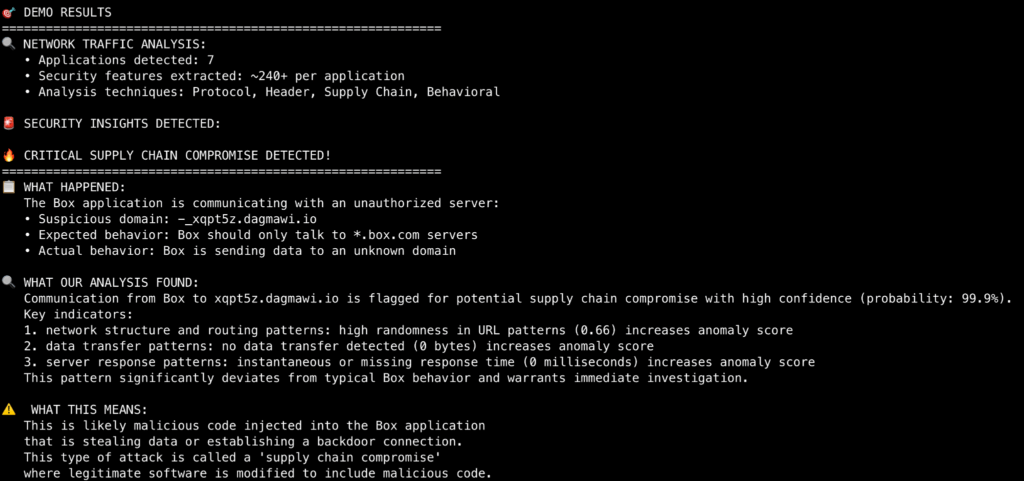
Netskope Threat Labs released BEAM, an open-source tool that detects supply chain attacks by analyzing network traffic without requiring endpoint agents. BEAM uses user agent strings and machine learning models to identify suspicious application behavior and anomalous communications. #BEAM #SolarWinds #NetskopeThreatLabs
Category: Threat Research

A new DarkCloud campaign targeting Microsoft Windows users was uncovered, beginning with a phishing email containing a malicious RAR attachment that executes a multi-stage attack to steal sensitive information. The malware uses sophisticated techniques such as fileless payload deployment, process hollowing, and anti-analysis mechanisms to collect credentials, payment data, email contacts, and exfiltrate them via SMTP. #DarkCloud #ProcessHollowing #FortinetFortiGuard
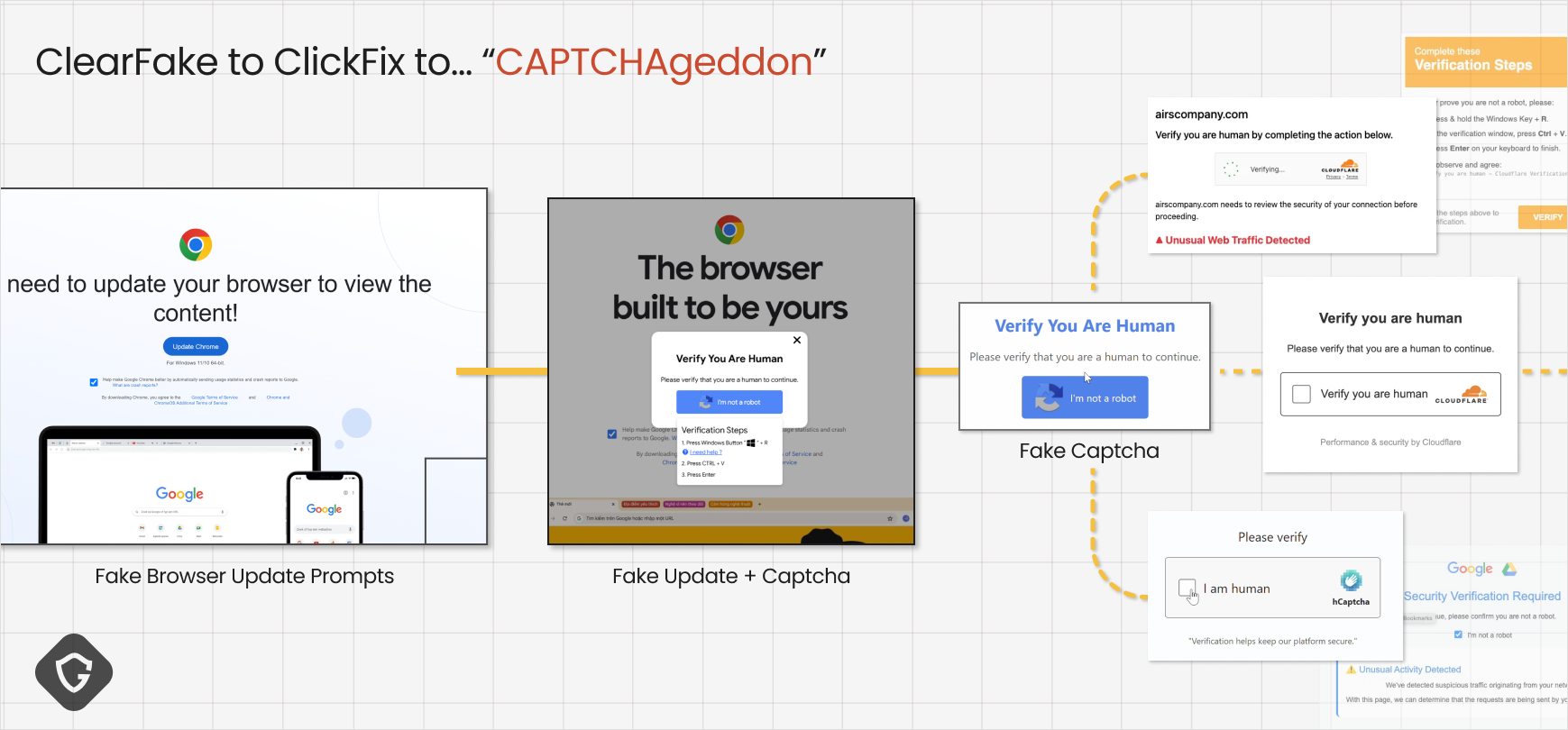
