Unit 42 has identified a nation-state linked threat cluster, CL-STA-0969, targeting telecommunications infrastructure in Southwest Asia using custom tools and advanced evasion techniques. The activity involves exploitation of mobile roaming networks and implements various backdoors and implants to maintain stealthy persistence without clear evidence of data exfiltration. #CL-STA-0969 #LiminalPanda #Cordscan
Keypoints
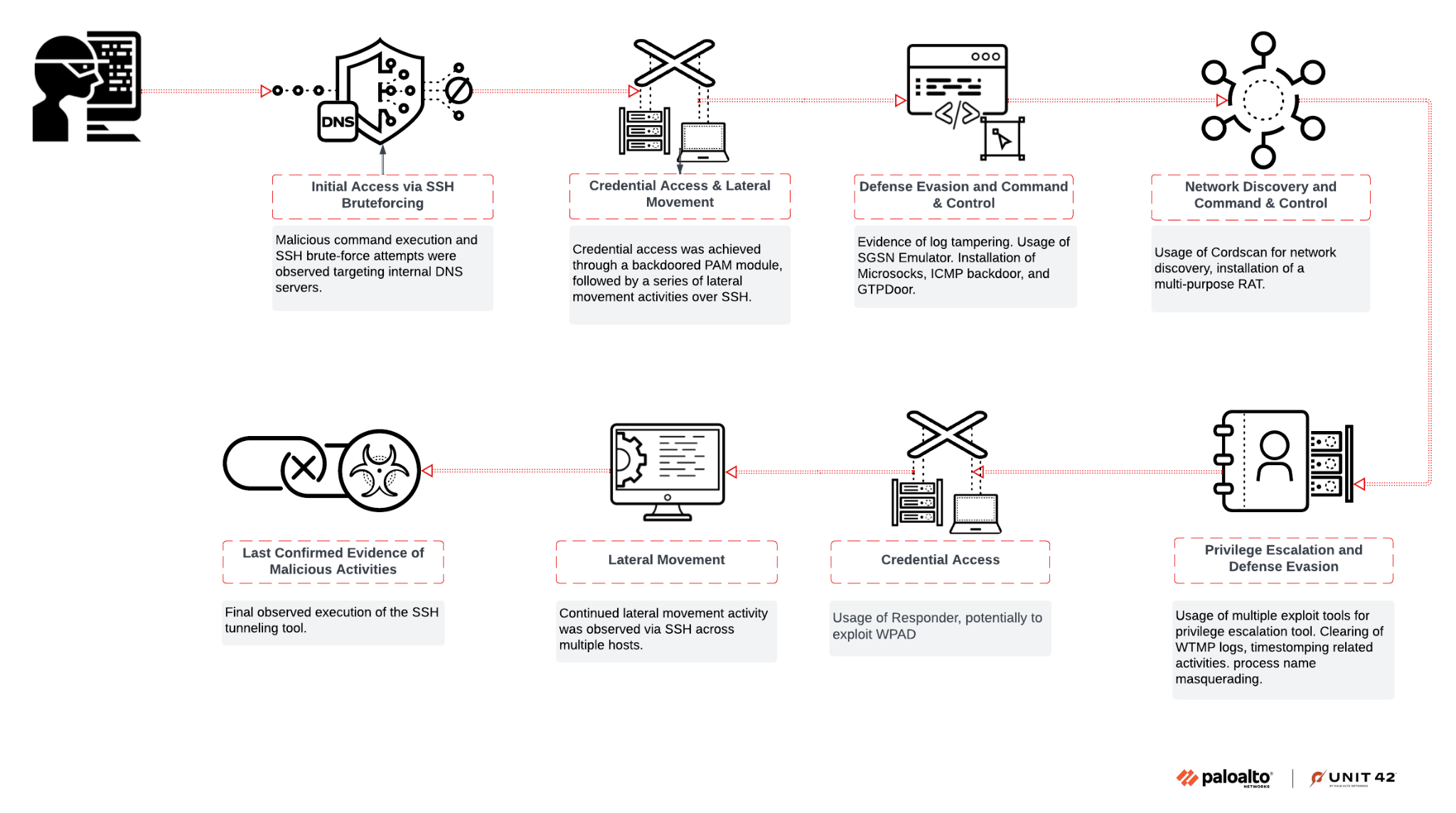
- CL-STA-0969 targeted telecom infrastructure in Southwest Asia between February and November 2024 with high operational security and defense evasion tactics.
