Multiple threat actors are exploiting on-premises Microsoft SharePoint servers using a new exploit chain called “ToolShell,” combining patched and zero-day vulnerabilities to achieve remote code execution. Advanced web shells like GhostWebShell and tools like KeySiphon enable attackers to maintain persistence and steal sensitive cryptographic keys, posing a critical risk to affected organizations. #ToolShell #GhostWebShell #KeySiphon #MicrosoftSharePoint #FortiGuardLabs
Category: Threat Research
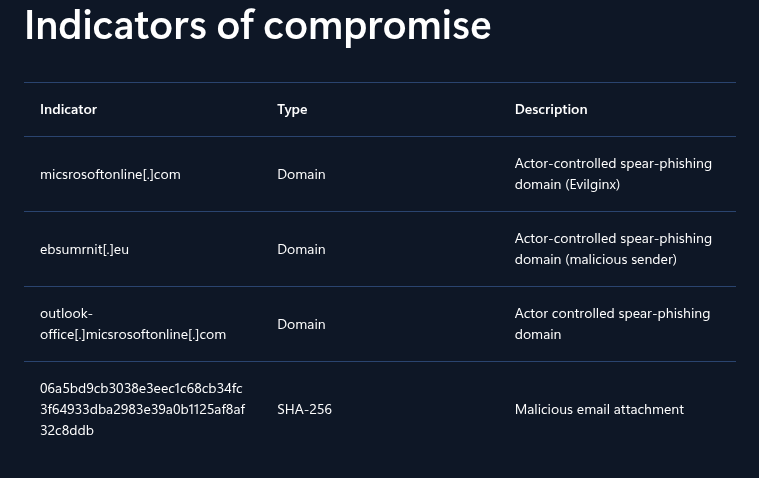
Laundry Bear, also known as Void Blizzard, is a Russian state-sponsored APT active since April 2024 targeting NATO countries and Ukraine using spear phishing and credential theft. Using Validin’s advanced pivoting techniques, multiple additional malicious domains and infrastructure linked to Laundry Bear have been uncovered, expanding beyond initial Microsoft-reported indicators. #LaundryBear #VoidBlizzard #Validin

