Grammarly adopted Wiz and the Wiz Model Context Protocol (MCP) Server to scale cloud visibility, automate incident triage, and integrate LLMs into security workflows, reducing investigation time from 30–45 minutes to under four minutes per ticket. The company expanded MCP use to threat hunting, detection engineering, and knowledge automation while following principles of starting small, iterating with real-world data, and keeping humans in the loop. #WizMCP #Grammarly
Keypoints
- Grammarly transitioned from consumer to enterprise needs, requiring a scalable security framework to support rapid engineering velocity.
- Initial adoption of Wiz provided unified cloud visibility, vulnerability detection, and secure-by-design workflows.
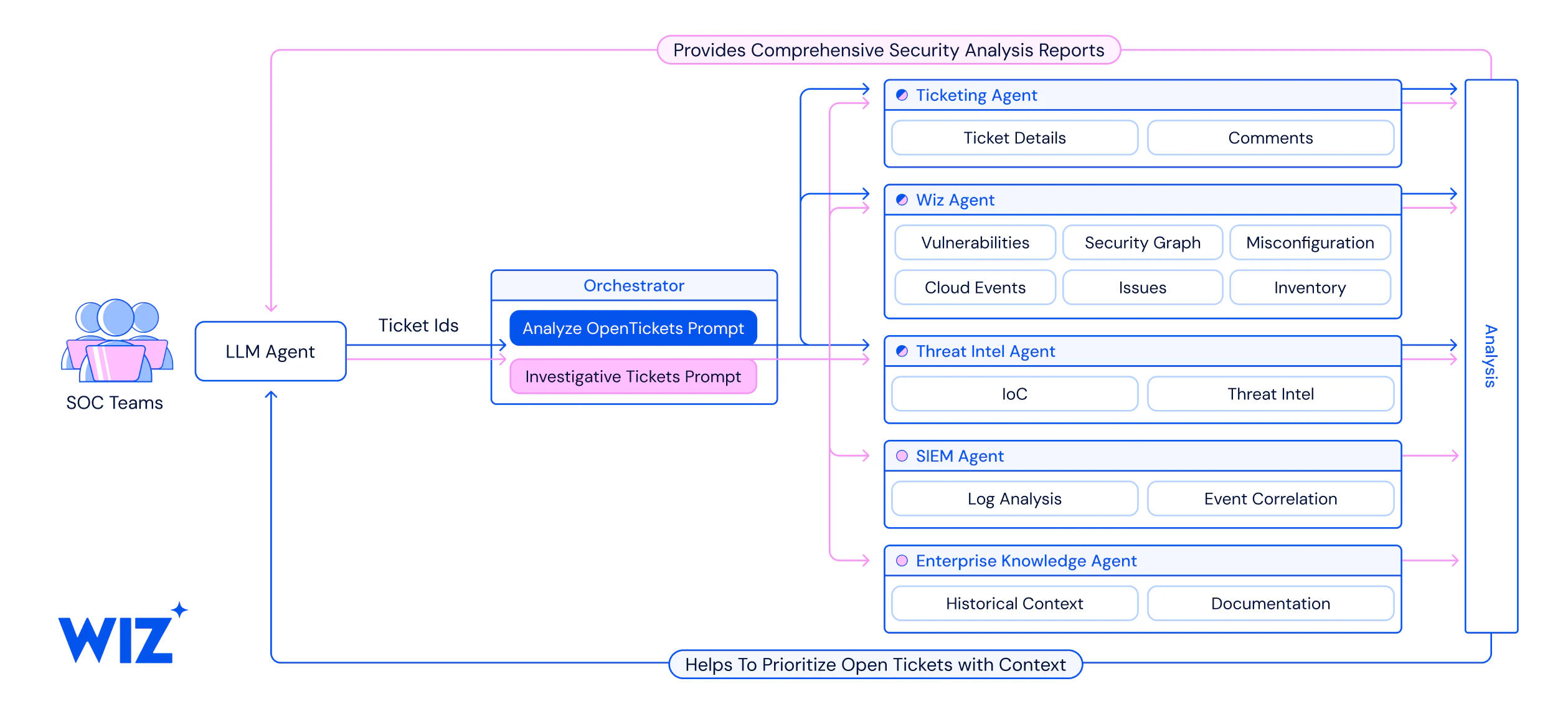
- Grammarly integrated the Wiz MCP Server (based on Anthropic’s MCP) to connect data sources and LLMs for automated, context-aware security tasks.
- They began with a focused use case—tier-1 incident triage—using custom prompts and orchestration, cutting triage time by ~90% (to ≤4 minutes).
- MCP workflows were refined with organizational data and prompt tuning, expanding use to threat hunting, detection engineering, and knowledge-building for SOC agents.
- Automation reduced manual toil, lowered ticket volume impact, and enabled security engineers to prioritize strategic work over routine monitoring.
- Core guiding principles: start small and iterate, prioritize team expertise, embrace human-in-the-loop, and shift from tactical firefighting to strategic initiatives.
MITRE Techniques
- [T1609] Container and Cloud Discovery – Used to gain unified visibility across cloud assets and identify vulnerabilities (“gain unified visibility and actionable intelligence across cloud assets, vulnerabilities, and potential risks”).
- [T1082] System Information Discovery – LLM-driven queries and Wiz tool calls retrieve providerData and resource configurations (“ALWAYS GET RAW PROVIDER DATA … include_fields”: [“providerData”]).
- [T1049] System Network Connections Discovery – MCP automates cross-referencing resources and checking logs to surface network-related context (“automate repetitive tasks like cross-referencing resources and checking logs”).
- [T1110] Brute Force (Mitigation/Detection) – MCP-assisted detection logic and mapping vulnerable paths help craft detections for new vulnerabilities (“MCP to map vulnerable paths and validate findings”).
- [T1606] Forge Web Credentials (Detection/Prevention) – Using Wiz MCP to validate findings and build detection logic implies detection/prevention workflows for credential-related exposures (“assist in crafting detection logic for new vulnerabilities”).
Indicators of Compromise
- [Tool/Service] context – Wiz MCP Server, Wiz, Claude Desktop (examples of tools/platforms integrated).
- [Ticket/Issue ID] context – example issue ID format: be21b858-b468-5bc8-de50-c5c9e97c5a92 (used in Wiz tool examples).
- [Resource Types] context – cloud resources and components referenced: S3 buckets (e.g., ‘prod-data’), RDS instances (‘my-service’), and IAM roles (examples used in investigation flows).