Threat actors continue exploiting Fortinet SSL‑VPN vulnerabilities CVE-2022-42475, CVE-2023-27997, and CVE-2024-21762 to gain unauthenticated remote code execution and persist on FortiGate devices. Darktrace observed HTTP-based exploitation, internal scanning, credential abuse, and RDP access, with Autonomous Response blocking connections and containing the incident. #CVE-2022-42475 #CVE-2024-21762
Keypoints
- Three Fortinet SSL‑VPN vulnerabilities (CVE-2022-42475, CVE-2023-27997, CVE-2024-21762) enable unauthenticated remote code execution against FortiOS/FortiProxy.
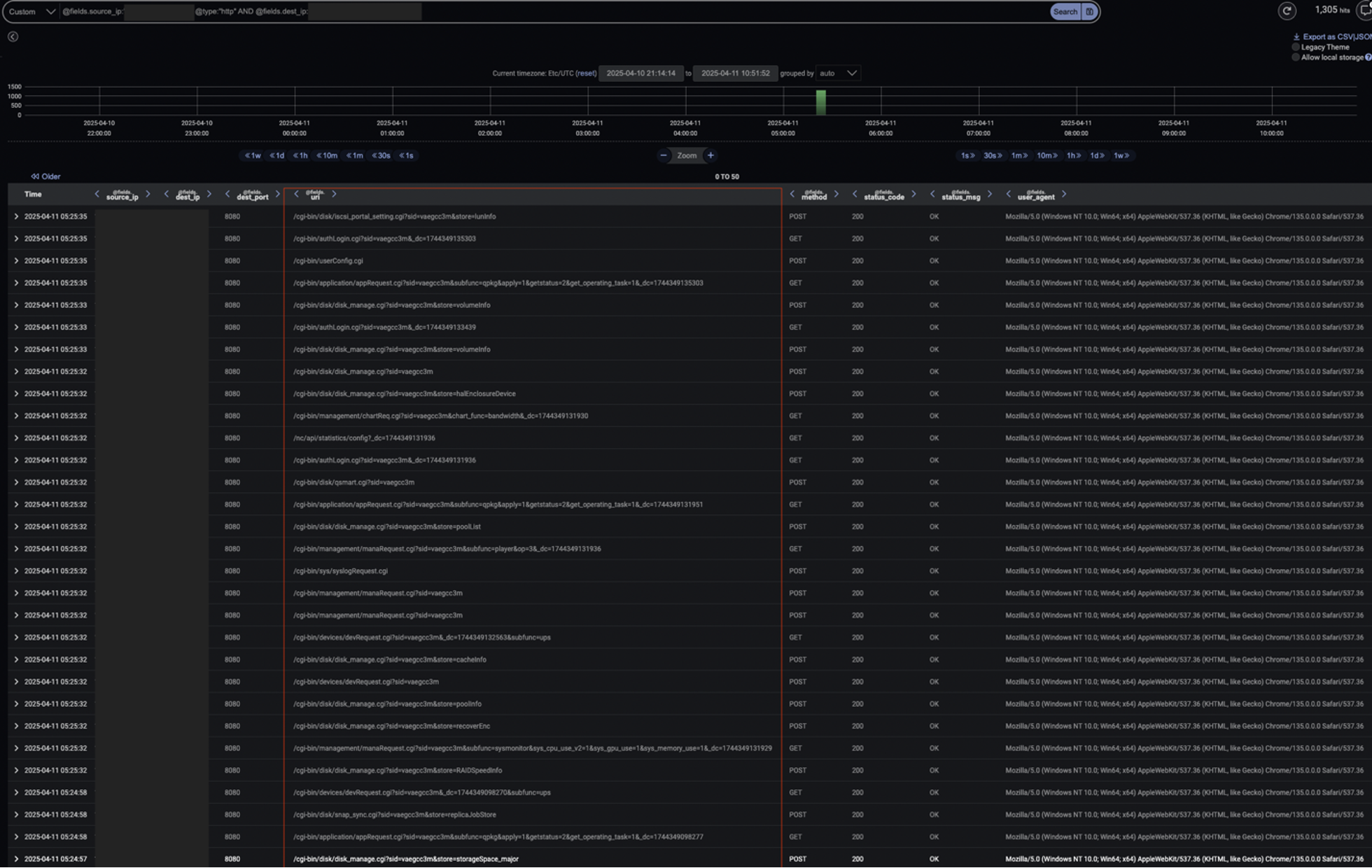
- Attackers exploited these CVEs to gain initial access to a customer Fortinet VPN device, sending high volumes of HTTP requests to /cgi-bin/ over port 8080.
