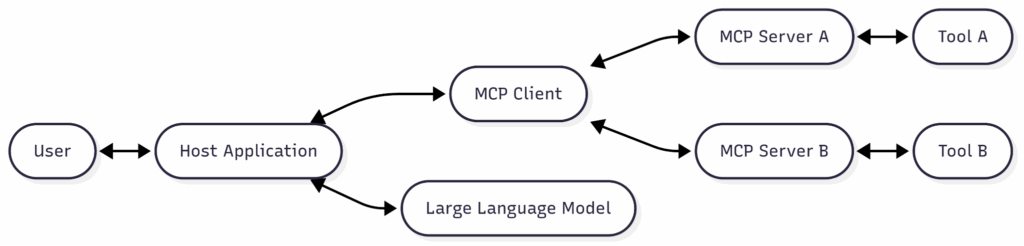
The Model Context Protocol (MCP) standardizes LLM access to external tools and data, enabling powerful integrations but introducing supply-chain and runtime security risks such as tool poisoning, session hijacking, cross‑server manipulation, ANSI escape injection, and typosquatting. The post outlines MCP architecture, common transports and flows, real-world use cases, and recommended priorities for stronger authentication, governance, and monitoring. #ModelContextProtocol #ANSIescape
Category: Threat Research

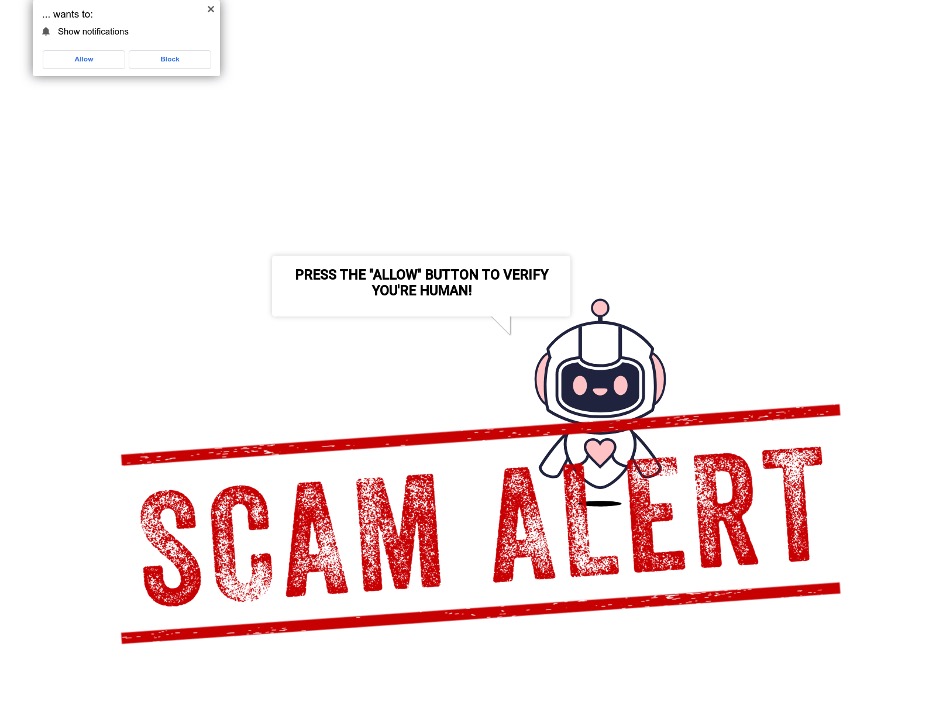
Researchers observed a ClickFix phishing campaign targeting macOS that delivers an AppleScript-based stealer (Odyssey Stealer) via a fake CAPTCHA and terminal “base64 -d | bash” command, harvesting browsers, crypto wallets, Keychain items, and files before exfiltrating to a remote server. IOCs and protections show the infrastructure centered on 45.146.130[.]131 and the phishing domain tradingviewen[.]com. #OdysseyStealer #tradingviewen #45.146.130.131

