AhnLab Security Intelligence Center (ASEC) has identified attacks on poorly managed Linux servers using the SVF Botnet, a Python-based DDoS bot that communicates via Discord and employs multiple proxy servers. The malware facilitates various DDoS attack methods, including L7 HTTP Flood and L4 UDP Flood, and uses public proxy lists to…
Category: Threat Research

A sophisticated Red Bull-themed phishing campaign utilized legitimate email services and validated TLS certificates to bypass standard security measures and steal user credentials via a fake Facebook login page. The attackers employed multi-domain infrastructure, stalling techniques, and brand impersonation to evade detection and scale their fraudulent operation. #RedBullPhishing #MailgunAbuse #JARMFingerprint

The ToolShell exploit chain leverages multiple SharePoint vulnerabilities to gain unauthenticated remote code execution and silently extract cryptographic keys, enabling attackers to forge trusted requests and maintain persistent access. This active threat targets especially unpatched on-premises SharePoint Server versions 2016 and earlier, posing a high risk to organizations that have not…
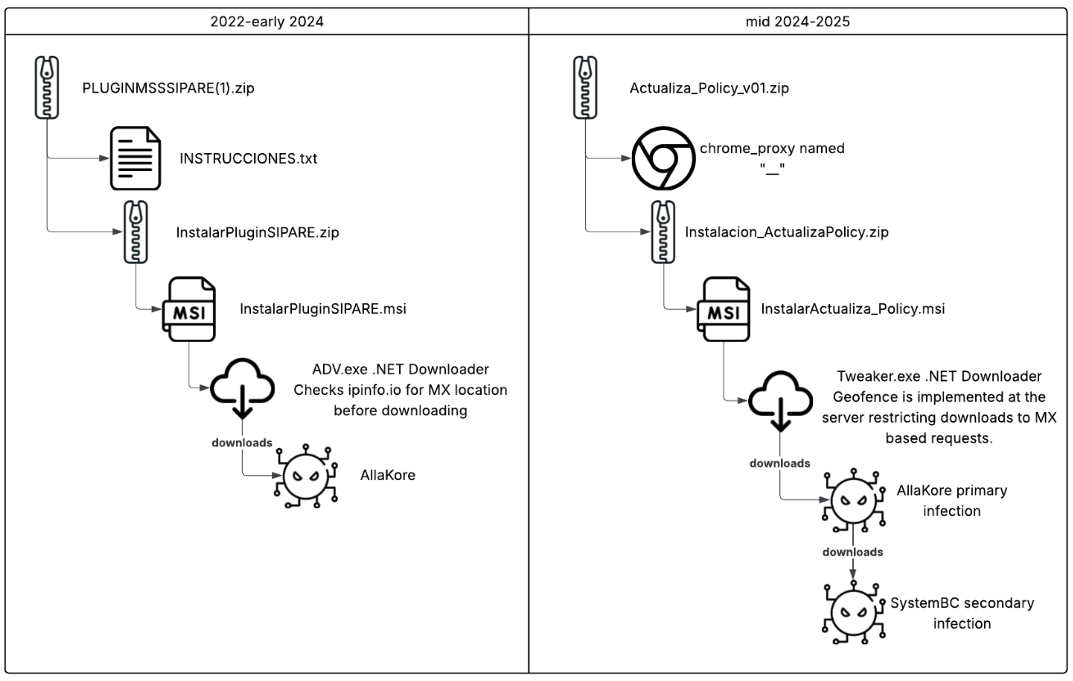
The Greedy Sponge threat actor has targeted Mexican organizations since 2021 using a heavily modified AllaKore RAT and additional malware like SystemBC for financial fraud. Recent campaigns employ advanced techniques such as server-side geofencing and custom data exfiltration methods to evade detection and steal banking credentials. #GreedySponge #AllaKore #SystemBC
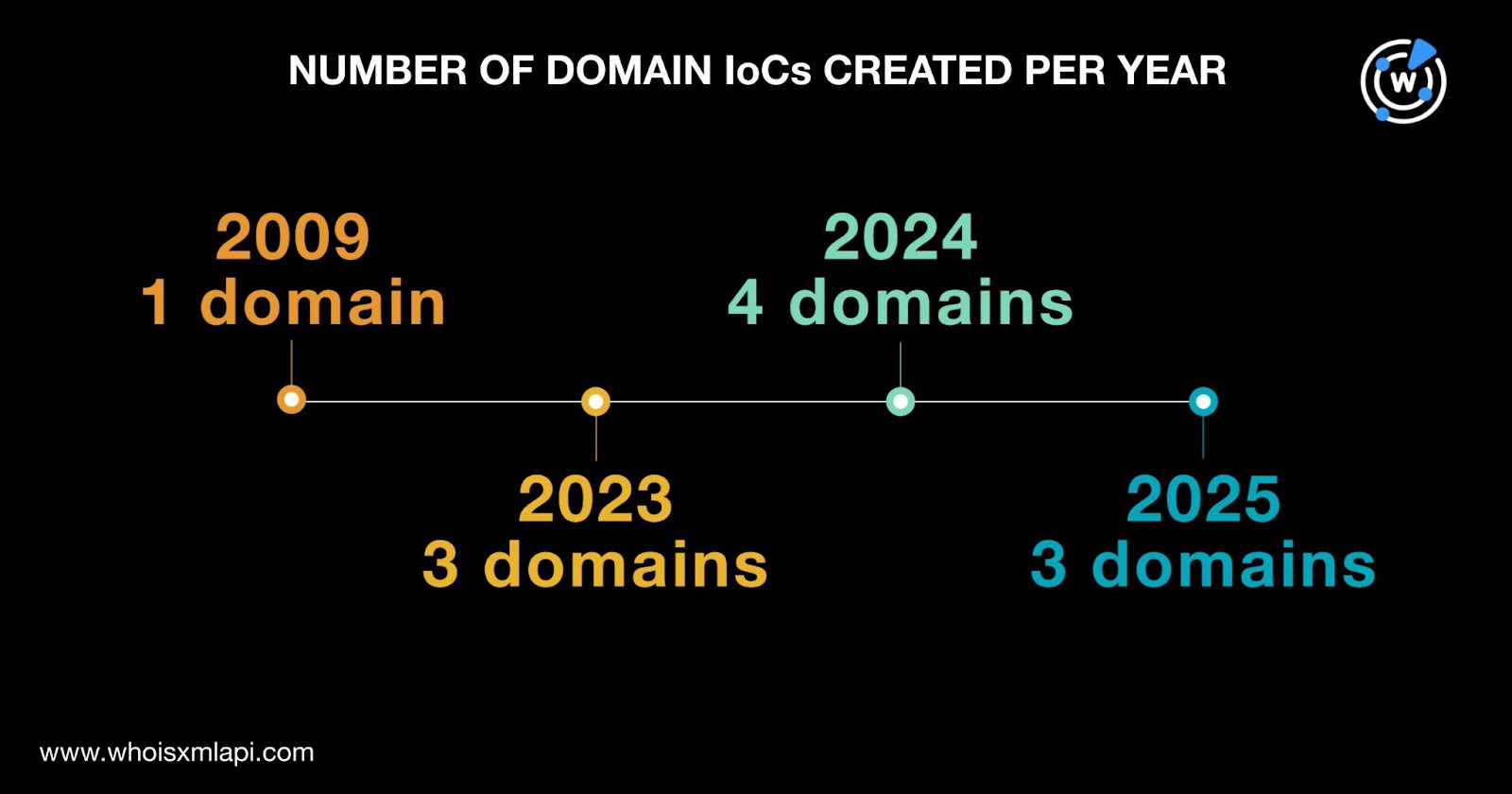
UNC5174, a Chinese-affiliated threat actor, has updated its attack toolkit with new open-source tools named “SNOWLIGHT” and “VShell,” expanding their command-and-control infrastructure and cyberattack capabilities. Recent investigations revealed more than 70 indicators of compromise (IoCs), including domains and IP addresses distributed globally, some of which have been weaponized in active attacks. #UNC5174 #SNOWLIGHT #VShell

