Hunt.io obtained the full ERMAC V3.0 source code in March 2024, revealing a Laravel/PHP backend, React frontend, Golang exfiltration server, and an obfuscated Android builder/backdoor that targets 700+ banking, shopping, and cryptocurrency apps. The leak exposed critical weaknesses (hardcoded JWT, static admin token, default credentials, open registration) and linked source artifacts to active C2, exfiltration, and builder infrastructure. #ERMAC #Ermac_v3
Keypoints
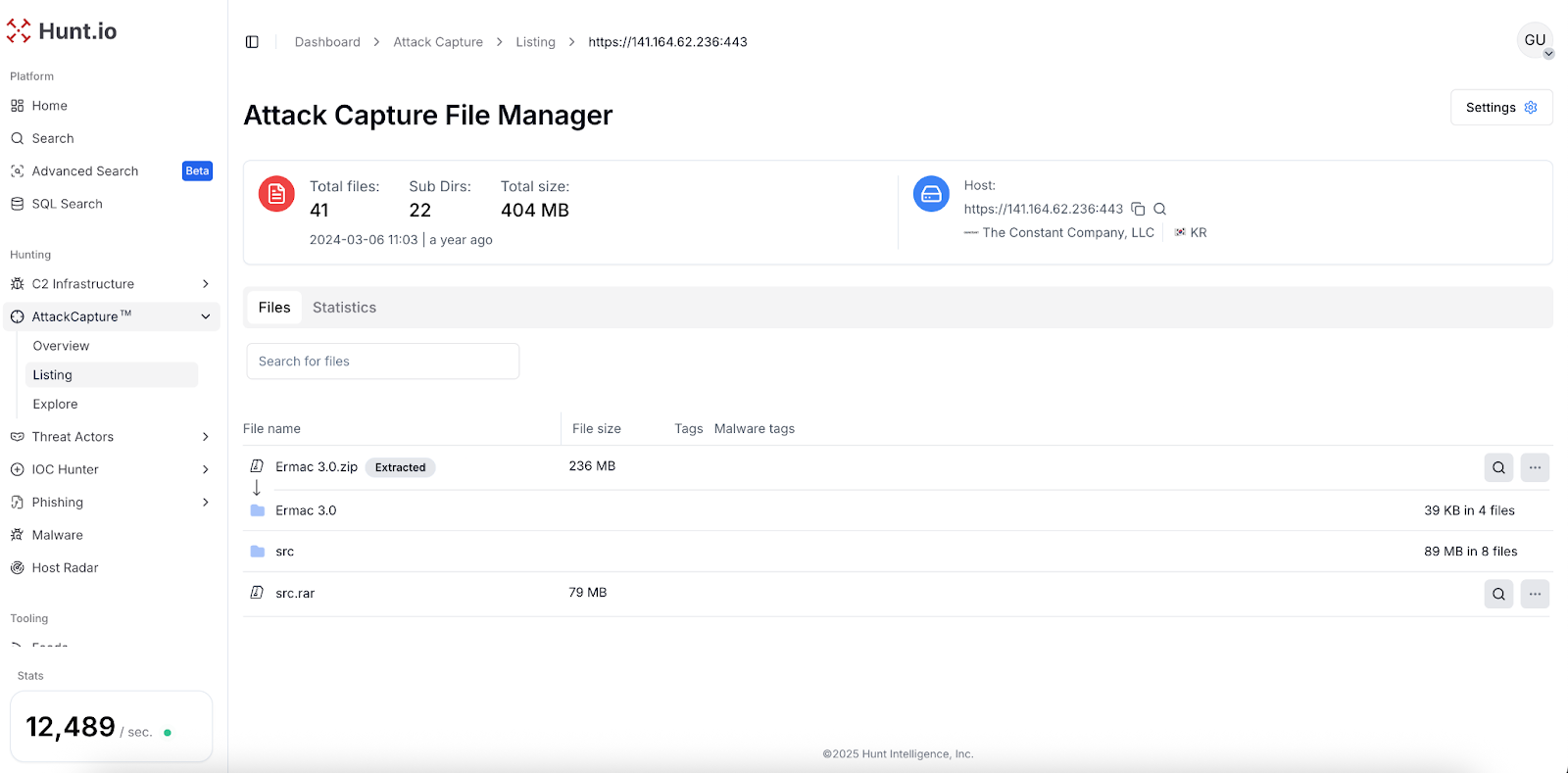
- Hunt.io discovered an open directory containing Ermac 3.0.zip with the complete ERMAC V3.0 source code on 141[.]164[.]62[.]236:443.
- ERMAC V3.0 components include a PHP Laravel backend, React frontend panel, Golang exfiltration server, and an Android builder/backdoor using AES-CBC encryption.
- Version 3.0 expands targeting to 700+ financial, shopping, and cryptocurrency apps via form injection overlays served from the backend’s public/injects directory.
- Leak analysis revealed critical vulnerabilities: hardcoded JWT secret, static admin bearer token, default root credentials (changemeplease), and open admin account registration.