MCP (Model Context Protocol) servers, which mediate AI access to internal resources, are vulnerable to DNS rebinding attacks that can bypass same-origin protections and expose internal APIs, data, and credentials. Defenses include network segmentation, host/IP validation, mTLS, DNSSEC, application allowlists, monitoring for rapid DNS changes, and incident response procedures. #ModelContextProtocol #DNSRebinding…
REVENANT describes a five-stage, fileless attack methodology that persists across endpoints, application UI resources, clipboard history, AI model context, and telemetry channels to evade traditional detection. The research demonstrates how font downloads, clipboard sequences, localization tampering, AI prompt poisoning, and crash-report exfiltration can be chained to achieve stealthy persistence and covert data transfer. #REVENANT #Tesseract
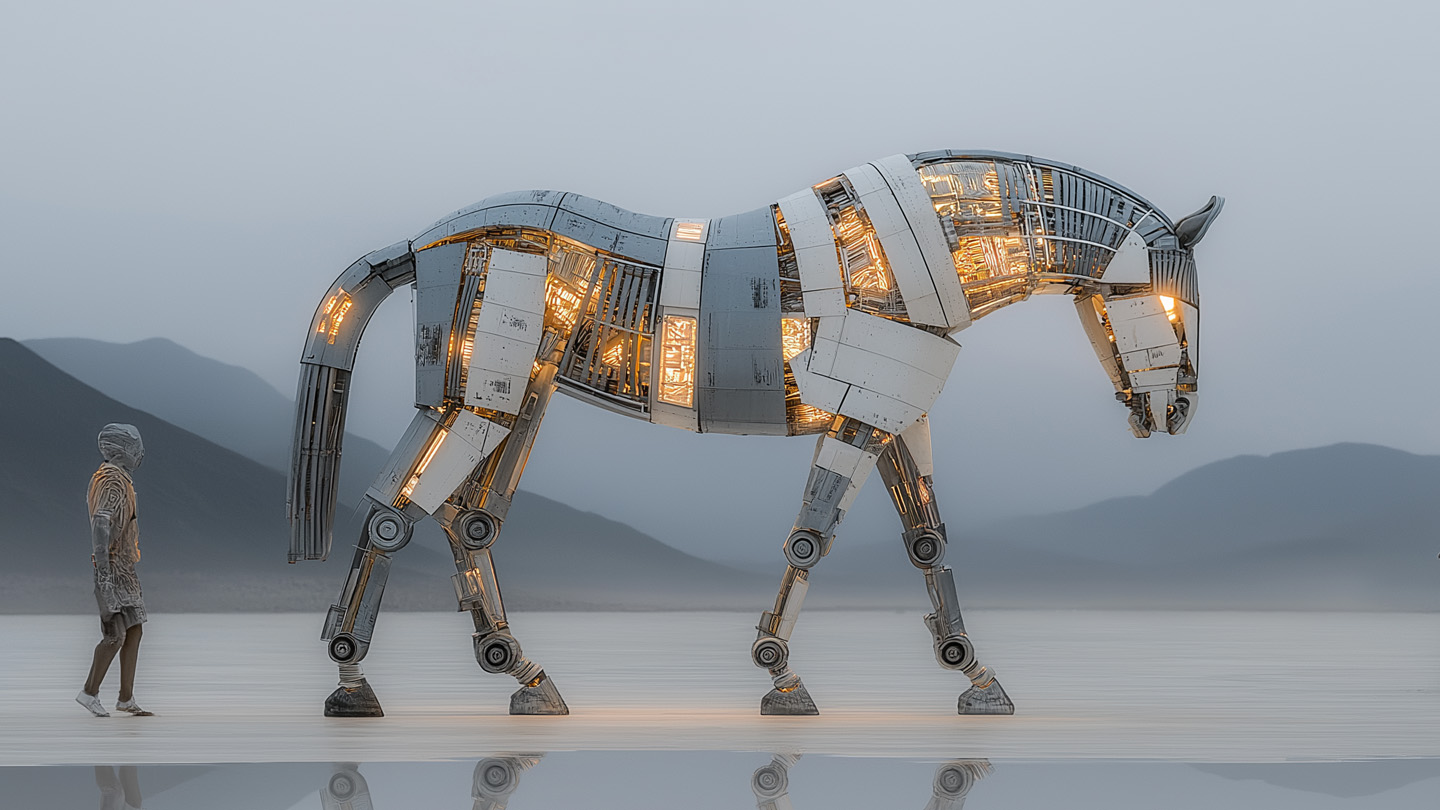
Trojan-style backdoors are resurging because AI/LLMs let threat actors cheaply generate convincing decoy apps, websites, and novel code that evade static multiscanner detection. Examples include JustAskJacky and TamperedChef, which use scheduled tasks, remote command execution, and steganographic command delivery. #JustAskJacky #TamperedChef
