Threat actors are exploiting fake Microsoft OAuth applications to bypass multifactor authentication and steal Microsoft 365 credentials using AiTM phishing kits like Tycoon. These campaigns impersonate well-known enterprise apps and leverage phishing to gain unauthorized access, affecting thousands of users and numerous tenants. #Tycoon #MicrosoftOAuth #ILSMart #Adobe #EntraID
Keypoints
- Threat actors use fake Microsoft OAuth apps impersonating companies such as RingCentral, SharePoint, Adobe, and DocuSign to conduct credential phishing attacks.
- These campaigns bypass MFA using attacker-in-the-middle (AiTM) phishing kits, predominantly Tycoon and ODx.
- Proofpoint identified over 50 impersonated applications and thousands of phishing emails targeting Microsoft 365 users since early 2025.
- Malicious OAuth apps request limited permissions but lead victims to counterfeit Microsoft authentication pages to harvest credentials and 2FA tokens.
- More than two dozen malicious apps were authorized by users across over 20 tenants, but actual account takeovers were limited to a few cases, indicating low success rates.
- The phishing kits use HTTP client axios and are linked to significant MFA bypass and session cookie theft for persistence in compromised accounts.
- Microsoft plans to enhance security by blocking legacy authentication and requiring admin consent for third-party app access starting mid-2025, aiming to disrupt these attacks.
MITRE Techniques
- [T1530] Data from Cloud Storage Object – The attackers use OAuth applications to gain access to Microsoft 365 cloud accounts by bypassing MFA. (“…to obtain access to Microsoft 365 accounts via MFA phishing.”)
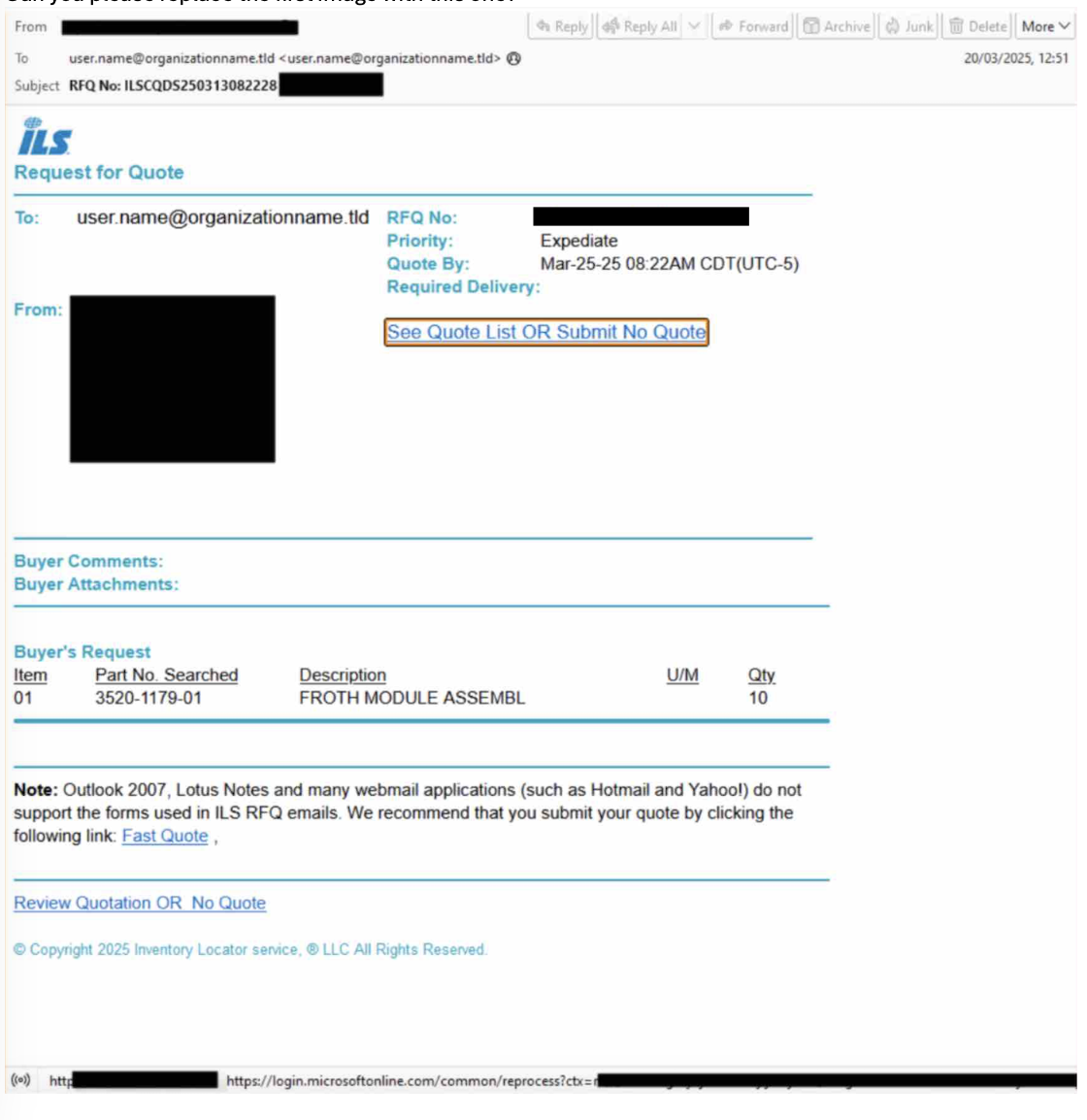
- [T1556.004] Spear Phishing Link – Malicious emails contain links to fake OAuth consent pages to lure victims into granting permissions. (“…messages are often sent from compromised email accounts and include subjects related to request for quotes or business contract agreements.”)
- [T1110.003] Password Spraying – Attackers attempt multiple OAuth app authorizations to capture credentials and tokens. (“…over 50 impersonated applications and multiple different phishing kits using this attack chain…”)
- [T1586] Compromise Infrastructure – The threat actors shifted from Russia-based proxy services to a U.S.-based data center hosting service to evade detection. (“…an abused U.S.-based DCH service appears to have replaced previously used Russia-based proxy services.”)
- [T1587] Establish Accounts – Attackers perform “Security Method Add” actions to maintain persistence through MFA manipulation after account compromise. (“Following sign-in, the researchers observed MFA manipulation, particularly the ‘Security Method Add’ action.”)
Indicators of Compromise
- [URL] Redirectors and landing pages used in Tycoon phishing campaigns – hxxps://azureapplicationregistration[.]pages[.]dev/redirectapp, hxxps://chikeukohandco[.]com/saas/Index.html
- [Domain] Tycoon phishing infrastructure domains – yrqwvevbjcfv[.]es, pw5[.]haykovx[.]es
- [IP Address] Sign-in facing IP for Tycoon activity – 2a00:b703:fff2:35::1
- [Microsoft OAuth Application IDs] Malicious app identifiers – 14b2864e-3cff-4d33-b5cd-7f14ca272ea4, 85da47ec-2977-40ab-af03-f3d45aaab169, and multiple others (total over 15)
- [User Agent] Axios HTTP client versions linked to Tycoon activity – axios/1.7.9, axios/1.8.2