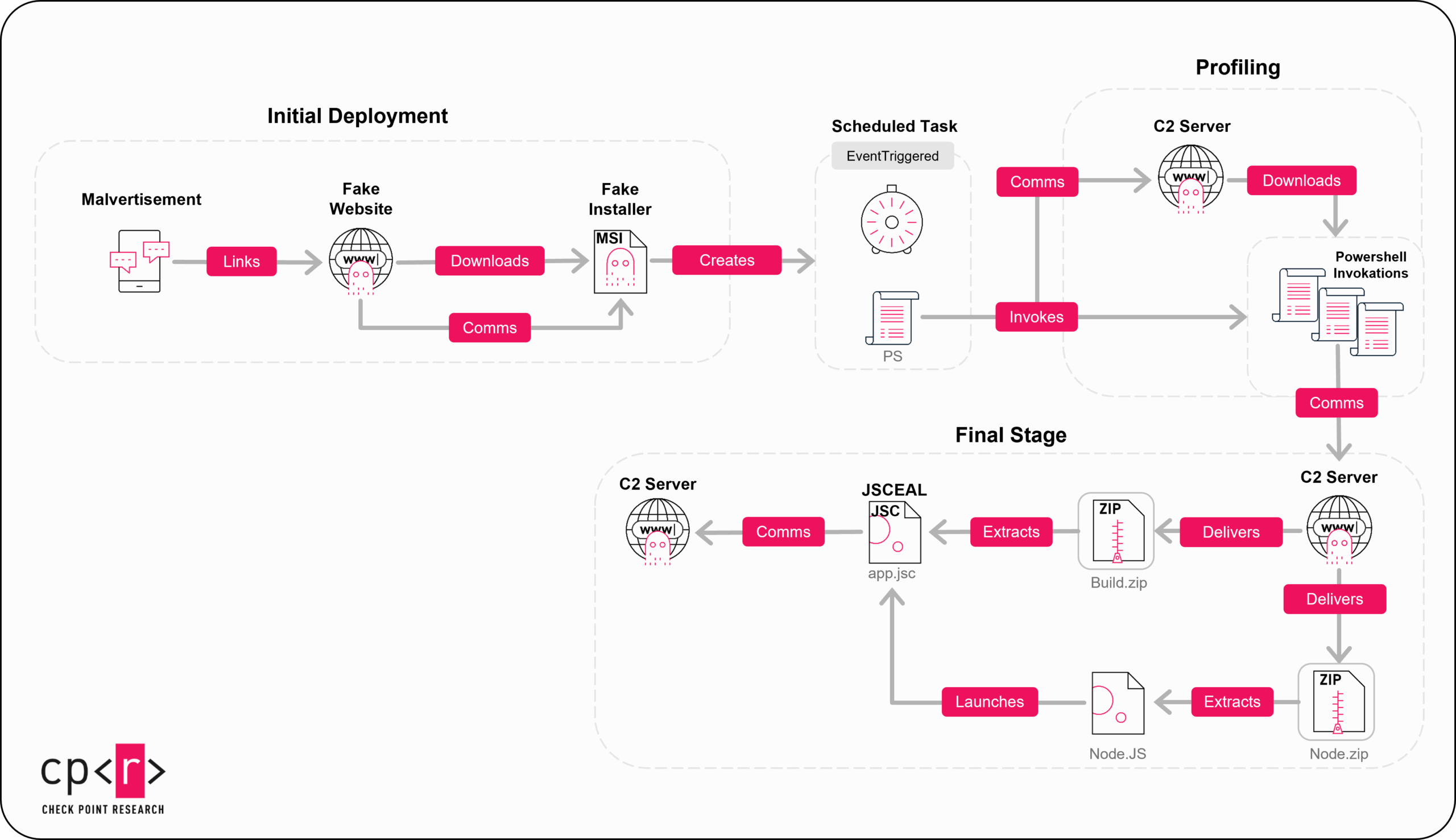
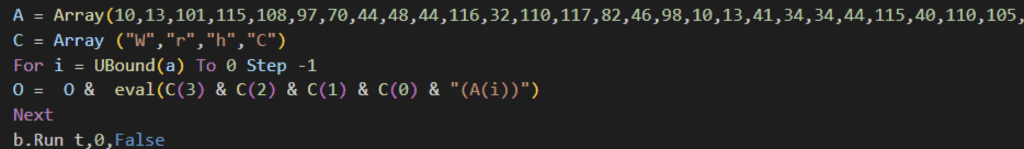
The JSCEAL campaign employs compiled JavaScript malware delivered via malicious advertisements impersonating popular cryptocurrency trading apps, targeting millions of users predominantly in the EU. This sophisticated campaign uses multi-layered infection chains, anti-analysis techniques, and Node.js to execute stealthy information stealing and remote access operations. #JSCEAL #CompiledJavaScript #CryptoMalware #NodeJS
Category: Threat Research

NOVABLIGHT is a NodeJS-based infostealer offered as Malware-as-a-Service by a group linked to Sordeal, demonstrated through French-language communications and evolving code. It features modular design, extensive system sabotage capabilities, and sophisticated obfuscation delivered via platforms like Telegram and Discord. #NOVABLIGHT #SordealGroup #Telegram #Discord

RedHook is a new Android banking trojan targeting Vietnamese users through phishing sites impersonating financial and government institutions, utilizing advanced techniques like WebSocket communication, keylogging, and screen capture via Android’s MediaProjection API. The malware’s low VirusTotal detection and Chinese-language artifacts suggest a Chinese-speaking threat actor behind the campaign. #RedHook #AndroidBankingTrojan #VietnamPhishing

