Datadog observed a surge in supply-chain and cloud-native persistence techniques in Q2 2025, including malicious VS Code extensions and obfuscated NPM packages that steal credentials and deploy cryptominers. Notable actors/techniques include MUT-9332, MUT-6149, Mimo, and a novel “persistence-as-a-service” via AWS Lambda/API Gateway. #MUT-9332 #MUT-6149 #Mimo #persistence-as-a-service
Category: Threat Research

Researchers detonated a Snake Keylogger sample from MalwareBazaar, traced its external connections, and developed a Suricata rule that decodes Base64-encoded SMTP exfiltration to detect stolen data such as cookies and host identifiers. The investigation linked C2 IPs and demonstrated that existing ET rules missed the exfiltration until a signature targeting the Subject header and base64-decoded payload was created. #SnakeKeylogger #VIPKeylogger
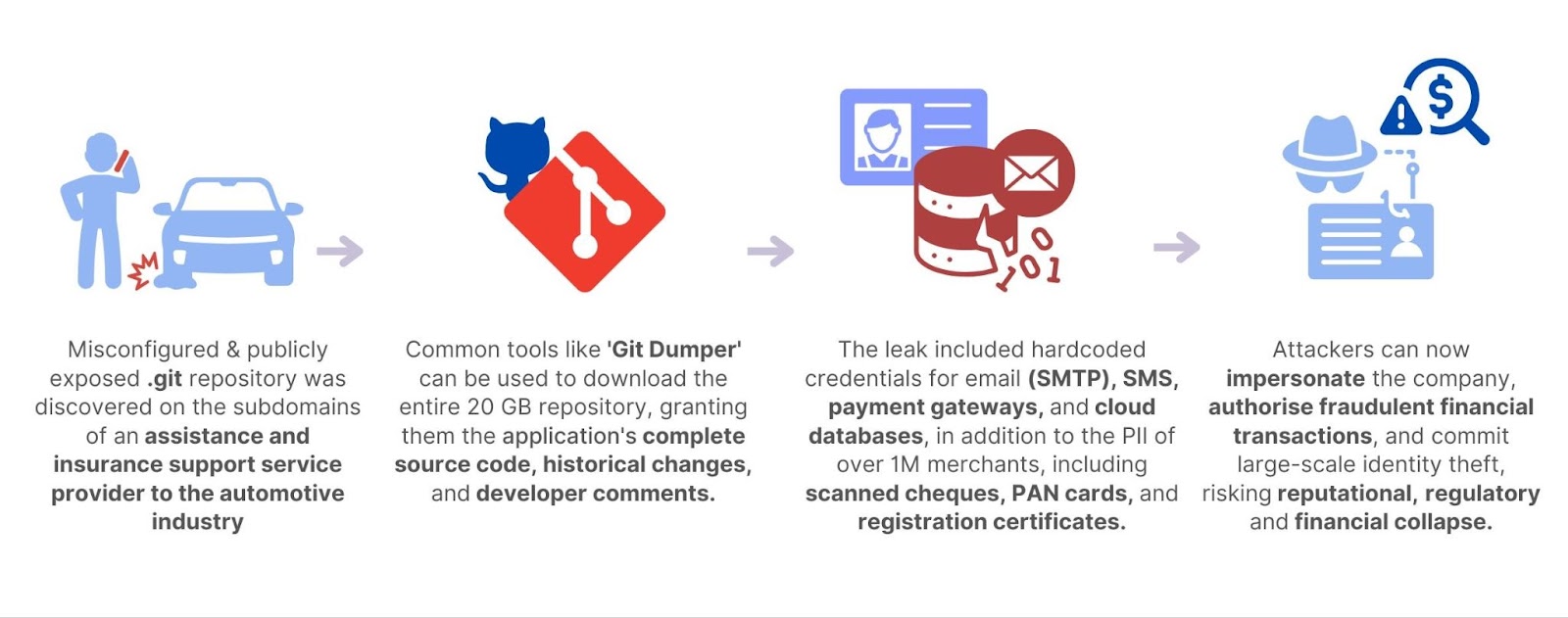
CloudSEK’s SVigil discovered a publicly accessible .git repository in a roadside assistance and insurance support vendor that exposed over 20 GB of sensitive data, including full source code, credentials, customer PII, and financial documents. The exposure enabled trivial extraction (e.g., with Git Dumper) and risked phishing, SMS impersonation, payment fraud, database compromise, identity theft, and broad supply-chain impacts. #SVigil #GitDumper
From Sept–Dec 2024 JPCERT/CC observed incidents using CrossC2 (a C/C++-based Cross-platform Cobalt Strike Beacon/builder) together with tools like PsExec, Plink, SystemBC, and a custom Nim loader dubbed ReadNimeLoader to deploy Cobalt Strike Beacons across multiple countries. The campaign shows overlaps with BlackBasta-related infrastructure and techniques, and JPCERT/CC published a CrossC2 config parser to aid analysis. #CrossC2 #ReadNimeLoader

