ENHANCED STEALTH WALLETDRAINER is a malicious NPM package (@kodane/patch-manager) that installs hidden scripts, achieves persistence, connects to a public C2, and drains Solana wallets using a hard-coded RPC and destination address. Analysis suggests the package and documentation were AI-generated to appear legitimate while abusing NPM to spread; notable IOCs include the C2 domain and Solana address. #ENHANCEDSTEALTHWALLETDRAINER
Keypoints
- The package @kodane/patch-manager masquerades as an NPM registry cache manager while containing an “ENHANCED STEALTH WALLET DRAINER” payload.
- post-install.js renames and installs malicious files into hidden cache-like directories on macOS, Linux, and Windows, then spawns a detached background process.
- connection-pool.js establishes persistent C2 communication with https://sweeper-monitor-production.up.railway.app and registers a unique machine ID for each infected host.
- transaction-cache.js locates wallet files, uses a hard-coded Solana RPC endpoint (helius-rpc) to identify assets, drains most funds while leaving fees, and forwards assets to a hard-coded Solana address.
- The C2 server was publicly accessible and showed active management and multiple compromised hosts during analysis.
- Evidence (consistent, polished docs, excessive comments, emojis, console logs, and naming like “Enhanced”) indicates the author likely used AI to generate code and documentation to evade detection.
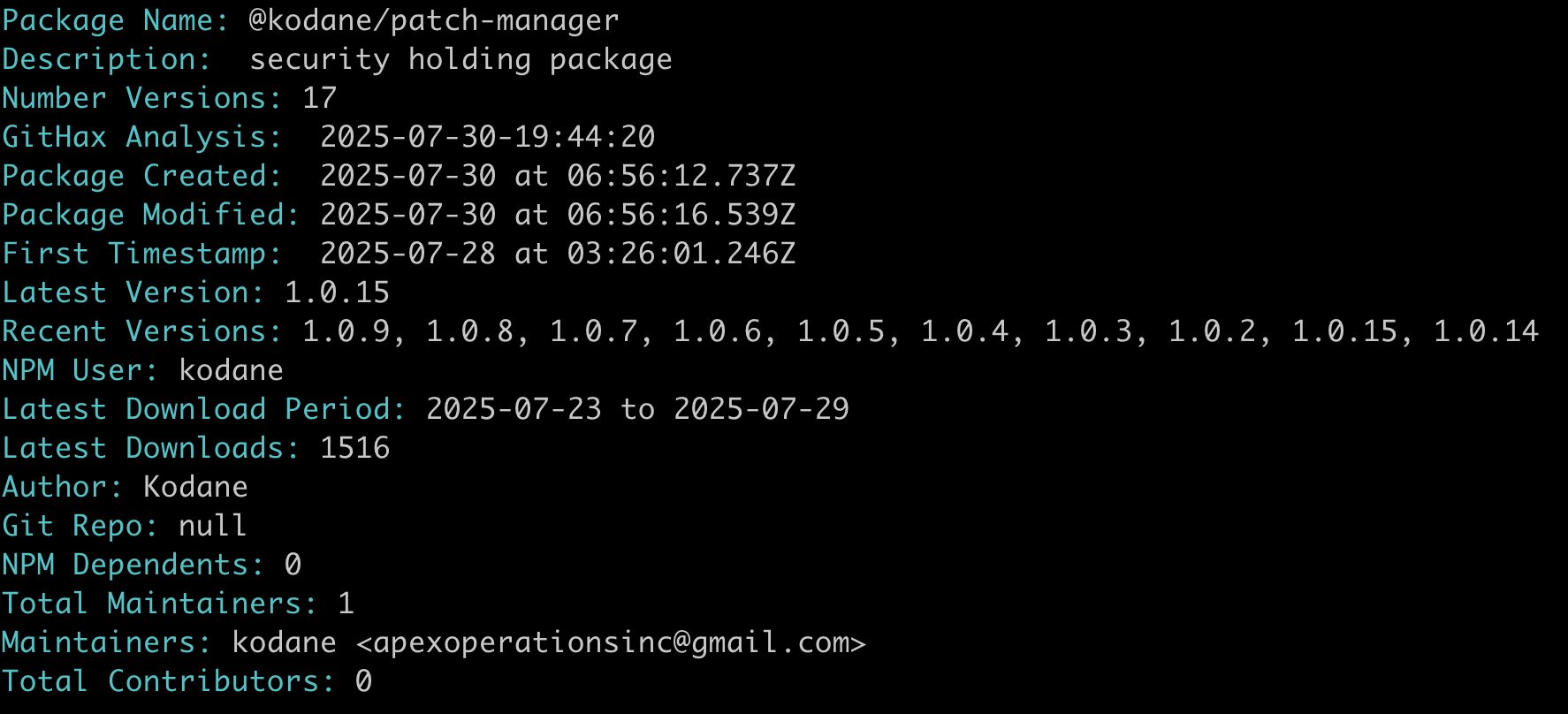
- Package was published July 28, 2025 with 19 versions over two days, had ~1500 downloads, and was marked malicious by NPM on July 30, 2025.
MITRE Techniques
- [T1543] Create or Modify System Process – post-install script spawns and detaches connection-pool.js to run persistently in the background (“spawning the connection-pool.js script and detaching the spawned process from its parent process”).
- [T1090] Proxy/Connect to Command and Control – connection-pool.js connects to a command-and-control server at https://sweeper-monitor-production.up[.]railway[.]app (“it connects to a C2 server at https://sweeper-monitor-production.up[.]railway[.]app”).
