Social engineering remains the top initial access method in cybersecurity incidents from May 2024 to May 2025, exploiting human trust and identity systems rather than relying on technical exploits. Attackers like Muddled Libra and state-aligned groups utilize high-touch methods and AI-enhanced tactics to bypass controls, escalate privileges quickly, and cause significant data exposure and business disruption. #MuddledLibra #AgentSerpens #ClickFix
Keypoints
- Social engineering accounted for over one-third of incident responses, with more than 35% involving non-phishing techniques such as SEO poisoning and help desk manipulation.
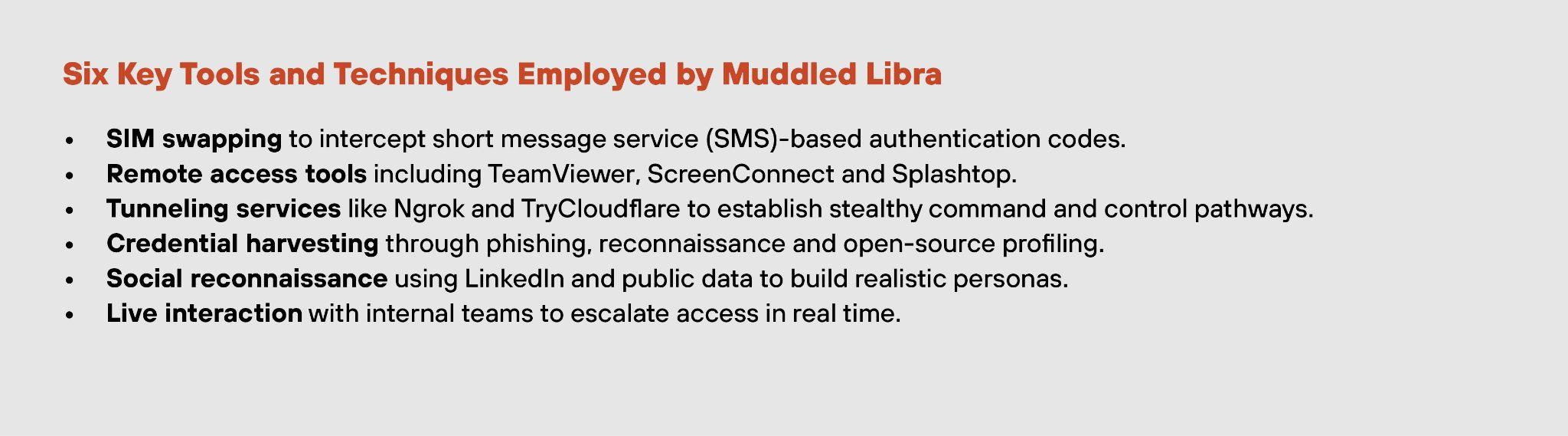
- High-touch attacks by groups like Muddled Libra can bypass MFA and escalate from initial access to domain administrator in under 40 minutes without malware.
- AI is accelerating social engineering through automation, generative AI for personalized lures and cloned voices, and agentic AI for multi-step attack execution.
- At-scale deception campaigns, like ClickFix, exploit fake system prompts and SEO poisoning to initiate credential theft and remote access tool deployment.
- Social engineering intrusions lead to data exposure in 60% of cases, significantly higher than other attack vectors, often involving credential reuse and lateral movement.
- Organizational weaknesses include over-permissioned access, insufficient MFA deployment, alert fatigue, and low detection coverage of identity abuse.
- Defensive strategies emphasize behavioral analytics, identity threat detection and response (ITDR), Zero Trust enforcement across users, and strengthening help desk credential reset processes.
MITRE Techniques
- [T1078] Valid Accounts – Used by attackers impersonating employees to reset MFA and gain legitimate credentials (“…impersonating a locked-out employee…passed identity checks and gained the agent’s trust…”).
- [T1204] User Execution – Victims initiated compromise by clicking on fake update prompts or following SEO-poisoned links (“…employee encountered what appeared to be an authentic Microsoft update notification…triggered a payload download…”).
- [T1566] Phishing – Used particularly in the initial delivery of payloads and lures, including voice-based phishing (“…employed GenAI to craft highly personalized lures…using cloned executive voices in callback scams…”).
- [T1556] Modify Authentication Process – Attackers manipulated help desk protocols to reset credentials and bypass MFA (“…convincing pretext to prompt a reset of MFA credentials…”).
- [T1086] PowerShell – Living-off-the-land binaries like PowerShell were used for lateral movement and persistence without triggering alerts (“…moved laterally using legitimate administrative tools…”).
- [T1059] Command and Scripting Interpreter – Use of built-in tools to escalate privileges without malware (“…using only built-in tools and social pretexts…”).
Indicators of Compromise
- [File hashes] Examples include RedLine and Lumma malware hashes used as credential harvesters in ClickFix campaigns.
- [Domains] Malicious SEO-poisoned domains used as spoofed landing pages for payload delivery in at-scale deception attacks.
- [File names] Fake update prompt executables and loaders deployed during campaigns targeting retail and healthcare sectors.
- [IP addresses] Command and control tunneling service IPs linked to Muddled Libra operations for stealthy external communication.