Raven Stealer is a sophisticated information-stealing malware targeting Chromium-based browsers through in-memory DLL injection and exfiltrating data via Telegram bots. It is actively developed and distributed by the ZeroTrace Team using GitHub and Telegram channels, facilitating credential theft campaigns with high stealth and ease of deployment. #RavenStealer #ZeroTraceTeam #TelegramC2
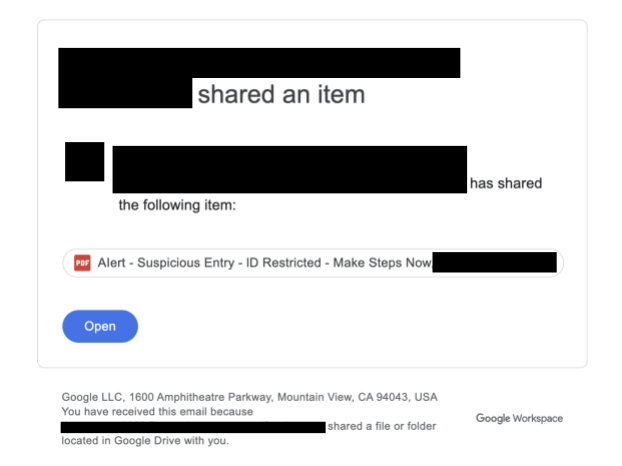
Homograph attacks exploit visually similar non-Latin characters to evade email security filters and impersonate trusted entities, leading to potential credential theft and malware infection. Three real-world case studies demonstrate how threat actors use homographs in email fields to bypass detection and deliver malicious content. #HomographAttack #PaloAltoNetworks #Unit42…
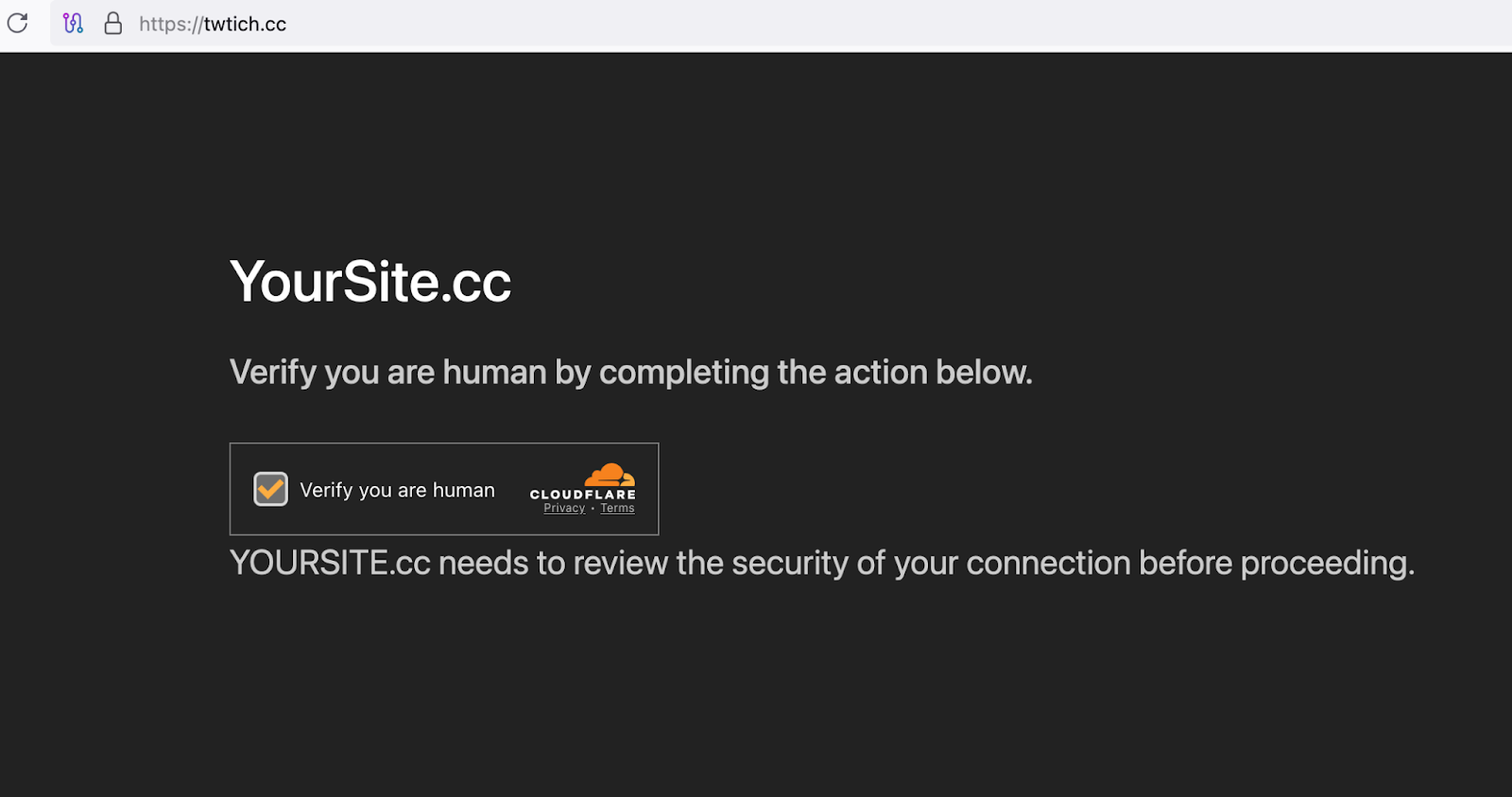
CloudSEK’s TRIAD discovered a Clickfix-themed malware delivery site linked to the Epsilon Red ransomware that uses ActiveX to silently execute shell commands and download payloads. The threat actors employ social engineering with fake verification codes and impersonate popular services like Discord Captcha Bot and Twitch to increase victim engagement. #EpsilonRed #Clickfix #DiscordCaptchaBot
Cybercriminal EncryptHub abused the Steam platform by embedding Trojan downloaders within the early access game Chemia, distributing multiple information stealers such as Fickle Stealer, HijackLoader, and Vidar. This incident highlights how popular gaming platforms can be exploited to spread malware targeting gamers’ sensitive data and digital assets. #EncryptHub #Chemia #FickleStealer #Vidar…