VexTrio operates a large, resilient malicious adtech and traffic distribution infrastructure that leverages trackers (Binom, Keitaro), cloakers (IM KLO), CDNs, and automation tools to run global spamming, scamming, and scareware campaigns. Key infrastructure elements include dedicated IP ranges and CDN domains (e.g., imghst-de[.]com), DevOps tooling (Terraform, Kubernetes, GitLab), and affiliate networks like RollerAds that funnel victims into VexTrio-controlled trackers and landing pages. #Binom #IMKLO
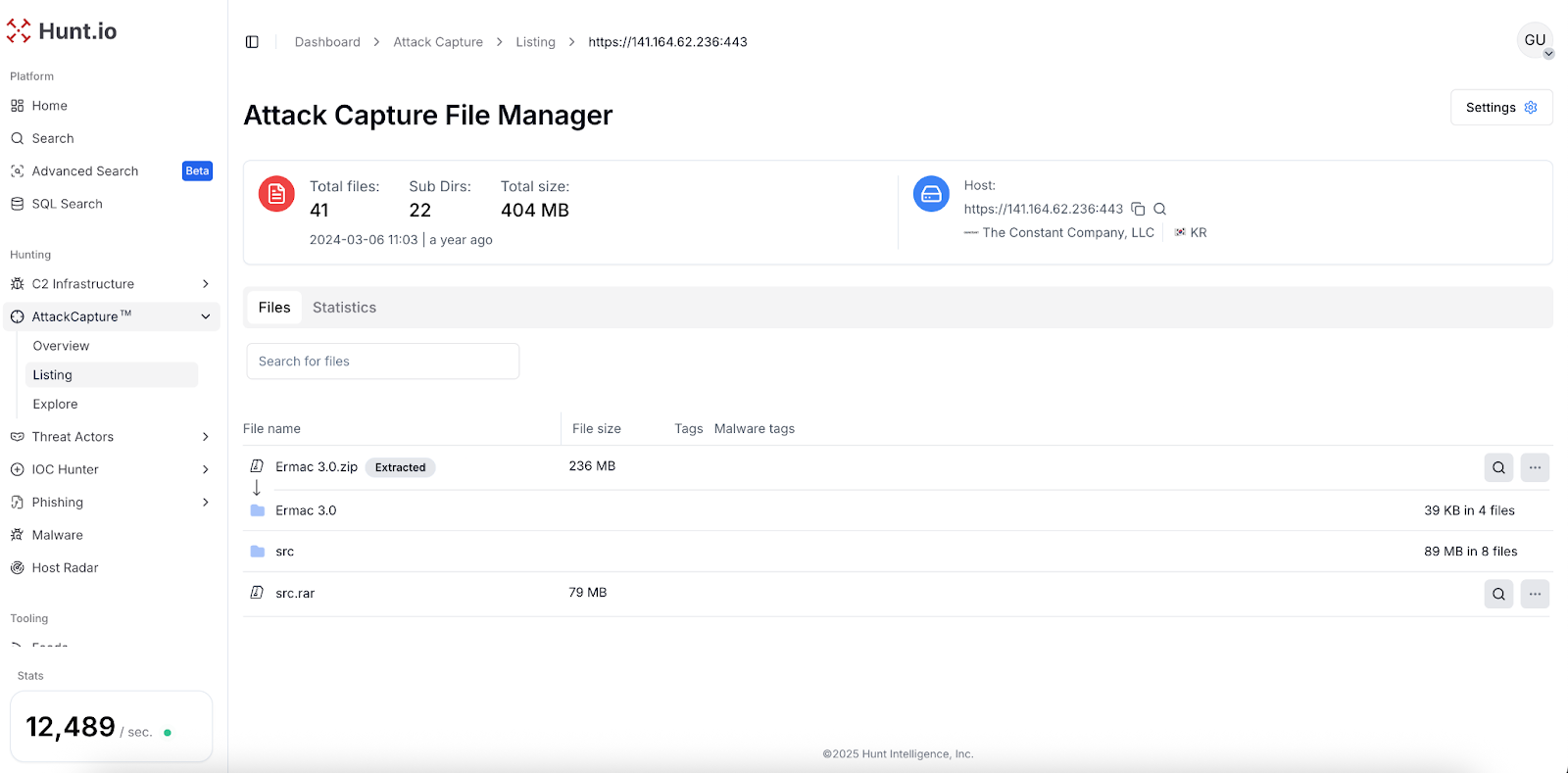
Hunt.io obtained the full ERMAC V3.0 source code in March 2024, revealing a Laravel/PHP backend, React frontend, Golang exfiltration server, and an obfuscated Android builder/backdoor that targets 700+ banking, shopping, and cryptocurrency