- HuntSQL analysis linked leaked source code to live infrastructure (C2 panels, exfiltration servers, builder panels) with multiple IPs identified (e.g., 43[.]160[.]253[.]145, 91[.]92[.]46[.]12).
- The Android backdoor supports extensive commands (SMS, USSD, overlays, file manager, front-camera capture) and evasion (geofencing, emulator checks, obfuscation, disabling Play Protect).
- Mitigations include blocking identified infrastructure, scanning for ERMAC traits (ermac_session cookie, panel titles, hardcoded nonce), and strengthening mobile app defenses against overlays.
MITRE Techniques
- [T1204] User Execution – ERMAC is executed through user interaction (“ERMAC is executed through user interaction”).
- [T1059] Command and Scripting Interpreter – Uses WebView components to execute remote JavaScript from its C2 server for data collection (“ERMAC uses WebView components to execute remote JavaScript from its C2 server, for data collection.”).
- [T1053] Scheduled Task/Job – Uses StartReceiver to schedule callbacks to maintain persistence (“Uses StartReceiver to schedule callbacks to maintain persistence.”).
- [T1543] Create or Modify System Process (Service) – Uses ActivityManager to ensure service stays online (“ERMAC uses ActivityManager to ensure service stays online.”).
- [T1412] Mobile SMS Control – Uses Android intents to intercept and control SMS messages (“Uses Android intents to intercept and control SMS messages.”).
- [T1548] Abuse Elevation Control Mechanism (Elevated Execution with Prompt) – Requests Device Administrator privileges to lock the screen and prevent uninstallation (“Requests Device Administrator privileges to lock the screen and prevent uninstallation.”).
- [T1048] Encrypted Channel – All communication with the C2 server is encrypted using AES (“All communication with the C2 server is encrypted using AES, which prevents network-level detection of commands and exfiltrated data.”).
- [T1036] Masquerading – Deletes its launcher icon after first run to hide presence (“ERMAC deletes its launcher icon after the first run to hide its presence on the device.”).
- [T1027] Obfuscated Files or Information – Strings and variable names are obfuscated with Russian text and Base64 to hinder static analysis (“Strings and variable names are obfuscated with Russian text and Base64 encoding to hinder static analysis.”).
- [T1497] Virtualization/Sandbox Evasion – Checks for emulation to prevent analysis (“Checks for emulation to prevent analysis.”).
- [T1499] Geofencing – Blocks execution in CIS countries to avoid prosecution (“Blocks [ua][ru][by][tj][uz][tm][az][am][kz][kg][md] from running the malware.”).
- [T1405] Disable or Modify System Firewall (via Accessibility) – Uses Accessibility Services to disable Google Play Protect (“Using Accessibility Services, ERMAC disables Google Play Protect to reduce the likelihood of being detected and removed.”).
- [T1056] Input Capture (Keylogging) – Includes a keylogger to capture user input across applications (“Includes a keylogger functionality to capture user input across all applications.”).
- [T1598] GUI Input Capture (Form Injection) – Utilizes form injection overlays to capture credentials and form data (“Utilizes form injection to capture form data from Android applications.”).
- [T1402] Access Notification – Intercepts incoming SMS to steal 2FA codes (“Intercepts incoming SMS messages to steal sensitive information like two-factor authentication (2FA) codes.”).
- [T1087] Account Discovery – Gathers a list of all user accounts on the device (“Gathers a list of all user accounts on the device.”).
- [T1083] File and Directory Discovery – Built-in file manager allows browsing and downloading files (“A built-in file manager module allows the attacker to browse the device’s file system and download files.”).
- [T1113] Screen Capture / Video Capture – Can remotely take photos using the front camera (“It can remotely take photos using the front camera without the user’s knowledge.”).
- [T1071] Application Layer Protocol – Communicates with its C2 server over HTTP/S (“Communicates with its C2 server over HTTP/S.”).
- [T1041] Exfiltration Over C2 Channel – All collected data is sent to the attacker using the primary C2 channel (“All collected data, including credentials, contacts, and files, is sent to the attacker using the primary C2 channel.”).
Indicators of Compromise
- [IP Address] ERMAC panels and servers – 43[.]160[.]253[.]145 (panel/exfiltration/C2), 91[.]92[.]46[.]12 (panel).
- [IP Address] Additional C2/exfil servers – 121[.]127[.]231[.]163:8082, 121[.]127[.]231[.]198:8082 (exfiltration servers) and 172[.]191[.]69[.]182:8089 (C2 server).
- [Filename] Source archive and binary – Ermac 3.0.zip (ERMAC Source Code), server_go (compiled exfiltration server, SHA-256 8c81cebb…d545).
- [File Hash] Source and binary hashes – Ermac 3.0.zip SHA-256 175d4adc5fc0…992aaa (source code), server_go SHA-256 8c81cebbaff9…d545 (exfil server).
- [Cookie/Header] ermac_session cookie and Basic auth realm – ermac_session cookie used by C2 APIs; Www-Authenticate: Basic realm=”LOGIN | ERMAC” on exfiltration servers.
Read more: https://hunt.io/blog/ermac-v3-banking-trojan-source-code-leak