KAWA4096 is a ransomware that emerged in June 2025, targeting countries like the United States and Japan, and features encryption of network shares and multithreading for efficient file encryption. Its data leak site mimics the Akira ransomware group while its ransom note resembles Qilin’s, aiming to boost its credibility and visibility. #KAWA4096 #Akira #Qilin
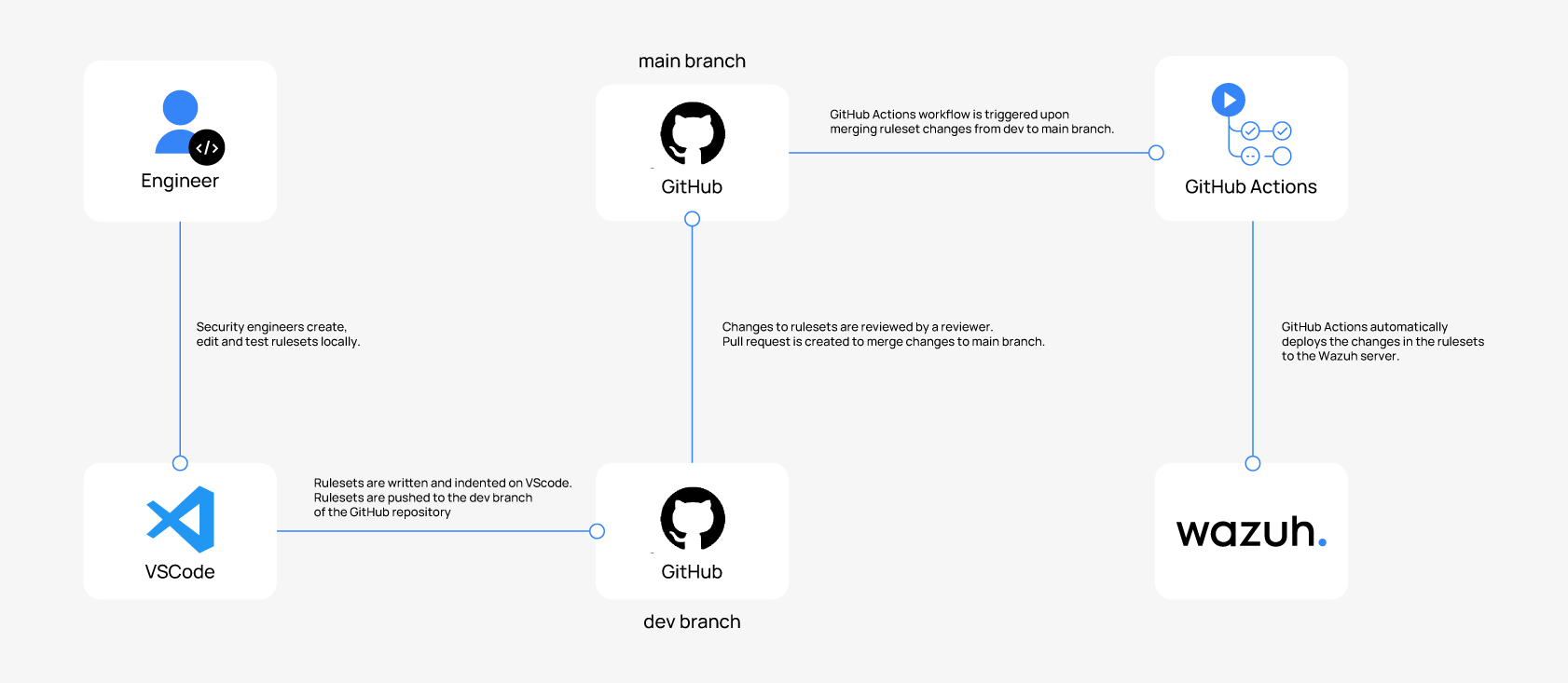
Wazuh Ruleset as Code (RaC) enables security teams to manage Wazuh detection rulesets using DevOps practices such as version control and CI/CD pipelines for automated deployment. This approach improves collaboration, change tracking, and minimizes manual errors by automating ruleset integration and validation processes. #WazuhRaC #DetectionEngineeringAsCode…
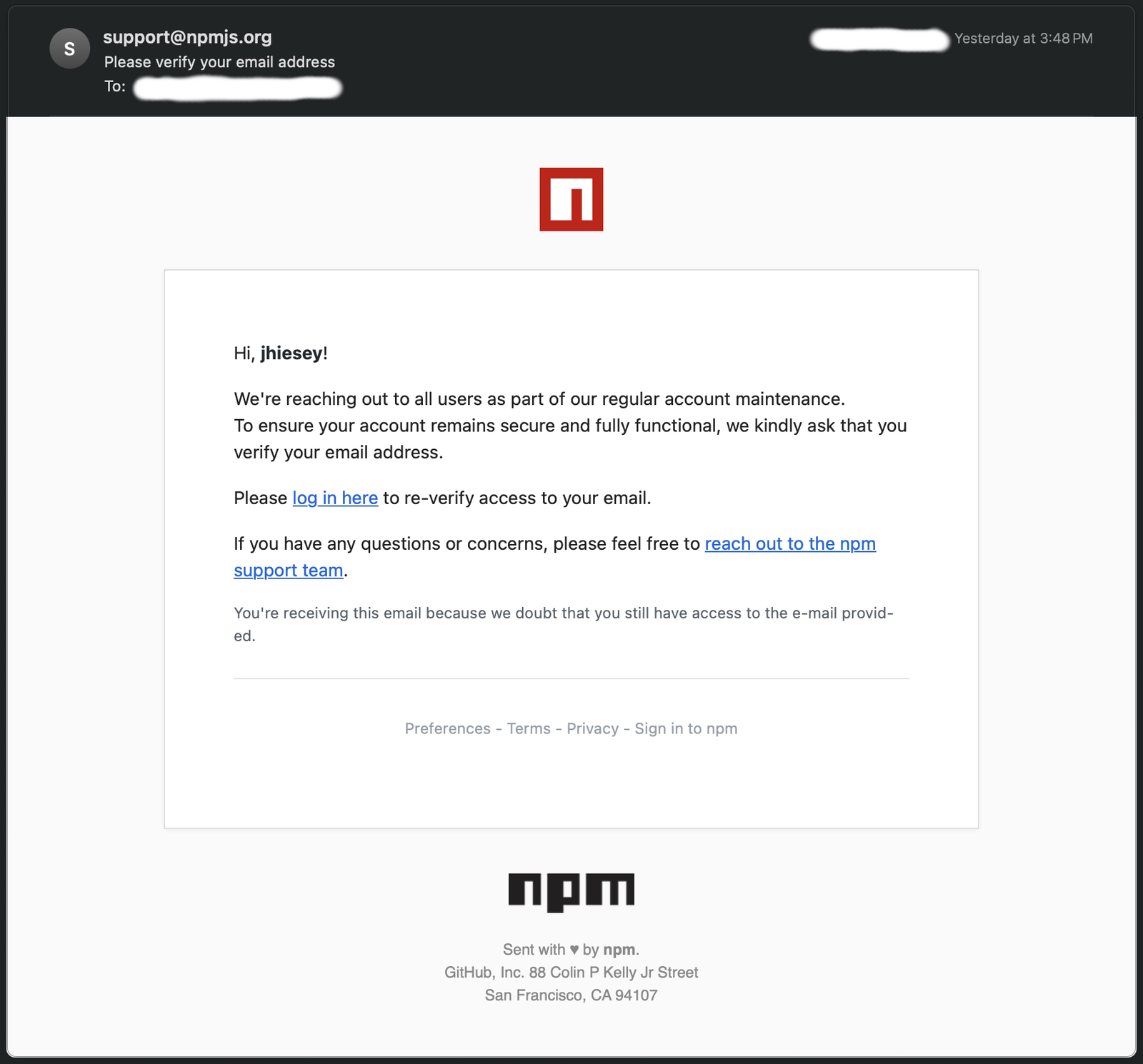
A phishing email impersonating npm targeted a package maintainer by linking to a typosquatted domain, npnjs.com, which hosted a cloned npm website to steal credentials. The email failed multiple authentication checks, was flagged as spam, and involved sophisticated tactics like tokenized URLs and legitimate support links to increase credibility. #npm #npnjs.com #typosquatting
