Multiple critical vulnerabilities affecting on-premises Microsoft SharePoint servers have been actively exploited to bypass authentication and gain unauthorized access, leading to data exfiltration and persistent backdoors. Immediate patching, cryptographic material rotation, and professional incident response are strongly advised to mitigate these ongoing threats. #CVE-2025-49704 #CVE-2025-53770 #MicrosoftSharePoint
Keypoints
- Four critical vulnerabilities (CVE-2025-49704, CVE-2025-49706, CVE-2025-53770, CVE-2025-53771) affect on-premises Microsoft SharePoint Server 2016, 2019, and Subscription Edition, allowing code execution and spoofing.
- SharePoint Online in Microsoft 365 is not impacted by these vulnerabilities.
- Exploitation includes bypassing MFA and SSO to gain privileged access, exfiltrate sensitive data, deploy backdoors, and steal cryptographic keys.
- Attack chains such as “ToolShell” demonstrate unauthenticated access and arbitrary command execution on vulnerable SharePoint instances.
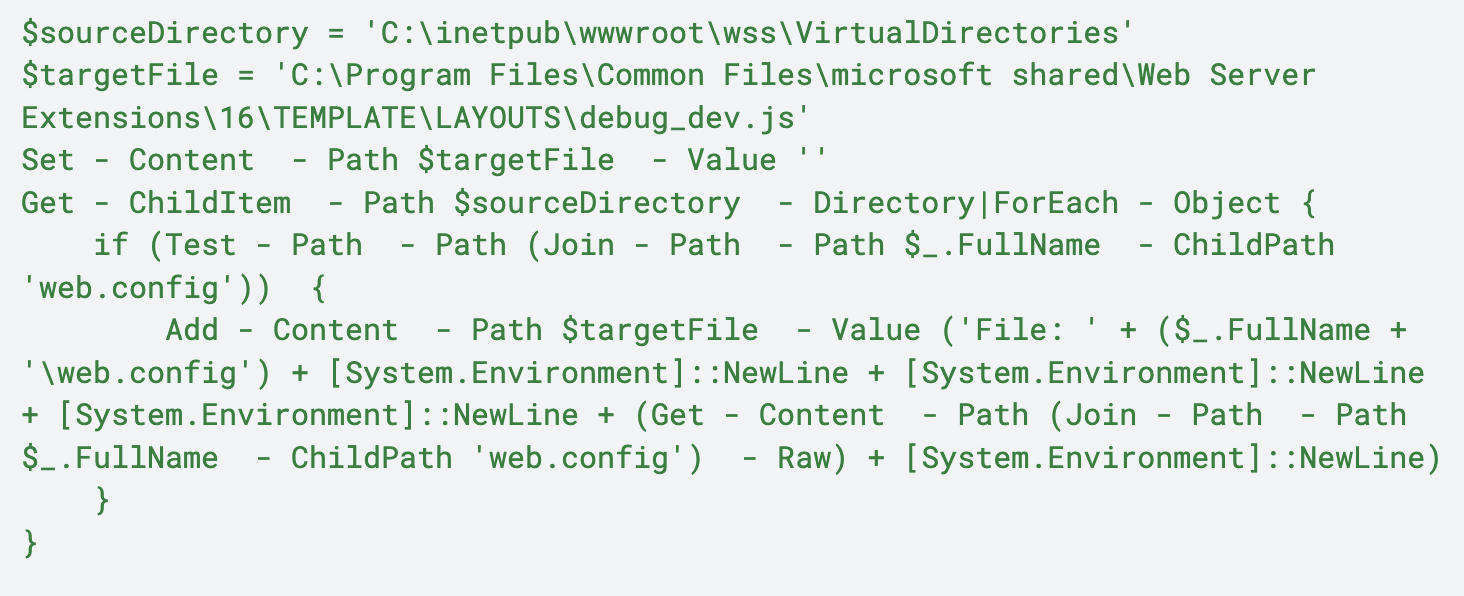
- Multiple observed exploitation variations involve PowerShell commands creating web shells (spinstall0.aspx) and harvesting configuration files.
- Palo Alto Networks and Unit 42 recommend immediate disconnection of vulnerable servers from the internet, patching, cryptographic rotation, and engaging incident response teams.
- Palo Alto Networks products like Cortex XDR and Cortex Xpanse provide detection, blocking, and exposure identification capabilities against these threats.
MITRE Techniques
- [T1059] Command and Scripting Interpreter – Attackers executed PowerShell commands via command shell to run arbitrary code and create web shells (‘Commands seen in active exploitation of the SharePoint vulnerability’).
- [T1036] Masquerading – Use of spoofing and impersonation techniques to bypass authentication (‘Improper authentication in Microsoft Office SharePoint allows an authorized attacker to perform spoofing over a network’).
- [T1105] Ingress Tool Transfer – Attackers deployed spinstall0.aspx web shell to the server for persistent access (‘The spinstall0.aspx file is a web shell that can execute various functions to retrieve ValidationKeys, DecryptionKeys and the CompatibilityMode of the server’).
- [T1041] Exfiltration Over C2 Channel – Exfiltration of sensitive data including cryptographic keys after gaining privileged access (‘Once inside, they’re exfiltrating sensitive data, deploying persistent backdoors and stealing cryptographic keys’).
- [T1078] Valid Accounts – Bypassing identity controls, including MFA and SSO, to gain privileged access (‘Attackers are bypassing identity controls, including multi-factor authentication (MFA) and single sign-on (SSO), to gain privileged access’).
Indicators of Compromise
- [IP Address] Exploitation source IPs – 107.191.58[.]76, 104.238.159[.]149, and 8 more IP addresses associated with attacks.
- [File Path] Created or modified files during exploitation – C:PROGRA~1COMMON~1MICROS~1WEBSER~116TEMPLATELAYOUTSspinstall0.aspx, C:PROGRA~1COMMON~1MICROS~1WEBSER~115TEMPLATELAYOUTSspinstall0.aspx, and debug_dev.js file path.
- [File Hash] .NET modules used in exploitation – 4A02A72AEDC3356D8CB38F01F0E0B9F26DDC5CCB7C0F04A561337CF24AA84030, B39C14BECB62AEB55DF7FD55C814AFBB0D659687D947D917512FE67973100B70, and five more hashes.