Gunra ransomware has introduced a new Linux variant that enhances encryption speed and customization, enabling attackers to use up to 100 parallel encryption threads and partial file encryption. The group has expanded its targets across multiple countries and industries, showcasing advanced cross-platform tactics to increase its reach. #GunraRansomware #LinuxRansomware #Conti…
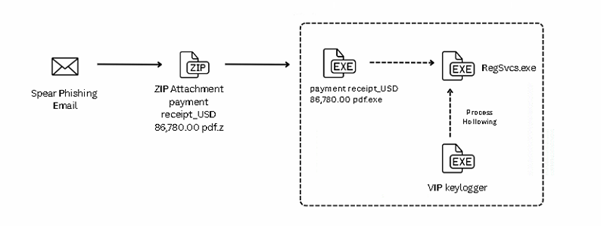
The recent campaign involving the VIP keylogger malware uses spear-phishing emails with malicious ZIP attachments and an AutoIt-based injector to deploy the payload. This malware performs keystroke logging, credential theft from major web browsers, and ensures persistence through a VBScript. #VIPKeylogger #AutoIt #RegSvcsInjection

Hacker Summer Camp in Las Vegas hosts several conferences focused on diverse aspects of information security, including application security, cloud security, red teaming, and AI security. Datadog researchers participate actively by delivering talks and open source tools while providing resources for remote attendees. #HackerSummerCamp #Datadog #AIsecurity