Despite Microsoft’s enhanced security measures blocking macros in Office files downloaded from the internet, macros remain an effective tool for attackers due to widespread use of outdated Office versions and human error. CERT-AGID recently identified a targeted email campaign spreading Formbook malware through spoofed documents linked to a major Italian energy company. #Formbook #CERTAGID #MicrosoftOffice

NimDoor is a sophisticated MacOS malware used by North Korean threat actors, likely Stardust Chollima, targeting cryptocurrency and Web3 organizations through advanced technical methods and social engineering. The malware employs unique persistence mechanisms, process injection, and encrypted communications to steal sensitive credentials and data. #NimDoor #StardustChollima #MacOSMalware #Cryptocurrency
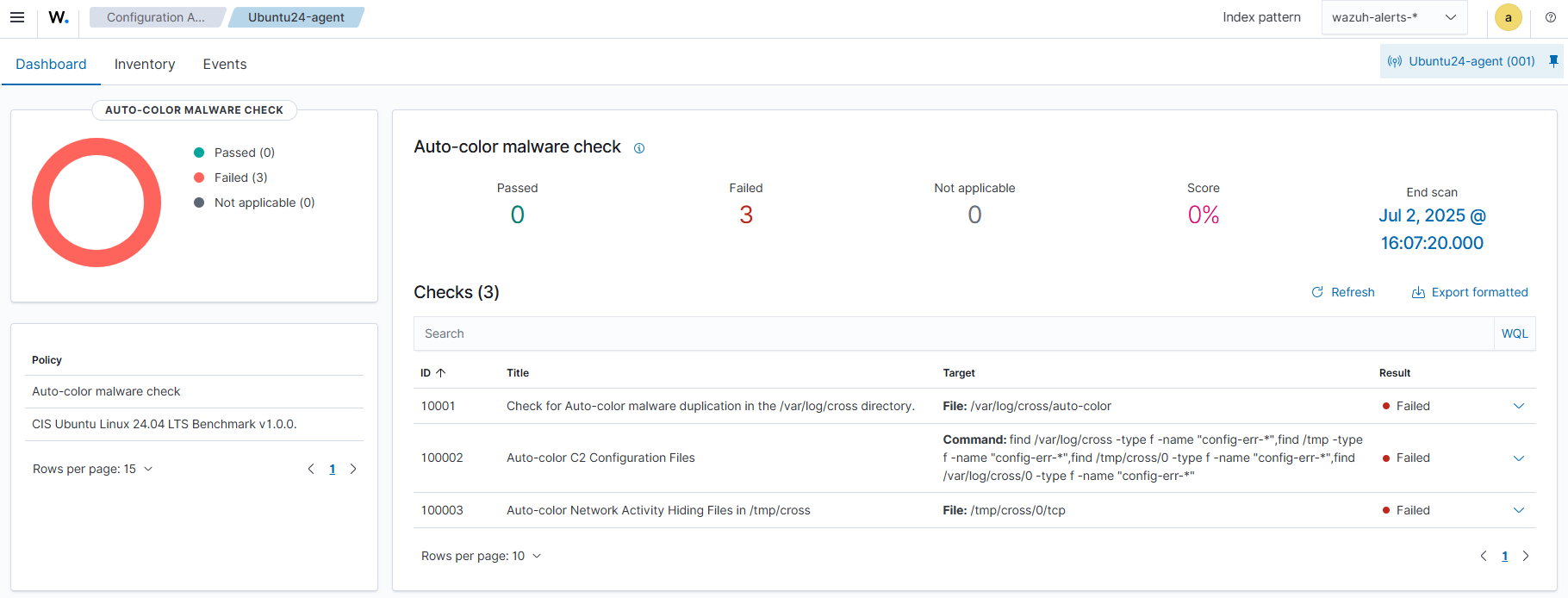