In early 2024, attackers evolved from ClearFake’s fake browser update malware delivery to the more effective ClickFix fake captcha technique, leading to widespread credential theft. This evolution demonstrates sophisticated propagation, social engineering narratives, and technical evasion strategies, including abuse of trusted platforms like Google Scripts and cross-platform payloads. #ClearFake #ClickFix #LummaStealer…
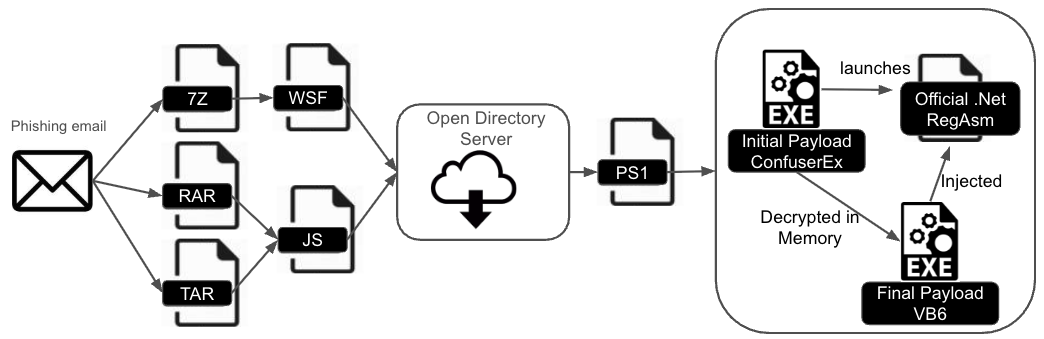
DarkCloud Stealer has evolved with new infection chains using ConfuserEx obfuscation and a Visual Basic 6 payload, complicating detection and analysis. The malware is distributed via phishing emails containing various archive types that deliver obfuscated scripts to deploy the payload. #DarkCloudStealer #ConfuserEx #RunPE…
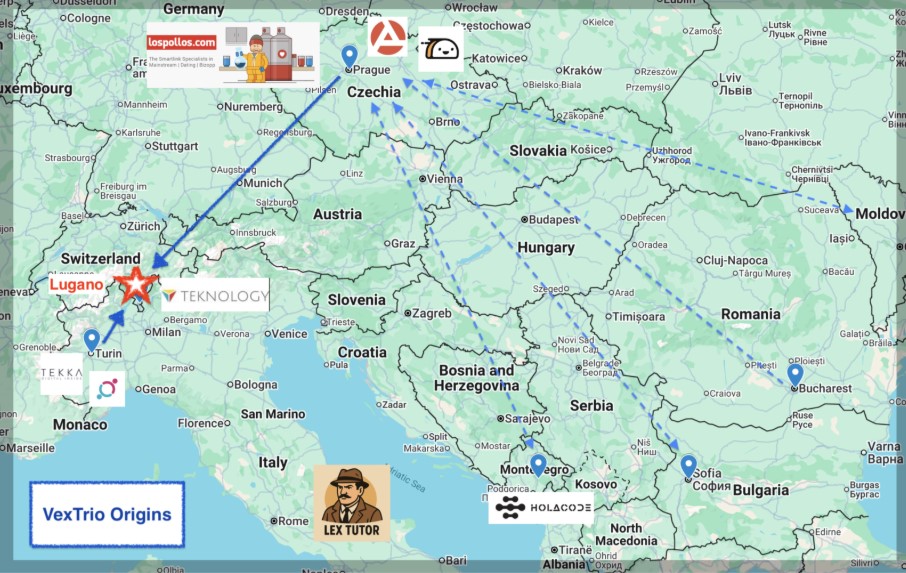