apps. The leak exposed critical weaknesses (hardcoded JWT, static admin token, default credentials, open registration) and linked source artifacts to active C2, exfiltration, and builder infrastructure. #ERMAC #Ermac_v3
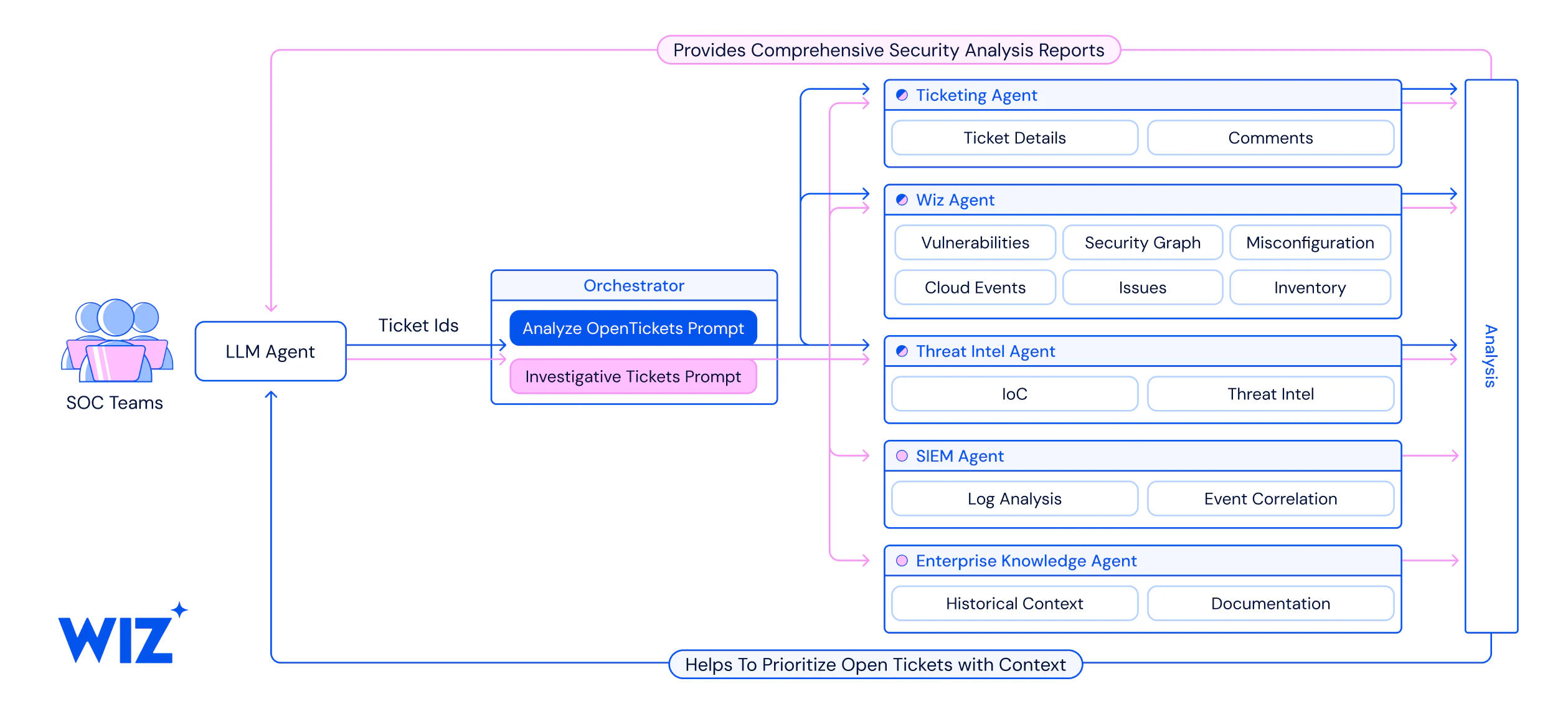
Grammarly adopted Wiz and the Wiz Model Context Protocol (MCP) Server to scale cloud visibility, automate incident triage, and integrate LLMs into security workflows, reducing investigation time from 30–45 minutes to under four minutes per ticket. The company expanded MCP use to threat hunting, detection engineering, and knowledge automation while following principles of starting small, iterating with real-world data, and keeping humans in the loop. #WizMCP #Grammarly
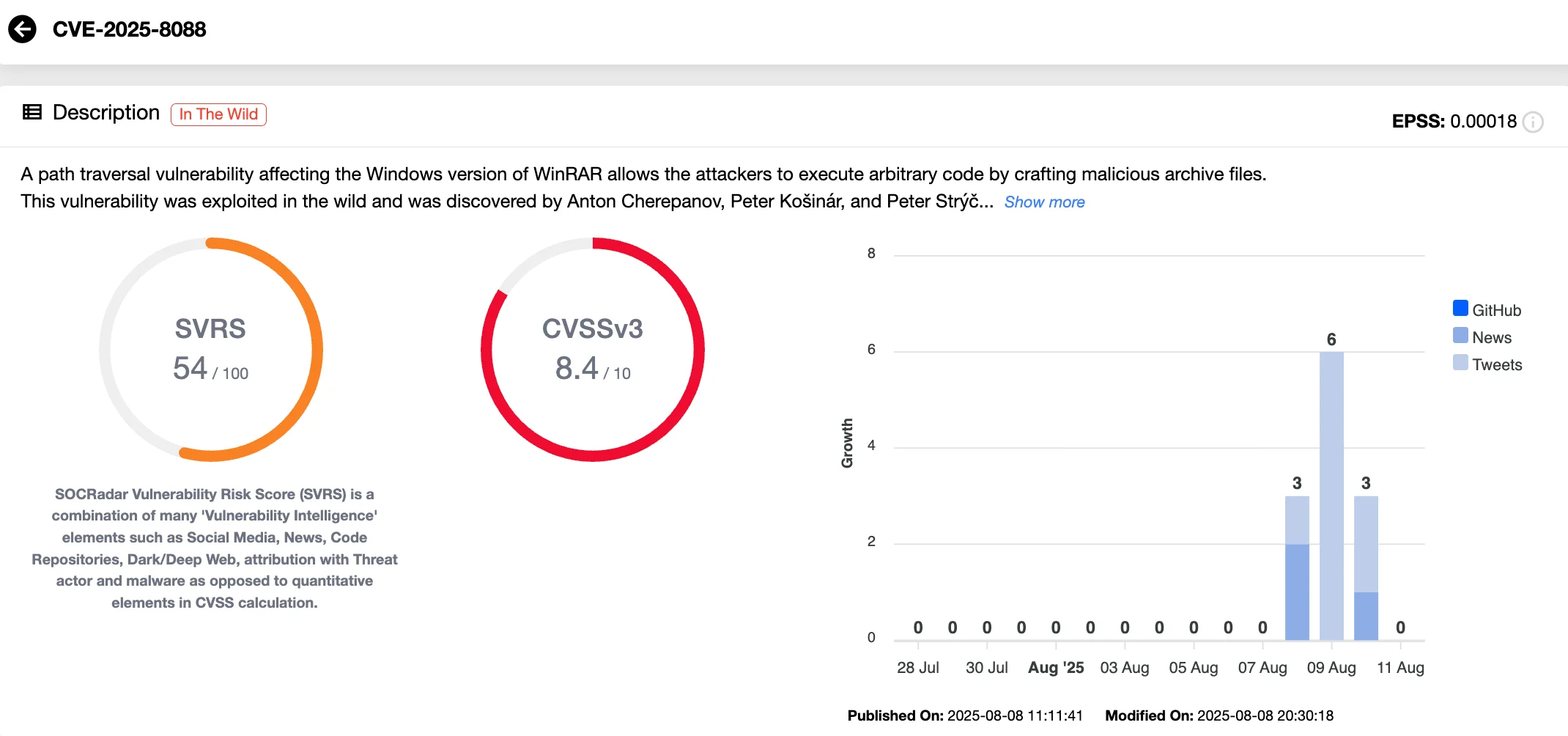
