A targeted supply chain attack was discovered involving a backdoor in Gravity Forms plugin version 2.9.12, which exfiltrated site data and allowed remote code execution via a malicious domain gravityapi.org. Multiple malicious functionalities including user creation, file upload, and directory listing were identified, prompting the release of a patched version 2.9.13…
Category: Threat Research
A new variant of the RoKRAT malware used by the APT37 group employs encrypted shellcode and steganography to evade detection and persist through fileless attacks. The report emphasizes the critical need for effective EDR systems to detect abnormal endpoint behaviors and manage such sophisticated threats. #RoKRAT #APT37 #Steganography
An ISO image targeting Chinese-speaking users utilizes a malicious DLL sideloaded by a legitimate Alibaba executable to deploy a Cobalt Strike Beacon with a decoy PDF. The threat leverages an LNK file named after the Zhengzhou Commodity Exchange to initiate execution, disguising malicious traffic as Bilibili video sharing platform communications. #CobaltStrike #SLOWTEMPEST #ZhengzhouCommodityExchange

A stealthy Linux backdoor named Plague was discovered that modifies PAM authentication to enable persistent, covert SSH access while evading detection by antivirus tools. The malware employs advanced obfuscation, anti-debugging, and session-clearing techniques to maintain stealth and persistence. #Plague #PAMBackdoor…
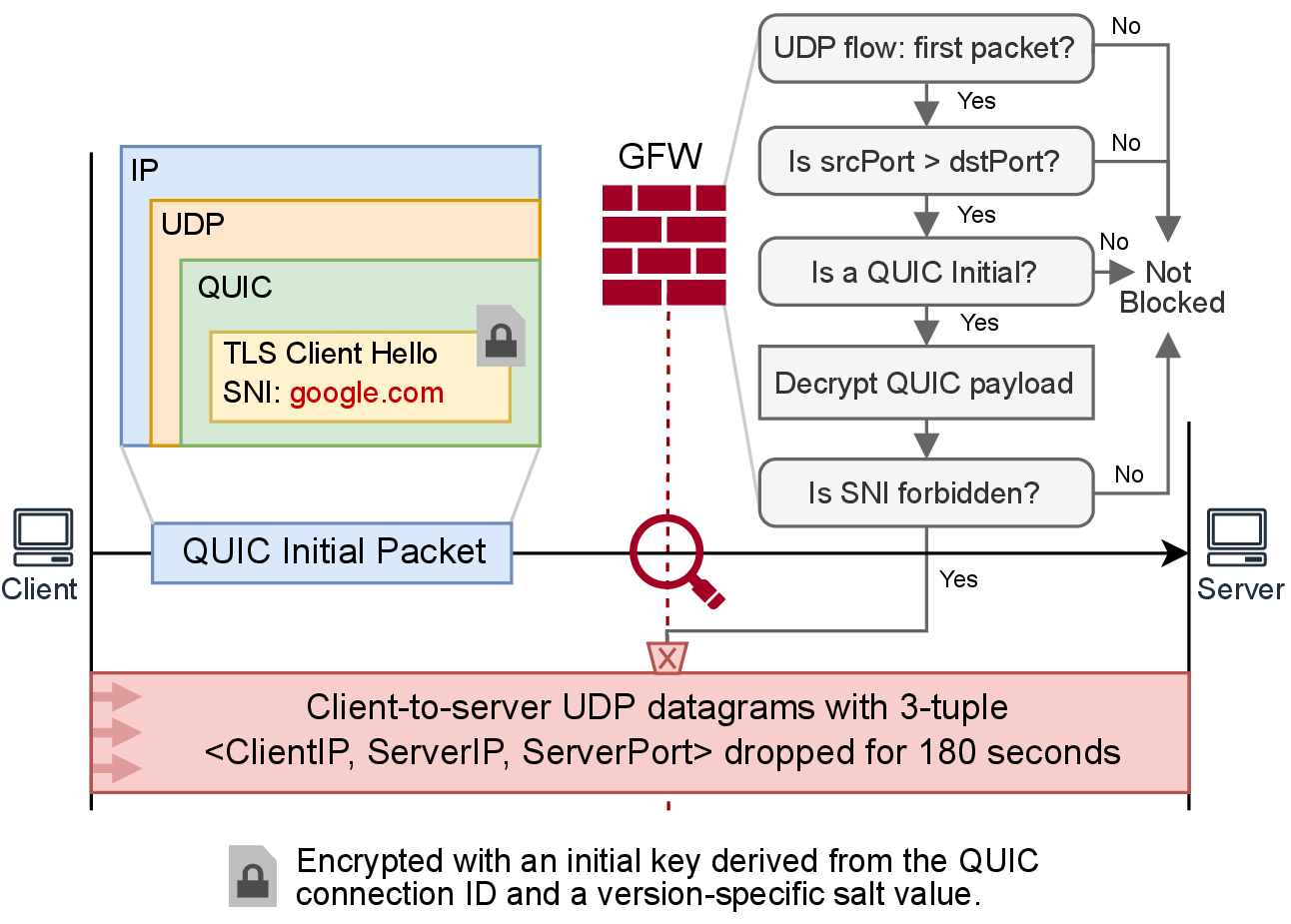
The Great Firewall of China (GFW) has started selectively blocking QUIC protocol connections based on the Server Name Indication (SNI) in April 2024 by decrypting and inspecting QUIC Initial packets, revealing a unique and resource-intensive censorship mechanism. Researchers identified a vulnerability allowing attackers to exploit this censorship system to block UDP…

The Qilin Ransomware group operates through a RaaS model with multiple affiliates, including “hastalamuerte,” who leaked affiliate panel credentials and exhibited extensive use of tools like Mimikatz and NetExec for attacks. The investigation reveals their targeting of Windows environments, use of obfuscation techniques, and interest in cryptocurrency via Bitkub API, along…

A new variant of the Lumma Stealer malware is being distributed via a fake Telegram Premium website that automatically downloads a malicious executable to steal sensitive data such as browser credentials