Validin has launched significant enhancements to its threat intelligence platform, including over 8 months of historical HTTPS banner data and on-demand access to full HTTP response artifacts. These upgrades enable deeper threat hunting, malware infrastructure analysis, and incident response capabilities, as demonstrated by uncovering additional Lazarus Group infrastructure linked to the Bybit heist. #Validin #TraderTraitor #LazarusGroup
Keypoints
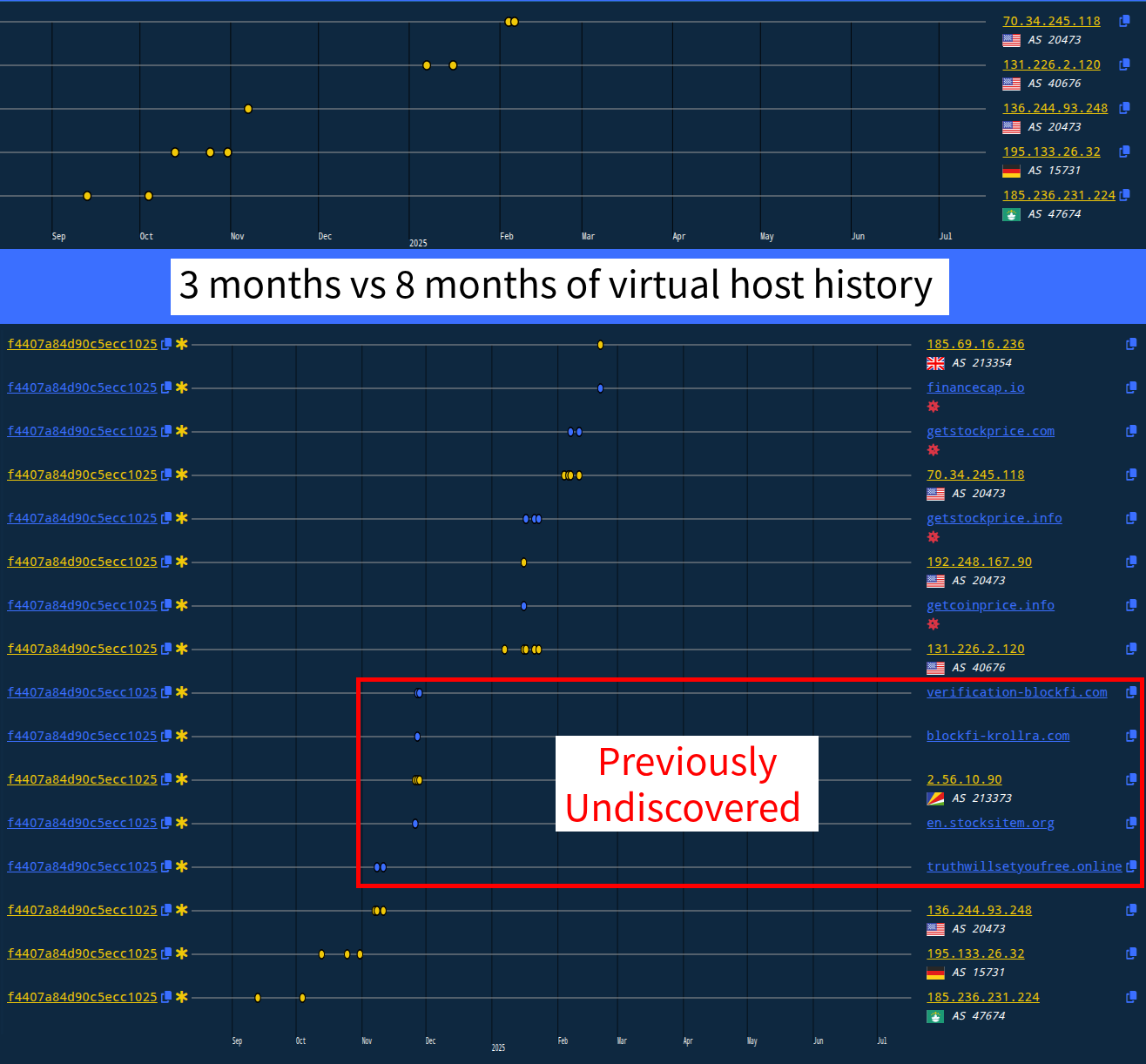
- Validin now provides searchable access to more than 100 billion HTTPS banner and virtual host responses dating back over 8 months to early November 2024.
- The platform offers on-demand access to complete HTTP response artifacts, including HTML content, favicons, and SSL/TLS certificates.
- Expanded historical data enables analysts to monitor changes in malicious domains and IPs, track pre- and post-weaponization, and identify operational security mistakes.
- Validin processes vast internet infrastructure data daily, including over 5 billion domain name resolutions and nearly 1 billion host responses, supported by a patented cloud-agnostic database.
- The host response history was used to identify previously unknown infrastructure linked to the Lazarus Group’s “TraderTraitor” campaign involved in the Bybit heist.
- Enterprise users can view, copy, and download full HTML pages, favicon files, and human-readable as well as raw SSL certificate data via a user-friendly interface.
- These advancements strengthen Validin’s position as a leading threat intelligence provider for threat hunters, analysts, and incident responders.
MITRE Techniques
- [T1583] Acquire Infrastructure – Used to monitor the activation and weaponization lifecycle of malicious domains and IPs (“When was a domain first active? Was there a delay between activation and weaponization?”).
- [T1598] Phishing – Historical domain tracking helps detect phishing domain setup and timelines (“malware infrastructure analysis, phishing domain tracking”).
- [T1609] Container and Resource Discovery – Analyzing HTTP/S banners, favicons, and certificates for host response features to identify adversary behaviors (“importance of HTTP/S banners and host response features”).
Indicators of Compromise
- [Domain] Previously unknown domain linked to Lazarus Group activity – en.stocksitem.org
- [IP Address] New IP address related to TraderTraitor activity – 2.56.10.90
- [Header Hash] Specific HTTP header hash aiding in cluster identification – f4407a84d90c5ecc1025
- [HTML Title Tag] “404 Not Found” used as cluster identification tag
- [Artifact Hashes] HTTPS banner hashes, favicon hashes, and SSL certificate fingerprints used for historic search and analysis
Read more: https://www.validin.com/blog/crawl_history_artifact_upgrade/