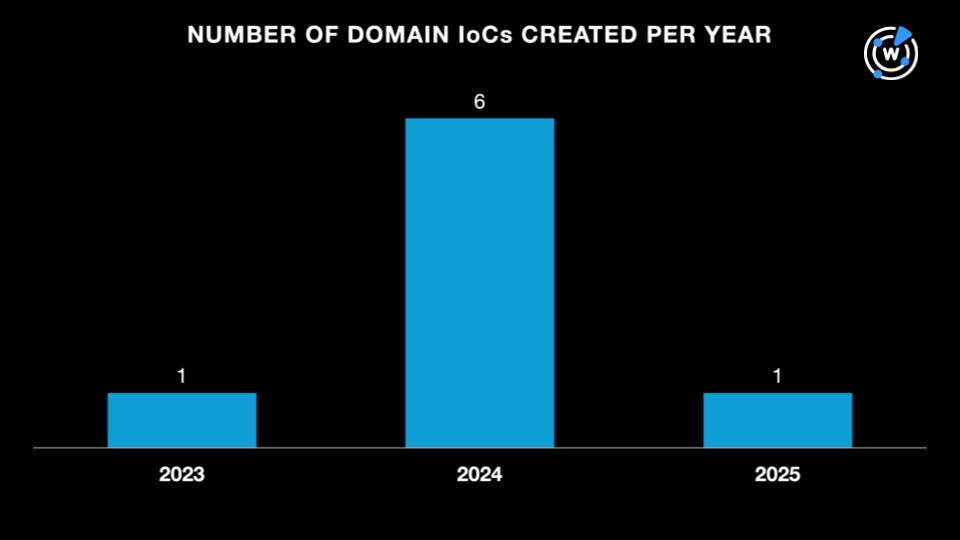
CISA added CVE-2025-32433 and CVE-2024-42009 to its Known Exploited Vulnerabilities Catalog after APT28 exploited them to breach government webmail servers in Operation RoundPress. ESET and WhoisXML API uncovered numerous related domains and IPs, revealing extensive malicious infrastructure tied to this campaign. #APT28 #RoundPress #CVE202532433 #CVE202442009
TraderTraitor is a North Korean state-sponsored cyber threat group targeting cryptocurrency and blockchain ecosystems through sophisticated social engineering, supply chain attacks, and cloud compromises. The group has been linked to massive crypto heists, including the $308 million DMM Bitcoin breach and the $1.5 billion Bybit hack. #TraderTraitor #LazarusGroup #DMMBitcoin #Bybit #JumpCloud
In September 2024, Netskope Threat Labs disclosed the discovery of XWorm malware version 6.0, which introduces enhanced persistence, anti-analysis techniques, and AMSI bypass capabilities. This latest variant marks its process as critical to prevent termination and continues to execute primarily in memory, posing ongoing threats to targeted systems. #XWorm #AMSIbypass #ProcessProtection
