Cybercriminal EncryptHub abused the Steam platform by embedding Trojan downloaders within the early access game Chemia, distributing multiple information stealers such as Fickle Stealer, HijackLoader, and Vidar. This incident highlights how popular gaming platforms can be exploited to spread malware targeting gamers’ sensitive data and digital assets. #EncryptHub #Chemia #FickleStealer #Vidar #HijackLoader
Keypoints
- EncryptHub injected a Trojan downloader into the early access game Chemia on Steam starting July 22, 2025.
- The Trojan downloader was used to install Fickle Stealer, HijackLoader, and Vidar malware on infected machines.
- Vidar operates as Malware-as-a-Service, using platforms like Steam for its command and control infrastructure.
- Fickle Stealer uses PowerShell scripts to bypass User Account Control and steal sensitive system and browser data.
- HijackLoader is used to load additional malware such as Danabot and RedLine stealer onto compromised devices.
- Steam’s large user base makes it a lucrative target for cybercriminals to distribute malicious software through game files.
- Gamers are advised to verify game invitations, avoid unsolicited downloads, and run updated anti-malware solutions to stay protected.
MITRE Techniques
- [T1059 ] Command and Scripting Interpreter – Fickle Stealer uses PowerShell scripts to bypass User Account Control (“uses PowerShell scripts to bypass User Account Control (UAC)”).
- [T1105 ] Ingress Tool Transfer – Trojan downloader delivers multiple malware payloads including Fickle Stealer, HijackLoader, and Vidar (“added a Trojan downloader to the game files that runs alongside the actual application”).
- [T1543 ] Create or Modify System Process – The Trojan downloader establishes persistence on infected machines (“The downloader establishes persistence on the affected machine”).
- [T1071 ] Application Layer Protocol – Vidar uses public networks such as Steam for command and control communications (“Vidar…uses public networks such as social media, communication platforms—and Steam—as parts of its Command & Control infrastructure”).
Indicators of Compromise
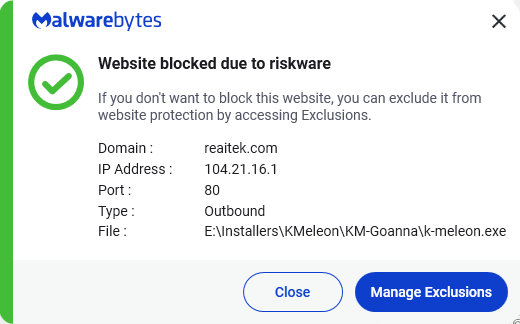
- [Domain ] Malicious domains used for hosting malware and scripts – soft-gets[.]com, reaitek[.]com, safesurf.fastdomain-uoemathhvq.workers[.]dev
- [File Hash ] Fickle Stealer downloader – ed076c27b420bfa66c251488b4121913fa461367a60c5fa32cee3953efcae32b
- [File Hash ] Fickle Stealer payload – 6fb7fd9763d6b269793c80bbc03a1be358390781af4b698fba1591cb8dbb8825
- [File Hash ] Vidar Stealer – 2cd8c0e75cf76381f06dfe465a542e52eefa713b0bea2557763e0c0c45b21481
- [File Hash ] HijackLoader samples – 9a733b2de84e2bf466287abd034b04b18c8c269535606e8f6403eee2a3b288c4, 12935315254175719cbbaad0b213204ddebd4100ffc551d54f8cf39ced1be227
Read more: https://www.malwarebytes.com/blog/news/2025/07/steam-games-abused-to-deliver-malware-once-again