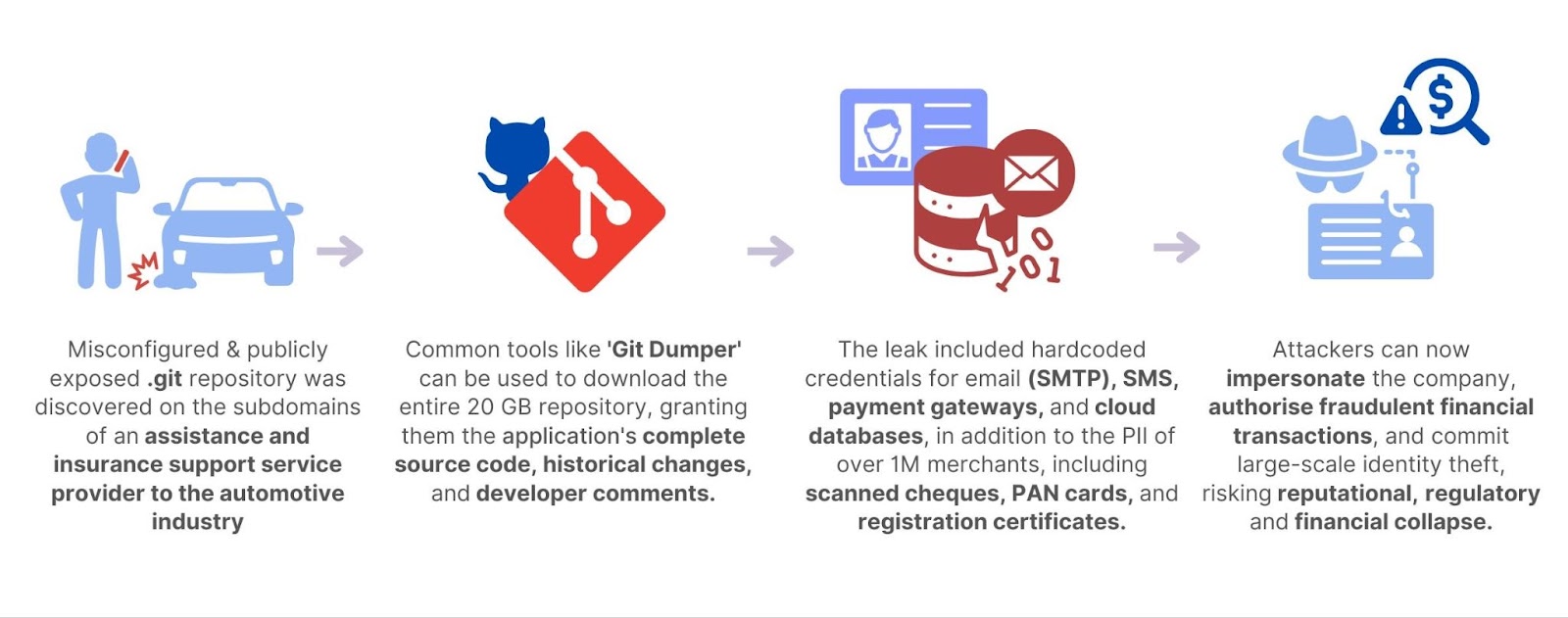
CloudSEK’s SVigil discovered a publicly accessible .git repository in a roadside assistance and insurance support vendor that exposed over 20 GB of sensitive data, including full source code, credentials, customer PII, and financial documents. The exposure enabled trivial extraction (e.g., with Git Dumper) and risked phishing, SMS impersonation, payment fraud, database compromise, identity theft, and broad supply-chain impacts. #SVigil #GitDumper
Keypoints
- SVigil detected a publicly accessible .git folder on two vendor subdomains, exposing the repository and revision history.
- Over 20 GB of confidential data was exposed, including full source code for e-portals and hardcoded secrets (SMTP, SMS gateway, payment tokens, cloud DB credentials).
- Personal and financial records for thousands were leaked: ~6,700 merchants/customers, 6,000 cancelled cheques, 6,000 tax certificates, and over 2,000 PAN cards.
- Attackers could easily retrieve the repo using tools like Git Dumper, enabling source-code theft and secret harvesting with minimal skill.
- Compromise risks include large-scale phishing/SMS impersonation, unauthorized transactions, credential stuffing, identity theft, and document forgery.
- Business impacts include reputational damage, regulatory exposure, operational disruption, and financial loss across automotive partners and insurers.
- Recommended mitigations: remove exposed development artifacts, rotate and secure credentials, continuously monitor vendors, and adopt proactive detection (like SVigil).
MITRE Techniques
- [T1609] Active Scanning – Scanners (SVigil) identified publicly accessible .git folders by scanning vendor subdomains (“SVigil flagged a critical vulnerability on two key subdomains belonging to the vendor: a publicly accessible .git folder.”).
- [T1218] Signed Binary Proxy Execution – Use of readily available tooling (e.g., Git Dumper) to retrieve git objects and reconstruct files (“An attacker could utilize a readily available tool, such as Git Dumper, to retrieve the git object and decompress it into individual files.”).
- [T1531] Account Discovery – Extraction of hardcoded credentials and tokens from source code to enumerate and access email, SMS, payment, and cloud DB services (“Hardcoded directly within this code were critical secrets, including: Email (SMTP) Credentials… SMS Gateway Secrets… Payment Gateway Tokens… Cloud Database Credentials.”).
- [T1078] Valid Accounts – Use of exposed service credentials (SMTP/SMS/payment/cloud) to impersonate legitimate communications and perform transactions (“Credentials for multiple SMTP service providers were exposed, allowing attackers to send emails as the company… SMS Gateway Secrets… payment gateway tokens…”).
- [T1530] Data from Information Repositories – Exfiltration of source code, revision history, and stored documents from the exposed .git repository (“The exposed .git folder… contained the entire source code and its revision history… exposed over 20 GB of confidential data…”).
- [T1586] Compromise Infrastructure – Potential compromise of cloud database infrastructure using exposed cloud DB credentials (“Credentials for the company’s leading cloud service provider’s Relational Database Service were exposed, risking a complete compromise of their cloud database infrastructure.”).
Indicators of Compromise
- [Exposed Repository] public .git folder – accessible .git directories on two vendor subdomains (exposed via internet scan).
- [Tooling] attack method – Git Dumper mentioned as a tool to extract repository contents (“Git Dumper”).
- [Credentials] hardcoded secrets – SMTP credentials, SMS gateway secrets, payment gateway tokens, cloud DB credentials (examples described in text; specific values not provided).
- [Documents] sensitive files – cancelled cheques and service tax certificates (e.g., ~6,000 cheques, ~6,000 tax certificates) and scanned PAN cards (~2,000) associated with merchants/customers.
- [Data Volume] dataset size – over 20 GB of exposed data containing source code, PII, and financial records.