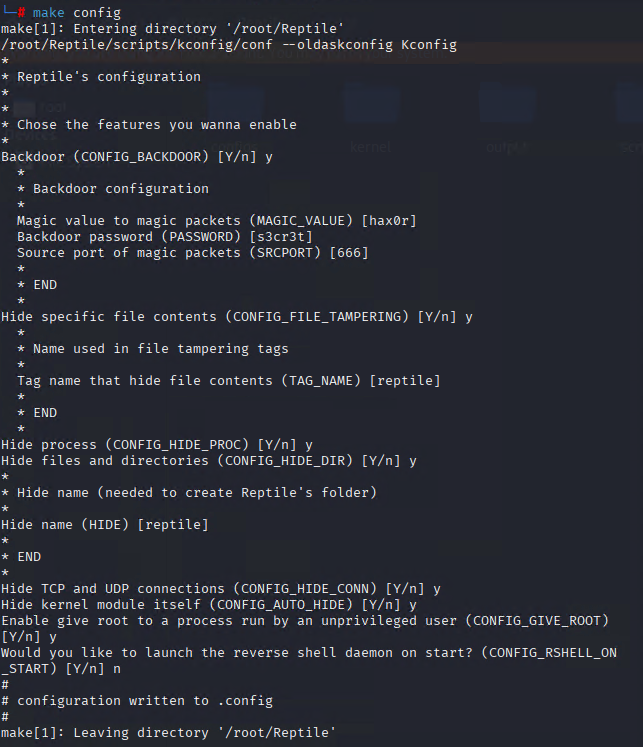
UNC3886 is an advanced persistent threat group targeting critical infrastructure sectors such as telecommunications, government, and technology through exploitation of zero-day vulnerabilities and sophisticated malware like TinyShell and Reptile. The group employs advanced techniques including custom Linux rootkits and living-off-the-land tactics to maintain stealth and persistence in compromised networks. #UNC3886 #TinyShell…
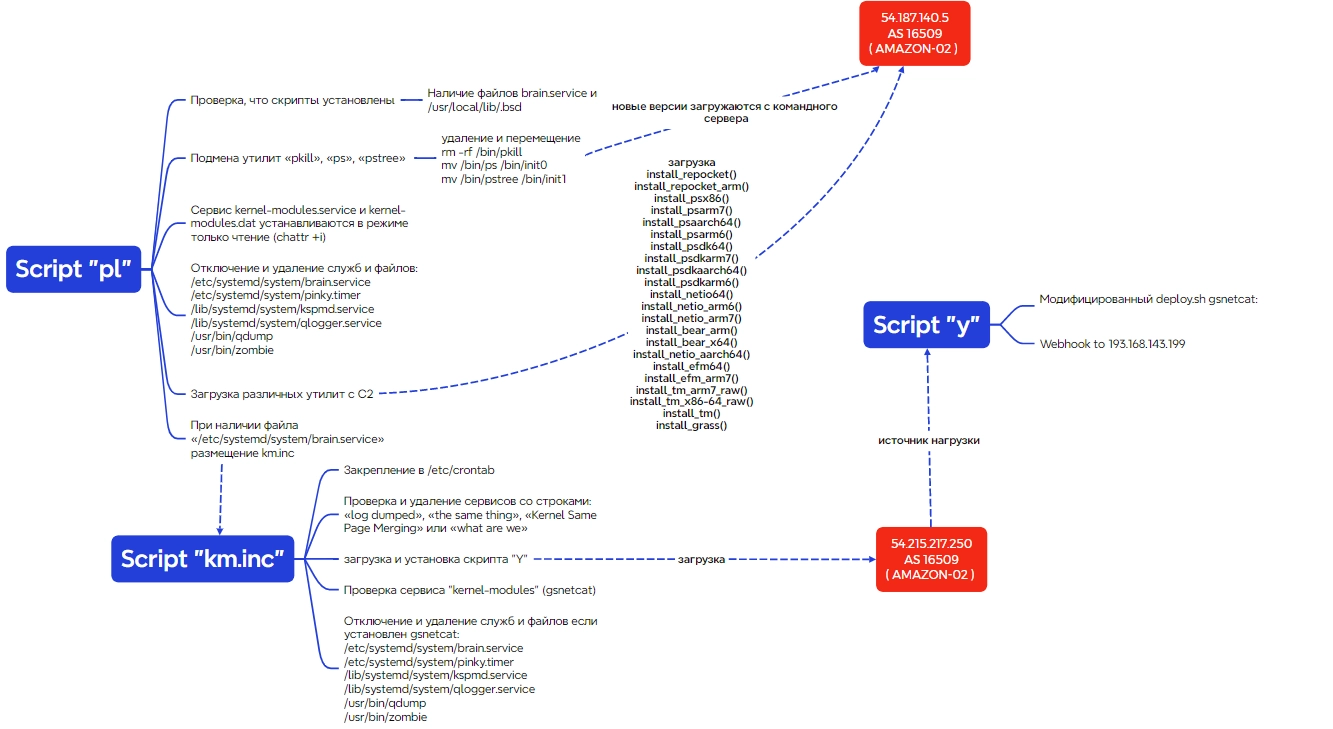
The Proxy Trickster group has been active since 2024, targeting hundreds of global IT infrastructures for financial gain through proxyjacking and cryptocurrency mining. They employ advanced evasion techniques like utility masquerading and automate attacks via complex script chains, leveraging tools such as gs-netcat for remote control. #ProxyTrickster #gs-netcat #XMRig
The 2025 Belgian Grand Prix is a prime target for cyberattacks and scams involving phishing, fake tickets, and counterfeit merchandise, affecting both fans and Formula 1 teams. High-profile incidents have demonstrated risks such as ransomware attacks and cyber espionage on teams like Ferrari and Mercedes-AMG Petronas. #RansomEXX #Ferrari #BelgianGrandPrix2025