- The threat actor used custom implants such as AuthDoor, Cordscan, GTPDoor, EchoBackdoor, SGSN Emulator, ChronosRAT, and NoDepDNS targeting mobile networks and protocols.
- Initial access was primarily gained via SSH brute-force attacks using telecommunications-specific account dictionaries.
- Privilege escalation exploited known vulnerabilities such as CVE-2016-5195 (DirtyCoW), CVE-2021-4034 (PwnKit), and CVE-2021-3156 using custom and publicly available exploits.
- Malicious communication channels used tunneling over protocols like DNS, GTP, ICMP, and SSH reverse tunneling over uncommon ports like port 53.
- Defense evasion techniques included log clearing, process masquerading with legitimate-looking names, timestomping, and disabling SELinux enforcement.
- The activity strongly overlaps with the nation-state adversary Liminal Panda and shares tooling similarities with groups such as Light Basin, UNC3886, UNC2891, and UNC1945.
MITRE Techniques
- [T1110] Brute Force – Used SSH brute-force attacks with tuned dictionaries for initial access (‘initial compromise likely originated from a brute-force attack against authentication mechanisms’).
- [T1548] Abuse Elevation Control Mechanism – Privilege escalation via exploitation of CVE-2016-5195, CVE-2021-4034, and CVE-2021-3156 vulnerabilities (‘used PwnKit… used a Python script exploit_userspec.py’).
- [T1027] Obfuscated Files or Information – Use of process name masquerading and timestomping to hide malicious executables (‘hid executables with convincing names tailored to the client environment’).
- [T1071] Application Layer Protocol – Command and control traffic tunneled over DNS, GTP, and ICMP protocols (‘tunneling traffic over DNS’, ‘communicates C2 traffic over GTP-C signaling messages’).
- [T1562] Impair Defenses – Disabling SELinux to avoid detection and clearing authentication logs (‘observed modifications to the SELinux configuration file… setenforce 0’).
- [T1090] Proxy – Use of reverse SSH tunneling and proxies like ProxyChains and Microsocks for command and control and lateral movement (‘established a reverse SSH tunnel’, ‘used ProxyChains to tunnel an SCP connection’).
- [T1005] Data from Local System – Credential harvesting using AuthDoor PAM backdoor (‘captures credentials encoded in ASCII hex format… opens file /usr/bin/.dbus.log’).
Indicators of Compromise
- [File Hashes] Examples of malware and tooling: bacbe2a793d8ddca0a195b67def527e66d280a13a8d4df90b507546b76e87d29 (Cordscan dbusquery), 705a035e54ce328227341ff9d55de15f4e16d387829cba26dc948170dac1c70f (Fscan /tmp/catlog), 827f41fc1a6f8a4c8a8575b3e2349aeaba0dfc2c9390ef1cceeef1bb85c34161 (GTPDoor dnsd_el5), and 432125ca41a2c5957013c8bff09c4037ad18addccab872d46230dd662a2b8123 (ChronosRAT /tmp/httpds).
- [File Names] Examples include pam_unix.so (AuthDoor backdoor), dbus-console (SGSN Emulator), evip-echo/pickup (EchoBackdoor), and vmware-daemon.py (Responder tool).
Read more: https://unit42.paloaltonetworks.com/infiltration-of-global-telecom-networks/