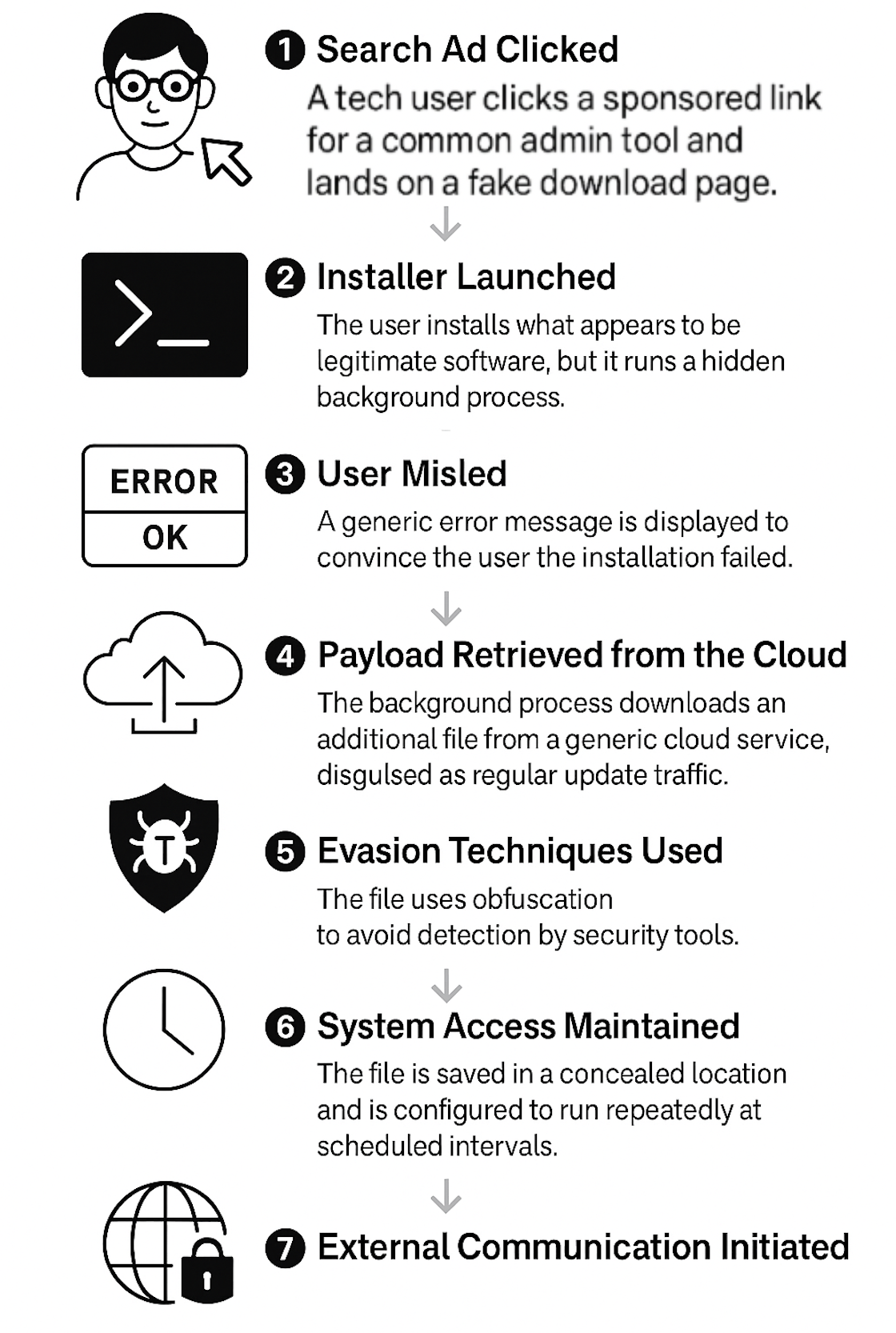
Oyster returned in July 2025 with a stealthier, modular loader delivered via malvertising that spoofed PuTTY and used a compromised real estate site to host a trojanized installer, fetching a second-stage DLL from a cloud CDN and maintaining persistence via a scheduled task. The campaign features AV evasion through GDI noise, cloud-based C2 traffic, hardcoded IP 45[.]86[.]230[.]77, and indicators including putty[.]us[.]com and skyviberealty[.]com. #Oyster #Rhysida

The Lazarus Group is a long-running, state-sponsored North Korean APT that conducts both espionage and large-scale financially motivated attacks, notably targeting cryptocurrency platforms, regional software, and supply chains. Recent campaigns include the Bybit $1.5B heist, Operation SyncHole watering‑hole infections using ThreatNeedle, and supply‑chain “Phantom Circuit” code‑injection attacks. #ThreatNeedle #Bybit