VexTrio is a sophisticated cybercriminal enterprise formed from Italian spammers and Eastern European developers, operating a vast malicious traffic distribution system that facilitates widespread digital fraud, including dating scams and cryptocurrency scams. Their affiliate advertising networks, such as Los Pollos, Taco Loco, and Adtrafico, are deeply intertwined with website hackers and use smartlinks to monetize compromised websites globally. #VexTrio #LosPollos #AdsPro #TacoLoco #Adtrafico

Since 2022, ransomware groups and underground marketplaces have increasingly utilized sophisticated EDR killer tools, such as those packed with HeartCrypt, to disable endpoint security during multi-stage attacks. Evidence suggests significant tool sharing and technical knowledge transfer among competing ransomware groups, complicating defense efforts. #EDRKillShifter #HeartCrypt #RansomHub #MedusaLocker #INC
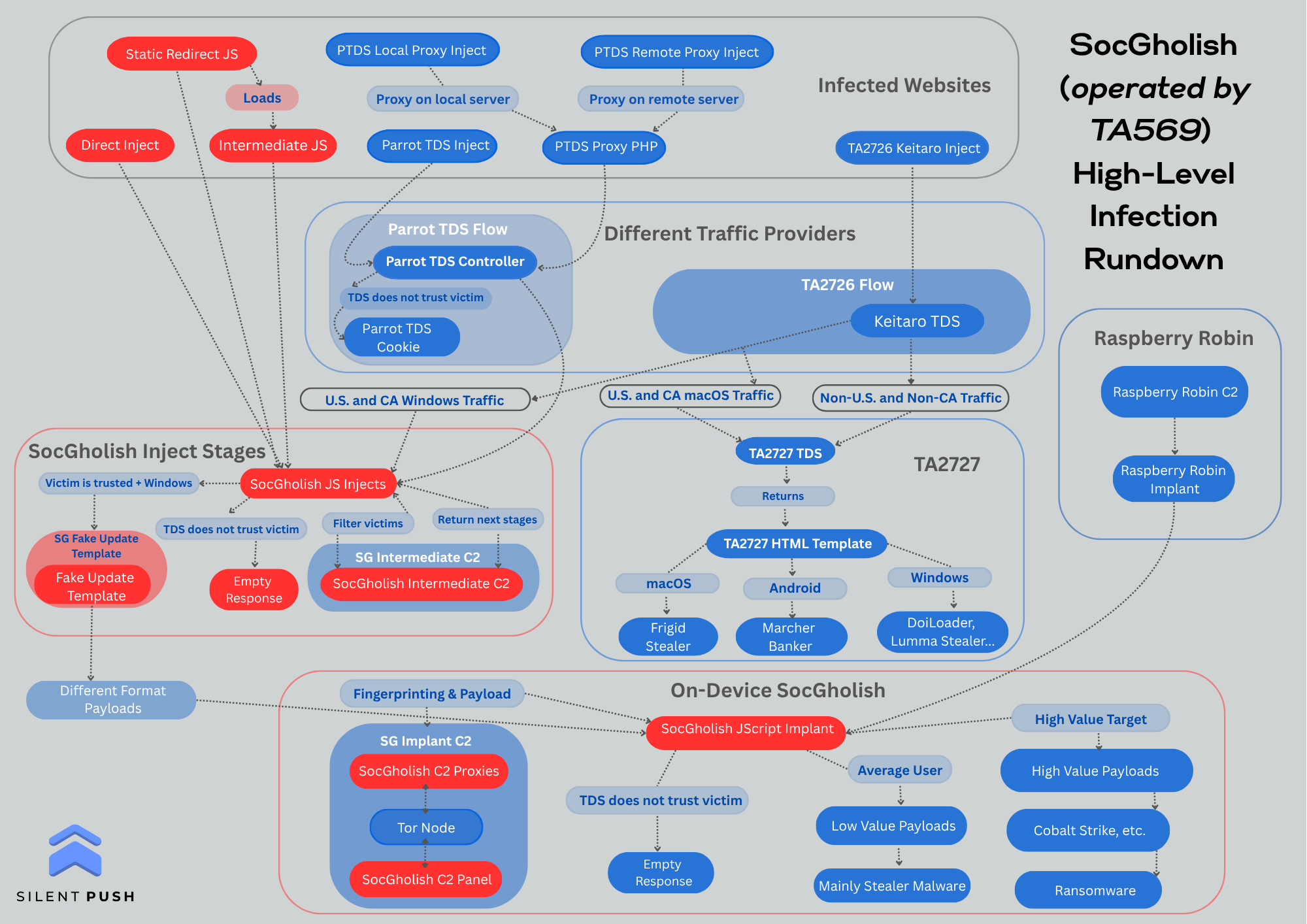