and cryptocurrency wallets. The campaign employs drive-by downloads, domain impersonation, and evasive network techniques, posing significant threats to Windows systems. #LummaStealer #TelegramPremium #DriveByDownload

CISA conducted a proactive hunt engagement with the U.S. Coast Guard, finding no evidence of malicious cyber activity but identifying several cybersecurity risks including insufficient logging and insecure credential storage. AttackIQ provides scenarios and recommendations to help organizations test and mitigate these risks effectively. #CISA #USCoastGuard #AttackIQ…

A critical Remote Code Execution vulnerability was discovered in the @nestjs/devtools-integration package due to an insecure JavaScript sandbox environment combined with insufficient CORS and content-type validations. This flaw allows attackers to execute arbitrary code on a developer’s local machine simply by visiting a malicious website. #nestjs #Socket #safe-eval

LockBit ransomware operators use sophisticated DLL sideloading and masquerading techniques to evade detection and execute malicious payloads under the cover of legitimate system processes. These techniques are integrated throughout the attack chain, from initial access to encryption, enabling persistence and stealth in compromised environments. #LockBit #DLLSideloading #Masquerading #Syrphid
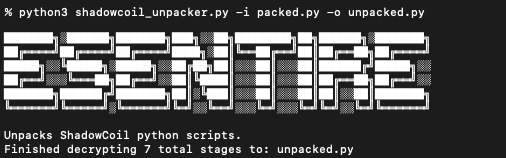
In July 2025, eSentire’s Threat Response Unit (TRU) identified the use of SocGholish malware combined with a new python-based password stealer targeting Chrome and Edge browsers, linked to ex-affiliates of the RansomHub group now called ShadowCoil. The TRU provided a detailed unpacking process, detection Yara rule, and mitigation recommendations to enhance defense against this evolving threat. #SocGholish #ShadowCoil #RansomHub

CISA and USCG conducted a proactive hunt engagement at a U.S. critical infrastructure organization, finding no malicious activity but identifying significant cybersecurity risks including shared local admin credentials and insufficient network segmentation between IT and OT environments. The advisory provides detailed recommendations and mitigations to improve cybersecurity posture, aligning with CISA,…
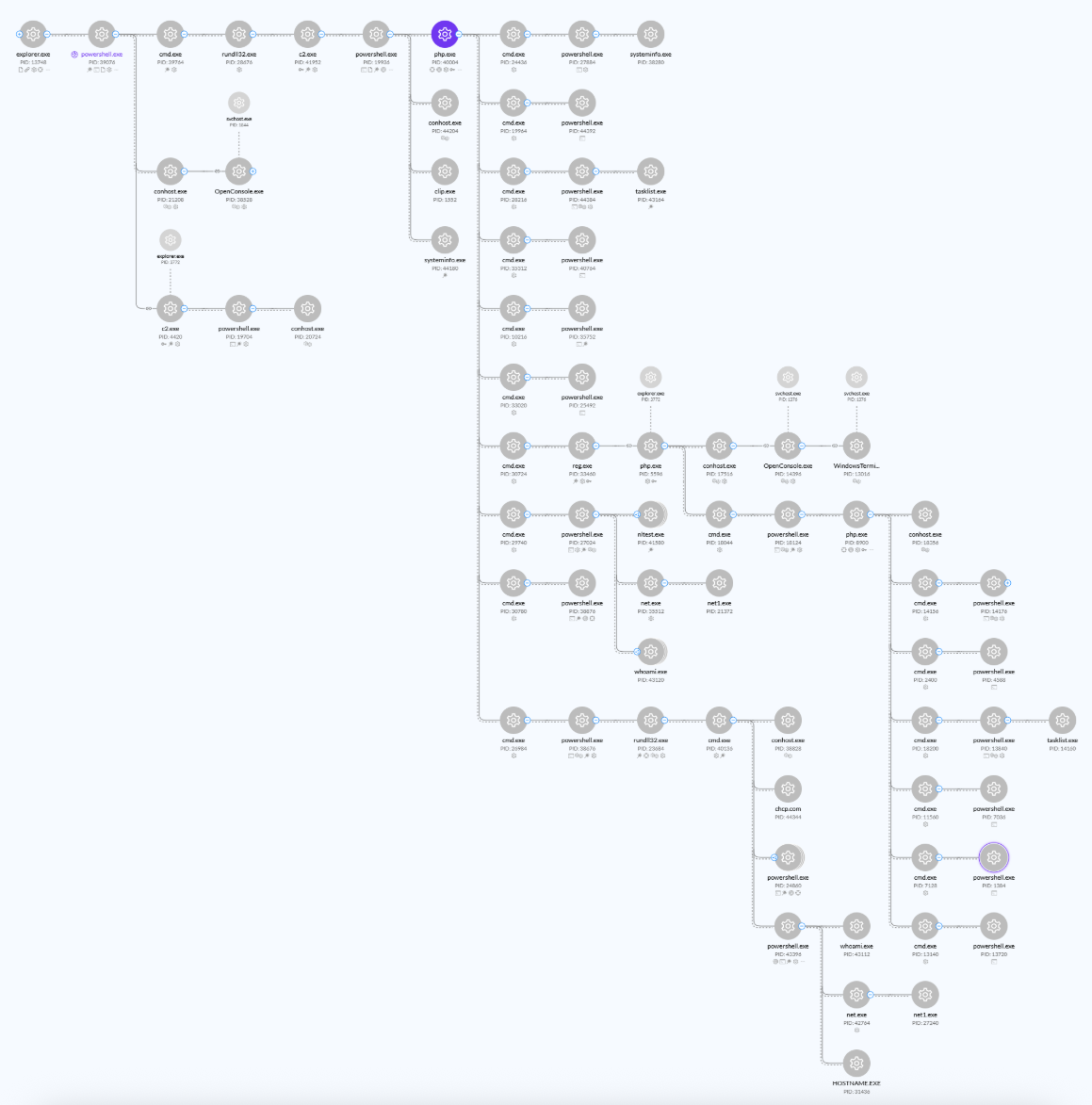
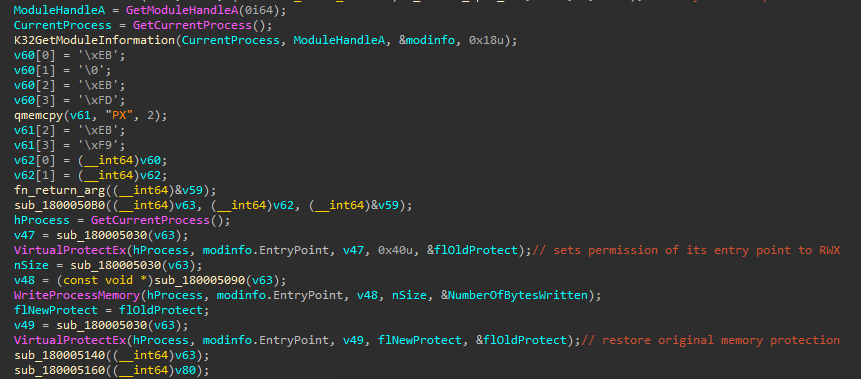