VexTrio operates a large-scale fraud enterprise centered on smartlink-driven scams, spam distribution, and scam apps that impersonate legitimate brands and services. Their operations include affiliated ad networks, fake VPNs and spam‑blocker apps, and extensive DNS/mail infrastructure tying domains like datingcell[.]com and mail.holaco[.]de to their campaigns. #VexTrio #datingcell[.]com #mail.holaco[.]de
FIDO-based passkeys greatly reduce credential phishing and ATO risks, but Proofpoint researchers show attackers can force a downgrade from FIDO to weaker authentication using a tailored AiTM phishlet. While not observed in the wild yet, this technique could enable session cookie theft and account takeover, particularly via Evilginx-style frameworks. #FIDO #Evilginx…
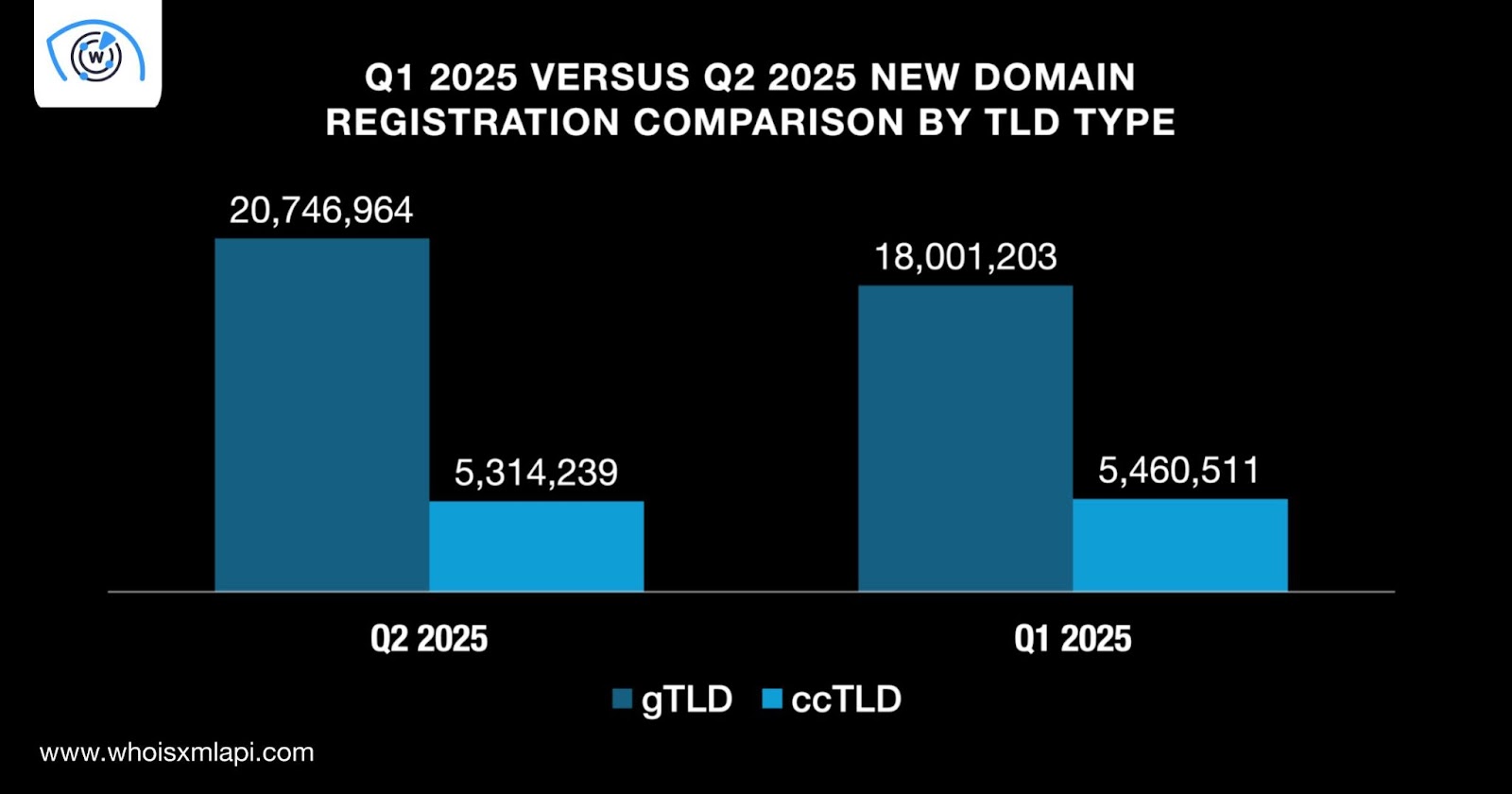
The Q2 2025 Global Domain Activity Report analyzed 26.0+ million newly registered domains, noting an 11.0% increase from Q1 2025 and identifying 3.9+ million domains tagged as indicators of compromise. Key findings include .com dominating both NRDs and IoC volumes, .cc showing extreme NRD-per-capita incongruence, and GoDaddy, Namecheap, and Dynadot topping registrar market share. #GoDaddy #CocosKeelingIslands