SocGholish, operated by TA569, is a Malware-as-a-Service platform that sells access to compromised systems using deceptive fake browser update lures and Traffic Distribution Systems (TDSs) such as Parrot TDS and Keitaro TDS. Its infrastructure supports various financially motivated threat actors, including Russian groups like Evil Corp (DEV-0243) and UNC2165, and is…
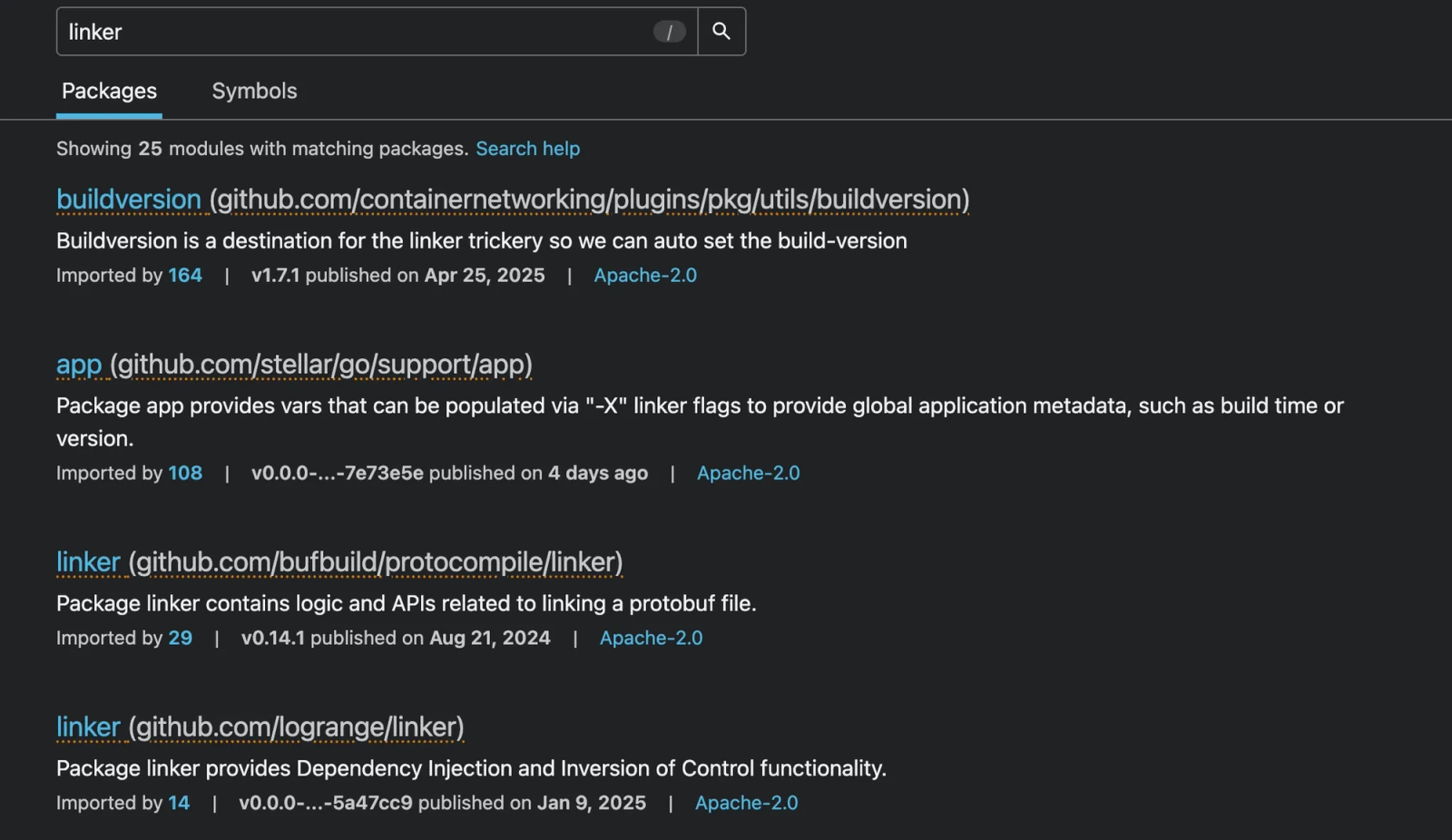
Socket’s Threat Research Team found eleven malicious Go packages, mostly typosquats, that use an index-based string obfuscation to silently execute a shell and fetch second-stage payloads from various .icu and .tech domains. These payloads target both Linux and Windows systems, enabling attackers to exfiltrate data and maintain persistence. #GoModules #Typosquatting #MonsoletterICU #InfinityHELicu

Illegal activity involving the sale of stolen identity documents from Italian hotels has been detected, with tens of thousands of high-resolution scans