A WinRAR zero‑day, CVE-2025-8088, allowed attackers to abuse alternate data streams and path traversal to extract malicious files into privileged locations and was exploited in the wild from July 18, 2025 until patched in WinRAR 7.13 on July 30, 2025. ESET attributes primary exploitation to Russia-aligned RomCom (aka Storm-0978/UNC2596) and other actors like Paper Werewolf, with observed payloads including Mythic Agent, SnipBot variants, RustyClaw, and MeltingClaw. #CVE-2025-8088 #RomCom #MythicAgent #SnipBot #RustyClaw #MeltingClaw
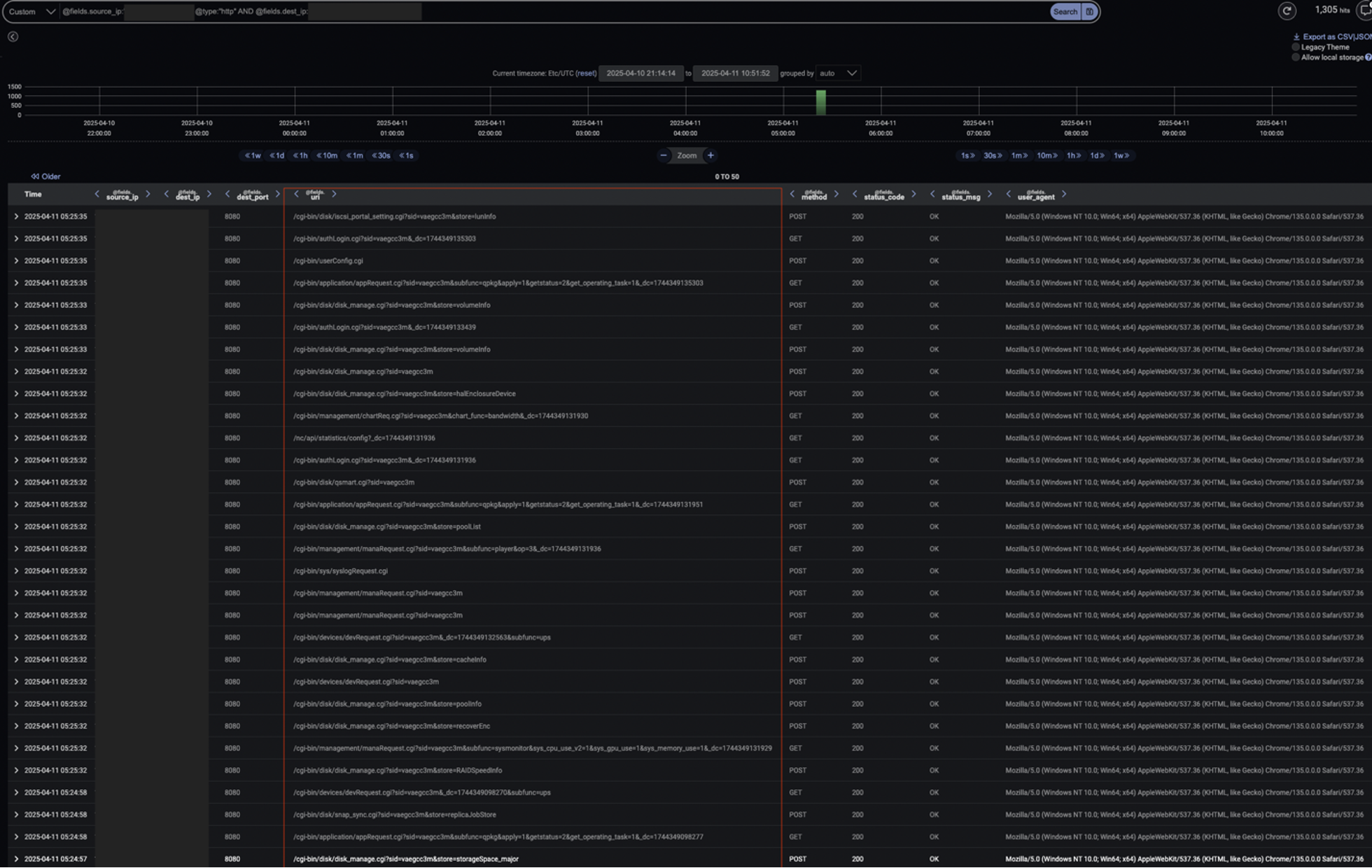
Threat actors continue exploiting Fortinet SSL‑VPN vulnerabilities CVE-2022-42475, CVE-2023-27997, and CVE-2024-21762 to gain unauthenticated remote code execution and persist on FortiGate devices. Darktrace observed HTTP-based exploitation, internal scanning, credential abuse, and RDP access, with Autonomous Response blocking connections and containing the incident. #CVE-2022-42475 #CVE-2024-21762
