Trend Research discovered a targeted campaign using a newly observed ransomware family named Charon that employs APT-style techniques like DLL sideloading, process injection, and anti-EDR capabilities to deliver customized ransom demands. The campaign impacted Middle East public sector and aviation targets and shows technical overlap with Earth Baxia toolchains but lacks definitive attribution. #Charon #EarthBaxia
Keypoints
- Trend Research identified Charon, a new ransomware family deployed in targeted attacks against Middle East public sector and aviation organizations.
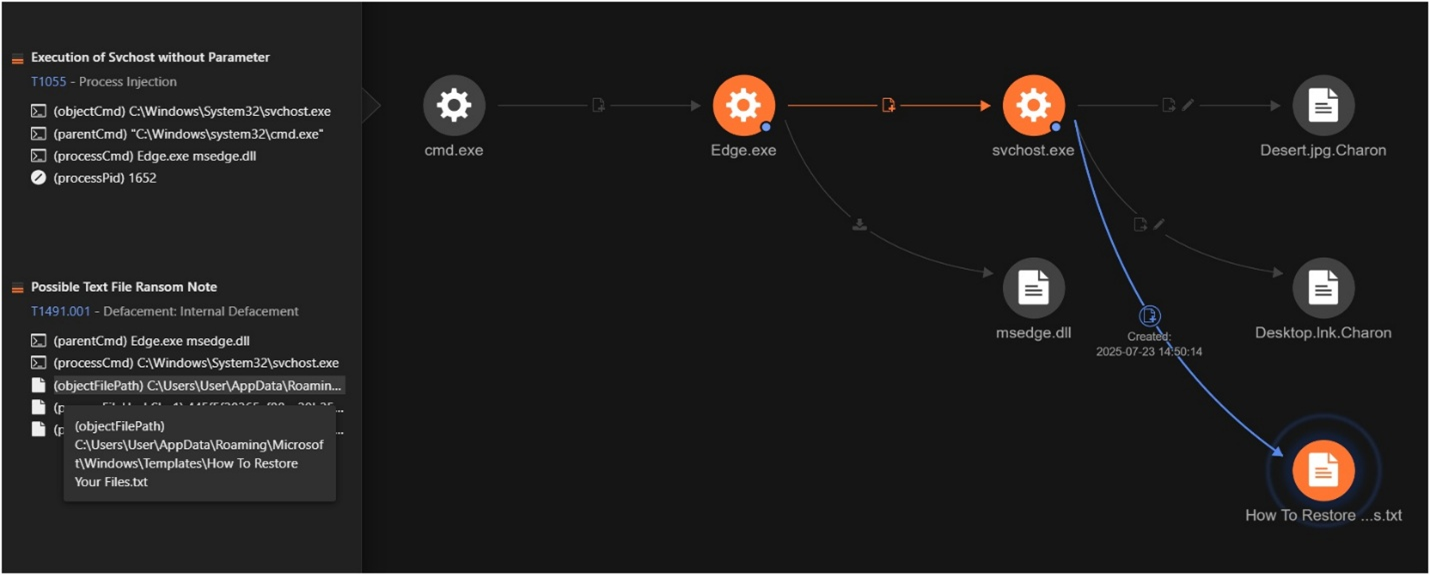
- Attack chain uses DLL sideloading of msedge.dll (SWORDLDR) via a legitimate Edge.exe binary to load encrypted shellcode from DumpStack.log.
- Charon performs multistage decryption to extract a final PE ransomware payload and injects it into svchost.exe for execution.
- Ransomware includes advanced features: shared-secret Curve25519 + ChaCha20 hybrid encryption, partial-file encryption strategy, multithreaded encryption, and customized victim-specific ransom notes.
- Operational tactics include stopping security services, terminating processes, deleting shadow copies, emptying the Recycle Bin, and network share enumeration/propagation.
- Evidence shows technical convergence with Earth Baxia toolchains (DLL sideloading pattern) but insufficient infrastructure/targeting overlap for definitive attribution.
- Binary contains an embedded anti-EDR driver (Dark-Kill project) stored in data section but dormant in this variant, suggesting future capability expansion.
MITRE Techniques
- [T1073] DLL Side-Loading – A legitimate Edge.exe is abused to load a malicious msedge.dll (“SWORDLDR”) which decrypts and loads the ransomware payload. Quote: ‘…abused to sideload a malicious DLL named msedge.dll (SWORDLDR)…’
- [T1055] Process Injection – The loader decrypts the payload and injects Charon into a newly spawned svchost.exe process to masquerade as a service. Quote: ‘…injecting it into a newly spawned svchost.exe process…’
- [T1486] Data Encrypted for Impact – Charon encrypts files with a .Charon extension, appends a 72-byte footer with the victim’s public key, and drops a ransom note. Quote: ‘…appends the .Charon extension…writes the infection marker…drops “How To Restore Your Files.txt”…’
- [T1112] Modify Registry or System Image (Driver Installation) – Attempts to drop and register an anti-EDR driver WWC.sys under System32Drivers and register it as a service (dormant in this variant). Quote: ‘…attempts to drop this driver as %SystemRoot%System32DriversWWC.sys and register it as the “WWC” service…’
- [T1490] Inhibit System Recovery – Deletes shadow copies and empties the Recycle Bin to prevent recovery. Quote: ‘…systematically deletes all shadow copies on the system…also empties the contents of the Recycle Bin…’
- [T1021] Remote Services / Lateral Movement via Network Shares – Scans and encrypts accessible network shares using NetShareEnum and WNetEnumResource, processing mapped drives and UNC paths while skipping ADMIN$. Quote: ‘…actively scanning for and encrypting accessible network shares across the infrastructure via NetShareEnum and WNetEnumResource…skips ADMIN$ shares…’
Indicators of Compromise
- [File Name] loader and payload components – msedge.dll (SWORDLDR), DumpStack.log, Edge.exe (originally cookie_exporter.exe)
- [File Name] ransomware artifacts – Encrypted files with .Charon extension, ransom note “How To Restore Your Files.txt”, infection marker “hCharon is enter to the urworld!”
- [Registry/Service/Driver] anti-EDR driver path and service – %SystemRoot%System32DriversWWC.sys (service name “WWC”) – driver present in binary but dormant
- [Technique/Behavior] mutex name – OopsCharonHere (used to prevent multiple instances)
- [Network/Enumeration] network enumeration APIs – use of NetShareEnum and WNetEnumResource to discover and encrypt network shares (mapped drives and UNC paths)
Read more: https://www.trendmicro.com/en_us/research/25/h/new-ransomware-charon.html