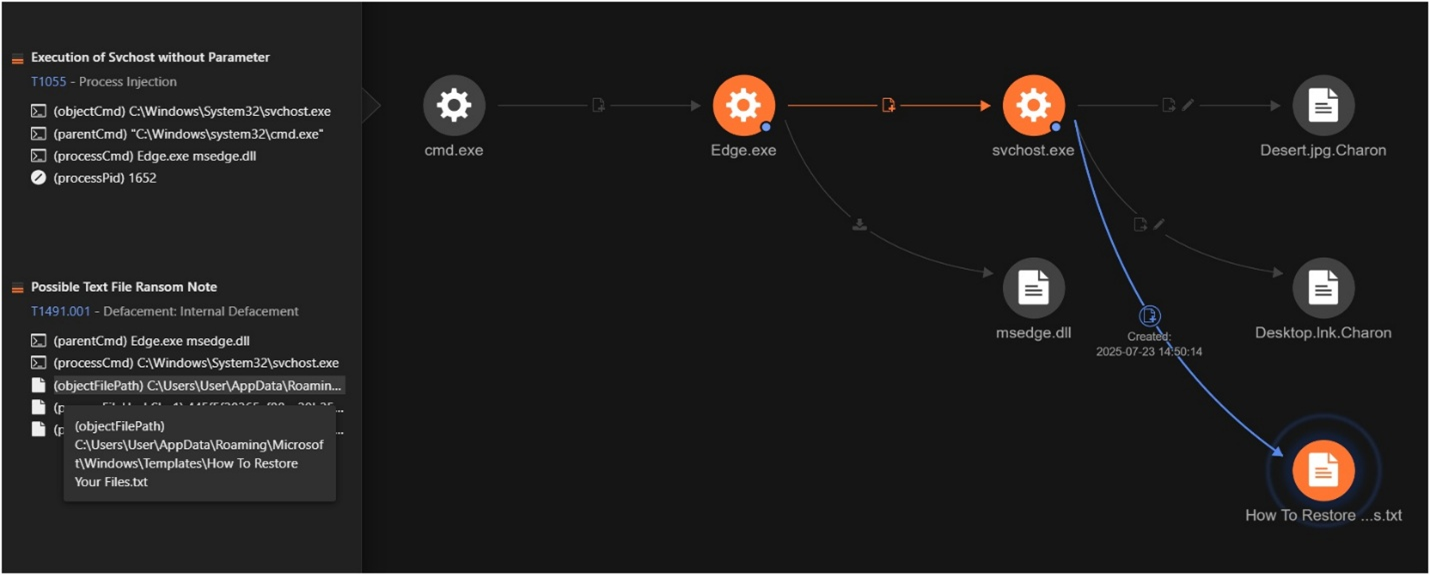
Trend Research discovered a targeted campaign using a newly observed ransomware family named Charon that employs APT-style techniques like DLL sideloading, process injection, and anti-EDR capabilities to deliver customized ransom demands. The campaign impacted Middle East public sector and aviation targets and shows technical overlap with Earth Baxia toolchains but lacks…

The campaign used compromised internal email and a spoofed Teams page to trick Israeli victims into running a multi-stage, fully PowerShell-based loader that delivered a PowerShell RAT. The malware communicated with hxxps[:]//pharmacynod[.]com for C2, victim registration, command polling, and exfiltration. #pharmacynod #MuddyWater

AhnLab ASEC found SmartLoader being widely distributed via GitHub repositories disguised as legitimate projects (game cheats, cracks, automation tools), where users download compressed files that deploy SmartLoader and additional payloads like Rhadamanthys. Infected systems persist via Task Scheduler, exfiltrate screenshots/system info, and fetch further loaders/tasks from C2 servers. #SmartLoader #Rhadamanthys…

Cyble tracked 717 new vulnerabilities from July 30–Aug 5, 2025, including 222 with public PoCs, 17 in EOL products, one zero-day, and multiple exploits traded on underground forums. High-impact flaws affect vendors and products such as Trend Micro Apex One, D-Link, Microsoft SharePoint, Adobe AEM, SonicWall SMA, and Google/Apple browser engines. #TrendMicroApexOne #D-Link #CVE-2025-53770 #CVE-2025-54253

CastleLoader is a modular malware loader that has infected 469 devices since May 2025 by using Cloudflare-themed ClickFix phishing pages and fake GitHub repositories to trick victims into executing malicious PowerShell or installers. It delivers multiple payloads including StealC, RedLine, NetSupport RAT, DeerStealer, HijackLoader, and SectopRAT, and has targeted U.S. government entities. #CastleLoader #StealC #RedLine #NetSupportRAT #DeerStealer #HijackLoader #SectopRAT