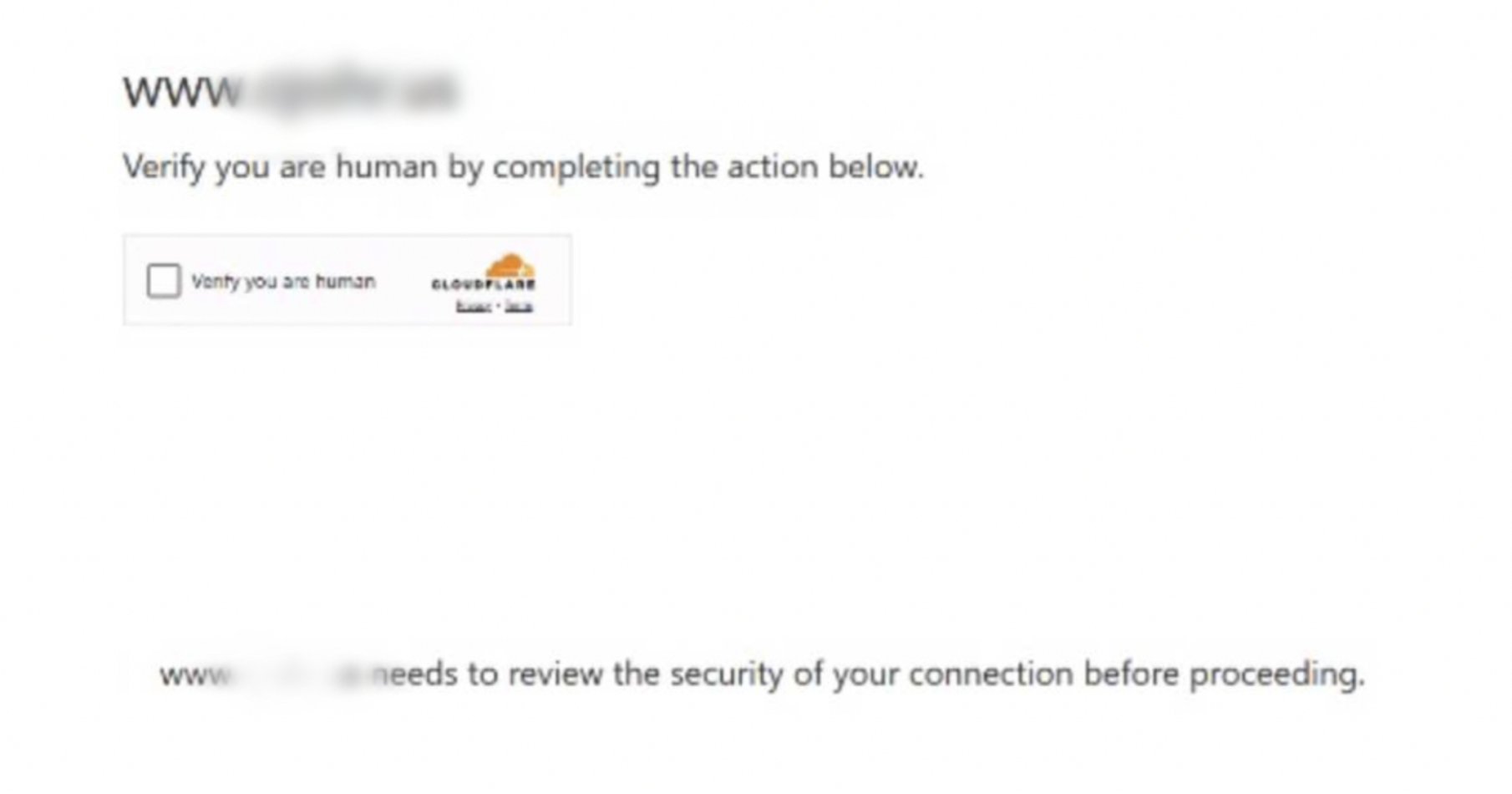
A JavaScript-based campaign injected a fullscreen iframe from suspicious domains (notably capcloud[.]icu and wallpaper-engine[.]pro) into compromised WordPress sites via the wp_options wpcode_snippets entry, using anti-debugging, function hijacking, and localStorage to persist and evade detection. The fake Cloudflare captcha lures Windows users into running a Base64 PowerShell command that downloads and executes a remote payload from 180.178.189.7. #capcloud[.]icu #wallpaper-engine[.]pro
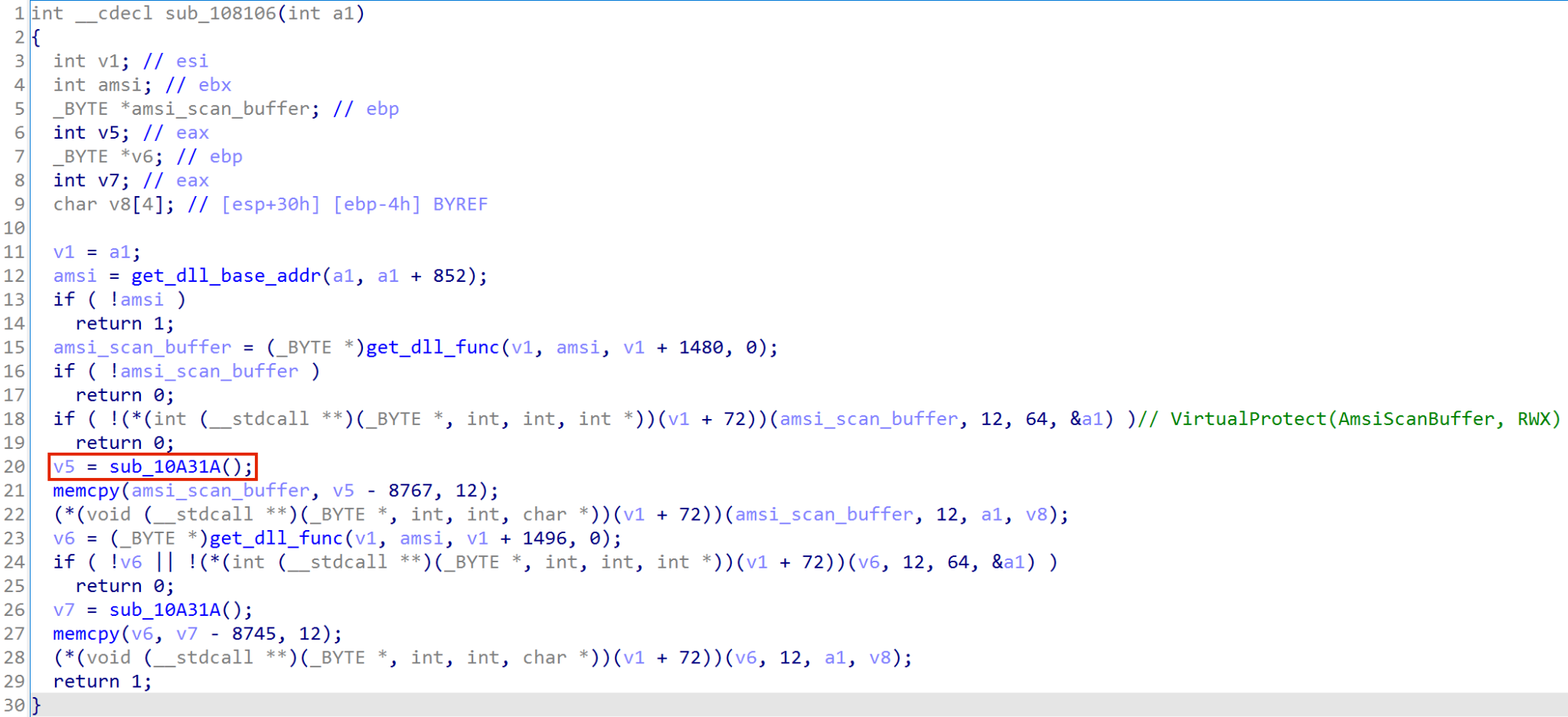
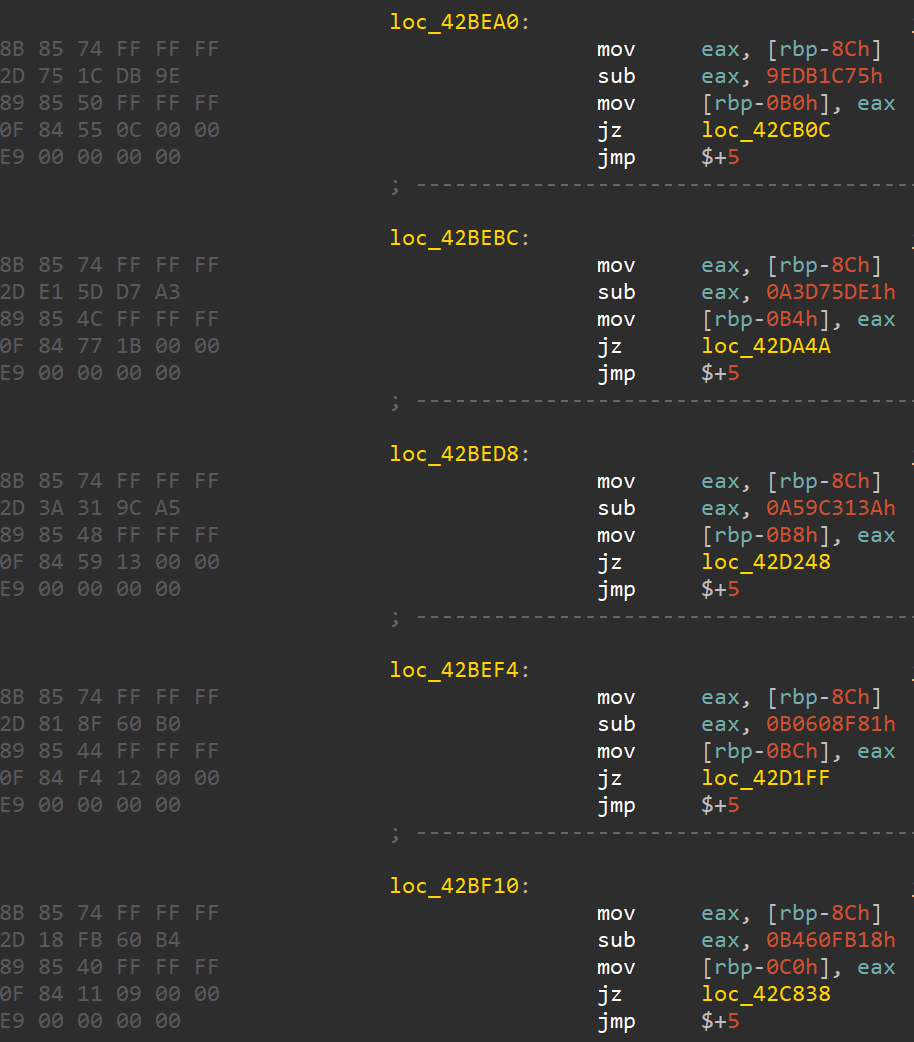
This article excerpts a Donut-generated shellcode malware analysis tutorial that walks through an end-to-end infection chain and demonstrates beginner-friendly static and dynamic analysis techniques. The excerpt focuses on a position-independent PC-relative addressing routine used in the shellcode and tools/methods used to analyze it. #Donut…
