The Slow Pisces threat actors targeted cryptocurrency developers on LinkedIn by posing as employers and distributing malware disguised as coding challenges, infecting victims with RN Loader and RN Stealer. Analysis of 54 indicators of compromise led to the discovery of numerous connected domains, IP addresses, and email-related artifacts, revealing a broad and evolving infrastructure. #SlowPisces #RNLoader #RNStealer
Keypoints
- Slow Pisces threat actors engaged cryptocurrency developers on LinkedIn, distributing malware disguised as coding challenges, leading to infections by RN Loader and RN Stealer.
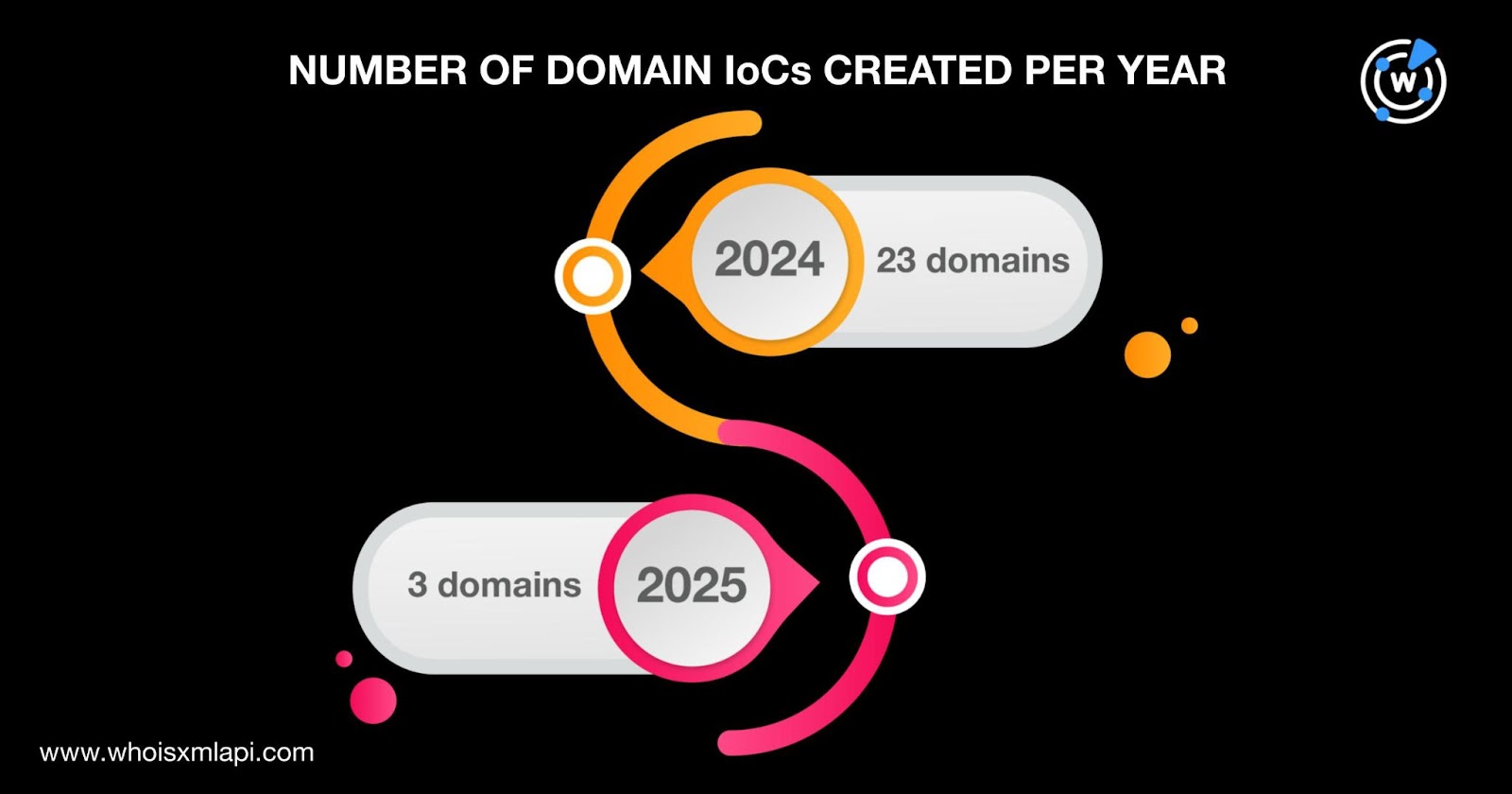
- Palo Alto Unit 42 identified 54 IoCs including 27 domains and 27 IP addresses, which were further expanded through WhoisXML API analysis.
- Domains associated with the campaign were primarily registered via Namecheap between 2024 and 2025, with a high concentration registered in Iceland and the U.S.
- Historical domain-to-IP and IP-to-domain resolution data revealed re-registrations and long-term activity dating back to 2017 on certain domains and IPs.
- IP addresses linked to the activity were geolocated across 12 countries, with significant presence in the Netherlands, France, Poland, and the U.K.
- Command-and-control IP addresses were identified and analyzed, revealing ongoing communication patterns with victim IPs over HTTPS.
- Expansion of IoCs uncovered 551 email-connected domains and additional malicious IP addresses, indicating a large and complex infrastructure supporting the campaign.
MITRE Techniques
- [T1193] Spearphishing Attachment – Threat actors used malware disguised as coding challenges sent to cryptocurrency developers via LinkedIn messages (“posing as potential employers and sent malware disguised as coding challenges”).
- [T1105] Ingress Tool Transfer – Compromised projects including RN Loader and RN Stealer were delivered to and executed on victim systems (“infecting their systems with RN Loader and RN Stealer”).
- [T1574] Hijack Execution Flow – The campaign utilized domain and IP re-registration to maintain persistence and evade detection (“domains created recently but resolved to IP addresses from years ago”).
Indicators of Compromise
- [Domain] Identified IoCs include 27 domains primarily registered through Namecheap, e.g., leaguehub[.]net, bitzone[.]io, and stocksindex[.]org, with many showing historical resolution data.
- [IP Address] 27 IP addresses geolocated across 12 countries, such as 54[.]39[.]83[.]151 and 91[.]103[.]140[.]191, with several linked to command-and-control activity.
- [Email Domain] 551 email-connected domains discovered via historical WHOIS data linked to IoC email addresses.
- [Email Address] 44 email addresses found in historical WHOIS records of the identified domains, including 7 public emails used to trace further IoCs.
- [Additional IP] One new malicious IP address 199[.]59[.]243[.]228 identified beyond the initial IoCs.