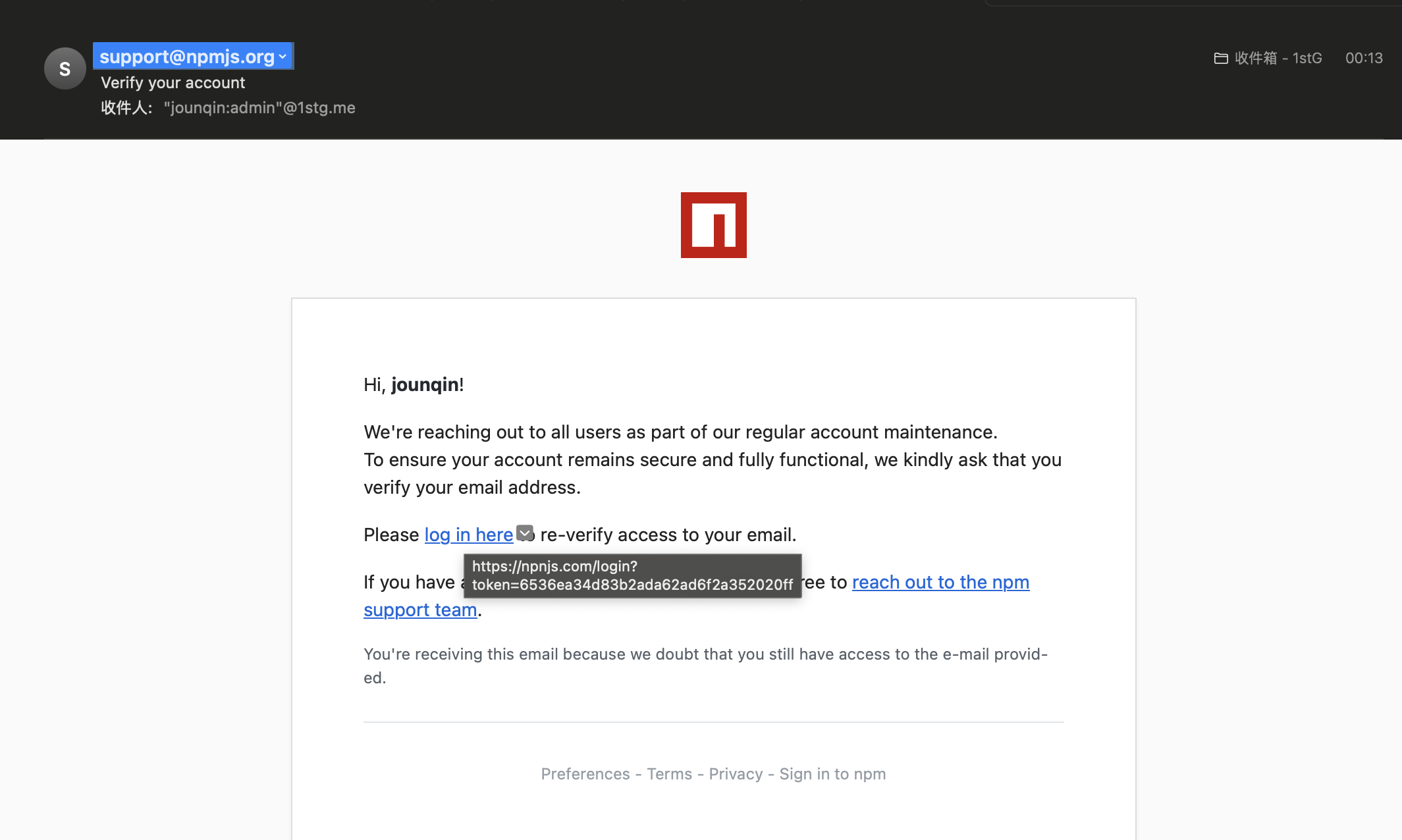
A compromised NPM package, eslint-config-prettier, was used to distribute the Scavenger Loader malware, which includes sophisticated anti-analysis features and delivers stealer payloads. The loader communicates with a hard-coded C2 infrastructure to download and execute additional modules, including theft of npmrc files that could lead to further compromise. #ScavengerLoader #eslint-config-prettier #SupplyChainAttack…
The SlowMist security team uncovered a crypto-stealing mechanism hidden within open-source Solana trading bots on GitHub that exfiltrate private keys to attacker-controlled servers. The attack exploits user trust in open-source projects by embedding malicious code that sends sensitive data silently upon execution. #Solana #pumpfun #SlowMist…

A phishing campaign exploiting fears during the Israel-Iran conflict offered fraudulent evacuation flights on a fake Embraer Lineage 1000E jet, aiming to steal personal and financial information. The scam involved a suspicious domain and fake booking details, misleading users with unrealistic prices and travel logistics. #OperationRisingLion #lineageembraer.online