Request for Quote (RFQ) scammers exploit vendor-supplied Net financing options to fraudulently acquire high-value electronics and goods, using stolen identities and fake business credentials. Proofpoint researchers disrupted these operations by taking down malicious domains and intercepting shipments, highlighting the complexity and sophistication of these scams. #NetRFQScam #Proofpoint #FreightForwardingFraud
Keypoints
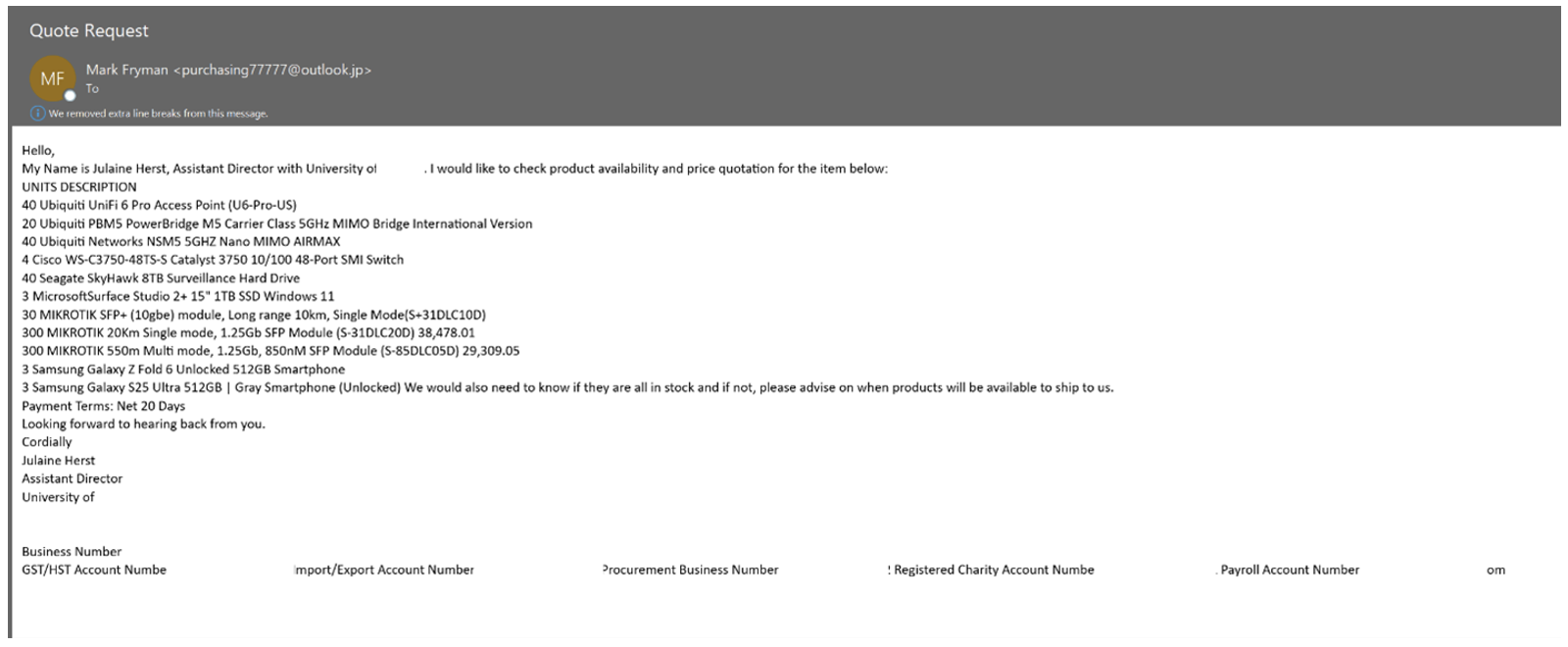
- RFQ scammers use vendor Net financing terms (Net 15/30/45) to obtain goods by posing as legitimate procurement agents.
- Threat actors employ stolen business information such as EINs, DUNS numbers, and employee identities to create believable requests.
- Commonly targeted products include technology equipment like Fluke testing tools, hard drives, surveillance cameras, and medical devices.
- Scammers rely on freight forwarding services and residential addresses, especially linking shipments to West African countries, with warehouses rented for logistics.
- Proofpoint’s takedown efforts removed 19 malicious domains and coordinated with shipping companies to stop fraudulent deliveries.
- The scammers often use lookalike domains and free email accounts to impersonate organizations and increase credibility.
- Organizations are advised to verify delivery addresses and email domains and exercise caution with urgent financing and shipping requests.
MITRE Techniques
- [T1587.001] Develop Capabilities: Domain Generation – The actors create lookalike domains mimicking legitimate companies to send fraudulent RFQ emails (use of “lookalike domain—capitalizing on a trusted brand’s reputation”).
- [T1586.001] Compromise Infrastructure: Email Accounts – Use of free or spoofed email accounts to impersonate procurement agents (“many threat actors send these quote requests from a free email account”).
- [T1078] Valid Accounts – Use of stolen identities, EINs, and DUNS numbers to create convincing credit applications (“fraudsters posing as procurement agents using stolen or publicly available information like EINs”).
- [T1584] Compromise Infrastructure: Proxy Services – Use of shipping forwarding services and mules to receive and transport stolen goods (“network of shipping forwarding services, standalone warehouses, and individual money mules to enable their crimes”).
Indicators of Compromise
- [Domains] Malicious and lookalike domains related to RFQ scams – novartispharmaceuticalscorp[.]com, hbfullercompany[.]net, magnetek-inc[.]com, and 16 more domains taken down by Proofpoint.
- [Email Addresses] Threat actor-controlled email addresses used to communicate with shipping carriers and targets (specific addresses not disclosed; used to intercept fraudulent shipments).
- [Delivery Addresses] Use of residential addresses and freight forwarding service locations in West Africa for shipment reception.
- [Business Identifiers] Stolen business information including Employer Identification Numbers (EINs) and Data Universal Numbering System (DUNS) numbers used for credit applications.