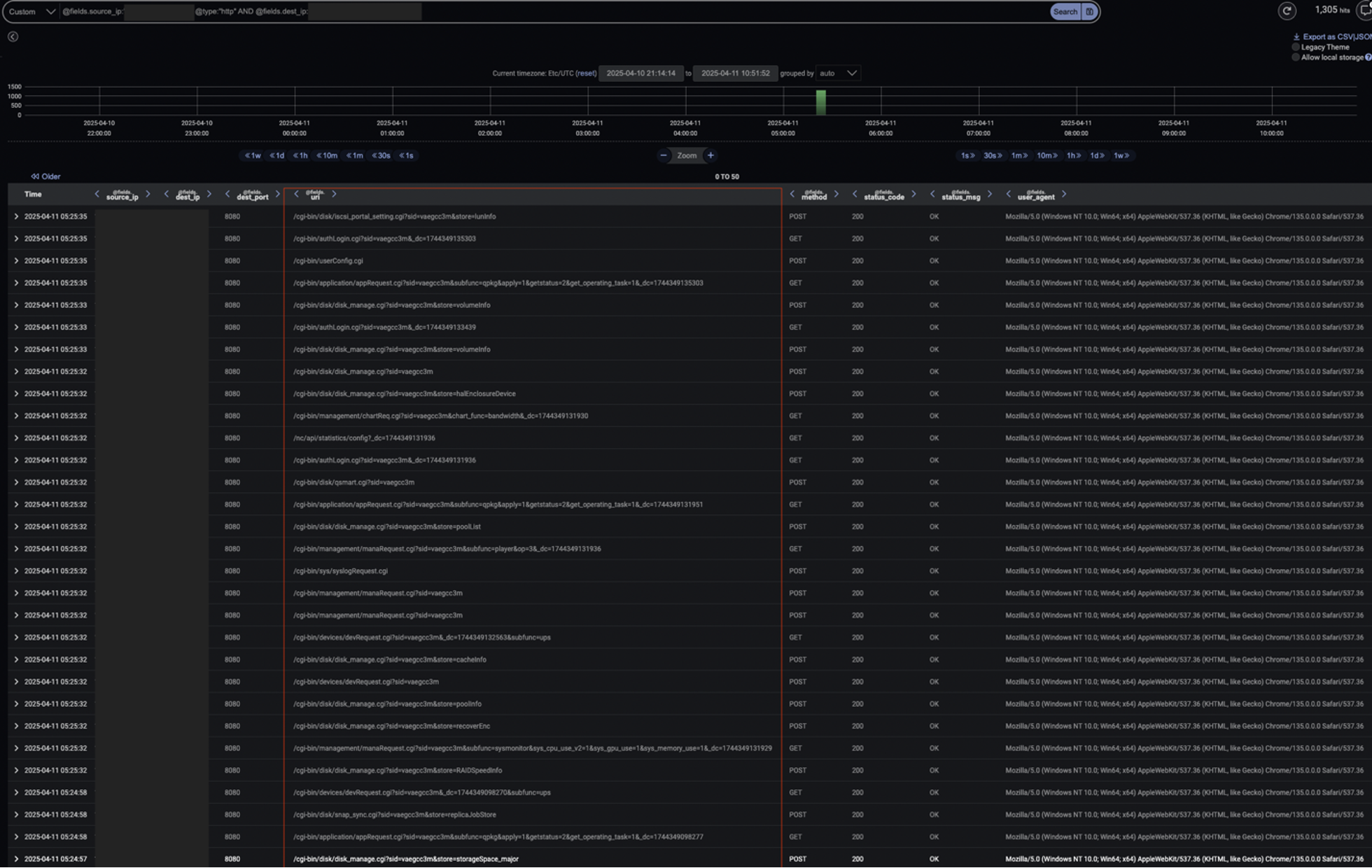
Threat actors continued exploiting Fortinet SSL‑VPN vulnerabilities (CVE-2022-42475, CVE-2023-27997, CVE-2024-21762) to gain unauthenticated remote code execution on FortiGate devices and establish persistent footholds. Darktrace detected post-exploitation behaviors—HTTP abuse of /cgi-bin/, internal Nmap scanning, SMB/NTLM credential activity, and long RDP sessions—and used Autonomous Response to block connections and contain the intrusion. #CVE-2024-21762 #CVE-2023-27997 #CVE-2022-42475