A deeply obfuscated ASPX web shell named UpdateChecker.aspx was analyzed, revealing its use on compromised Microsoft IIS servers to enable full remote control over affected Windows systems. The web shell uses encrypted JSON-formatted commands sent via HTTP POST requests to execute a wide range of operations including file manipulation and command execution. #UpdateChecker.aspx #MicrosoftIIS #WebShell

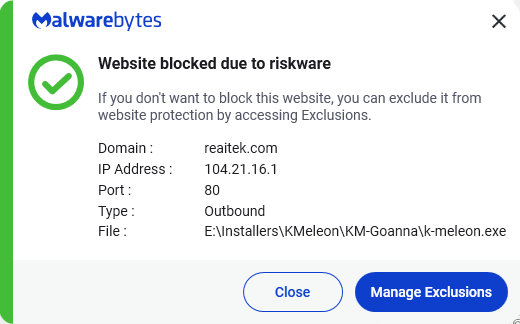
Cyber Stealer is a sophisticated and actively developed infostealer and botnet malware discovered in May 2025, targeting a wide range of applications including browsers, cryptocurrency wallets, and communication platforms. It features extensive data theft capabilities, modular functionalities like cryptocurrency mining and DDoS, and communicates with its C2 server for updates and commands. #CyberStealer #eSentire #ClipperModule

Acronis Threat Research Unit discovered a malware campaign using Leet Stealer, RMC Stealer, and Sniffer Stealer disguised as fake indie games distributed mainly via Discord. These stealers target browser data, credentials, and Discord tokens, enabling attackers to perform extortion, impersonation, and financial theft. #LeetStealer #RMCStealer #SnifferStealer #Discord

UNC6040 is a threat group conducting voice phishing (vishing) campaigns to breach Salesforce environments and steal large volumes of sensitive data for extortion purposes. Their attacks involve impersonating IT support to trick employees into authorizing malicious apps, enabling data exfiltration and lateral network movement. #UNC6040 #Salesforce #ShinyHunters…

An Android malware poses as legitimate Indian banking apps to steal credentials, intercept SMS, and execute unauthorized financial activities using advanced stealth and persistence techniques. It exploits Android permissions, employs Firebase for command-and-control, and uses phishing interfaces to deceive users. #AndroidBankingMalware #FirebaseC2 #CredentialTheft

