Cmimai Stealer is a VBS-based infostealer first observed in June 2025 that uses Visual Basic scripting and spawned PowerShell scripts to collect system information via WMI, gather browser profile metadata, capture screenshots, and exfiltrate collected data to attackers using Discord webhooks. The sample logs activity in the %TEMP% folder, repeatedly runs every 60 minutes for persistent data collection, uses HTTPS with a unique User-Agent, lacks advanced features like restart persistence or built-in browser decryption, and includes identifiable filenames and hashes for detection. #CmimaiStealer #Discord
Keypoints
- Cmimai Stealer is a VBS (Visual Basic Script) infostealer observed in June 2025 that leverages native Windows scripting and PowerShell for operations.
- The malware collects system information by querying WMI (Win32_OperatingSystem) and records events to vbs_reporter_log.txt in the %TEMP% folder.
- It spawns PowerShell scripts (notably vbs_ps_browser.ps1 and vbs_ps_diag.ps1) to gather browser profile metadata and capture screenshots using .NET assemblies, compressing images to stay under Discord’s 8MB limit.
- Exfiltration is performed via Discord webhooks (JSON over HTTPS) using WinHttpRequest or MSXML, and traffic includes a distinct User-Agent string “Cmimai Stealer VBS UI Rev”.
- Persistence is implemented as an endless loop that runs every 60 minutes (timed execution), but the sample lacks persistence across system restart and does not perform encrypted command-and-control.
- Defensive indicators include specific filenames, PowerShell command lines, temp image files (vbs_diag_*.png/.jpg), webhook URLs to discord.com/api/webhooks, and two known sample hashes.
- The stealer does not currently decrypt browser-stored credentials in this sample but can be used for reconnaissance or as a second-stage tool for future attacks.
MITRE Techniques
- [T1059.001 ] PowerShell – Used to create and run helper scripts for browser metadata and screenshot capture. (‘creates and runs a PowerShell script “vbs_ps_browser.ps1″‘)
- [T1059.005 ] Visual Basic – Primary delivery and execution through VBS scripts executed with wscript.exe. (‘VBS (Visual Basic Script) infostealer’)
- [T1047 ] Windows Management Instrumentation – Collected OS version, caption, username, and computer name via WMI queries. (‘querying the Windows Management Instrumentation (WMI) Win32_OperatingSystem class.’)
- [T1113 ] Screen Capture – Captured screenshots using .NET assemblies, converting to 70% quality JPEG for exfiltration. (‘takes the screenshot, converts it to a 70% quality JPEG’)
- [T1555.003 ] Credentials from Web Browsers – Parsed Chromium “Local State” to collect profile names and user emails and identified encrypted_key/master key material (no decryption performed in sample). (‘attempting to parse the Local State JSON file’)
- [T1567.002 ] Exfiltration over Web Service – Staged and sent stolen data in JSON to a configured Discord webhook. (‘sends stolen data to the configured Discord webhook in a JSON object’)
- [T1071.001 ] Application Layer Protocol: Web Protocols (HTTPS) – Used HTTPS calls (WinHttpRequest/MSXML) to transmit data to discord.com/api/webhooks. (‘uses HTTPS to send stolen data to discord.com/api/webhooks/…’)
Indicators of Compromise
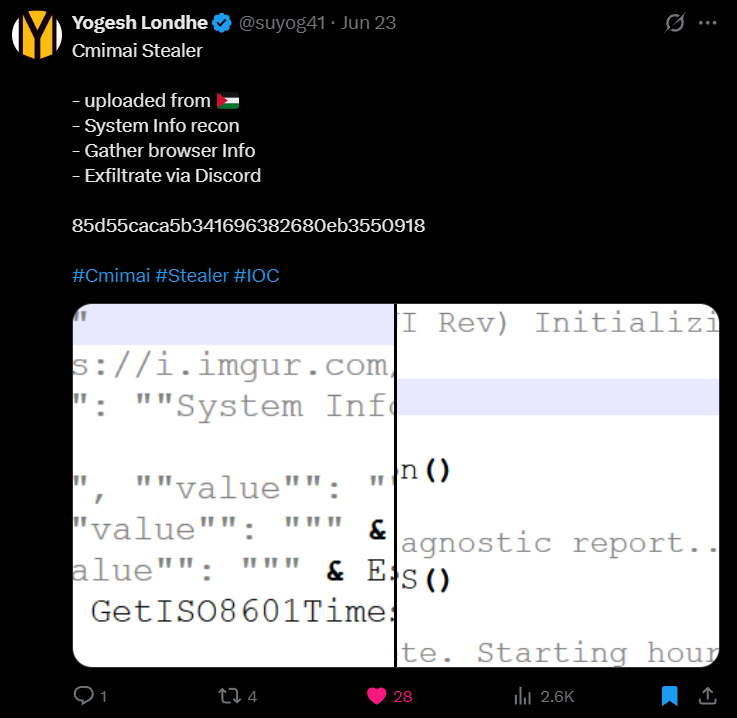
- [File Hashes ] sample identifiers – 85d55caca5b341696382680eb3550918, ea792d0458d40471cefa26ebccf4ed45
- [File Names ] suspicious helper and output files – vbs_ps_browser.ps1, vbs_ps_diag.ps1
- [Log / Temp Files ] local logging and artifacts – vbs_reporter_log.txt, ps_browser_log.txt
- [Image Files ] screenshot artifacts in temp – vbs_diag_*.png, vbs_diag_*.jpg
- [Domains / Webhook URLs ] exfiltration endpoints – discord.com/api/webhooks/… (configured webhook URLs observed)
- [User-Agent ] network fingerprint – “Cmimai Stealer VBS UI Rev” used in HTTP requests
- [Command Lines ] PowerShell execution patterns – ‘…powershell.exe -NoProfile -ExecutionPolicy Bypass -WindowStyle Hidden -File “…Tempvbs_ps_browser.ps1″‘, ‘…powershell.exe -NoProfile -ExecutionPolicy Bypass -WindowStyle Hidden -File “…Tempvbs_ps_diag.ps1″‘
Read more: https://labs.k7computing.com/index.php/silent-watcher-dissecting-cmimai-stealers-vbs-payload/