A zero-day vulnerability, CVE-2025-53770, in Microsoft SharePoint Server allows unauthenticated remote code execution by exposing MachineKey configuration details. The vulnerability is actively exploited in the wild, with thousands of SharePoint servers potentially affected, and patches for related vulnerabilities have been released but not yet for CVE-2025-53770. #CVE202553770 #SharePoint #ToolShell
Keypoints
- A zero-day SharePoint vulnerability, CVE-2025-53770, permits unauthenticated remote code execution by leaking MachineKey configuration details.
- CVE-2025-53770 is a variant of the earlier ToolShell vulnerability CVE-2025-49706, both affecting Microsoft SharePoint Server.
- Researchers reported active, large-scale exploitation of SharePoint servers globally starting July 19, 2025.
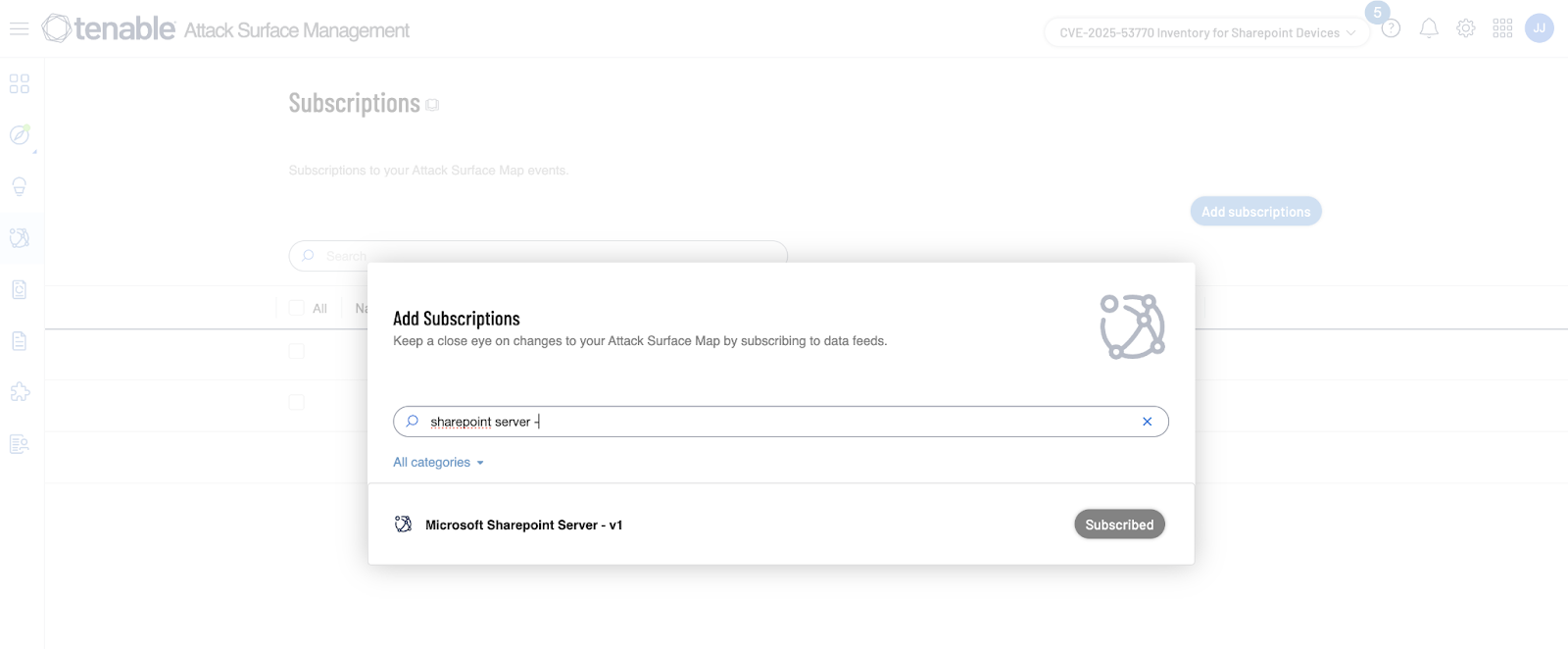
- At least 9,300 SharePoint servers were found publicly accessible as of July 20, but not all are vulnerable.
- No proof-of-concept is available for CVE-2025-53770, though variants in the ToolShell chain have been reproduced.
- Microsoft released patches for ToolShell vulnerabilities on July 2025 Patch Tuesday, but CVE-2025-53770 remains unpatched.
- Indicators of compromise include creation of the spinstall0.aspx file and specific IP addresses and user agent strings used in exploitation.
MITRE Techniques
- [T1190] Exploit Public-Facing Application – CVE-2025-53770 exploits a SharePoint Server vulnerability allowing unauthenticated remote code execution (“Successful exploitation of CVE-2025-53770 could grant an attacker the ability to obtain MachineKey configuration details … and enable unauthenticated remote code execution”).
- [T1105] Ingress Tool Transfer – Attackers create spinstall0.aspx on compromised SharePoint servers to retrieve MachineKey configuration details (“creation of a file, spinstall0.aspx, on vulnerable SharePoint Servers”).
- [T1566] Phishing – The exploitation involves specially crafted requests exploiting spoofing vulnerabilities (“Microsoft SharePoint Server Spoofing Vulnerability”).
Indicators of Compromise
- [File Name] Creation of spinstall0.aspx on SharePoint Servers used to obtain MachineKey configuration.
- [IP Addresses] Several known malicious IPs used in attacks as listed by Eye Security and Shadowserver Foundation (specific IP examples not provided in the article).
- [User Agent Strings] Malicious user agent strings identified in exploitation attempts (exact examples not provided).