The eSentire Threat Response Unit (TRU) uncovered a sophisticated multi-stage attack by the Interlock Group ransomware gang using PHP backdoors, PowerShell, and LOLBins for system reconnaissance and payload deployment. They provided detailed analysis, Python scripts for detection, and guidance to enhance threat hunting and incident response efforts. #InterlockGroup #InterlockRAT #ClickFix
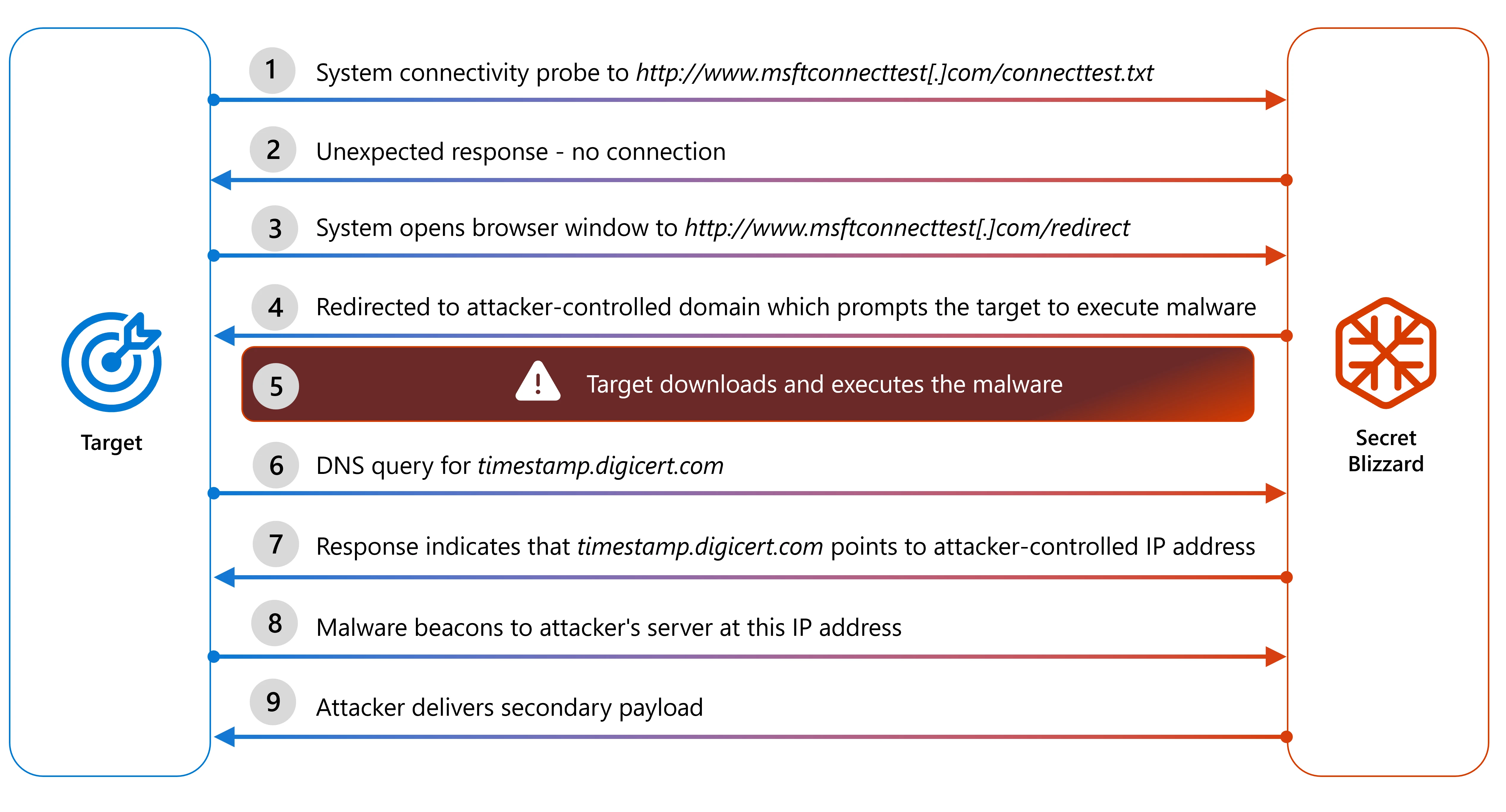
Microsoft Threat Intelligence revealed that the Russian state actor Secret Blizzard is conducting a cyberespionage campaign using an adversary-in-the-middle (AiTM) position at ISPs in Moscow to deploy ApolloShadow malware targeting foreign embassies. The malware installs root certificates to intercept encrypted traffic, allowing persistent access for intelligence gathering. #SecretBlizzard #ApolloShadow
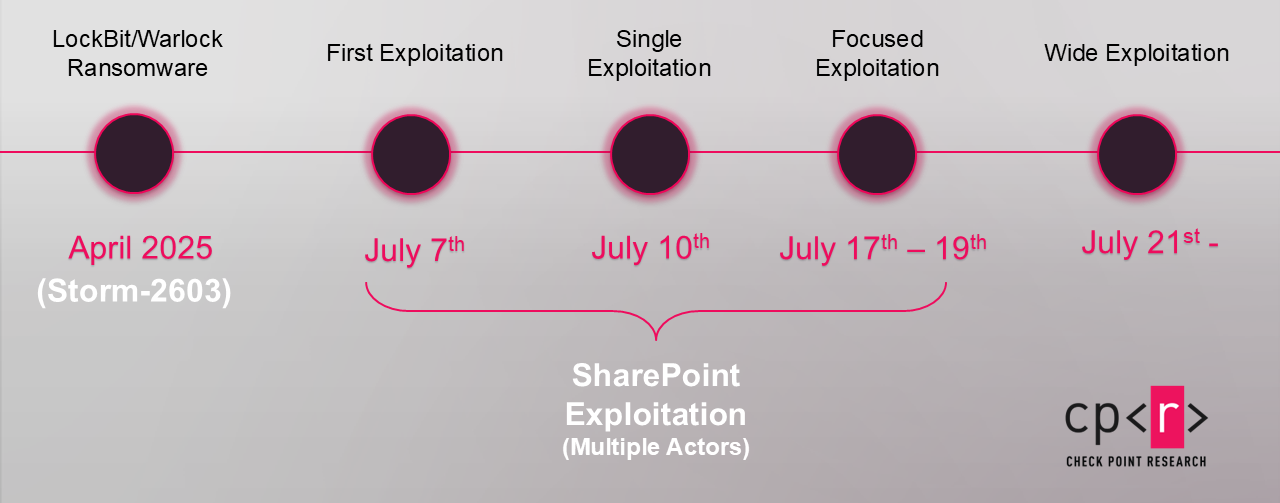
Storm-2603 is a newly identified Chinese-affiliated threat actor leveraging the ToolShell SharePoint vulnerabilities using a custom malware framework called ak47c2 to deploy multiple ransomware variants including LockBit Black and Warlock/x2anylock. The actor employs sophisticated techniques such as DNS and HTTP-based backdoors, BYOVD for disabling endpoint protections, and DLL hijacking for ransomware deployment. #Storm2603 #ak47c2 #ToolShell #LockBitBlack #WarlockRansomware