- [T1027] Obfuscated Files or Information – malware installs files in hidden directories and uses OS-specific hiding (e.g., attrib +H on Windows) to conceal its components (“installs its malicious files in hidden directories that mimic legitimate cache folders” and “runs the `attrib +H` command to make the installation directory hidden”).
- [T1486] Data Encrypted for Impact (credential/wallet theft variant) – transaction-cache.js identifies wallet files and drains funds, preserving a small amount for transaction fees (“this file actually does the ‘sweeping’ which is the draining of funds from the wallet… leaves enough in the wallet to cover the transfer fee”).
- [T1086] PowerShell / Command Shell – uses OS commands to manipulate file attributes on Windows (“the malware runs the `attrib +H` command to make the installation directory hidden”).
- [T1496] Resource Hijacking (cryptocurrency theft) – uses a hard-coded Solana RPC endpoint and a hard-coded recipient address to siphon crypto assets (“uses a single hard coded RPC endpoint… sends the crypto assets to a hard coded Solana address: B2XwbrGSXs3L…”).
Indicators of Compromise
- [NPM Package] Malicious package – @kodane/patch-manager
- [File Hashes] malicious scripts – monitor.js (7a0a3e64ecb4212ce08315400ed7ed79617843e2bc4326439ca8b81d1960ecbc), sweeper.js (3aa51674e3d46062b6de2cfd6c20f8b70fef2b6a28add462a870f686e387f9de)
- [File Hashes] installer/utility files – utils.js (e8e5ace2a791d519e69c547e1a8491bf6a5d3060c080ff7e8350b86f2a0aab30), post-install.js (f64a8ac3604c712fc1ace85c3262da3dfe693a4b4082f7365f849eea6908ee8b)
- [Email] actor contact – [email protected]
- [Domains/URLs] C2 and infrastructure – https://sweeper-monitor-production.up.railway.app, https://sweeper-monitor.railway.app, http://va.vision-node.com:8899
- [Crypto Address] destination wallet – Solana address B2XwbrGSXs3LAAcqFqKqGUug5TFA1Bug2NNGH3F3mWNK (observed transaction activity)
Read more: https://getsafety.com/blog-posts/threat-actor-uses-ai-to-create-a-better-crypto-wallet-drainer