Auto-color is a stealthy Linux backdoor targeting government institutions and universities, designed for persistence and evasion by masquerading as a color-enhancement utility. Detection methods using the open source Wazuh platform, including Security Configuration Assessment and SysmonForLinux integration, are demonstrated to identify and alert on Auto-color malware activities. #Auto-color #Wazuh #SysmonForLinux…
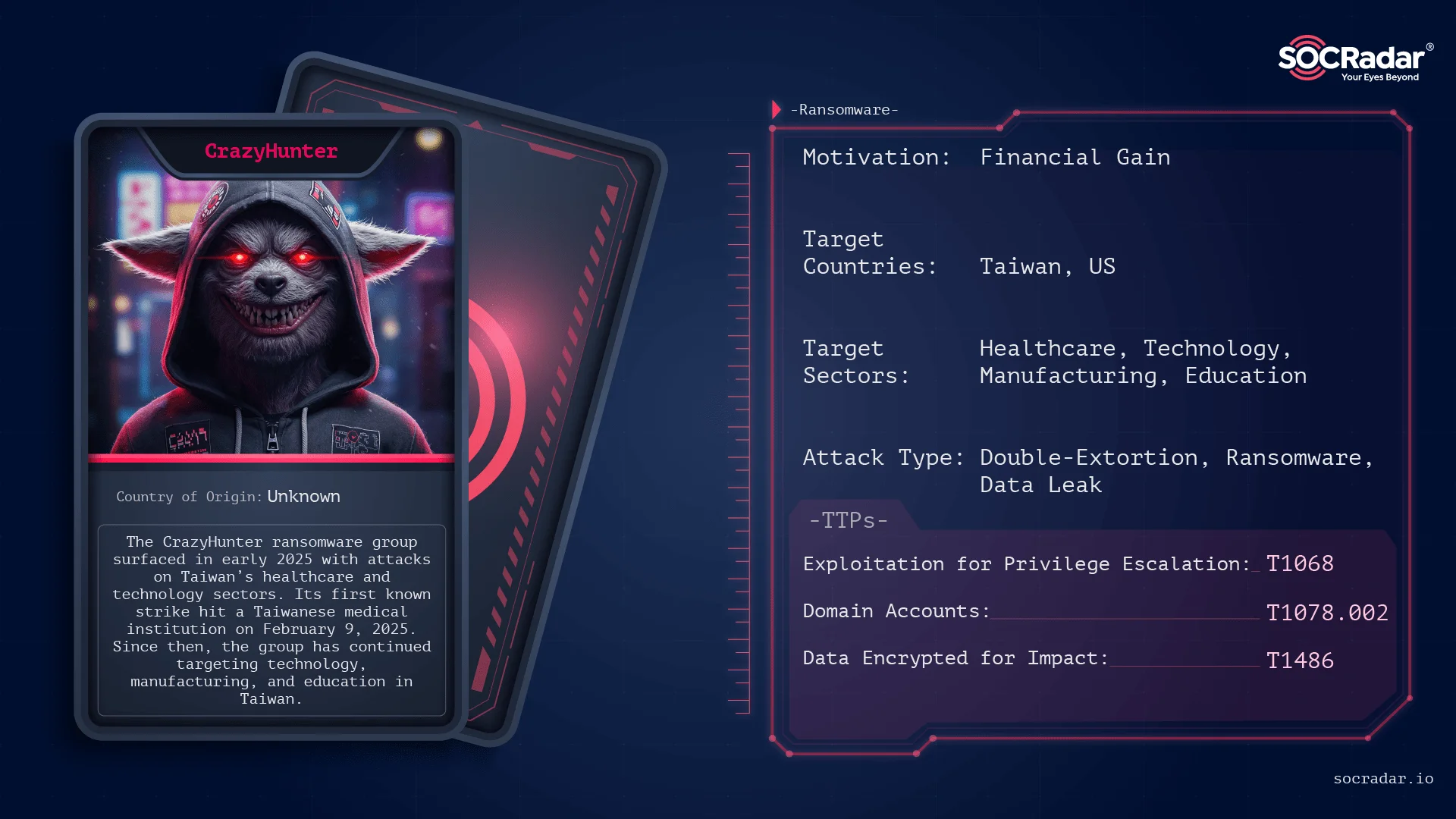
Taiwan MacKay Memorial Hospital was hit by the CrazyHunter ransomware, which used a USB-borne infection vector to deploy its payload through exploited vulnerable drivers and privileged escalation techniques. CrazyHunter targets primarily Taiwanese organizations in healthcare, technology, and manufacturing sectors by leveraging publicly available tools and methods such as Bring Your Own Vulnerable Driver (BYOVD) and SharpGPOAbuse. #CrazyHunter #MacKayMemorialHospital #BYOVD

The newly identified Crux ransomware variant claims association with the BlackByte group and has been observed in three separate incidents, primarily using RDP for initial access. The ransomware employs a unique process chain involving svchost.exe and bcdedit.exe to disable system recovery before encrypting files. #Crux #BlackByte #RDP

Malware notifications reported by MS-ISAC decreased 18% from Q1 to Q2 2025, with SocGholish remaining the most prevalent malware, accounting for 31% of detections. New and returning malware such as VenomRAT, ClearFake, Mirai, and NanoCore contributed to ongoing threats using various infection vectors like malvertisement and malspam. #SocGholish #VenomRAT #MSISAC…

This report details the ongoing exploitation of vulnerabilities CVE-2025-0282 and CVE-2025-22457 targeting Ivanti Connect Secure devices, utilizing sophisticated malware loaders like MDifyLoader to execute Cobalt Strike Beacons and other tools such as vshell and Fscan. Attackers employ advanced tactics for lateral movement, persistence, and defense evasion within compromised networks. #MDifyLoader #CobaltStrike #vshell #Fscan #IvantiConnectSecure #CVE20250282 #CVE202522457