Azure App Services stores encrypted tokens for authenticated sessions that can be decrypted by users with Contributor permissions, enabling access to applications as other users. A PowerShell tool has been developed to automate the extraction and decryption of these tokens, aiding penetration testers in simulating real-world attacks. #AzureAppServices #EasyAuth #GetAzWebAppTokens
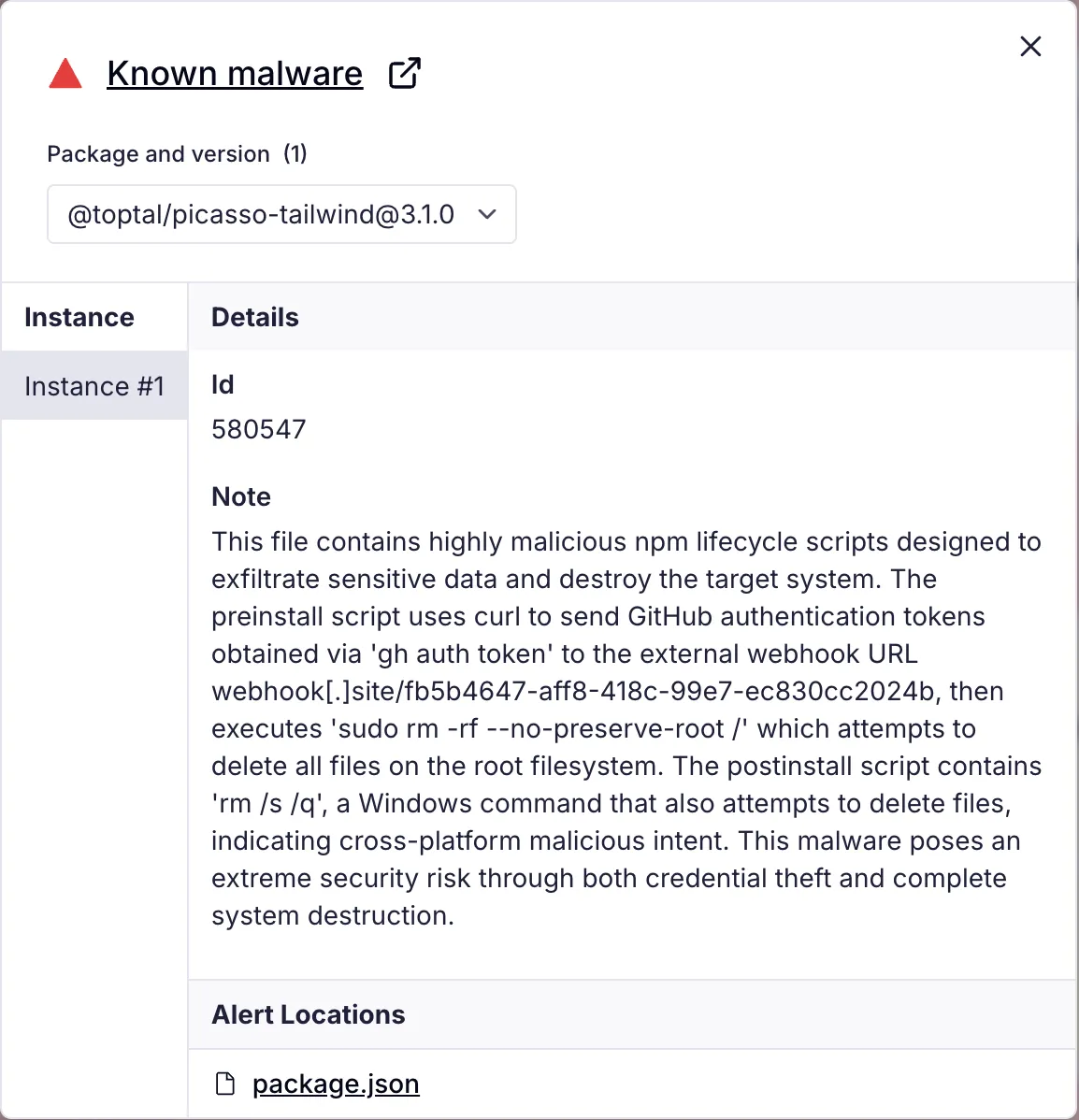
Threat actors compromised Toptal’s GitHub organization, publishing 73 repositories publicly, including at least 10 with malicious payloads designed to steal GitHub authentication tokens and destroy victim systems. The attack used npm package lifecycle hooks to execute token exfiltration and system deletion commands across Unix and Windows platforms. #Toptal #GitHub #SupplyChainCompromise

AhnLab TIP monitors ransomware group activities on the dark web, highlighting Gunra ransomware’s use of leaked Conti code with enhanced social engineering tactics and time-based pressure. Gunra ransomware encrypts files with ChaCha20 using RSA key generation and deletes volume shadow copies to prevent recovery. #Gunra #Conti #AhnLabTIP…

In June 2025, two coordinated cyberattacks, Operation GhostChat and Operation PhantomPrayers, targeted the Tibetan community leveraging the Dalai Lama’s 90th birthday to distribute Ghost RAT and PhantomNet backdoors via malicious web compromises. These attacks employed sophisticated multi-stage infection chains involving DLL sideloading, shellcode injection, and encrypted payloads, attributed to a China-nexus APT group. #GhostRAT #PhantomNet #ChinaAPT #TibetanCommunity