of passports and ID cards compromised. These documents were taken via unauthorized access to three hotel facilities between June and July 2025 and are used for sophisticated fraud schemes. #mydocs #ItalianHotels #IdentityTheft
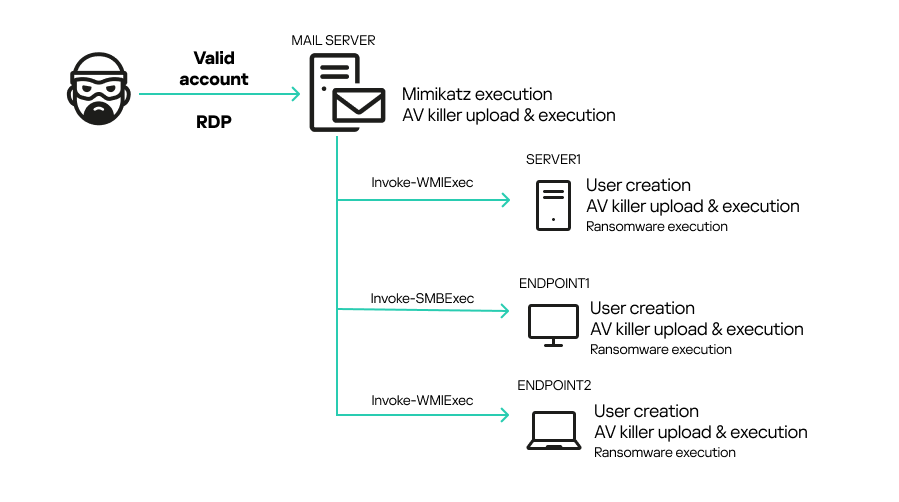
A novel AV killer malware leveraging the vulnerable ThrottleStop.sys driver has been active since at least October 2024, used to terminate antivirus processes and facilitate lateral movement in ransomware attacks such as MedusaLocker. Kaspersky’s products include mechanisms to defend against such threats, but this incident emphasizes the importance of defense in depth and strong access controls. #MedusaLocker #ThrottleStop.sys #BYOVD

AhnLab Security Intelligence Center (ASEC) uncovered malware distributed via Facebook ads targeting cryptocurrency users by impersonating a Binance exchange website. The malware installs via an “installer.msi” file, opens a local listening port, communicates with a command and control server, and executes an Infostealer to collect sensitive system and browser data. #Binance…
North Korean Lazarus subgroup Famous Chollima has developed PyLangGhost RAT, a Python-based remote access trojan targeting technology, finance, and cryptocurrency sectors through fake job interviews and social engineering. The malware steals browser-stored credentials and cryptocurrency wallet data by exploiting privilege escalation and sophisticated decryption methods. #PyLangGhostRAT #FamousChollima #LazarusGroup #GoLangGhostRAT…
The Bumblebee malware campaign used trojanized IT management tools distributed via SEO poisoning to gain initial access, ultimately leading to Akira ransomware deployment in July 2025. Multiple organizations were affected, with attackers leveraging privileged IT accounts for lateral movement, credential dumping, and data exfiltration. #Bumblebee #AkiraRansomware #SEOpoisoning #ManageEngineOpManager

Makop ransomware attacks in South Korea have increasingly exploited Remote Desktop Protocol (RDP) to gain initial access, using brute force attacks to compromise accounts. The threat actor also deploys credential-stealing tools similar to those used in Crysis and Venus ransomware attacks, suggesting a possible connection between these campaigns. #Makop #RDP #Mimikatz…
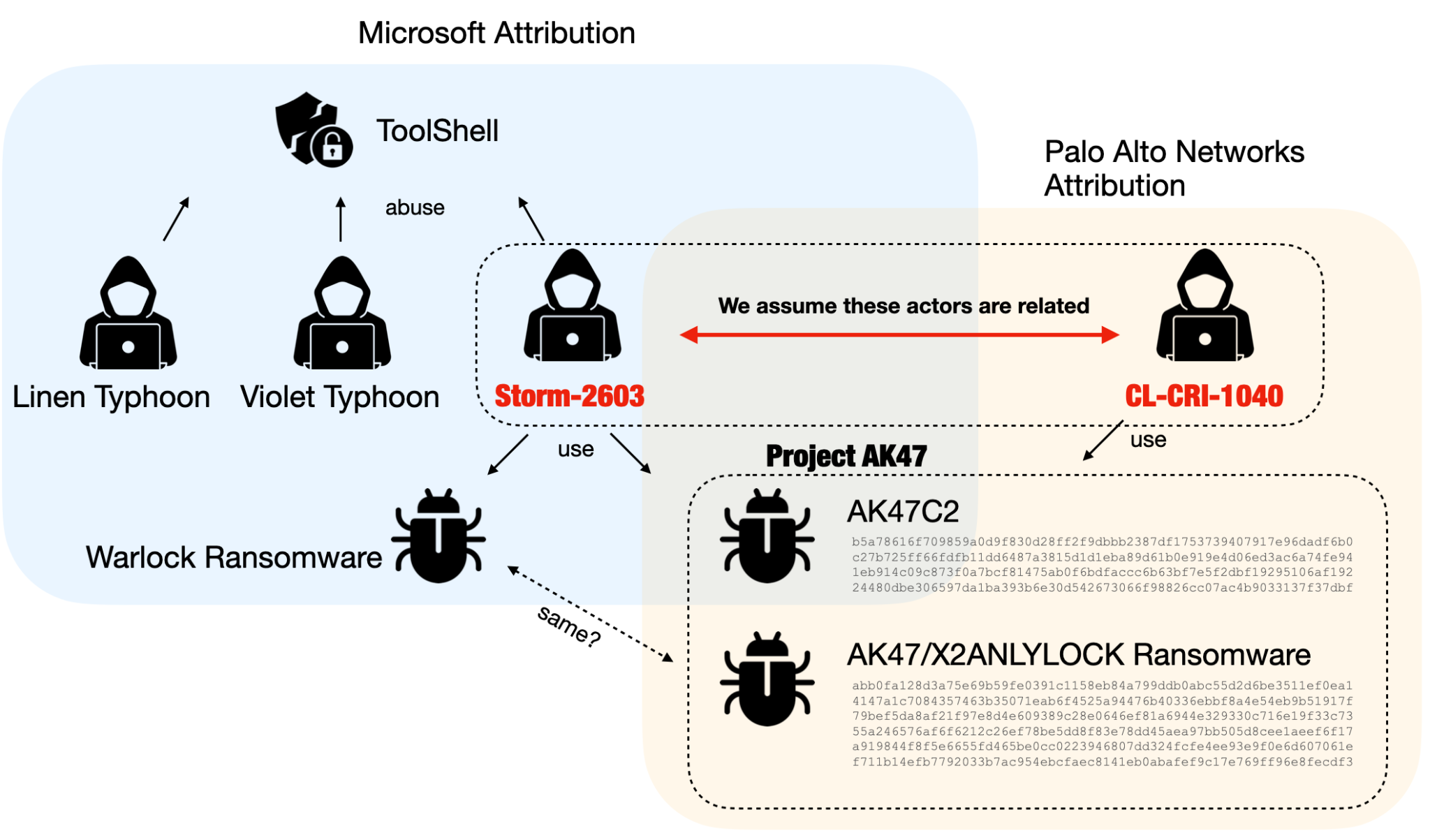
Unit 42 identified a financially motivated threat actor cluster named CL-CRI-1040, linked with Microsoft’s Storm-2603, targeting SharePoint vulnerabilities using the ToolShell exploit chain and deploying a malware suite called Project AK47. Project AK47 comprises a backdoor (AK47C2), ransomware (AK47/X2ANYLOCK), and loaders leveraging DLL side-loading, with ties to previous LockBit 3.0 affiliates…