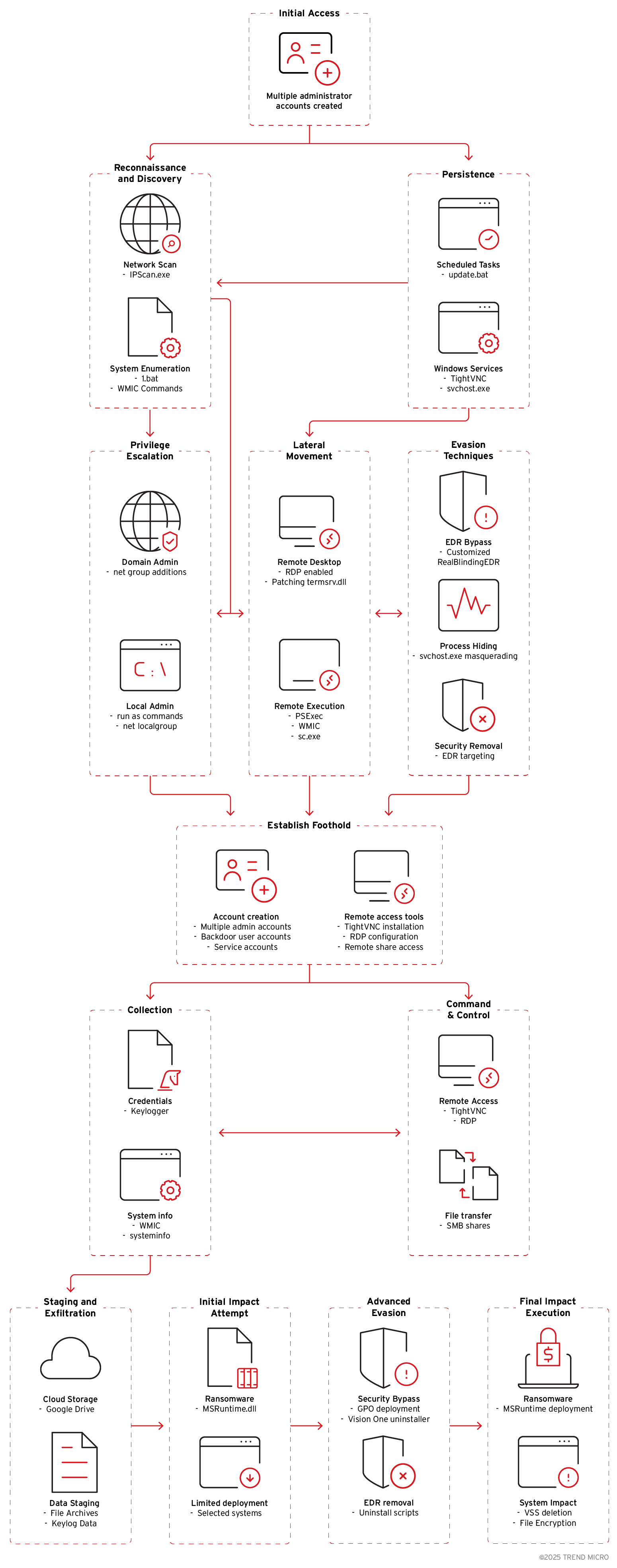
Crypto24 conducts coordinated, multi-stage ransomware attacks combining legitimate administrative tools (PsExec, AnyDesk, gpscript.exe) with custom malware (keyloggers, MSRuntime.dll, RealBlindingEDR variant) to gain persistence, move laterally, and evade EDR. The group targets large enterprises across Asia, Europe, and the USA, exfiltrates data via Google Drive, and disables security agents using tools like…

Researchers demonstrated that many Azure services expose an owning tenant ID via authentication-related HTTP responses, enabling attribution of publicly enumerable resource hostnames to specific tenants. They released ATEAM (Azure Tenant Enumeration and Attribution Module) to automate large-scale discovery and mapping of these resources. #Azure #ATEAM

India faces coordinated, ideologically driven cyber campaigns around Independence Day that include hacktivist defacements, DDoS, data breaches, widespread phishing, and fake domains targeting government and critical sectors. State‑linked APTs such as APT36, SideCopy, and APT41 are conducting targeted credential harvesting and malware-enabled espionage while criminal actors run festival scams and phishing lures. #APT36 #SideCopy #APT41

The report details data breaches, ransomware, and DDoS incidents targeting financial and insurance organizations, highlighting leaked customer records, ransomware exfiltration, and politically motivated service disruptions. Key actors and malware include Xsskiller (data seller), DAIXIN ransomware, and the hacktivist group Black Ember. #Xsskiller #DAIXIN #BlackEmber…