- Post‑exploit activity included internal network scanning (Nmap), SMB/NTLM credential probing, DCE_RPC enumeration, and large numbers of Netlogon requests indicating brute‑force or credential testing.
- Threat actors established persistence via symbolic link abuse in SSL‑VPN language file directories and likely modified firewall rules to maintain long‑term access.
- Lateral movement led to prolonged RDP sessions without cookies, significant data transfer, and probing of FTP/SSH/Telnet/HTTP(S) and administrative ports (135, 137, 389, 445, 3389).
- Darktrace’s real‑time models detected anomalous behaviors and its Autonomous Response blocked suspicious connections and enforced device patterns of life to contain the attack.
- Incident underscores the importance of timely patching and continuous monitoring of internet‑facing VPN infrastructure despite available fixes.
MITRE Techniques
- [T1133] External Remote Services – Exploited Fortinet SSL‑VPN vulnerabilities to gain initial external access (“exploitation of a Fortinet VPN device running an outdated version of FortiOS”).
- [T1078] Valid Accounts – Used NTLM/SMB authentication with accounts like ‘anonymous’ and ‘guest’ for access and escalation (“successful NTLM authentication from the internal firewall interface to the domain controller… using the account ‘anonymous’”).
- [T1203] Exploitation for Client Execution – Remote code execution via memory corruption in SSL‑VPN components (heap buffer overflows/out‑of‑bounds writes) to run attacker code (“send specially crafted HTTP requests that write data outside of allocated memory bounds”).
- [T1098] Account Manipulation – Persistence via symbolic link abuse in SSL‑VPN language file directories to maintain footholds (“deploy symbolic links in the SSL‑VPN language file directory on the Fortinet device”).
- [T1071.001] Application Layer Protocol – Malicious HTTP traffic to /cgi-bin/ and over port 8080 used for exploitation and command activity (“high volume of HTTP traffic… many of these requests were directed at the /cgi-bin/ directory”).
- [T1068] Exploitation for Privilege Escalation – Post‑compromise exploitation and service enumeration to elevate privileges (DCE_RPC and Netlogon activity consistent with escalation attempts: “DCE_RPC service enumeration… over 300 requests to the Endpoint Mapper”).
- [T1036] Masquerading – Use of self‑signed/invalid SSL certificates and stealthy RDP sessions to evade detection (“SSL certificate validation failures on port 3389, indicating… self-signed or invalid certificates”).
- [T1110] Brute Force – Repeated authentication attempts and Netlogon requests suggesting credential brute‑forcing (“over 300 Netlogon requests to the domain controller… just over half of these connections were successful”).
- [T1046] Network Service Scanning – Internal network scanning with Nmap to discover services and targets (“use of Nmap to probe the internal environment”).
- [T1018] Remote System Discovery – Enumeration and service probing of internal systems following VPN compromise (“more than 1,700 outbound connections… targeted common services such as FTP, SSH, Telnet, HTTP, and HTTPS”).
- [T1021] Remote Services – Lateral movement via RDP and other remote services to access internal hosts (“initiated an RDP session from the internal firewall interface device to an internal server”).
- [T1072] Software Deployment Tools – Use of tools like Nmap and remote services for propagation and reconnaissance (“Nmap for enumeration and brute-force attempts”).
- [T1005] Data from Local System – Collection activity during RDP sessions and local data access implied by uploads/downloads (“more than 1.5MB of data was uploaded and over 5MB was downloaded”).
- [T1074] Data Staging – Preparation of collected data prior to exfiltration implied by observed activity and staging behaviors (post‑exploitation data movement patterns observed during sessions).
- [T1048] Exfiltration Over Alternative Protocol – Potential exfiltration via RDP/other channels during prolonged sessions and outbound connections (significant data transfers during RDP session).
Indicators of Compromise
- [Vulnerabilities] exploited CVEs – CVE-2022-42475, CVE-2023-27997, CVE-2024-21762 (FortiOS/FortiProxy SSL‑VPN vulnerabilities).
- [HTTP endpoints] suspicious request targets – repeated requests to /cgi-bin/ over port 8080 observed from compromised Fortinet device.
- [Accounts/credentials] authentication context – use of ‘anonymous’ and ‘guest’ accounts during NTLM/SMB authentication attempts.
- [Network activity] scanning and ports probed – Nmap scans and >1,700 outbound connections targeting FTP(21), SSH(22), Telnet(23), HTTP(80), HTTPS(443), RDP(3389), and services on ports 135, 137, 389, 445.
- [Persistence artifacts] filesystem manipulation – symbolic link creation in SSL‑VPN language file directories (Fortinet‑identified persistence technique).